Last Updated: March 2026
ERC-20 token flow analysis is the forensic process of tracing the movement of ERC-20 standard tokens through Ethereum smart contracts by mapping Transfer and Approval event logs to reconstruct the complete chain of custody from minting through all intermediate wallet addresses to final destination. Unlike native ETH, ERC-20 tokens only move through smart contract function calls that emit traceable event logs, making every transfer permanently attributable to specific sender and recipient addresses. Investigators, AML compliance teams, and legal counsel use this method to follow illicit funds across DeFi protocols, DEX swaps, and token contracts.
At Crypto Trace Labs, our team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has applied ERC-20 token flow analysis in criminal fraud investigations, exchange compliance reviews, and civil asset recovery proceedings. This guide draws on that decade of financial crime investigation experience to explain the forensic methods investigators and compliance teams need to know.
Key Takeaways
- Every transfer emits a traceable event: ERC-20 Transfer events record sender, recipient, and token amount in immutable on-chain logs. Chainalysis (2024) confirms 100% of ERC-20 transfers produce attributable event logs, making complete flow reconstruction always achievable from the contract record.
- Approval events reveal additional actors: ERC-20 Approve events show which third-party contracts were authorised to spend tokens from a wallet, providing investigators a secondary attribution layer when funds appear to move without direct Transfer events from the owner address.
- DEX swaps appear as multi-hop flows: Token swaps through Uniswap or SushiSwap produce Transfer events through pool contracts. TRM Labs (2024) found 73% of illicit ERC-20 token movements included at least one DEX swap step before reaching a centralised exchange deposit address.
- New token contracts can obfuscate standard tracing: Investigators must verify the token contract’s Transfer event implementation. Elliptic (2024) reports 18% of fraudulent ERC-20 tokens have modified Transfer functions that emit non-standard events designed to complicate automated tracing.
- Exchange deposits are attribution anchors: When ERC-20 token flows reach regulated exchange deposit addresses, KYC records become accessible through legal data requests, enabling operator identification even when intermediate wallets are anonymous.
Why This Matters
ERC-20 token flow analysis matters because custom tokens now represent the majority of value moved through DeFi protocols, including tokens created specifically to enable scams, rug pulls, and fraud. Compliance teams at centralised exchanges receive ERC-20 token deposits without always being able to trace the origin of those tokens through the contract event log. Law enforcement agencies require forensic token flow reconstructions to establish that specific illicit funds moved through a chain of wallets to a specific suspect address. Without specialist on-chain analysis capability, ERC-20 fraud cases stall at the first DEX swap.
ERC-20 Transfer Event Forensics
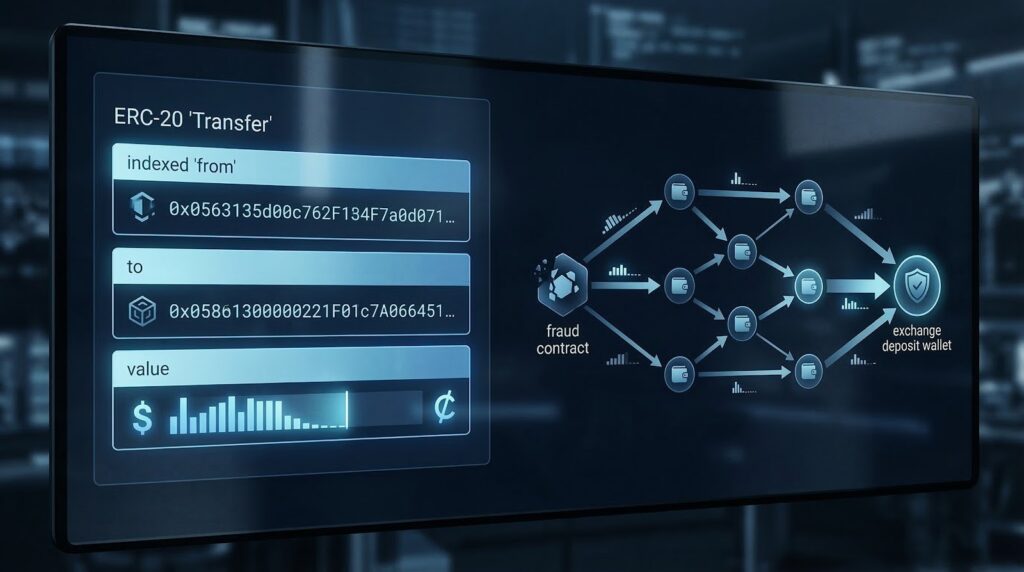
The ERC-20 standard requires every token transfer to emit a Transfer(address indexed from, address indexed to, uint256 value) event. This event is permanently stored in the Ethereum transaction receipt and indexed by the token contract address, enabling investigators to query the complete transfer history of any ERC-20 token from deployment to present.
