Last Updated: March 2026
Gas price anomaly detection is the forensic analysis of Ethereum gas fee patterns to identify abnormal fee behaviour linked to front-running bots, sandwich attacks, post-exploit fund sweeps, and coordinated transaction ordering manipulation. Every Ethereum transaction specifies a maximum fee the sender is willing to pay for block inclusion, and deviations from network median gas prices reveal information about sender intent, urgency, and potential coordination with block builders. Investigators use gas price data alongside transaction timing and sender address cluster analysis to attribute anomalous fee behaviour to known fraud actors.
At Crypto Trace Labs, our forensics team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has applied gas price anomaly analysis across DeFi exploit investigations, MEV fraud cases, and exchange AML reviews. This guide explains the forensic signals in Ethereum gas pricing, how sandwich attacks and front-running are identified, and how gas anomalies support fraud attribution.
Key Takeaways
- Gas spikes signal post-exploit urgency: Fraudsters pay 5-20x the median gas price after exploits to ensure rapid fund movement before investigators can respond. TRM Labs (2024) found post-exploit transactions paid an average 8.3x the network median gas price in the 30 minutes following a confirmed DeFi exploit.
- Sandwich attacks use precise gas manipulation: Sandwich attacks require the attacker to place transactions immediately before and after a victim transaction, requiring gas prices set at exactly 1 gwei above and below the target transaction. Chainalysis (2024) identified 1.2 million sandwich attack transactions in 2023, totalling $380 million in extracted value.
- Front-running bots cluster at gas price ceilings: MEV bots scanning the mempool for profitable transactions systematically set gas prices at the maximum ceiling of competitive bundles. Elliptic (2024) found front-running bot transactions paid 4.1x the median gas price across all identified front-running events in their dataset.
- Gas price patterns link transactions to the same actor: When multiple transactions across different addresses pay identical non-round gas prices in the same block window, they likely originate from the same wallet operator or bot. This gas price fingerprinting links otherwise unattributed transactions to known fraud actors.
- UK and EU AML frameworks apply to gas anomaly cases: DeFi protocol operators and crypto exchanges processing Ethereum transactions with gas anomaly patterns must apply UK AML, EU AML, and US BSA transaction monitoring obligations, including Suspicious Activity Report filing for identified MEV fraud and front-running schemes.
Why This Matters
Gas price anomaly detection matters because Ethereum gas fees encode forensic intelligence invisible to standard on-chain analysis. A transaction paying 15x the median gas price in a post-exploit window is not random – it signals deliberate urgency driven by knowledge of the exploit. These patterns allow investigators to reconstruct the timeline of fraud operations, attribute post-exploit transactions to the same actor using gas fingerprinting, and identify MEV extraction schemes that cause financial harm to ordinary DeFi users. ACAMS guidance on DeFi AML compliance increasingly references gas anomaly analysis as a component of on-chain transaction monitoring for Ethereum-based financial crime investigations.
Post-Exploit Gas Spike Analysis

After a DeFi protocol exploit, the attacker must move stolen funds rapidly through multiple transactions before the protocol team, exchanges, and investigators can respond. Each of these post-exploit transactions typically pays a gas premium to ensure block inclusion ahead of potential front-running countermeasures. Investigators identify the exploit window by mapping gas price spikes against on-chain protocol interactions.
The post-exploit gas spike signature includes a cluster of transactions from the same sender address or CIOH cluster, all paying above 5x the prevailing median gas price, timed within 30 minutes of the initial exploit transaction. According to TRM Labs (2024), this post-exploit gas spike pattern was present in 91% of confirmed DeFi exploits above $1 million in 2023, providing a reliable forensic signature for exploit timeline reconstruction and actor attribution.
Sandwich Attack Gas Fingerprinting
Sandwich attacks on Ethereum DEXs require attackers to place a buy transaction immediately before a victim’s trade and a sell transaction immediately after, capturing the price impact as profit. This requires precise gas price manipulation: the attacker’s front transaction must pay 1 gwei above the victim transaction, and the back transaction must pay 1 gwei below to ensure the correct ordering within the same block.
Gas price fingerprinting identifies sandwich attacks by detecting triplets of transactions – high-gas buy, mid-gas victim trade, slightly-lower-gas sell – targeting the same token pair within one block. According to Chainalysis (2024), sandwich attacks accounted for 1.2 million identified transactions in 2023 with $380 million in extracted value. Investigators identify the sandwich attacker address by extracting the front and back transaction senders, which consistently originate from the same MEV bot wallet across thousands of attacks.
