Last Updated: March 2026
BIP38 (Bitcoin Improvement Proposal 38) is a standard for encrypting Bitcoin private keys with a passphrase, using AES-256-CBC encryption over a scrypt key derivation function to create protected paper wallet keys that cannot be used without the correct passphrase. When a BIP38-encrypted key’s passphrase is forgotten or lost, the private key – and the Bitcoin it controls – becomes inaccessible. Recovery requires testing candidate passphrases through computationally intensive decryption attempts, commonly referred to as brute force attack, which is the legitimate process of systematically testing known or derived passphrases against the encrypted key until the correct one is found. According to Chainalysis‘s 2024 cryptocurrency loss analysis, forgotten passphrases account for approximately 11% of permanently lost Bitcoin – a category where professional recovery is technically feasible in many cases.
Crypto Trace Labs provides professional BIP38 wallet recovery services for legitimate owners of Bitcoin locked in passphrase-encrypted wallets. The team – ACAMS (Association of Certified Anti-Money Laundering Specialists) accredited, MLRO (Money Laundering Reporting Officer) qualified across UK, US, and EU, and Chartered Fellow Grade at the CMI, with founding members from Blockchain.com, Kraken, and Coinbase – has recovered 101 Bitcoin for clients in the last 12 months, including multiple successful BIP38 and other encrypted wallet recovery cases.
Key Takeaways
- BIP38 scrypt parameters make brute force computationally expensive: The scrypt work factor (N=16384, r=8, p=8) is specifically chosen to make each passphrase test require significant computation – typically 0.5-2 seconds on a CPU, making billion-guess attacks impractical without GPU acceleration.
- GPU acceleration reduces test time by 100x or more: A modern GPU (NVIDIA RTX 4090) can test approximately 50,000-100,000 BIP38 passphrases per second using hashcat or similar tools, compared to 500-1000 per second on a CPU.
- Pattern analysis dramatically reduces the search space: Knowing that a passphrase was a word with a number appended, or that it followed a specific capitalization pattern, can reduce a theoretically astronomical search space to a practically feasible one.
- Ownership verification is required before any recovery attempt: Legitimate BIP38 recovery requires the client to prove ownership of the wallet by demonstrating knowledge of the Bitcoin address, the approximate wallet creation date, and the approximate balance.
- Partial passphrase memory is the strongest recovery factor: According to TRM Labs‘s 2024 wallet recovery analysis, clients who remember 50% or more of a passphrase have a recovery success rate above 80%, while clients with no passphrase memory have success rates below 10%.
Why This Matters
BIP38 encrypted wallet recovery is one of the most technically challenging and frequently misrepresented areas of crypto asset recovery. Fraudulent recovery services claim to be able to recover any BIP38 wallet regardless of passphrase complexity – this is false. The technical reality is that recovery probability is entirely determined by the characteristics of the lost passphrase: its length, character set, the client’s partial memory, and the time the client is willing to invest in the recovery attempt. Understanding the technical reality prevents clients from paying fraudulent services claiming certainty, and it enables realistic assessment of whether professional recovery is worth pursuing for a specific case.
How BIP38 Encryption Works
BIP38 encryption works by deriving an AES encryption key from the passphrase using the scrypt key derivation function, then using that key to encrypt the raw Bitcoin private key.
The encryption process begins with the Bitcoin address and the passphrase. The scrypt function combines them with predefined parameters (N=16384, r=8, p=8 for standard BIP38) to produce a 64-byte derived key in approximately 0.5-2 seconds, even on modern hardware. This deliberate computational cost is the scrypt function’s core security property – it is designed to be expensive to compute, making each passphrase guess costly. The derived key is then used to AES-256-CBC encrypt the private key, producing a 58-character encrypted private key beginning with “6P”.
