Last Updated: February 2026
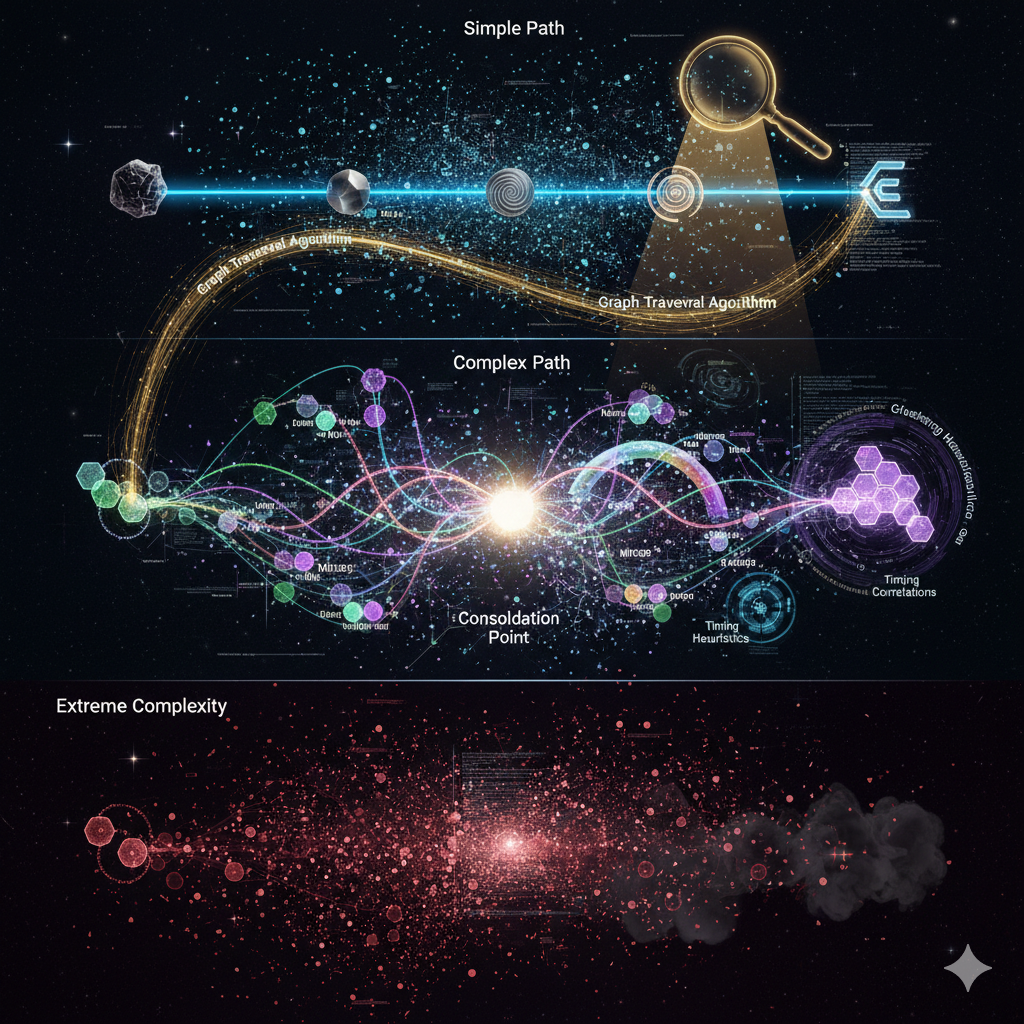
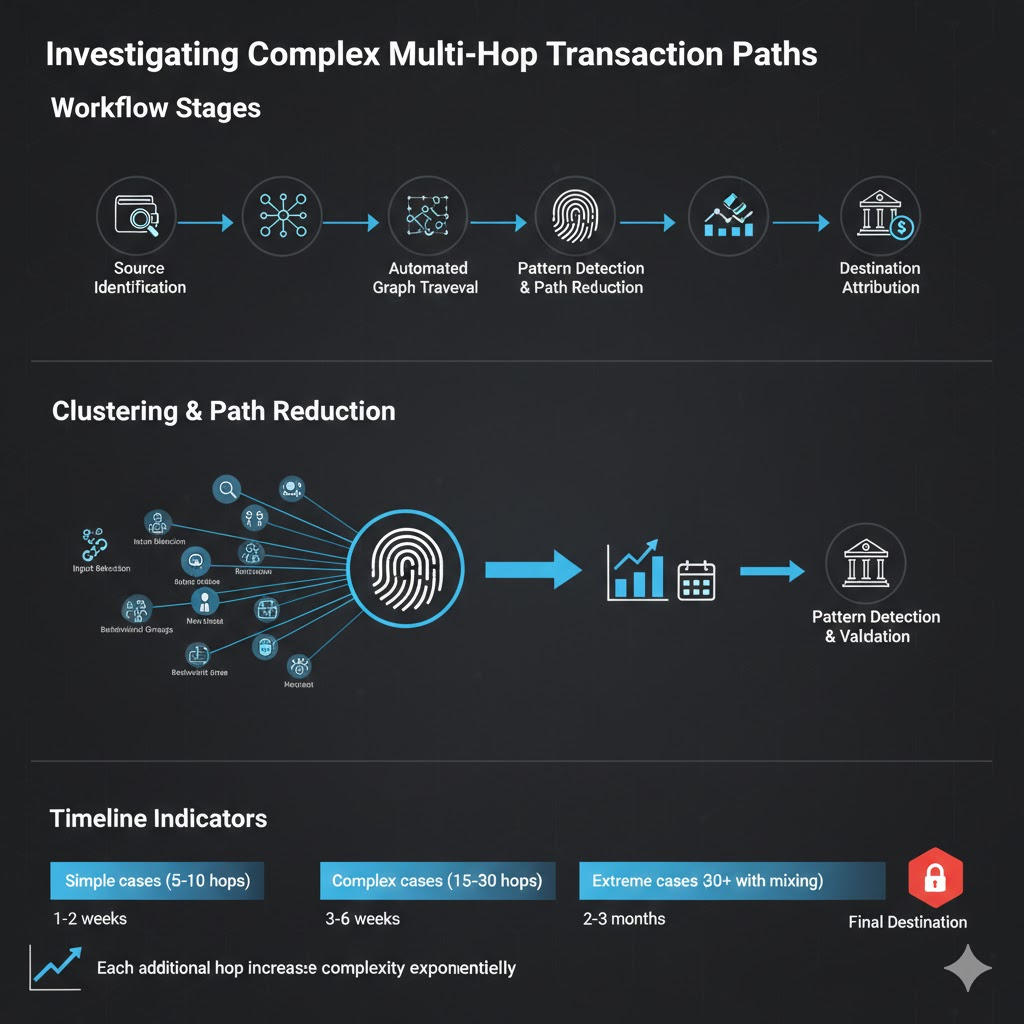
Multi-hop transaction tracking follows cryptocurrency as it moves through multiple sequential transfers designed to obscure the connection between original source and final destination addresses. Investigators reconstruct these chains by analyzing blockchain transaction graphs, identifying clustering patterns that link intermediate addresses to common ownership, detecting timing correlations revealing coordinated movement, and mapping network relationships exposing systematic fund flows across dozens or hundreds of hops. Advanced tracking combines automated graph analysis traversing millions of potential paths, machine learning models predicting likely routes through complex networks, exchange cooperation identifying consolidation points, and heuristic analysis recognizing behavioral patterns criminals inadvertently create when attempting to hide transaction trails.
At Crypto Trace Labs, our team tracks multi-hop transactions across hundreds of cryptocurrency asset recovery and blockchain forensics cases. This guide draws on that decade of on-chain analysis experience to explain multi-hop tracking methodologies, investigation challenges, and successful reconstruction techniques.
