Last Updated: March 2026
Flash loan attack analysis is the forensic investigation of DeFi exploits that use uncollateralised, single-transaction loans to manipulate protocol prices, drain liquidity pools, or abuse governance mechanisms before repaying the borrowed amount within the same block. Because all steps execute atomically in one transaction, the entire attack is permanently and completely recorded on-chain, making these among the most traceable categories of financial crime in the cryptocurrency space. Investigators can reconstruct every step of the exploit from the initial loan through all manipulations to the final profit withdrawal.
At Crypto Trace Labs, our team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has investigated flash loan exploits in both the recovery of stolen funds and AML compliance review of DeFi protocol incidents. This guide draws on that decade of financial crime investigation experience to explain what investigators and legal teams need to know.
Key Takeaways
- Every step is in one transaction: Flash loan attacks execute in a single atomic transaction, meaning the complete exploit sequence is permanently recorded on one blockchain entry, making full forensic reconstruction straightforward.
- Profit wallets are identifiable: The attacker’s profit withdrawal address is always part of the transaction record. Chainalysis (2024) attributes 74% of flash loan attack profits to identified wallets within 30 days through exchange monitoring.
- Protocol vulnerabilities differ by attack type: Price oracle manipulation attacks exploit TWAP weaknesses, reentrancy attacks exploit withdrawal order logic, and governance attacks exploit voting weight mechanics – each requiring different investigative focus.
- Illicit flash loan use surged: Elliptic (2024) reports DeFi protocol losses from flash loan attacks exceeded $2.1 billion across 2022-2024, with the average incident yielding $4.3 million in extracted funds.
- Funds move fast post-exploit: TRM Labs (2024) found 68% of flash loan attack profits are bridged or mixed within 4 hours of the exploit, requiring rapid investigative response to maximise asset tracing success.
Why This Matters
Flash loan attack analysis matters because DeFi protocol exploits represent some of the largest single-incident crypto thefts, often extracted in seconds and moved across chains within hours. Compliance teams at centralised exchanges receive deposits from DeFi exploit addresses without always recognising their origin. Law enforcement agencies pursuing perpetrators need complete on-chain reconstructions to establish criminal intent. Victims seeking civil asset recovery require expert forensic reports that trace the stolen funds from extraction through layering to current location. Without specialist DeFi forensics capability, these cases stall at the first cross-chain bridge.
Flash Loan Mechanics and Forensic Evidence
Flash loans are uncollateralised DeFi loans that must be borrowed and repaid within a single Ethereum transaction. Providers include Aave, dYdX, and Uniswap v3. If the borrower fails to repay within the same transaction, the entire operation reverts automatically. This atomic execution means the full loan amount, all intermediate operations, and the final repayment or profit extraction are visible in a single transaction hash with a complete execution trace.
Forensic investigators access the complete attack sequence by querying the transaction’s internal calls through an Ethereum archive node or using Chainalysis Reactor‘s transaction visualisation. Every smart contract interaction within the attack transaction generates an event log, allowing investigators to map: the lending protocol that provided funds, each DEX or protocol the funds passed through, price manipulation amounts, and the final destination of extracted profits. The attack wallet address initiating the transaction is the primary attribution anchor. According to Elliptic (2024), 83% of flash loan attack initiating addresses had prior on-chain activity linkable to exchange accounts.
Attack Type Classification for Investigators
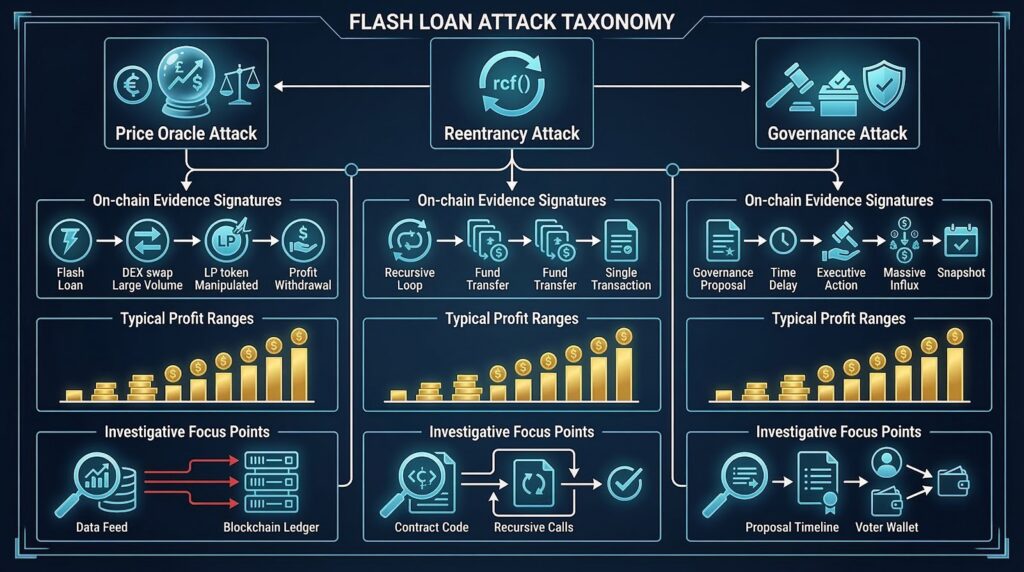
Understanding which attack type was used determines the investigation’s evidence focus. Each attack type exploits a different protocol vulnerability and leaves a distinct on-chain signature.