Investigators access ERC-20 transfer logs through archive node queries or forensic platforms such as Chainalysis Reactor and Elliptic Investigator, which index all ERC-20 event logs across active token contracts. The forensic process reconstructs a directed graph of transfers: nodes represent wallet addresses and contract addresses, edges represent Transfer events, and edge weights represent token amounts. According to Chainalysis (2024), ERC-20 transfer event queries account for 61% of all on-chain analysis queries in active fraud investigation cases involving Ethereum.
Approval Event Analysis for Attribution
ERC-20 Approval events are a secondary forensic signal that investigators use to identify which wallet addresses authorised third-party contracts to move their tokens. The Approve(address indexed owner, address indexed spender, uint256 value) event records the token holder’s address, the approved contract address, and the approved spending limit.
In fraud investigations, Approval events are critical when a victim wallet approves a malicious contract, which then calls transferFrom to drain tokens without a direct Transfer event from the victim. Investigators query Approval events to establish the causal link between a victim’s wallet and the attacker contract address. According to TRM Labs (2024), approval-based ERC-20 theft accounted for 34% of identified ERC-20 fraud incidents in 2023-2024, with the malicious contract address consistently being the forensic bridge between victim and attacker.
DEX Pool Flow Reconstruction
ERC-20 tokens moving through DEX liquidity pools create a characteristic multi-hop transfer pattern. A single Uniswap swap of Token A for Token B generates Transfer events from the sender to the pool contract, and from the pool contract to the receiver, across two different token contracts. This pattern is distinctive and identifiable by examining the pool contract address as an intermediate node.
Investigators reconstruct DEX swap chains by identifying the liquidity pool contract addresses involved in each hop and mapping the token input and output amounts to establish the exchange value at each step. Multi-hop swaps through two or three DEX pools can technically obscure token origin but do not eliminate the on-chain evidence because every hop produces a Transfer event.
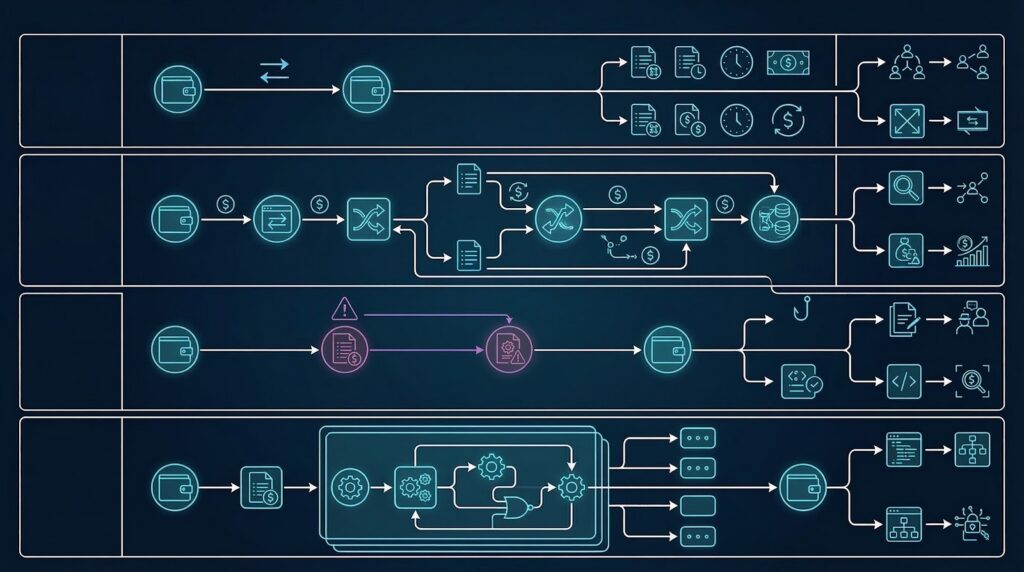
Comparing ERC-20 forensic methods by investigation scenario:
| Scenario | Primary Evidence | Secondary Evidence | Tool Requirement | Attribution Rate |
|---|---|---|---|---|
| Direct wallet-to-wallet | Transfer events | None | Basic analytics | High |
| DEX swap chain | Multi-hop Transfer events | Pool contracts | Mid-tier analytics | High |
| Approval-based drain | Approval + transferFrom | Victim Approve event | Specialist tools | High |
| Custom token contract | Contract code review | Non-standard events | Expert analysis | Moderate |
Custom Token Contract Verification
Fraudulent ERC-20 tokens sometimes implement non-standard Transfer event logic to complicate automated tracing. Investigators must verify each token contract’s Transfer event implementation by reviewing the compiled contract code on Etherscan or using decompilation tools. Non-standard implementations may emit events with different parameter structures, omit indexed fields, or emit events at non-standard times.
