Last Updated: February 2026
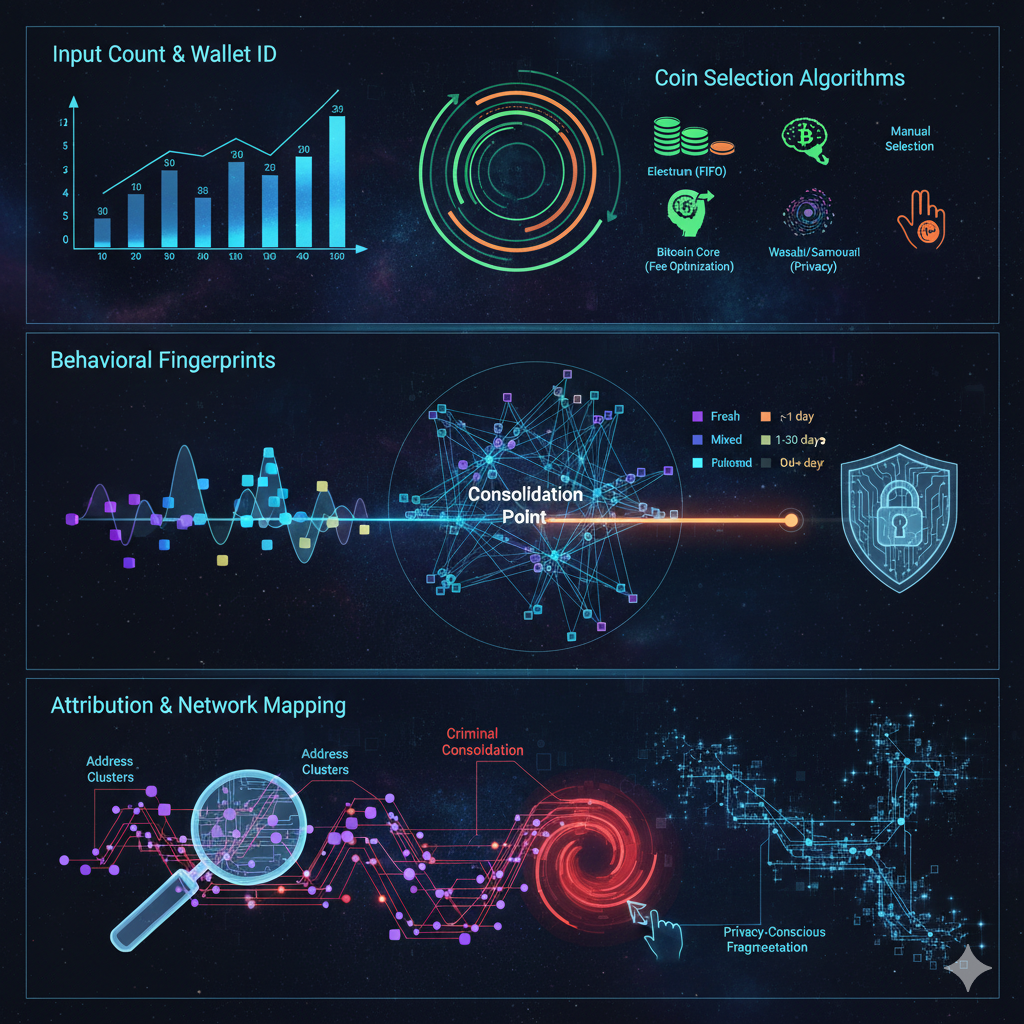
Transaction input pattern analysis examines which unspent transaction outputs (UTXOs) users select when creating Bitcoin and cryptocurrency transactions, revealing wallet ownership, operational sophistication, and behavioral fingerprints that enable address clustering and entity attribution. Investigators analyze input selection methodologies including coin selection algorithms wallet software implements, UTXO consolidation behaviors indicating operational priorities, privacy-consciousness signals through strategic UTXO management, and temporal patterns revealing automated versus manual operations. These patterns enable attribution because different wallet software employs distinctive coin selection strategies, criminal operations exhibit systematic UTXO consolidation revealing network structures, and privacy-focused users demonstrate characteristic behaviors attempting to minimize transaction graph linkages.
At Crypto Trace Labs, our team analyzes transaction input patterns across hundreds of blockchain forensics and cryptocurrency investigation cases. This guide draws on that decade of on-chain analysis experience to explain input pattern analysis, attribution methodologies, and investigative applications.
