Last Updated: March 2026
AML (Anti-Money Laundering) transaction monitoring for crypto platforms is the automated and manual process of reviewing transaction flows to identify patterns consistent with money laundering, terrorist financing, sanctions evasion, and other financial crime. Unlike traditional banking transaction monitoring, crypto AML monitoring must handle pseudonymous addresses, cross-chain asset flows, DeFi protocol interactions, and the absence of correspondent banking relationships that conventional systems rely on for context. According to FATF‘s 2024 Virtual Assets Guidance, the most effective crypto transaction monitoring systems combine deterministic rule engines with machine learning risk scoring and structured human review workflows – and the majority of poorly performing systems fail because they rely on rules alone or machine learning alone, without integrating both.
Crypto Trace Labs designs and audits AML transaction monitoring systems for crypto exchanges, payment processors, and digital asset custodians. Our team – ACAMS (Association of Certified Anti-Money Laundering Specialists) accredited, MLRO (Money Laundering Reporting Officer) qualified across UK, US, and EU, Chartered Fellow Grade at the CMI, with founding members from Blockchain.com, Kraken, and Coinbase – built the fraud reduction strategy for a $14bn crypto exchange and has direct experience of what monitoring architecture performs under regulatory scrutiny.
Key Takeaways
- Rule engines catch known typologies, ML catches novel ones: Rule-based monitoring reliably flags structuring, velocity anomalies, and OFAC-listed addresses. Machine learning identifies unusual patterns not covered by existing rules, reducing blind spots.
- Risk scoring must be explainable: According to the FCA‘s 2024 Financial Crime Guide, transaction monitoring systems whose outputs cannot be explained in plain English to a regulator are treated as inadequate, regardless of their technical sophistication.
- Alert disposition workflows determine real-world effectiveness: The best monitoring engine produces poor results if alert volumes overwhelm analysts or if disposition decisions are not properly documented and auditable.
- Blockchain analytics integration is essential: Standalone rule engines operating on internal transaction data alone, without integration with external blockchain analytics platforms such as Chainalysis or Elliptic, miss significant risk signals visible from the public blockchain.
- Tuning is continuous, not one-time: According to Chainalysis’s 2024 crypto crime report, platforms that tune alert thresholds quarterly produce 40% fewer false positives than those that set rules once at implementation.
Why This Matters
Transaction monitoring is the operational core of AML compliance for crypto platforms. A system that generates too many false positives overwhelms analysts and leads to superficial reviews that miss genuine suspicious activity – known as alert fatigue. A system that generates too few alerts is systemically blind to money laundering and will fail a regulatory examination. The FCA has taken enforcement action against crypto platforms operating monitoring systems that were either not calibrated for the actual risk profile of their customer base or that lacked documented alert disposition procedures. Building an effective system means understanding both the technical architecture and the operational reality of running it at scale under regulatory pressure.
Rule Engine Design for Crypto Monitoring
Rule-based transaction monitoring engines use deterministic logic to flag transactions or account activity that matches predefined patterns associated with financial crime typologies.
For crypto platforms, effective rule categories include: velocity rules (more than X transactions in Y hours, total value exceeding Z in 24 hours); structuring rules (multiple transactions just below reporting thresholds within a defined period); address risk rules (transactions involving OFAC-sanctioned addresses, known darknet market wallets, or high-risk mixer deposits); counterparty geography rules (transactions to or from exchanges in high-risk jurisdictions without equivalent AML standards); and pattern rules (rapid deposit-to-withdrawal with no internal activity, consistent with pass-through layering).
Rules must be calibrated to the platform’s specific customer base. A rule threshold set for a retail exchange will produce an unacceptable false positive rate on a B2B institutional platform with legitimate high-value transaction volumes. Calibration data should be drawn from 90 days of recent transaction history, and thresholds should be reviewed quarterly.
| Rule Category | Example Condition | False Positive Risk | Tuning Parameter |
|---|---|---|---|
| Velocity | >20 txns in 1 hour | High for active traders | Per customer segment |
| Structuring | 3x deposits just below £10k within 24h | Medium | Threshold proximity range |
| OFAC match | Direct interaction with sanctioned address | Low | Confidence threshold |
| Mixer exposure | Funds received from Tornado Cash within 5 hops | Medium | Hop depth limit |
| Rapid transit | Deposit withdrawn within 10 minutes, >£5k | Low for retail | Customer risk tier |
Machine Learning Risk Scoring Architecture
Machine learning risk scoring supplements rule engines by identifying anomalous transaction patterns that do not match any predefined rule but deviate significantly from a customer’s established behavioural baseline.
The standard ML architecture for crypto transaction monitoring uses unsupervised anomaly detection (such as isolation forests or autoencoders) to establish normal behaviour for each customer segment, and supervised classification (gradient boosted trees, neural networks) trained on labelled examples of confirmed suspicious activity to score new transactions. Feature engineering for crypto must include: transaction frequency and value distributions; counterparty address risk scores from external intelligence sources; on-chain behaviour indicators such as mixer exposure, peel chain participation, and privacy coin conversion; and cross-platform indicators where available.