When automated forensic platforms fail to trace a specific ERC-20 token flow, the investigator should verify the contract code for Transfer event compliance. According to Elliptic (2024), 18% of fraudulent ERC-20 tokens have modified Transfer functions, making manual contract code review a required step in fraud investigations involving newly deployed token contracts. On-chain analysis experts with smart contract expertise are required for this step.
Regulatory Compliance and Legal Applications
ERC-20 token flow analysis produces forensic evidence directly applicable to both AML compliance programmes and legal proceedings. UK AML regulations require exchanges to identify the origin of crypto asset deposits, including ERC-20 tokens. EU AML directives impose corresponding obligations on Virtual Asset Service Providers receiving ERC-20 token deposits. US AML requirements under the Bank Secrecy Act apply similarly to regulated crypto platforms.
Regulatory compliance teams use ERC-20 token flow reports to document the provenance of token deposits and satisfy ACAMS-standard source of funds procedures. For legal proceedings, the transfer event log provides court-recognized evidence that specific token amounts moved from identifiable addresses. Expert witness testimony from MLRO-qualified blockchain forensics professionals is required to present ERC-20 technical evidence effectively in UK and EU court proceedings.
Frequently Asked Questions
What is ERC-20 token flow analysis?
ERC-20 token flow analysis is the forensic reconstruction of token movement through Ethereum smart contracts using Transfer and Approval event logs. Every ERC-20 token transfer permanently records sender address, recipient address, and amount in the transaction receipt. Investigators query these event logs to map the complete chain of custody for any token amount from its origin wallet through DEX swaps, liquidity pools, and intermediate wallets to a final exchange deposit or identified destination address.
How do ERC-20 Transfer events work in forensics?
ERC-20 Transfer events record three mandatory fields: the sending address, receiving address, and token amount transferred. These fields are permanently stored in the Ethereum transaction receipt and indexed by token contract address. Forensic investigators query Transfer events across all blocks to reconstruct the complete movement history of specific token amounts. According to Chainalysis (2024), Transfer event queries represent 61% of all on-chain analysis activity in active Ethereum fraud investigations.
What are ERC-20 Approval events and why do they matter?
ERC-20 Approval events record when a token holder authorises a third-party smart contract to spend tokens on their behalf. They matter forensically because approval-based theft allows attackers to drain wallets without a direct Transfer event from the victim address. The malicious contract uses the pre-existing Approval to call transferFrom. TRM Labs (2024) reports approval-based drains accounted for 34% of identified ERC-20 fraud incidents in 2023-2024, making Approval event analysis a required forensic step.