Key Takeaways
- Multi-hop transactions separate origins from destinations through systematic movement across 10-100+ intermediate addresses making direct source-to-destination tracking computationally infeasible
- Graph traversal algorithms automate path reconstruction analyzing billions of potential routes to identify highest-probability chains connecting known source addresses to target destinations
- Clustering heuristics reduce complexity by grouping intermediate addresses under common ownership, transforming 50-address chains into 5-6 entity transitions
- Timing analysis reveals coordination patterns when multiple hops execute within suspicious time windows (under 10 minutes) indicating single-operator control rather than organic transfers
- Exchange consolidation points create investigation bottlenecks where criminals must convert cryptocurrency to fiat, enabling investigators to identify cash-out attempts through KYC records
- Cross-chain hopping complicates tracking requiring investigators to bridge Bitcoin, Ethereum, and privacy coin analysis when criminals exploit blockchain interoperability protocols
What Makes Multi-Hop Tracking Challenging?
Multi-hop transactions exploit blockchain’s fundamental characteristic – every wallet can receive and send to any other wallet without restriction. Criminals fragment stolen cryptocurrency across hundreds of addresses, moving funds through complex paths that exponentially increase analysis difficulty. A simple 10-hop transaction creates thousands of potential path variations.
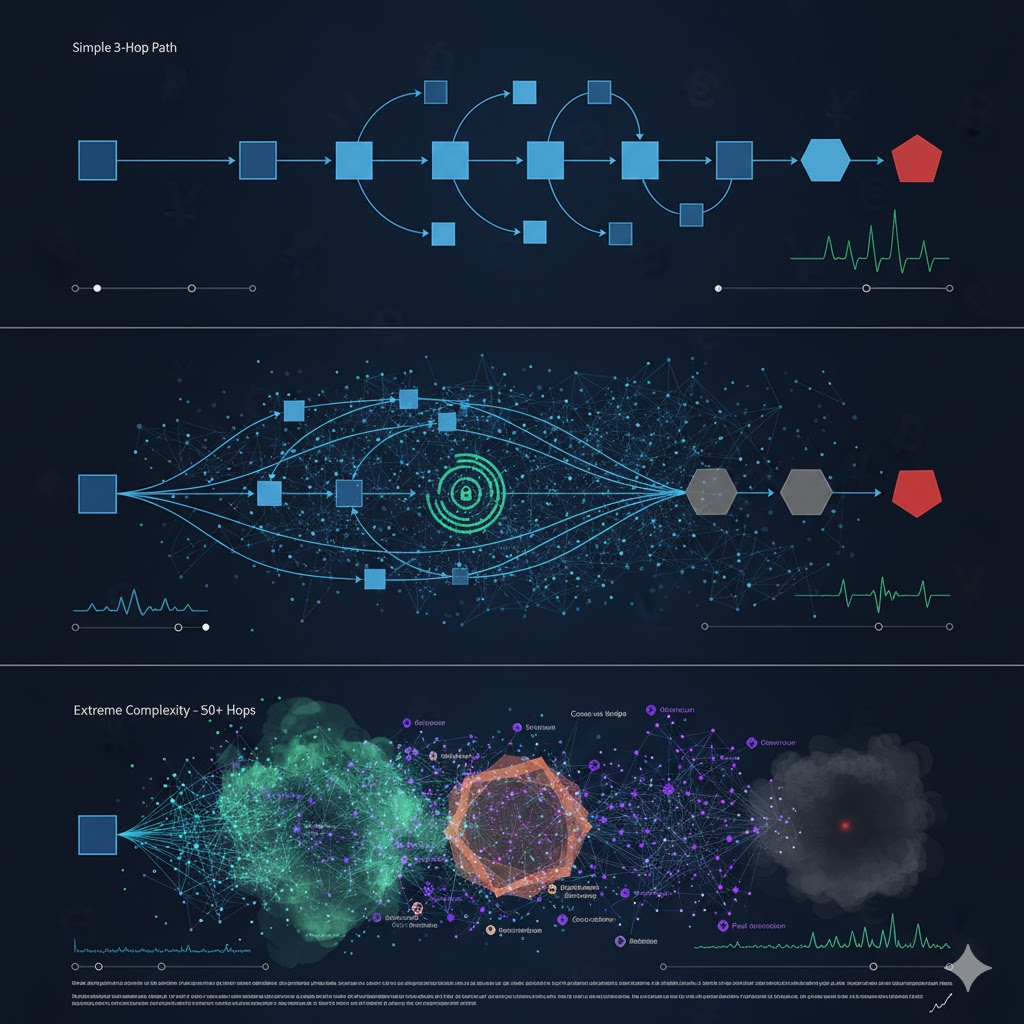
Computational complexity grows exponentially with hop count. Tracking through 5 hops requires analyzing dozens of paths. Tracking through 20 hops generates millions of potential routes. When criminals add mixing services or cross-chain bridges, path complexity increases by orders of magnitude.
