Last Updated: March 2026
Blockchain evidence documentation for legal admissibility is the structured process of recording, preserving, and presenting on-chain data in a form that satisfies the procedural requirements of UK courts. Admissibility is not determined by whether the blockchain data is technically accurate – it is determined by whether the documentation accompanying that data can prove its integrity, establish its provenance, and withstand scrutiny by an opposing expert. According to the Forensic Science Regulator’s 2024 Codes of Practice, any digital evidence presented in UK proceedings must be accompanied by records establishing how it was obtained, who handled it, and what steps were taken to ensure it was not altered.
Crypto Trace Labs produces legally admissible blockchain evidence packages for civil fraud claims, criminal referrals, regulatory proceedings, and injunction applications. The team holds ACAMS (Association of Certified Anti-Money Laundering Specialists) accreditations, MLRO (Money Laundering Reporting Officer) qualifications across the UK, US, and EU, and Chartered Fellow Grade at the CMI – with founding members from Blockchain.com, Kraken, and Coinbase operating at VP and Director level.
Key Takeaways
- Documentation is what makes data evidence: Raw blockchain data is not evidence until it is accompanied by source records, hash verification, and a chain of custody log that courts can evaluate.
- Source URLs and timestamps are mandatory: Every API call or block explorer query used to collect blockchain data must be logged with its full URL and the exact time the query was made.
- Hash verification proves integrity: An SHA-256 hash computed at the moment of collection and again before submission proves the data has not been altered between collection and court.
- Expert reports must comply with CPR Part 35: According to Chainalysis‘s 2024 litigation guidance, courts disregard blockchain analysis reports where the expert has not formally declared their duty to the court and confirmed their independence from the instructing party.
- Annotation of analysis steps is required: Each analytical conclusion must be traceable back through documented steps to the underlying raw data.
Why This Matters
Inadequate documentation is the leading cause of otherwise sound blockchain evidence being excluded or discounted in UK court proceedings. A forensic analyst may correctly identify the movement of stolen Bitcoin through five exchanges and into a defendant’s wallet – but if the collection process was not documented, if hash verification was skipped, or if the chain of custody log has gaps, opposing counsel can argue the evidence is unreliable. In crypto fraud cases, where technical complexity already creates barriers for judges, any procedural weakness in evidence documentation is amplified. Cases worth hundreds of thousands or millions of pounds can fail not because the blockchain evidence was wrong, but because it was not properly documented from the start.
The Documentation Framework Courts Expect
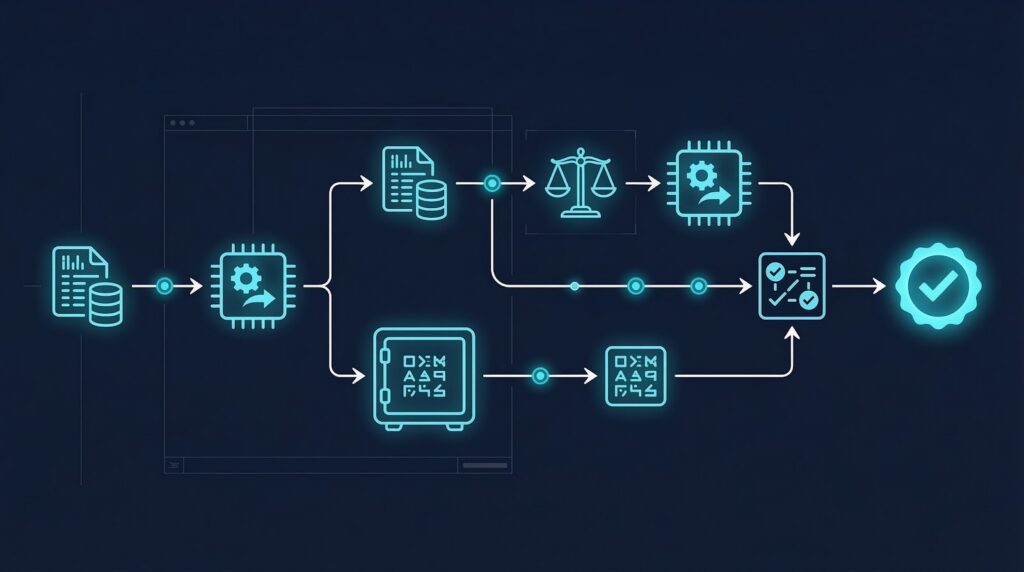
The documentation framework for legally admissible blockchain evidence consists of four interconnected layers that must be completed before any analysis is presented to a court.