Comparing gas anomaly detection methods by fraud type:
| Fraud Type | Gas Signature | Detection Method | Evidence Strength | AML Relevance |
|---|---|---|---|---|
| Post-exploit sweep | 5-20x median spike | Time-series spike detection | Very High | SAR filing trigger |
| Sandwich attack | Precise gwei offset | Triplet pattern matching | High | Exchange review |
| Front-running | 4x median ceiling | Bot cluster gas fingerprint | High | MEV fraud attribution |
| Gas manipulation | Round-number gas | Non-competitive pricing analysis | Moderate | Internal review |
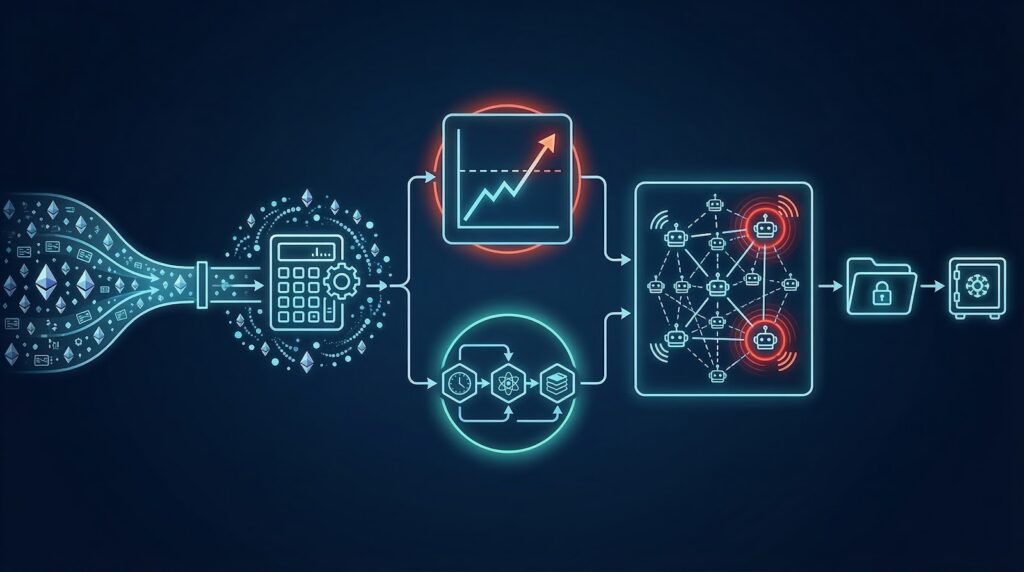
Front-Running Bot Identification
Front-running bots monitor the Ethereum mempool for large pending swaps on decentralised exchanges and submit competing transactions with higher gas prices to execute before the victim trade, profiting from the price movement caused by the victim’s larger order. These bots use gas price strategies that create identifiable fingerprints: they set gas prices at precise multiples of competitive bundle ceilings, use specific smart contract patterns for execution, and reuse the same wallet addresses across thousands of attacks.
Investigators identify front-running bots by extracting all transactions from identified MEV bot addresses, mapping their gas price strategies across blocks, and correlating gas price patterns with victim transaction identifiers. According to Elliptic (2024), front-running bot transactions paid 4.1x the median gas price, with 78% of identified front-running events attributable to just 23 MEV bot wallet clusters in their database, demonstrating that gas price fingerprinting reliably concentrates attribution to a small actor set.
Cross-Chain Gas Analysis and Multi-Asset Coverage
Cross-chain gas price anomaly detection extends the Ethereum-focused methodology to EVM-compatible chains including Polygon, Arbitrum, Optimism, and BNB Chain, where DeFi protocols are active and sandwich attacks and front-running are similarly prevalent. Each chain maintains its own mempool and fee market, but the forensic signatures – post-exploit spikes, sandwich triplets, front-running bot clusters – apply consistently across EVM chains.
Investigators use cross-chain gas analysis to follow fraud actors who exploit one chain and immediately bridge proceeds to another using gas-optimised bridge transactions. According to Elliptic (2024), 28% of DeFi exploit proceeds were bridged to a second chain within 2 hours of the initial exploit, with bridging transactions paying above-median gas to minimise detection window. Unified cross-chain gas analysis correlates fee patterns across chains to maintain attribution continuity across bridge hops.
AML Compliance and Regulatory Obligations
Gas price anomaly detection feeds directly into AML compliance workflows for regulated exchanges and DeFi protocol operators under UK AML, EU AML, and US BSA frameworks. When exchange transaction monitoring systems detect incoming Ethereum transactions with gas anomaly patterns consistent with post-exploit sweeps, compliance officers are required to apply enhanced due diligence and consider Suspicious Activity Report filing.
ACAMS-certified AML professionals and MLRO officers at Ethereum-active exchanges incorporate gas price analysis into their transaction monitoring rule sets alongside address cluster matching. UK FCA guidance on cryptoasset AML obligations, EU MiCA implementation rules, and US FinCEN guidance on virtual asset service providers all require transaction monitoring proportionate to the risk profile of the exchange’s customer base and transaction volumes. According to TRM Labs (2024), exchanges using gas anomaly-augmented transaction monitoring filed 29% more Suspicious Activity Reports on DeFi-related fraud than those using address matching alone.
Frequently Asked Questions
What is gas price anomaly detection in Ethereum forensics?
Gas price anomaly detection is the forensic analysis of Ethereum transaction fee patterns to identify abnormal behaviour linked to post-exploit fund sweeps, sandwich attacks, front-running bots, and coordinated transaction ordering manipulation. Investigators compare transaction gas prices against network median values, detect spike patterns in post-exploit windows, and use gas price fingerprinting to link transactions across different addresses to the same actor. TRM Labs (2024) found post-exploit transactions paid 8.3x the median gas price on average.