Address clustering uncertainty compounds difficulty. Investigators must determine which addresses belong to the same entity. If addresses A, B, and C are controlled by one criminal, a 10-transaction path represents 3 hops not 10. However, clustering operates probabilistically – 85% confidence compounds across multiple hops, deteriorating overall attribution confidence.
Time delays create investigation windows where criminals obscure trails. When funds sit dormant for weeks between hops, real-time monitoring becomes impossible. Investigators must retrospectively reconstruct paths after crimes are reported.
How Do Graph Analysis Algorithms Track Multi-Hop Paths?
Comparison Table: Multi-Hop Tracking Methodologies
| Tracking Method | Technical Approach | Hop Complexity Handled | Success Rate | Investigation Timeline | Best Application |
| Direct Graph Traversal | Follow transaction outputs recursively from source | 1-5 hops | 95%+ | Hours to days | Simple linear paths, recent transactions |
| Breadth-First Search | Explore all possible paths systematically by depth level | 5-15 hops | 85-92% | Days to weeks | Moderate complexity, known destination hints |
| Heuristic Path Pruning | Eliminate unlikely paths using clustering and timing rules | 10-25 hops | 75-88% | Weeks | Complex fragmentation, multiple branch paths |
| Machine Learning Path Prediction | Neural networks predict probable routes through networks | 15-50+ hops | 70-85% | Weeks to months | Extreme complexity, mixing service usage |
| Temporal Correlation Analysis | Identify coordinated hops through timing patterns | Any complexity | 80-90% (combined) | Weeks | Rapid sequential transfers, bot operations |
| Exchange Consolidation Detection | Focus on likely cash-out points rather than full paths | Any complexity | 85-95% | Days to weeks | Cases where criminals must eventually cash out |
Breadth-first search algorithms systematically explore transaction graphs level by level. Starting from criminal source addresses, algorithms identify all direct recipients (first hop), then all recipients from those addresses (second hop), continuing until reaching target depth. This ensures no paths are missed but becomes computationally expensive beyond 10-15 hops.
Heuristic pruning reduces computational overhead by eliminating unlikely paths. Algorithms discard routes through addresses with very old transactions, known public entities, or amount mismatches inconsistent with criminal behavior.
Machine learning models trained on confirmed criminal transaction paths predict probable routes through complex networks. These models learn criminal tendencies – fragmentation patterns, mixing service preferences, timing behaviors – then assign probability scores to millions of potential paths.
Temporal correlation analysis identifies coordinated hops through transaction timing. When multiple addresses execute transactions within 5-minute windows repeatedly, investigators recognize single-operator control enabling path reconstruction despite limited clustering confidence.
What Patterns Reveal Multi-Hop Criminal Operations?
Numbered Listicle: 6 Multi-Hop Patterns That Expose Criminal Operations
1. Systematic Fragmentation-Consolidation Cycles
Criminals split large stolen amounts into dozens of smaller outputs across multiple addresses (fragmentation), let funds sit dormant, then systematically consolidate back into fewer addresses before the next hop. Investigators identify these cycles by detecting addresses receiving funds from 10+ sources within short timeframes, then sending consolidated amounts to single destinations. The pattern reveals criminal operations because legitimate users rarely consolidate funds from dozens of unrelated sources.
2. Consistent Amount Splitting Algorithms
When criminals fragment cryptocurrency, they often use algorithmic splitting – dividing $100,000 into exactly 20 addresses of $5,000 each, or using Fibonacci sequences. These mathematical patterns distinguish criminal fragmentation from organic transaction networks where amounts vary naturally. Investigators detect algorithmic splitting through statistical analysis, enabling tracking across multiple hops.
