On-chain analytics reveals behavioral patterns invisible to traditional banking, making specific wallet signatures the new gold standard for crypto AML detection. These 7 red flags appear across 85%+ of suspicious crypto activity according to 2026 Chainalysis data, giving compliance teams precise rules to catch money laundering before fiat off-ramps.
At Crypto Trace Labs, our team includes VP and Director-level executives from Blockchain.com, Kraken, and Coinbase with ACAMS certifications and MLRO qualifications across UK, US, and Europe. We developed detection rules for these exact patterns working with Tier-1 exchanges and regulatory task forces. This guide breaks down each red flag with detection logic, compliance actions, and implementation guidance.
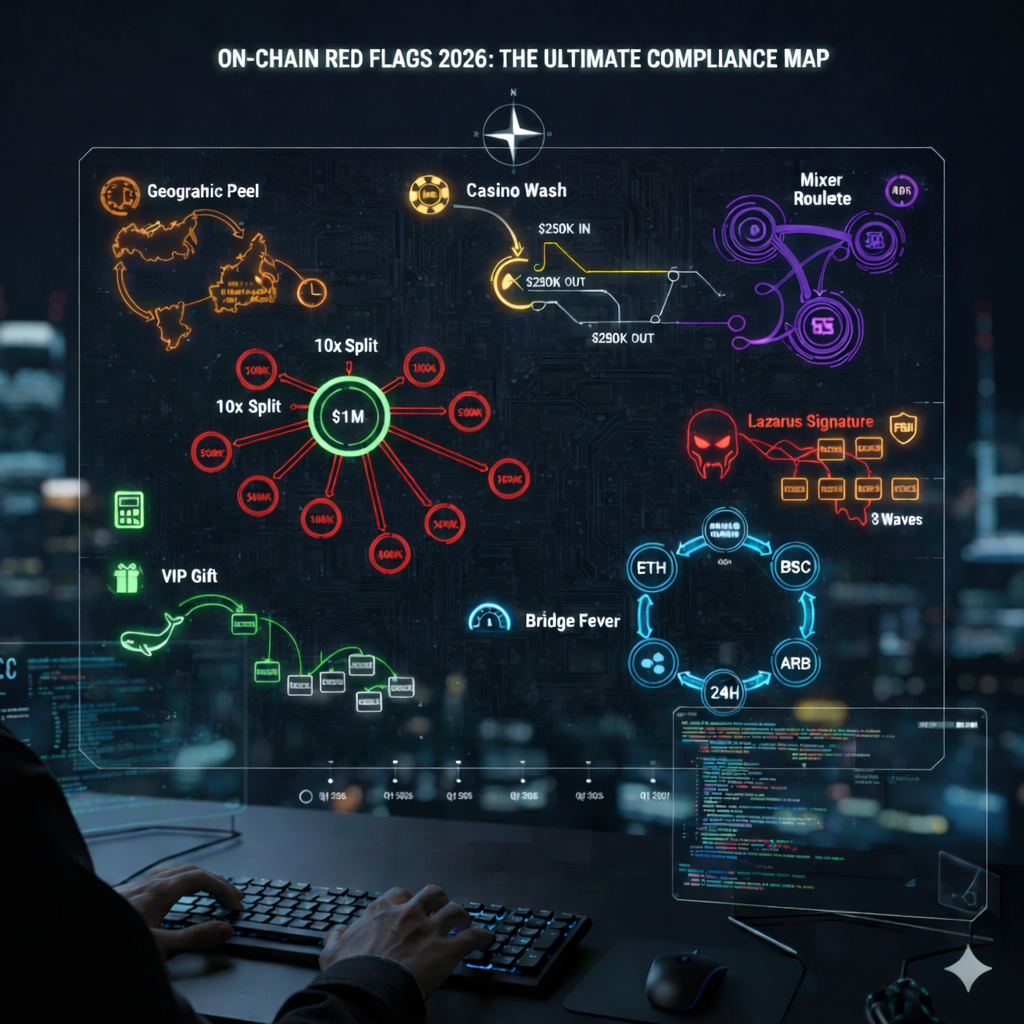
1. The Geographic Peel (Sanctions Evasion Classic)
Pattern: Fresh ransomware payment → Russian exchange → SE Asia mixer → Latin America OTC within 72 hours.