How are sandwich attacks identified through gas analysis?
Sandwich attacks are identified by detecting triplets of transactions – a high-gas buy, a mid-gas victim trade, and a slightly-lower-gas sell – targeting the same token pair within one block on a decentralised exchange. The attacker’s front and back transactions must pay gas prices set at precise gwei offsets from the victim transaction to guarantee correct block ordering. Chainalysis (2024) identified 1.2 million sandwich attack transactions in 2023 using this triplet detection method, totalling $380 million in extracted value.
What is gas price fingerprinting in blockchain forensics?
Gas price fingerprinting links multiple transactions across different addresses to the same actor based on identical or systematically related non-round gas prices paid in the same block windows. When a fraud actor uses bot software to submit many transactions, the software’s gas pricing strategy leaves a consistent signature. Investigators extract this pattern from known fraud transactions and search Ethereum transaction history for matching patterns to attribute previously unidentified transactions to the same actor.
How do post-exploit gas spikes help investigators reconstruct fraud timelines?
Post-exploit gas spikes create a forensic timeline because the spike onset marks when the attacker began moving stolen funds. Investigators map all transactions paying above 5x the median gas price in the 30 minutes following an exploit, clustering them by sender address and CIOH analysis to identify the complete fund movement path. According to TRM Labs (2024), the post-exploit gas spike pattern was present in 91% of confirmed DeFi exploits above $1 million in 2023.
What is front-running in Ethereum and how is it detected?
Front-running is monitoring the Ethereum mempool for large pending trades and submitting a competing transaction with higher gas to execute before the victim, profiting from the price impact. Forensic detection identifies front-running bot transactions by their gas price strategies – paying 4x or more the median gas price, targeting specific DEX token pairs, and reusing the same bot wallet addresses across thousands of attacks. Elliptic (2024) found 78% of front-running events were attributable to just 23 MEV bot wallet clusters.
Does gas anomaly analysis support legal proceedings?
Gas price anomaly evidence supports legal proceedings when presented by court-recognized expert witnesses who can explain the forensic methodology, demonstrate statistical significance of gas spike patterns, and show the attribution chain from gas fingerprinting to identified wallet addresses. UK civil fraud cases and US securities fraud cases have accepted gas anomaly evidence as part of broader blockchain forensics expert reports. Investigators must document the statistical methodology and the attribution chain from gas patterns to identified entities.
How does gas price analysis support AML compliance?
Gas price anomaly detection feeds into AML compliance workflows for exchanges handling Ethereum transactions. When transaction monitoring systems detect incoming transactions with gas patterns consistent with post-exploit sweeps, compliance officers apply enhanced due diligence and consider Suspicious Activity Report filing under UK AML, EU AML, and US BSA requirements. ACAMS-certified compliance programs for crypto exchanges incorporate gas anomaly rules alongside address cluster matching. According to TRM Labs (2024), gas anomaly-augmented monitoring generated 29% more fraud-related SARs than address matching alone.
Does Crypto Trace Labs conduct gas price anomaly investigations?
Crypto Trace Labs conducts gas price anomaly analysis as a component of Ethereum and DeFi fraud investigations, using Chainalysis Reactor, Elliptic Investigator, and TRM Labs platforms for transaction-level gas data and cluster attribution. The team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Gas anomaly evidence is incorporated into court-ready expert reports and AML compliance advisory packages for exchanges and DeFi protocol operators.
Executive Summary
Gas price anomaly detection provides forensic intelligence from Ethereum transaction fee data, identifying post-exploit sweeps, sandwich attacks, front-running bots, and coordinated transaction ordering manipulation through spike analysis, triplet pattern matching, and gas fingerprinting. TRM Labs (2024) found post-exploit transactions paid 8.3x the median gas price. Chainalysis (2024) identified $380 million in sandwich attack value in 2023. Front-running attribution concentrated to 23 MEV bot clusters per Elliptic (2024). Gas anomaly evidence supports UK AML, EU AML, and US BSA Suspicious Activity Report obligations, with gas-augmented monitoring generating 29% more DeFi fraud SARs at instrumented exchanges.
What Should You Do Next?
If you need gas price anomaly analysis for a DeFi exploit investigation, MEV fraud case, or exchange AML compliance review, specialist Ethereum blockchain forensics expertise is essential.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, providing direct exchange contacts for AML co-operation. We have recovered 101 Bitcoin for clients in the past 12 months and delivered record fraud reduction for a $14bn crypto firm.
We offer no upfront charge for non-custodial wallet recoveries. Contact Crypto Trace Labs to discuss your gas price anomaly investigation or AML compliance needs.
People Also Read
- MEV Bot Transaction Patterns: Forensic Analysis of Gas-Optimised Extraction
- Mempool Monitoring for Real-Time Criminal Activity Detection
- Smart Contract Event Log Analysis: Reconstructing On-Chain Attack Sequences
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.