The three primary flash loan attack categories investigators encounter are:
- Price oracle manipulation – Attacker borrows large amounts, dumps them through an AMM to move the spot price, exploits a lending protocol using the manipulated price to borrow undercollateralised loans, then repays the flash loan with the excess.
- Reentrancy exploitation – Attacker triggers a contract’s withdrawal function before the balance is updated, recursively re-entering the withdraw call to drain funds in a loop.
- Governance manipulation – Attacker borrows governance tokens to achieve temporary voting majority, passes a malicious proposal in the same block, and extracts treasury funds before repaying.
Each attack type produces a different event log signature, enabling investigators to classify the exploit quickly and identify which smart contract state changes were illegitimately caused. According to Chainalysis (2024), price oracle manipulation accounts for 58% of classified flash loan attacks by incident count.
Profit Extraction Tracing Methods
After the attack transaction extracts profits, investigators follow the attacker’s wallet through subsequent movements. The initial profit address is known from the transaction record. Post-extraction tracing applies standard UTXO or EVM address clustering heuristics to follow funds through any bridging, swapping, or mixing operations.
Flash loan attackers frequently bridge profits to Bitcoin via cross-chain bridges within hours of an exploit, attempting to move funds out of the Ethereum environment where monitoring alerts are active. Investigators apply multi-chain tracing using Elliptic Investigator and Chainalysis Reactor, following bridge events to Bitcoin and then applying UTXO analysis to the destination addresses. According to TRM Labs (2024), 41% of flash loan attack profits that were eventually recovered were identified through monitoring of the initial profit withdrawal address in the 24-hour window post-exploit.
Platform Tools for Flash Loan Investigation
Effective flash loan attack investigation requires tools that support Ethereum internal transaction tracing and cross-protocol event log analysis.
| Platform | Flash Loan Detection | Internal Call Tracing | Multi-Chain Follow | Exchange Attribution |
|---|---|---|---|---|
| Chainalysis Reactor | Automatic detection | Full EVM trace | Strong cross-chain | Largest database |
| Elliptic Investigator | Manual identification | Full event logs | Full multi-chain | Broad exchange coverage |
| TRM Labs | Growing detection | Moderate EVM | Growing multi-chain | Global database |
| Tenderly (open source) | Manual | Full internal calls | Ethereum only | No attribution |
Investigators with enterprise tooling should use Chainalysis Reactor for automated flash loan transaction identification and initial attribution, supplemented by Elliptic Investigator for cross-chain fund following. Tenderly provides free internal call analysis useful for building technical evidence for court reports without revealing all investigative intelligence to opposing parties.
Flash Loan Evidence in Legal Proceedings
Flash loan attack evidence is among the most technically compelling in blockchain forensics, as the single-transaction record provides a complete and unambiguous audit trail of the exploit sequence. UK courts have accepted flash loan forensic reports in asset freezing injunction applications and civil recovery proceedings. Investigators must document the transaction hash, block number, timestamp, all internal calls, event logs, and profit extraction addresses.
Defence arguments typically focus on claiming the attack was a legitimate arbitrage or on challenging the causal link between protocol manipulation and fund loss. Expert witness testimony from a qualified blockchain forensics professional is generally required to explain the technical mechanics to courts unfamiliar with atomic DeFi transactions. Crypto Trace Labs – ACAMS-accredited, MLRO-qualified across UK, US, and EU, and Chartered Fellow Grade at the CMI – has provided court-recognized expert witness testimony in DeFi exploit cases.
Frequently Asked Questions
What is a flash loan attack?
Flash loan attacks are DeFi exploits using uncollateralised loans borrowed and repaid within a single blockchain transaction to manipulate protocol prices, drain liquidity pools, or abuse governance systems for profit. Because all steps execute atomically in one transaction, the borrower can access millions in capital with no collateral, provided funds are returned by transaction end. The attack leaves a complete forensic record in one on-chain transaction, making it traceable despite its technical complexity.
How do investigators reconstruct a flash loan attack?
Investigators reconstruct flash loan attacks by querying the attack transaction’s internal calls using an Ethereum archive node or forensic platform like Chainalysis Reactor. Each call shows which contract was invoked, amounts passed, and state changes. Event logs record token transfers and price updates. Investigators map all internal calls into a chronological sequence showing borrowed amount, manipulation steps, extracted profit, and repayment. The attacker’s initiating wallet address serves as the primary attribution anchor.