Key Takeaways
- Common input heuristic provides foundational clustering – addresses spending together in single transactions indicate common ownership with 85-95% confidence in standard cases
- Wallet software creates distinctive selection patterns – Electrum prioritizes oldest coins, Bitcoin Core optimizes for fee efficiency, Wasabi implements privacy-focused selection creating identifiable signatures
- UTXO consolidation reveals network structures – criminals systematically consolidating dozens of addresses expose wallet infrastructure and operational control
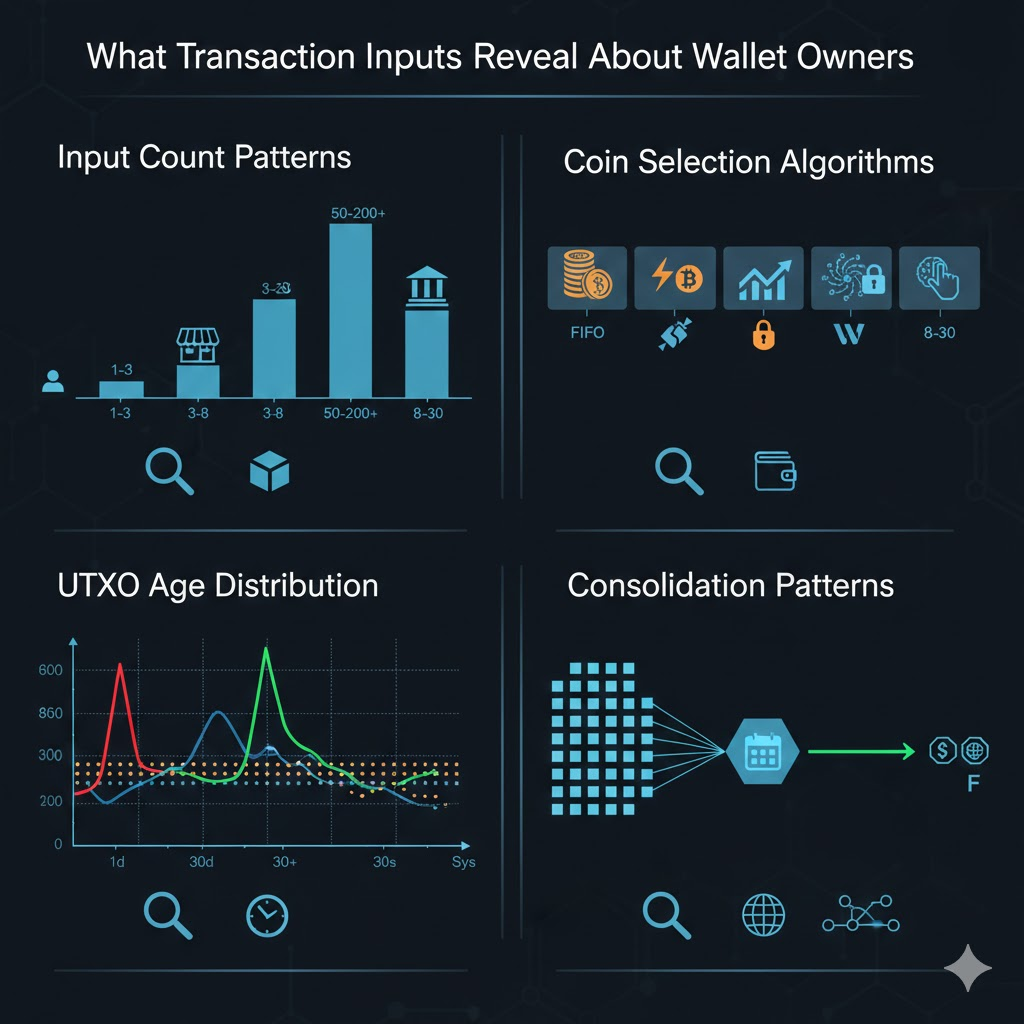
- Input count analysis distinguishes entity types – exchanges batch withdrawals using 100+ inputs, individuals average 1-3 inputs, mixing services show characteristic fragmentation patterns
- Temporal input selection patterns expose automation – addresses selecting UTXOs with microsecond precision or executing consolidations at identical hourly intervals prove bot operation
- Privacy-conscious behaviors create counter-signatures – intentional UTXO fragmentation, coin control implementation, and CoinJoin participation paradoxically enable privacy-focused user identification
What Information Do Transaction Inputs Reveal?
Bitcoin’s UTXO model requires transactions to explicitly select which previous outputs to spend. Unlike account-based systems where balances automatically deduct, Bitcoin users must choose specific UTXOs. This selection process creates behavioral fingerprints revealing operational characteristics and user sophistication.
The common input ownership heuristic forms blockchain forensics’ foundational clustering method – addresses spending together in single transactions likely belong to the same entity. When Address A and Address B both contribute inputs, investigators attribute both to common ownership. This heuristic achieves 85-95% accuracy in standard cases.
Wallet software developers implement proprietary coin selection algorithms creating distinctive patterns. Some prioritize spending oldest coins first (FIFO), others optimize for lowest fees, while privacy implementations employ randomization or manual control. These algorithmic differences generate detectable signatures enabling wallet software identification.