The first layer is collection documentation: records of what was collected, from where, when, and by whom. The second layer is integrity verification: hash values and comparison records proving the data has not changed. The third layer is analysis documentation: a step-by-step record of how raw data was processed into forensic conclusions. The fourth layer is the expert declaration: formal confirmation by the analyst that they are qualified, independent, and compliant with CPR Part 35.
Each layer must be prepared contemporaneously – that is, at the time the work is done, not reconstructed afterwards. Courts are experienced at identifying retrospective documentation.
| Documentation Layer | Required Content | When Completed |
|---|---|---|
| Collection records | Source URL, timestamp, raw data, hash | At collection |
| Integrity verification | SHA-256 hashes at collection and submission | At collection + submission |
| Analysis log | Step-by-step methodology, tool names, outputs | During analysis |
| Expert declaration | Qualifications, independence, CPR Part 35 | Before report submission |
Source Documentation Requirements
Source documentation establishes where blockchain data came from, which is the foundation of any admissibility challenge response.
For every data collection action, the analyst must record: the full URL of the endpoint queried (including any query parameters); the authentication method used if applicable (API key type, not the key itself); the date and time of the query in UTC; the full raw response received; and an SHA-256 hash of that response computed immediately after receipt. This record must be stored in a format that cannot be retrospectively altered – a signed PDF, a notarised record, or an evidence management system with audit logging.
According to TRM Labs‘s 2024 forensic best practice guide, courts are increasingly asking analysts to demonstrate that the data they collected is identical to what a second analyst would collect if they ran the same query against the same source at the same time. Cross-verification – querying the same transaction or address from two independent sources and documenting both – is the most effective way to satisfy this requirement.
Hash Verification Procedures
Hash verification is the technical mechanism that proves blockchain evidence has not been altered between the moment of collection and the moment it is presented to a court.
The standard hashing algorithm for digital evidence in UK proceedings is SHA-256, which produces a 64-character hexadecimal string unique to the specific content of a file or data object. If a single character of the data is altered after hashing, the hash value changes completely, making tampering detectable. The analyst must compute and record the hash of each collected dataset at the moment of collection, store it in the chain of custody log, and recompute it before submission to court to confirm the values match.
For large datasets – full blockchain downloads, extended address history exports – the hash must be computed on the complete file, not a sample. Chainalysis and Elliptic both recommend that evidence packages submitted to courts include a hash manifest listing every file in the package with its SHA-256 value, allowing the court or opposing expert to verify the integrity of each component independently.
Chain of Custody Log Standards
The chain of custody log is the documentary spine of the evidence package, tracking every person and process that touched the evidence from collection to court presentation.
For blockchain evidence, the log must record: who initially collected the data; what storage medium was used; how the evidence was transferred to the next handler (encrypted email, secure evidence management system, physical media); who received it and when; what analysis work was performed and by whom; and any exports, transformations, or format changes applied at each stage. Each entry must be signed or initialled by the person responsible.
Gaps in the chain of custody – periods where the evidence cannot be accounted for, or transfers that are undocumented – create presumptions of potential tampering that opposing experts will exploit. Evidence management software such as Nuix or EnCase maintains automatic audit logs, but even a carefully maintained spreadsheet with signed entries can satisfy the requirement if it is genuinely contemporaneous.
Annotating Analysis Steps for Court Presentation
Every analytical conclusion in a blockchain forensic report must be supported by documented analysis steps that allow the court or an opposing expert to trace the conclusion back to the underlying raw data.
This means that when a report states that Wallet A sent 2.5 BTC to Wallet B, and Wallet B subsequently sent those funds to Exchange C’s deposit address, the report must be accompanied by documentation showing: the transaction hashes for each transfer, the block heights and timestamps, the source of the attribution linking Wallet B to the defendant, and the source of the attribution identifying Exchange C’s deposit address. Each attribution must state whether it is confirmed (from KYC data or exchange records) or probabilistic (from clustering heuristics), and the confidence level must be stated.
According to Elliptic’s 2024 forensic methodology documentation, courts have increasingly required analysts to distinguish between what the blockchain data directly shows and what has been inferred from it – treating these as separate categories of evidence with different weights.
Frequently Asked Questions
What makes blockchain evidence legally admissible in UK courts?
Blockchain evidence is legally admissible when it is accompanied by documentation proving its integrity and provenance. This requires source records showing where the data came from, hash values proving it has not been altered, a chain of custody log tracking every handler, and an expert report compliant with CPR Part 35. The technical accuracy of the blockchain data itself is secondary – courts assess admissibility primarily on the quality of the documentation.
Do I need a solicitor to collect blockchain evidence?