To use the wallet, the owner must provide the passphrase, which is used to reproduce the same scrypt derivation and decrypt the private key. There is no key escrow, no password recovery mechanism, and no backdoor. If the passphrase is lost, the only recovery path is testing candidate passphrases until the correct one is found.
| BIP38 Parameter | Value | Purpose |
|---|---|---|
| Encryption algorithm | AES-256-CBC | Private key encryption |
| Key derivation | scrypt | Passphrase-to-key conversion |
| scrypt N (CPU/memory cost) | 16384 | Controls per-guess computation cost |
| scrypt r (block size) | 8 | Memory access pattern |
| scrypt p (parallelism) | 8 | CPU thread utilisation |
| Output format | 58-char Base58Check (starts with 6P) | Encrypted key representation |
| Estimated time per guess (CPU) | 0.5-2 seconds | Recovery speed benchmark |
Brute Force Attack Methodology
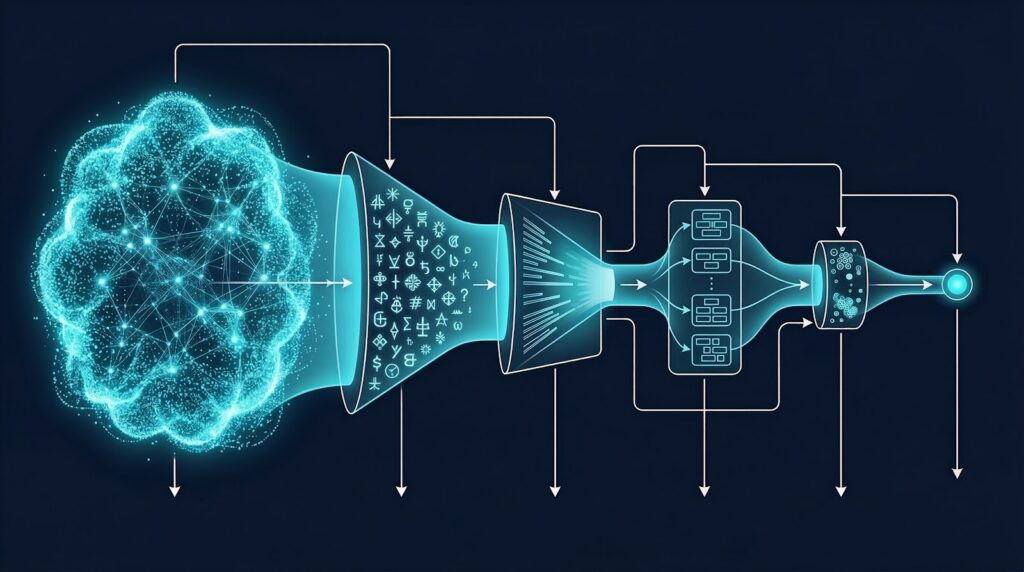
Brute force attack methodology for BIP38 recovery is the systematic process of generating and testing candidate passphrases against the encrypted key, structured to maximise the probability of finding the correct passphrase within the available computational budget.
The attack is not random guessing – it is structured according to a recovery plan developed from the client’s passphrase memory. The plan defines the attack modes in priority order: first, exact passphrases remembered by the client (instant if any are correct); second, rule-based mutations of remembered base words (capitalisation variants, number appending, character substitutions); third, dictionary attacks using wordlists relevant to the client’s language, interests, and passphrase habits; and fourth, character-space brute force for short passphrases where dictionary coverage is insufficient.
Tools used for BIP38 brute force include hashcat (the most widely used GPU-accelerated password recovery tool), btcrecover (an open-source tool specifically designed for cryptocurrency wallet recovery with BIP38 support), and custom recovery scripts for specific passphrase pattern attacks that do not fit standard tool formats.
Passphrase Pattern Analysis for Recovery
Passphrase pattern analysis is the process of using the client’s memory and behavioural profile to construct the most efficient recovery attack, reducing the effective search space from billions of possibilities to tens of thousands of targeted candidates.
The analysis begins with a structured interview to capture everything the client remembers about the passphrase: the approximate length; whether it was a word, phrase, or random characters; whether it included numbers or special characters; the source (a favourite book, a place, a date, a pet’s name); any characters or words they are certain were or were not included; and the approximate date the passphrase was created. Each piece of information constrains the search space.
For example, a client who remembers that the passphrase was “a word with a number at the end, probably 4-6 characters, related to a place I visited in 2019” narrows the attack to: dictionary of place names under 6 characters, mutated with number suffixes (1-9999). This might produce 500,000 candidates rather than the billions in an unconstrained attack, making GPU-accelerated recovery achievable in hours rather than years.