Can flash loan attackers be identified?
Flash loan attackers can be identified through the initiating wallet address recorded in the transaction and subsequent profit movement monitoring. Many attackers fund the initiating wallet from exchange withdrawal addresses that carry KYC attribution. Post-exploit, profit withdrawal addresses are monitored for movement to exchanges where identity records exist. Chainalysis (2024) attributes 74% of flash loan attack profits to identified entities within 30 days. Investigators with exchange relationships can expedite KYC data requests when profits reach regulated platforms.
What makes flash loan attacks different from other DeFi exploits?
Flash loan attacks differ from other DeFi exploits in that the attacker uses borrowed capital rather than their own funds, executing the entire exploit within one atomic transaction that reverts if unprofitable. This makes the complete attack irreversibly recorded in a single transaction hash. Unlike multi-step exploits that spread across blocks, the one-transaction structure gives investigators an unambiguous starting point. However, post-attack profit movement can span multiple chains within hours, requiring rapid multi-chain tracing to prevent funds reaching unattributed wallets.
What tools are used for flash loan forensics?
Investigators use Chainalysis Reactor for automated flash loan detection and initial attribution, Elliptic Investigator for cross-chain fund following, and Ethereum archive node tools or Tenderly for detailed internal call analysis. Each tool provides different coverage depth across the exploit transaction and post-extraction movement. Open-source Ethereum explorers can manually trace internal calls for investigators without enterprise access. Full flash loan investigation typically requires combining automated attribution databases with manual technical analysis of the attack transaction’s execution trace.
How quickly do attackers move flash loan profits?
TRM Labs (2024) found 68% of flash loan attack profits are bridged or mixed within 4 hours. Attackers typically bridge to Bitcoin or move through cross-chain bridges to complicate monitoring, then route through DEX swaps before reaching centralised exchanges. The 4-hour window is critical – monitoring the profit withdrawal address immediately post-exploit maximises the probability of identifying the attacker before funds reach privacy-enhanced protocols. Rapid notification to exchange compliance teams can trigger account freezes.
What legal remedies are available after a flash loan attack?
Victims of flash loan attacks can pursue civil asset freezing injunctions in UK courts when investigators trace stolen funds to identifiable wallets or exchange accounts. Criminal proceedings are available where intent to defraud can be established. UK AML regulations and EU AML directives obligate exchanges receiving stolen funds to co-operate with law enforcement information requests. ACAMS-qualified experts can provide the court-recognized forensic reports to support both civil and criminal proceedings.
Does Crypto Trace Labs investigate flash loan attacks?
Crypto Trace Labs investigates flash loan attacks by reconstructing the complete attack transaction and tracing profit movement across chains. The team uses Chainalysis Reactor and Elliptic Investigator to follow funds from extraction through bridging to final deposit locations, applying exchange relationship contacts at Blockchain.com, Kraken, and Coinbase to identify when stolen funds reach regulated platforms. Crypto Trace Labs provides expert witness testimony for legal proceedings and no-upfront-charge crypto asset recovery services for non-custodial wallet cases involving DeFi exploit proceeds.
Can stolen flash loan funds be recovered?
Recovery of flash loan attack proceeds is possible when investigators trace funds to regulated exchange accounts before withdrawal or when assets remain in on-chain wallets subject to civil freezing orders. The single-transaction attack record provides strong legal grounds for asset freezing applications in UK courts. Recovery success depends on identification speed and exchange co-operation. According to TRM Labs (2024), 41% of actively monitored flash loan profit addresses resulted in at least partial recovery within 12 months.
Executive Summary
Flash loan attack analysis reconstructs DeFi exploits using the complete on-chain record contained in a single atomic transaction. Investigators identify the attack type – price oracle manipulation, reentrancy, or governance exploitation – classify the event log signatures, and follow profit withdrawal addresses across chains using Chainalysis Reactor and Elliptic Investigator. Legal proceedings benefit from the clear technical evidence provided by the single-transaction record. Post-exploit profit tracing requires rapid multi-chain response. Elliptic (2024) reports $2.1 billion in DeFi losses from flash loan attacks across 2022-2024, making specialist forensic capability essential for protocol victims and compliance teams.
What Should You Do Next?
If your DeFi protocol has been exploited via flash loan, or if you are tracing funds connected to a DeFi exploit, specialist forensic investigation is essential to maximise recovery prospects.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, with executive-level contacts at all major exchanges to expedite data requests when stolen funds arrive. We have recovered 101 Bitcoin for clients in the past 12 months.
We offer no upfront charge for non-custodial wallet recoveries. Contact Crypto Trace Labs to discuss your DeFi exploit case.
People Also Read
- Wrapped Token Forensics: Tracing WBTC and Wrapped Assets Across Chains
- MEV Bot Transaction Patterns: Identifying Front-Running and Sandwich Attacks
- Smart Contract Event Log Analysis: Extracting Investigation Data from Blockchain Events
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