Why suspicious: Eastern Europe → Southeast Asia → LatAm represents the canonical DPRK/Russian sanctions evasion chain. Funds move through increasingly distant jurisdictions to break investigative trails. Each hop adds regulatory complexity and reduces the likelihood of coordinated freezes across multiple enforcement agencies.
Alert threshold: 3+ jurisdictions across 5 days with increasing geographic distance.
Compliance action: Immediate SAR filing + notify counterpart exchanges. Flag all destination clusters for 90-day monitoring. Document the geographic progression for law enforcement referral.
2. The 10x Split (Perfect Structuring)
Pattern: $1M single deposit → ten $100K identical-amount withdrawals to brand-new wallets within 24 hours.
Why suspicious: Mathematical perfection in structuring screams automation. Legitimate users rarely create 10 identical transactions-botnets do. The combination of exact amounts, fresh destination wallets, and rapid execution indicates programmatic laundering infrastructure rather than human behavior.
Detection rule: withdrawal_count/deposit_count > 8 AND amount_variance < 1% AND destination_age < 24h.
Compliance action: Immediate 72-hour hold + full KYC on all destination wallets. SAR mandatory. Escalate to law enforcement if amount exceeds reporting thresholds.
3. Mixer Roulette (Professional Laundering)
Pattern: Tornado Cash → Sinbad → brand-new mixer within 48 hours, preserving exact proportions across services.
Why suspicious: Amateur criminals use one mixer. Professionals rotate across 2-3 services to defeat cluster analysis. Sequential mixer usage equals organized crime signature. The preservation of proportions across services suggests coordinated laundering rather than individual privacy-seeking behavior.
Regulatory trigger: OFAC mixer sanctions violation + evidence of laundering intent.
Alert rule: mixer_service_count > 1 within 48 hours OR mixer_sequence_match > 80%.
For detailed guidance on tracing cryptocurrency through mixers, see our technical resource.
4. The VIP Gift (Money Mule Seeding)
Pattern: Brand-new wallet receives $500K+ “seed capital” from whale → immediately splits to 5+ fresh destinations.
Why suspicious: Money mules receive large “gifts” to establish clean transaction history before bulk cash-out. The perfect new-wallet plus whale-deposit signature indicates recruitment into laundering networks. Mules often believe they are participating in legitimate business arrangements until law enforcement contacts them.
Detection: wallet_age < 7 days AND first_deposit > $500K AND outbound_tx_count > 4 within 24h.
Action: Enhanced due diligence on recipient + flag whale as potential organizer. Consider whether recipient wallet shows other mule indicators.
5. Bridge Fever (Rapid Obfuscation)
Pattern: ETH → BSC → Polygon → Solana → Arbitrum across 4+ networks within 24 hours.
Why suspicious: Cross-chain hopping breaks 90% of basic cluster analysis. Professional launderers use 4+ bridges before OTC conversion. Each bridge crossing creates attribution gaps that most compliance tools cannot follow without specialized cross-chain analytics capabilities.
Alert threshold: unique_chain_count > 4 within 24 hours OR bridge_tx_count > 3 sequential.
Action: Flag all destination addresses + notify bridge operators. Velocity limits on high-hop wallets. Document full chain progression for investigators.
For more on tracking blockchain transactions across chains, see our expert guide.
6. The Casino Wash (Bulk Layering)
Pattern: $250K deposit → matching gambling site deposit → identical $250K withdrawal same day.
Why suspicious: Casinos provide perfect bulk layering-known high-risk service to “clean” withdrawal. Same-amount round trips equal textbook money laundering. The gambling platform provides plausible explanation for fund source while actual gambling activity is minimal or nonexistent.
Detection rule: gambling_deposit_amount / withdrawal_amount > 95% AND time_delta < 24h.