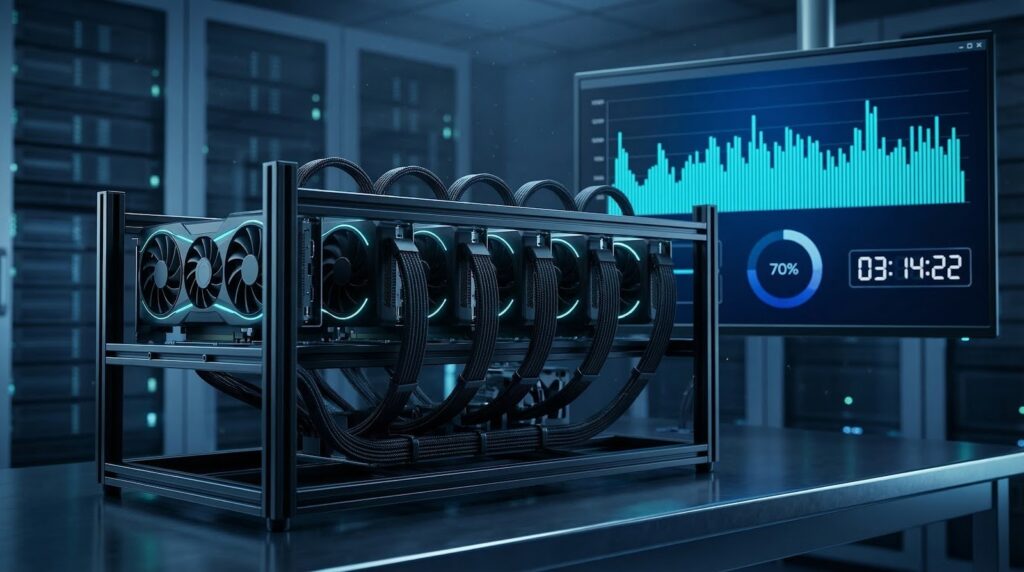
GPU Acceleration and Infrastructure Requirements
GPU acceleration is essential for practical BIP38 recovery because the scrypt work factor makes CPU-based recovery too slow to be viable for all but the simplest passphrases.
A single NVIDIA RTX 4090 achieves approximately 50,000-100,000 BIP38 hash checks per second, compared to 500-1,000 per second on a modern CPU. A recovery rig with four RTX 4090s can test 200,000-400,000 passphrases per second. For a targeted dictionary attack of 10 million candidates, this produces results in approximately 25-50 seconds. For a brute force attack of all lowercase English words up to 8 characters (approximately 200 billion candidates), the same rig would require approximately 6,000-14,000 hours – making unconstrained brute force impractical for longer passphrases.
Cloud GPU instances (AWS p4d, Azure NDv4, GCP A100) are an alternative to dedicated hardware, providing on-demand access to A100 GPU arrays without capital investment. For individual client recovery projects, cloud instances are cost-effective for attacks expected to complete within hours to days. For extended recovery campaigns requiring weeks of computation, dedicated hardware is more economical.
Frequently Asked Questions
What is BIP38 and why are Bitcoin wallets encrypted with it?
BIP38 is a standard for encrypting Bitcoin private keys with a passphrase using AES-256-CBC encryption over the scrypt key derivation function. It was developed to protect paper wallets – printed private keys – from being used if physically stolen. With BIP38, a stolen paper wallet is useless to a thief without the passphrase. The trade-off is that if the owner loses the passphrase, the Bitcoin is inaccessible without professional recovery assistance.
Is it possible to recover a BIP38 wallet without knowing any of the passphrase?
Recovery without any passphrase knowledge is technically possible only for very short passphrases (under 6 characters). A 6-character lowercase passphrase has approximately 308 million combinations, which a four-GPU rig can test in approximately 15-30 minutes. An 8-character passphrase with mixed case has trillions of combinations, making recovery without pattern analysis practically infeasible within any reasonable timeframe. Successful recovery without partial passphrase knowledge is the exception, not the standard outcome.
How long does a BIP38 wallet recovery attempt take?