You do not need a solicitor to collect blockchain evidence, but you do need a qualified forensic expert if the evidence will be used in proceedings. Solicitors typically engage specialist blockchain forensic firms to collect and analyze evidence on their clients’ behalf. The forensic expert then prepares a CPR Part 35 compliant report. Attempting to self-collect and self-document blockchain evidence without forensic qualifications creates serious admissibility risks.
How does hash verification work for blockchain evidence?
Hash verification involves computing an SHA-256 hash of a data file at the moment it is collected, recording that hash value in the chain of custody log, and recomputing the hash before submission to confirm the values match. If the hash values match, the data has not changed. If they do not match, the data has been altered and the evidence is compromised. Courts accept hash verification as the standard method for proving digital evidence integrity.
Can WhatsApp messages or emails showing crypto transactions be used as evidence?
Yes, but they must be collected and documented to the same standard as blockchain data. Screenshots of WhatsApp messages, email correspondence, or wallet interface screenshots require the same source documentation, hash verification, and chain of custody procedures. In practice, screenshots are weaker evidence than direct blockchain data because they can be fabricated, so they are typically used to corroborate rather than prove the underlying transaction.
What is CPR Part 35 and why does it matter for blockchain evidence?
CPR Part 35 governs expert evidence in UK civil proceedings. It requires that experts comply with their overriding duty to the court rather than the instructing party, that their reports contain a declaration of independence, and that they disclose any limitations in their evidence. Blockchain forensic reports that do not comply with CPR Part 35 are routinely challenged as partial, and courts may disregard them or require a further compliant report to be prepared.
How long should documentation be retained after proceedings conclude?
Documentation should be retained for a minimum of six years after proceedings conclude, consistent with the Limitation Act 1980. If there is any prospect of appeal, related proceedings, or regulatory action, retention for a longer period is advisable. The original collection records, hash values, and chain of custody logs must be preserved in their original form – not just the final report.
What is the difference between a forensic report and an expert witness report?
A forensic report documents the technical findings of blockchain analysis. An expert witness report presents those findings in a form compliant with CPR Part 35, including a declaration of the expert’s qualifications, independence, and duty to the court. In proceedings, the expert witness report is the document filed with the court. The forensic report forms the technical foundation of the expert witness report but is not itself a court document.
Can blockchain evidence from foreign jurisdictions be used in UK courts?
Blockchain evidence collected abroad is generally admissible in UK civil proceedings provided it meets UK standards for documentation and integrity. The collecting expert must be capable of addressing UK admissibility standards in cross-examination. Where evidence was collected under a different legal framework, a statement explaining the applicable collection standards in the foreign jurisdiction should accompany the evidence package to assist the court.
Executive Summary
Documenting blockchain evidence for legal admissibility requires a systematic approach covering collection records, hash verification, chain of custody logging, and analysis annotation – all completed contemporaneously and maintained to a standard that can withstand cross-examination by a specialist opposing expert. UK courts assess admissibility primarily on documentation quality, not technical accuracy. Blockchain forensic firms that treat documentation as an afterthought produce evidence that routinely fails admissibility challenges, regardless of how technically correct their analysis may be. Engaging ACAMS-accredited forensic experts from the outset, with documented collection procedures and CPR Part 35 compliance built in, is the only reliable approach.
What Should You Do Next?
If you are building a blockchain evidence package for litigation, a regulatory submission, or a law enforcement referral, ensure documentation standards are applied from the first query, not retrofitted before submission. Crypto Trace Labs provides end-to-end blockchain evidence documentation – from initial collection through to CPR Part 35 compliant expert reports – for clients across the UK, EU, and US.
Our team – ACAMS-accredited, MLRO-qualified across three jurisdictions, Chartered Fellow Grade at the CMI, with VP and Director-level experience at Blockchain.com, Kraken, and Coinbase – has recovered 101 Bitcoin for clients in the last 12 months and regularly provides expert witness testimony in UK High Court proceedings. We offer no upfront charge for non-custodial wallet recoveries. Contact us to discuss your case.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- Definition of Digital Evidence: Complete Guide for 2026
- Crypto Freezing Injunctions: How Courts Protect Victims of Cryptocurrency Theft
- On-Chain Heuristics: How Pattern Recognition Identifies Wallet Owners
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm founded by VP and Director-level executives formerly of Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across the UK, US, and EU, and Chartered Fellow Grade status at the CMI. With over 10 years of experience in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin for clients in the last 12 months and delivered record fraud reduction for a $14bn crypto exchange. We work with law enforcement agencies, regulated financial institutions, and private clients on crypto asset recovery, blockchain forensics, AML compliance, and expert witness testimony – globally. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