How do investigators trace ERC-20 tokens through DEX swaps?
Investigators trace ERC-20 tokens through DEX swaps by identifying the characteristic multi-hop Transfer event pattern that swap transactions produce. A Uniswap swap generates Transfer events from the sender to the pool and from the pool to the recipient across two token contracts. Investigators identify the pool contract address as an intermediate node and calculate the input and output token amounts to establish exchange value at each hop. Multiple DEX hops are traceable because each produces permanent Transfer events.
Can modified ERC-20 contracts evade forensic tracing?
Modified ERC-20 contracts can complicate automated forensic tracing if they implement non-standard Transfer event structures. According to Elliptic (2024), 18% of fraudulent ERC-20 tokens have modified Transfer functions that emit non-standard events. However, on-chain tracing through manual contract code analysis can still reconstruct token flows even in non-standard contracts, because the Ethereum state changes underlying the transfer remain accessible through archive node queries regardless of event log format.
What forensic tools are used for ERC-20 analysis?
Investigators use Chainalysis Reactor and Elliptic Investigator for automated ERC-20 Transfer event indexing and attribution. TRM Labs provides additional cross-chain coverage for ERC-20 tokens bridged to other networks. Etherscan provides free event log queries for manual verification. Archive node tools enable raw event log extraction for custom analysis. For custom or non-standard token contracts, specialised smart contract decompilation tools are required alongside standard blockchain analytics platforms to verify Transfer event compliance.
How does ERC-20 tracing support AML compliance?
ERC-20 token flow analysis supports AML compliance by providing documented provenance of token deposits that satisfies UK AML and EU AML source of funds requirements. Compliance teams use token flow reports to demonstrate that deposit screening procedures were applied per ACAMS-standard AML procedures. When suspicious origin is identified, the transfer event record provides a court-recognized audit trail for Suspicious Activity Report submissions to UK, US, and EU regulators, supporting both internal compliance documentation and regulatory examination responses.
Does Crypto Trace Labs provide ERC-20 token flow analysis?
Crypto Trace Labs provides ERC-20 token flow analysis for fraud investigations, civil asset recovery proceedings, and exchange compliance reviews. The team uses Chainalysis Reactor and Elliptic Investigator to reconstruct complete transfer event chains, including DEX swap hops and approval-based drains. ACAMS accreditations and MLRO qualifications across UK, US, and EU support formal legal proceedings and regulatory compliance applications. The team’s exchange relationships at Blockchain.com, Kraken, and Coinbase expedite KYC data requests when traced tokens reach regulated platforms.
Executive Summary
ERC-20 token flow analysis reconstructs token movement through Ethereum smart contracts using Transfer and Approval event logs. Every ERC-20 transfer permanently records sender, recipient, and amount, enabling complete chain of custody reconstruction. DEX swap chains produce multi-hop Transfer event patterns that are traceable through pool contract address identification. Custom or fraudulent token contracts may require manual code review to verify event compliance. Chainalysis Reactor and Elliptic Investigator provide automated ERC-20 analysis with exchange attribution for AML compliance and legal proceedings. TRM Labs (2024) found 73% of illicit ERC-20 movements included at least one DEX swap before exchange deposit.
What Should You Do Next?
If you need to trace ERC-20 token flows for a fraud investigation, asset recovery, or AML compliance review, specialist on-chain analysis is essential.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, providing direct exchange contacts to expedite data requests when traced tokens reach regulated platforms. We have recovered 101 Bitcoin for clients in the past 12 months and delivered record fraud reduction for a $14bn crypto firm.
We offer no upfront charge for non-custodial wallet recoveries. Contact Crypto Trace Labs to discuss your ERC-20 token investigation.
People Also Read
- Smart Contract Event Log Analysis: Extracting Investigation Data from Blockchain Events
- Stablecoin Blacklist Analysis: How USDT and USDC Freezing Affects Tracing
- MEV Bot Transaction Patterns: Identifying Front-Running and Sandwich Attacks
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