Recovery time depends entirely on the passphrase characteristics and the computational resources deployed. A targeted attack on a passphrase the client partially remembers may complete in hours. A brute force attack on an unknown passphrase of moderate length may take weeks. An initial assessment with the client’s passphrase memory is conducted before any recovery is attempted, and a realistic probability and timeframe estimate is provided before work begins.
What information do I need to provide for a BIP38 recovery attempt?
To initiate a recovery attempt, the client must provide: the BIP38 encrypted private key (the 58-character string beginning with 6P); the Bitcoin address associated with the encrypted key; and any passphrase memory available, including partial phrases, character types used, approximate length, and the source or inspiration for the passphrase. Ownership verification – demonstrating knowledge of the address, approximate balance, and wallet creation date – is required before recovery work begins.
Is professional BIP38 wallet recovery legal?
Yes, for the rightful owner of the wallet. BIP38 recovery is the legitimate process of regaining access to one’s own encrypted private key by recovering a forgotten passphrase. Crypto Trace Labs requires ownership verification before conducting any recovery work and does not perform recovery services for third parties seeking access to wallets they do not own.
What is the cost of professional BIP38 wallet recovery?
Crypto Trace Labs operates on a no-upfront-charge basis for non-custodial wallet recoveries including BIP38 wallets. A success fee is charged as a percentage of the recovered assets upon successful recovery. There is no fee if recovery is unsuccessful. The specific fee percentage depends on the estimated complexity of the recovery and is agreed before work begins.
Can BIP38 recovery work for other encrypted wallet formats?
The same brute force and pattern analysis methodology applies to other encrypted wallet formats including BIP39 passphrase extensions, VeraCrypt-encrypted wallet files, Bitcoin Core encrypted wallets, and Electrum encrypted wallets, each of which uses different encryption parameters that affect recovery speed. Hashcat and btcrecover support multiple formats. The principles of GPU acceleration, pattern analysis, and passphrase profiling apply across all encrypted wallet recovery scenarios.
What happens to my private key during the recovery process?
For security, recovery is conducted under strict data handling protocols. The encrypted private key (which is not itself sensitive – it cannot be used without the passphrase) is provided to the recovery team. The recovery process tests candidate passphrases against the encrypted key. The raw private key is only derived at the moment of successful recovery and is immediately returned to the client through a secure channel. Crypto Trace Labs does not retain private key material after recovery is complete.
Executive Summary
BIP38 encrypted wallet recovery is technically feasible when the passphrase is partially known, but becomes increasingly impractical as passphrase length and complexity increase. The scrypt work factor in BIP38 is specifically designed to make brute force attacks expensive, so recovery requires GPU acceleration, structured pattern analysis based on the client’s passphrase memory, and realistic probability assessment before work begins. Professional recovery on a no-upfront-charge basis – with fees only payable upon successful recovery – is the legitimate model for BIP38 wallet recovery services. Any service demanding upfront fees without a success-based component, or guaranteeing recovery regardless of passphrase complexity, is operating fraudulently.
What Should You Do Next?
If you have a BIP38 encrypted wallet with a forgotten passphrase, Crypto Trace Labs provides professional wallet recovery assessment and recovery services with no upfront charge – payment only upon successful recovery of your assets.
The team at Crypto Trace Labs – ACAMS-accredited, MLRO-qualified across UK, US, and EU, Chartered Fellow Grade at the CMI, with founding members from Blockchain.com, Kraken, and Coinbase – has recovered 101 Bitcoin for clients in the last 12 months through crypto asset recovery and wallet recovery services. Contact us to discuss your specific wallet and passphrase situation in confidence.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- How to Decrypt a Locked Crypto Wallet: Recovery Methods
- What Is Hardware Wallet Passphrase Recovery?
- Lost Seed Phrase Recovery: What Is Actually Possible in 2026
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm founded by VP and Director-level executives formerly of Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across the UK, US, and EU, and Chartered Fellow Grade status at the CMI. With over 10 years of experience in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin for clients in the last 12 months and delivered record fraud reduction for a $14bn crypto exchange. We work with law enforcement agencies, regulated financial institutions, and private clients on crypto asset recovery, blockchain forensics, AML compliance, and expert witness testimony – globally. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