3. Timing Precision Across Sequential Hops
Automated criminal systems execute multi-hop sequences with precise timing – transactions at 10:00:00, 10:05:00, 10:10:00 exhibiting 5-minute intervals impossible through manual operation. Investigators calculate time intervals between connected transactions discovering when sequential hops maintain consistent intervals proving automated coordination, dramatically reducing analysis complexity.
4. Mixer Exit Clustering Patterns
Criminals using cryptocurrency mixers create distinctive patterns when withdrawing mixed funds. Rather than withdrawing to single addresses, operators withdraw to 5-15 addresses simultaneously. However, these withdrawal addresses then exhibit correlated subsequent behavior – they consolidate funds or execute transactions during identical time windows. Investigators identify mixer exit addresses through withdrawal timing correlation.
5. Cross-Chain Bridge Timing Signatures
When criminals hop between Bitcoin and Ethereum using bridge protocols, they create timing signatures linking addresses across blockchains. Bitcoin transactions send funds to bridge addresses at timestamp T. Within 10-30 minutes, corresponding Ethereum addresses receive bridge outputs. Investigators correlate these timing patterns identifying which Ethereum addresses received bridge transfers corresponding to criminal Bitcoin deposits.
6. Exchange Deposit Clustering
Criminals eventually consolidate multi-hop funds before depositing to exchanges for fiat conversion. This final consolidation creates distinctive patterns – addresses that received funds through complex paths all send to common consolidation addresses, which then deposit to exchanges. Investigators work backwards from known exchange deposit addresses finding consolidation addresses, then tracing backwards to original criminal sources.
How Do Investigators Overcome Tracking Obstacles?
Exchange cooperation provides critical intelligence when multi-hop paths reach deposit addresses. Platforms like Coinbase, Kraken, and Binance maintain transaction records linking deposit addresses to customer identities through KYC documentation. When investigators trace paths to exchange deposits, cooperation requests reveal account holders enabling criminal identification.
Clustering algorithms reduce multi-hop complexity by grouping related addresses. A 50-transaction path might collapse to 8-10 entity transitions when clustering identifies address groups. Common input heuristics, change address detection, and behavioral fingerprinting enable clustering, allowing investigators to focus on entity-level transitions.
Cross-chain analysis tools track funds when criminals bridge between blockchains. Specialized platforms monitor bridge protocol addresses, correlate deposit/withdrawal timing, and maintain databases linking cross-chain transfers enabling investigation continuation despite blockchain transitions.
Timing correlation analysis reconstructs paths when address clustering provides limited confidence. By identifying sequential transactions occurring within suspicious time windows (under 10 minutes), investigators establish probable relationships providing additional attribution confidence.
What Legal and Investigative Challenges Exist?
Multi-jurisdictional coordination requirements slow investigations when multi-hop paths cross international boundaries. Criminals route funds through exchanges in countries with limited law enforcement cooperation, requiring mutual legal assistance requests taking months to fulfill.
Evidence preservation challenges arise when criminals use services with limited record retention. Mixing services and decentralized exchanges often delete transaction records after weeks. If investigations don’t identify mixing usage quickly, critical evidence may be permanently lost.
Privacy coin integration creates analysis dead-ends when criminals convert Bitcoin to Monero. Privacy coins employ cryptographic techniques obscuring transaction graphs. However, entry and exit points remain vulnerable – conversions at exchanges create records enabling partial path reconstruction.
Frequently Asked Questions
How many hops can investigators reliably track?
Reliable tracking depends on hop complexity and available intelligence. Simple linear paths through 10-15 hops achieve 85-95% confidence using automated graph traversal. Complex paths with fragmentation and mixing reduce confidence but remain trackable through 20-30 hops using clustering algorithms and pattern recognition. Beyond 30 hops, especially when involving privacy coins or sophisticated mixing, confidence drops to 60-75% requiring significant manual analysis and external intelligence. However, exchange consolidation detection often enables successful investigation regardless of hop count by focusing on cash-out points rather than complete path reconstruction.
What makes some multi-hop paths easier to track than others?