Model outputs must be explainable. SHAP (SHapley Additive exPlanations) values are the current standard for explaining which features drove a given risk score. Regulators and courts increasingly require that when a transaction is flagged by a machine learning model and a SAR is subsequently filed, the MLRO can articulate in plain language why the model scored the transaction as high risk.

Alert Disposition Workflow Requirements
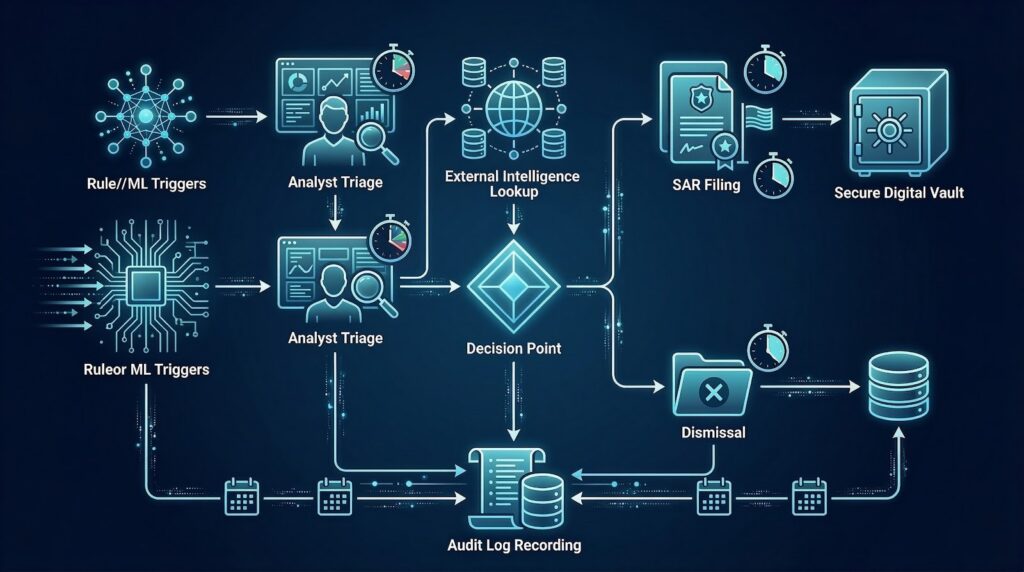
Alert disposition is the process by which compliance analysts review flagged transactions, investigate the context, make a decision (dismiss, escalate, file SAR), and document their reasoning.
An effective disposition workflow must: present the alert in context (full transaction history, KYC profile, previous alerts, external blockchain analytics data); enforce a documented review process with mandatory fields (analyst ID, review timestamp, evidence considered, decision rationale); require supervisor review for escalations above a defined risk threshold; and maintain a complete audit trail that can be presented to a regulator or court. Alert triage queues must be organised by risk score so that high-risk alerts are reviewed first, not on a first-in, first-out basis.
According to TRM Labs‘s 2024 compliance operations report, platforms with structured disposition workflows that include mandatory external intelligence consultation (blockchain analytics lookup before disposition) produce SAR filings with 60% higher conviction rates than platforms that rely on internal data alone.
Integration with External Blockchain Analytics
External blockchain analytics integration means connecting the internal transaction monitoring system to commercial platforms such as Chainalysis Reactor, Elliptic Lens, or Crystal Intelligence to enrich alerts with on-chain intelligence beyond what internal data provides.
The integration should work in two modes: pre-alert enrichment, where every transaction is scored against external risk databases before alert rules are applied (preventing alert generation for transactions that are demonstrably low-risk); and post-alert enrichment, where flagged transactions are automatically queried against external platforms to provide context for analyst review. API integrations with Chainalysis and Elliptic provide real-time address risk scores, exposure analysis (what percentage of funds in a wallet derive from known illicit sources), and counterparty identification.
For platforms that cannot afford commercial blockchain analytics subscriptions for every transaction, a tiered approach is effective: apply external intelligence checks only to transactions above a risk threshold, and use free public blockchain data for lower-risk transactions. This concentrates external intelligence costs where they have the most impact.
Frequently Asked Questions
What is the difference between rule-based and ML-based transaction monitoring?
Rule-based monitoring flags transactions that match predefined conditions, such as transactions to sanctioned addresses or structuring patterns. ML-based monitoring identifies anomalous transactions that deviate from established behavioural baselines without requiring predefined conditions. The most effective systems use both: rules provide high-confidence detection of known typologies while ML catches novel patterns that rules miss. Using only one approach leaves significant blind spots.
How many alerts should a well-tuned system produce per analyst per day?