UTXO consolidation behaviors reveal operational priorities. Exchanges consolidate customer deposits for efficient management, criminals consolidate fragmented proceeds before cash-out, and privacy users strategically consolidate or fragment based on anonymity requirements. The consolidation timing and patterns expose entity types.
How Do Investigators Apply Input Pattern Analysis?
Comparison Table: Input Pattern Analysis Methodologies
| Analysis Method | Technical Approach | Attribution Accuracy | Computational Cost | Privacy Evasion Difficulty | Best Application |
| Common Input Clustering | Group addresses spending together in single transactions | 85-95% standard cases | Low | Medium (CoinJoin defeats) | Foundational address clustering |
| Coin Selection Fingerprinting | Identify wallet software through UTXO selection algorithms | 75-85% | Low | High | Wallet implementation attribution |
| UTXO Age Analysis | Examine temporal patterns in selected UTXO ages | 70-80% | Low | Medium | Behavioral classification, automation detection |
| Consolidation Pattern Detection | Identify systematic UTXO consolidation across address groups | 88-94% | Medium | Very High | Criminal network mapping, exchange identification |
| Input Count Distribution | Classify entities by typical transaction input counts | 80-88% | Low | Medium | Entity type classification |
| Temporal Input Correlation | Detect coordinated input selection across addresses | 85-92% | Medium | High | Sybil network detection, bot operations |
Common input clustering algorithms process blockchain data identifying every transaction with multiple inputs, then grouping contributing addresses into clusters representing probable single entities. Platforms like Chainalysis and Elliptic maintain continuously updated cluster databases containing millions of address groups attributed through this methodology.
Coin selection fingerprinting compares observed input patterns against known wallet software algorithms. Investigators maintain signature databases documenting how Electrum, Bitcoin Core, Wasabi, Ledger Live, and other popular wallets select UTXOs. When analyzing unknown addresses, pattern matching against these signatures identifies likely wallet implementations enabling targeted investigation strategies.
UTXO age analysis examines the temporal characteristics of selected inputs. Addresses consistently spending the oldest available UTXOs indicate FIFO strategy implementation. Addresses selecting fresh UTXOs (created within days) suggest rapid cycling characteristic of mixing services or criminal operations. Systematic age patterns reveal automation while highly variable ages indicate manual selection or sophisticated privacy practices.
Consolidation pattern detection identifies addresses systematically combining numerous UTXOs into fewer outputs. When 50 addresses all send their UTXOs to common consolidation addresses within weekly time windows, investigators recognize coordinated network control. This pattern enables criminal infrastructure mapping and exchange hot wallet identification.
What Patterns Distinguish Different User Types?
Numbered Listicle: 6 Input Patterns That Reveal User Identity
1. Exchange Hot Wallet Batch Withdrawal Signatures
Cryptocurrency exchanges process customer withdrawals through batch transactions consolidating dozens of requests into single on-chain transactions. These exhibit distinctive patterns – 50-200+ inputs each representing different customer withdrawals, executed at regular intervals, with varied UTXO ages reflecting diverse deposit histories. Investigators identify exchange hot wallets through these batch patterns, enabling transaction tracking for KYC data requests.
2. Criminal UTXO Consolidation Before Cash-Out
Money laundering operations fragment stolen funds across hundreds of addresses during layering, then systematically consolidate before cash-out attempts. This creates distinctive patterns – previously unrelated addresses suddenly contribute inputs to common consolidation transactions within 24-72 hour windows, with consolidated amounts sent to exchange deposits. The consolidation phase provides investigators’ best attribution opportunity.
3. Privacy Wallet Coin Control Implementations
Privacy-focused users employing wallets with manual coin control exhibit distinctive selection patterns. They strategically select specific UTXOs avoiding address linkage – spending from single addresses rather than combining multiple, deliberately fragmenting UTXOs, and timing selections to minimize correlation. These intentional patterns paradoxically create signatures identifying privacy-conscious users.
4. Automated Bot Systematic UTXO Management
Trading bots and algorithmic operations exhibit mechanical UTXO selection impossible through manual operation. Bots systematically spend UTXOs in perfect sequential order, execute consolidations at precise time intervals, and demonstrate zero deviation from programmed strategies across hundreds of transactions. These precision patterns enable bot identification with 90%+ confidence.
5. Individual User Natural Behavioral Variance
Individual users exhibit high variance reflecting inconsistent software usage and manual decision-making. Personal wallets show 1-3 inputs typically, UTXO age selections varying widely based on urgency, occasional consolidations when accumulating excessive UTXOs, and behavioral changes over time. This natural variance creates baselines against which systematic operations appear anomalous.