Path tracking difficulty depends on several factors: timing between hops (rapid sequential transfers easier to correlate), amount consistency (similar amounts across hops indicate relationship), address reuse (criminals reusing addresses create clustering opportunities), mixing service usage (mixers break attribution), and cross-chain transitions (blockchain changes require specialized analysis). Paths through exchanges with strong KYC compliance are easier to track than paths through decentralized services. Criminals using automated systems paradoxically make tracking easier through precise timing patterns, while sophisticated manual operations with randomized delays prove more challenging.
How do investigators handle path fragmentation?
When criminals split funds across multiple branches, investigators use parallel tracking analyzing each fragment simultaneously. Graph traversal algorithms explore all branches documenting amounts, timing, and destinations. Consolidation point detection identifies where fragments reunite – criminals must eventually consolidate to manage funds efficiently. Investigators focus resources on tracking the largest value branches while monitoring smaller fragments for consolidation signals. Machine learning models predict likely consolidation addresses based on timing patterns and amount distributions, directing investigator attention toward probable reunion points.
What happens when multi-hop paths reach dead ends?
Dead ends occur when criminals successfully cash out through uncooperative exchanges, convert to privacy coins without trackable exits, or transfer to addresses that remain dormant. Investigators employ several strategies: monitoring dead-end addresses for future activity (criminals often return to dormant addresses), analyzing historical patterns suggesting likely next moves, submitting exchange cooperation requests to uncooperative platforms through legal channels, and correlating dead-end timing with real-world events (large purchases, travel, financial activity) revealing criminal identities despite blockchain attribution limits.
What new techniques are improving multi-hop tracking?
Machine learning path prediction models now achieve 70-85% accuracy predicting likely routes through complex networks, directing investigators toward probable paths rather than exhaustive analysis. Graph neural networks learn criminal behavioral patterns identifying which of thousands of potential next hops criminals will most likely choose. Real-time blockchain monitoring systems alert investigators within minutes of suspicious multi-hop sequences enabling intervention before criminals complete cash-out. Cross-chain analysis tools automatically detect bridge transactions and correlate activity across Bitcoin, Ethereum, and other blockchains. These advances significantly reduce investigation timelines while increasing success rates against sophisticated multi-hop operations.
Professional Multi-Hop Transaction Tracking
Multi-hop transaction tracking requires specialized expertise, advanced analytical tools, and exchange relationships that most organizations lack. When cryptocurrency moves through complex paths designed to obscure origins, professional blockchain forensics can determine whether funds are recoverable and identify criminal operators.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We’ve tracked funds through complex multi-hop paths in hundreds of investigations, recovering millions in stolen cryptocurrency by identifying consolidation points and cash-out attempts before criminals complete conversions.
What we provide:
- Automated graph analysis processing billions of potential transaction paths
- Clustering algorithms reducing complex 50-hop chains to manageable entity transitions
- Cross-chain tracking following funds through Bitcoin, Ethereum, and bridge protocols
- Exchange cooperation leveraging executive relationships for accelerated KYC data retrieval
- Pattern recognition identifying fragmentation-consolidation cycles and timing signatures
- Real-time monitoring alerting to suspicious multi-hop sequences enabling rapid response
We offer no upfront charge for non-custodial wallet recoveries. For investigation services, we provide transparent project-based pricing based on case complexity.
Schedule a Free Case Assessment – We’ll analyze your situation and explain how multi-hop tracking can support your investigation or recovery effort.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- How to Track Blockchain Transactions: Expert Guide
- How to Trace Cryptocurrency Through Mixers: Expert Guide
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- What Is Cryptocurrency AML Compliance?
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, transaction tracking, and asset recovery.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have successfully tracked cryptocurrency through complex multi-hop paths in ransomware investigations, theft cases, and fraud recovery operations, working with law enforcement and private clients globally.
For professional blockchain forensics, multi-hop transaction tracking, or cryptocurrency investigation services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Transaction tracking and asset recovery outcomes depend on specific circumstances, criminal sophistication, and cooperation from exchanges and law enforcement. Consult qualified professionals regarding your situation.