A well-tuned crypto AML monitoring system should produce 20-40 meaningful alerts per analyst per day – enough to keep analysts occupied with genuine review but not so many that alert fatigue produces superficial decisions. Systems producing more than 100 alerts per analyst per day typically have miscalibrated thresholds and high false positive rates. FCA examinations specifically look at alert-to-SAR conversion rates as a proxy for monitoring effectiveness.
What data sources should be integrated into crypto transaction monitoring?
Effective crypto transaction monitoring should integrate: internal transaction data and KYC records; external blockchain analytics intelligence (Chainalysis, Elliptic, TRM Labs); OFAC and HMT sanctions lists updated in real time; jurisdiction risk ratings (FATF grey and black lists); exchange and counterparty risk classifications; and where available, external financial crime intelligence feeds. The richer the data integrated at alert generation time, the better the context available to analysts.
How should monitoring be calibrated for different customer risk tiers?
Calibration should start with customer segmentation by risk tier – retail users, high-net-worth individuals, and institutional clients have different transaction profiles and different risk indicators. Rule thresholds should be set separately for each tier based on historical transaction data. For retail users, lower thresholds and more sensitive rules are appropriate. For institutional clients with documented legitimate high-volume activity, thresholds should reflect verified business purpose, with enhanced monitoring on new counterparties.
What should be documented in alert disposition records?
Alert disposition records must include: the alert trigger (which rule or ML model generated it), the analyst who reviewed it and when, the evidence consulted (internal data, external blockchain analytics, KYC records), the decision made (dismiss, escalate, file SAR), the rationale for the decision in plain language, and any follow-up actions taken. Records must be retained for at least five years and must be producible to the FCA on request within five business days.
How often should alert thresholds be reviewed?
Alert thresholds should be reviewed at least quarterly, with additional reviews triggered by: significant changes in transaction volumes, new product launches, material changes to the customer base, regulatory guidance updates, or adverse findings in regulatory examinations. Threshold reviews must be documented and approved by the MLRO. Platforms that have not reviewed thresholds in more than 12 months are at elevated regulatory risk.
What are the most common reasons crypto transaction monitoring systems fail regulators?
The most common failures identified in FCA and FinCEN examinations are: alert thresholds not calibrated to actual customer behaviour; no external blockchain analytics integration; insufficient analyst capacity relative to alert volumes; poorly documented disposition decisions that cannot withstand audit; and monitoring coverage gaps for specific asset types or transaction channels. Systems that were effective when implemented but not maintained as the business scaled are also commonly cited.
What is the cost of building versus buying a transaction monitoring system?
Building a custom system typically costs £500,000-£2 million over 18-24 months for a mid-size exchange, with ongoing maintenance costs of £200,000-£500,000 per year. Commercial platforms such as Chainalysis Tx Screening or Elliptic Navigator range from £50,000-£500,000 annually depending on transaction volumes. Most exchanges use a commercial platform as the baseline and build custom components for specific requirements not covered by commercial offerings.
Executive Summary
Effective AML transaction monitoring for crypto platforms requires three integrated components: a rule engine calibrated to the platform’s specific customer base and product mix; a machine learning risk scoring layer that identifies novel patterns with explainable outputs; and structured alert disposition workflows that document every review decision in an auditable format. External blockchain analytics integration – with Chainalysis, Elliptic, or TRM Labs – is not optional for platforms operating under FCA, FinCEN, or MiCA obligations. Systems that rely on a single component, fail to tune thresholds regularly, or lack documented disposition procedures will fail regulatory examination regardless of the sophistication of their underlying technology.
What Should You Do Next?
If your crypto platform’s AML transaction monitoring system is generating excessive false positives, failing to identify suspicious patterns, or lacks the documentation to satisfy an FCA examination, Crypto Trace Labs provides AML compliance consulting and transaction monitoring system design for regulated crypto platforms.
The team at Crypto Trace Labs – ACAMS-accredited, MLRO-qualified across UK, US, and EU, Chartered Fellow Grade at the CMI, with founding members from Blockchain.com, Kraken, and Coinbase who built the fraud reduction framework for a $14bn exchange – provides practical, regulator-ready AML solutions. We offer no upfront charge for non-custodial wallet recoveries. Contact us to discuss your monitoring requirements.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is Cryptocurrency AML Compliance?
- 7 On-Chain Red Flags Every Crypto Compliance Team Must Know in 2026
- When Cryptocurrency Transactions Become Suspicious
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm founded by VP and Director-level executives formerly of Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across the UK, US, and EU, and Chartered Fellow Grade status at the CMI. With over 10 years of experience in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin for clients in the last 12 months and delivered record fraud reduction for a $14bn crypto exchange. We work with law enforcement agencies, regulated financial institutions, and private clients on crypto asset recovery, blockchain forensics, AML compliance, and expert witness testimony – globally. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