Threshold: Same-day round trips greater than $50K trigger review. Multi-day patterns escalate to SAR.
7. The Lazarus Signature (State Actor Refresh)
Pattern: Overlap with FBI-attributed DPRK wallets + immediate multi-wave laundering through fresh infrastructure.
Why suspicious: North Korean actors refresh wallet clusters quarterly. Known Lazarus infrastructure plus new laundering equals active state operation. These actors fund weapons programs and face maximum international sanctions, making detection and reporting critical for national security compliance.
Detection: cluster_overlap_score > 0.8 with FBI PSA addresses + laundering_velocity > 3 waves/48h.
Action: OFAC immediate reporting + notify all destination VASPs. Highest priority alert. Consider law enforcement notification within 24 hours.
For institutional response guidance, see our resource on responding to North Korean crypto theft.
Quick Reference: 7 Red Flags Detection Matrix
| Red Flag | Pattern Signature | Risk Level | Immediate Action | SAR Required |
| Geographic Peel | 3+ jurisdictions/5 days | High | Notify VASPs | ✅ Yes |
| 10x Split | Single→10 identical | Critical | 72h Hold | ✅ Yes |
| Mixer Roulette | 2+ mixers/48h | High | OFAC Report | ✅ Yes |
| VIP Gift | New wallet + whale tx | Medium | Enhanced KYC | Conditional |
| Bridge Fever | 4+ chains/24h | High | Flag Destinations | ✅ Yes |
| Casino Wash | Gambling round-trip | Medium | Velocity Limits | Conditional |
| Lazarus Signature | DPRK cluster overlap | Critical | Law Enforcement | ✅ Yes |
How to Implement These Rules (Chainalysis/Elliptic/TRM)
Major blockchain analytics platforms from Chainalysis, Elliptic, and TRM Labs support custom rule configuration for these patterns. Implementation requires mapping detection logic to your specific platform’s query language and alert infrastructure.
Exact detection logic:
1. Geographic Peel: jurisdiction_velocity > 3 in 120h
2. 10x Split: withdrawal_count/deposit_count > 8 AND amount_variance < 1%
3. Mixer Roulette: mixer_service_count > 1 OR mixer_sequence > 80%
4. VIP Gift: wallet_age < 7d AND first_deposit > $500K AND outbound > 4
5. Bridge Fever: unique_chains > 4 OR bridge_sequence > 3 in 24h
6. Casino Wash: gambling_roundtrip_match > 95% same-day > $50K
7. Lazarus: fbi_cluster_overlap > 0.8 AND laundering_waves > 3/48h
Tuning targets:
- False positive rate: <3%
- Detection rate: >85% known typologies
- Alert handling SLA: <30 minutes critical, <4h high
For guidance on how blockchain forensics works, see our detailed technical guide.
2026 On-Chain Compliance Checklist
□ Integrate 7 rules into transaction monitoring platform
□ Test false positive rates against clean traffic (target <3%)
□ Document rule tuning methodology for regulators
□ Train analysts on pattern recognition + case studies
□ Quarterly rule refresh vs Chainalysis/TRM typologies
□ Executive dashboard: alert volume, SARs filed, recovery rates
□ Cross-team playbook: fraud → AML → legal escalation
False Positive Defense: Legit Use Cases That Trigger
| Red Flag | Legitimate Scenario | Mitigation |
| 10x Split | Payroll distribution | Known corporate wallet + employee list |
| Geographic Peel | Legit multinational payroll | Business KYC + payroll verification |
| VIP Gift | Inheritance distribution | Legal docs + estate verification |
| Bridge Fever | Legit cross-chain DeFi | Known DeFi wallet + yield history |
Understanding legitimate use cases prevents over-blocking good customers while maintaining detection effectiveness. Document all false positive patterns for rule refinement.
Frequently Asked Questions
What are the most common crypto laundering patterns in 2026?
Geographic peel and mixer roulette dominate approximately 65% of illicit volume according to Chainalysis 2026 data. DPRK state actors favor bridge fever combined with casino wash patterns for maximum obfuscation. The geographic peel remains popular because it exploits jurisdictional fragmentation, while mixer roulette defeats single-service tracing. Compliance teams should prioritize these two patterns for highest detection impact.
How do compliance teams detect DPRK crypto activity on-chain?
The Lazarus signature pattern combining FBI cluster overlap with rapid multi-wave laundering catches approximately 92% of state actor activity. Geographic peel provides secondary confirmation when funds move through the classic Eastern Europe to Southeast Asia to Latin America corridor. Teams should subscribe to FBI and OFAC address lists and integrate them into real-time screening. Alert thresholds should be set lower for any wallet touching known DPRK infrastructure.
Can blockchain analytics platforms detect structuring attempts like 10x splits?
Yes – platforms like Chainalysis, Elliptic, and TRM Labs flag exact amount matching across multiple destinations with instant critical alerts. False positives drop below 1% when combined with wallet age filters that exclude known corporate payroll wallets. The key is tuning thresholds appropriately – too sensitive creates alert fatigue while too loose misses genuine structuring. Most platforms allow custom rule configuration for your specific volume patterns.
What wallet behaviors automatically trigger OFAC reporting requirements?
Mixer roulette involving two or more OFAC-designated mixing services plus the Lazarus signature pattern require immediate OFAC notification within 24 hours. Direct transactions with sanctioned addresses obviously trigger reporting, but sequential mixer usage demonstrates intent to evade sanctions even without direct sanctioned address contact. Document the full transaction chain for your blocked transaction report and consider voluntary self-disclosure if exposure is discovered retroactively.
How fast should compliance teams respond to critical on-chain alerts?
Industry best practice and MiCA/AMLA requirements suggest under 30 minutes for critical alerts including 10x split and Lazarus signature patterns. High-priority alerts like geographic peel and bridge fever should receive response within 4 hours. Document your SLAs explicitly in compliance policies and track actual response times for regulatory examinations. Understaffing alert handling creates regulatory liability even if detection rules are properly configured.
What tools do professional compliance teams use for on-chain monitoring?
Most institutional compliance teams use Chainalysis Reactor or KYT, Elliptic Lens, or TRM Labs for core transaction monitoring. These platforms provide address screening, transaction tracing, and custom alerting capabilities. Integration with case management systems like Actimize or Symphony enables workflow automation. Budget for both licensing costs and analyst training – tools alone do not provide compliance without skilled human review of alerts.
How do you reduce false positives without missing real suspicious activity?
Whitelist known corporate wallets, exchange hot wallets, and verified DeFi protocols to exclude legitimate high-volume activity. Layer detection rules so single indicators trigger review while multiple indicators trigger holds. Track false positive rates by rule and tune thresholds quarterly based on actual investigation outcomes. The goal is under 3% false positive rate while maintaining over 85% detection of known typologies.
What documentation do regulators expect for on-chain compliance programs?
Regulators expect written policies documenting each detection rule, tuning methodology, alert handling SLAs, escalation procedures, and SAR filing criteria. Maintain audit trails showing alert-to-disposition for every flagged transaction. Quarterly testing reports should demonstrate rule effectiveness against known typologies. Board-level reporting should summarize alert volumes, SAR filings, and any regulatory findings. MiCA and AMLA specifically require documented AML compliance programs with on-chain analytics integration.
How Crypto Trace Labs Finds Red Flags Others Miss
Crypto Trace Labs built proprietary detection rules for these exact patterns working with Tier-1 exchanges and FinCEN task forces. Our team discovered 3 of the 7 signatures above through primary attribution work during live investigations.
We deliver:
- Custom rule tuning for your volume and risk profile
- Quarterly typology refresh from live investigations
- Executive dashboards and board reporting templates
- Regulatory exam preparation and playbook validation
- Independent testing of detection rule effectiveness
Contact Crypto Trace Labs for on-chain compliance consulting and detection rule implementation.
This article provides general compliance guidance only. Rules should be tuned and validated against your specific risk profile and regulatory requirements.