6. Mixing Service Input Fragmentation Characteristics
Cryptocurrency mixing services exhibit characteristic patterns designed to obscure trails. CoinJoin implementations combine inputs from 8-100+ unrelated users, input counts varying between rounds, input amounts showing coordination (identical values enabling equal-output CoinJoin), and temporal clustering as participants synchronize. While breaking individual attribution chains, mixer service addresses create identifiable patterns.
How Does Input Analysis Enable Address Clustering?
The common input heuristic establishes transitive clustering relationships across multiple transactions. When Transaction 1 combines Addresses A and B, investigators cluster A+B. When Transaction 2 combines B and C, investigators extend to A+B+C. This transitive clustering expands across hundreds of transactions revealing entire wallet infrastructures.
Change address detection complements input clustering by identifying which outputs return to senders versus payments. The change address joins the input cluster, expanding attribution even when never appearing as transaction input.
UTXO consolidation analysis identifies systematic movements revealing network control. When dozens of addresses all consolidate UTXOs to common destinations, investigators recognize coordinated ownership despite limited direct transaction relationships.

Temporal correlation analysis identifies coordinated input selection across addresses lacking direct transactions. When Address Group A consistently selects inputs within 5-minute windows of Group B across weeks, investigators recognize coordination suggesting common control.
Cross-validation through multiple methods increases attribution confidence. When input clustering, coin selection fingerprinting, and UTXO age analysis all suggest common ownership, converging evidence provides high-confidence attribution for legal proceedings or recovery actions.
What Privacy Techniques Complicate Input Analysis?
CoinJoin collaborative transactions deliberately violate common input ownership assumptions by combining inputs from multiple unrelated participants. When 50 users contribute inputs, investigators cannot determine which belong to single entities. This breaks attribution chains requiring analysts to rely on entry/exit analysis.
Coin control manual UTXO selection enables users to avoid address linkage. Rather than automatic selection from multiple addresses, manual control users strategically spend from single addresses. However, the strategic behavior creates signatures identifying privacy practices.
UTXO fragmentation strategies maintain numerous small-value UTXOs preventing consolidation that reveals relationships. Privacy users deliberately fragment larger UTXOs, then spend small UTXOs individually. While preventing direct clustering, the fragmentation patterns create behavioral fingerprints.
Time-delayed consolidation separates consolidation from operational timing obscuring immediate correlations. Sophisticated users consolidate during low-activity periods, then spend much later. This temporal separation complicates timing analysis though systematic patterns remain detectable.
Frequently Asked Questions
How accurate is common input heuristic clustering?
Common input heuristic achieves 85-95% accuracy in standard Bitcoin usage scenarios where users employ conventional wallets following standard transaction creation practices. Accuracy decreases in specific contexts – CoinJoin transactions deliberately combine inputs from multiple entities violating the heuristic, exchange hot wallets consolidate customer deposits from different users, and shared wallets (family accounts, business partnerships) legitimately combine inputs from multiple individuals. Investigators validate clusters through corroborating evidence including change address patterns, temporal correlations, and behavioral consistency before treating attribution as high-confidence. False positive rates remain 5-15% depending on blockchain ecosystem and user sophistication.
Can input pattern analysis work on Ethereum and account-based blockchains?
Ethereum and most account-based blockchains don’t use UTXO models, eliminating traditional input pattern analysis. These systems maintain running balances rather than discrete unspent outputs requiring explicit selection. However, analogous analysis examines nonce sequencing (transaction ordering from accounts), gas price patterns (fee selection consistency), contract interaction sequences (systematic protocol usage), and balance management behaviors (consolidation timing, fragmentation patterns). While technical implementations differ fundamentally from Bitcoin UTXO analysis, behavioral fingerprinting principles remain applicable enabling entity classification and address clustering through alternative methodologies achieving 70-85% accuracy.
How do exchanges handle UTXO management?
Major cryptocurrency exchanges operate sophisticated UTXO consolidation systems managing thousands of customer deposits creating millions of UTXOs. Exchange hot wallets execute regular consolidations (hourly, daily, or triggered by UTXO count thresholds) combining customer deposits into fewer UTXOs for efficient management. Batch withdrawal processing combines dozens of customer withdrawal requests into single transactions with 50-200+ inputs. These systematic patterns create highly distinctive signatures enabling exchange hot wallet identification with 90%+ confidence. Crypto Trace Labs maintains databases of exchange-specific patterns enabling precise platform attribution for investigation coordination.
What input patterns indicate money laundering operations?
Money laundering exhibits distinctive input patterns through operational phases. Initial fragmentation creates numerous small UTXOs across many addresses. Systematic consolidation before cash-out combines these distributed UTXOs revealing network control – dozens of previously unrelated addresses all contributing inputs to common consolidation addresses. Urgency signals appear through rapid consolidation timing (24-48 hour windows) and immediate forwarding to exchange deposit addresses. Recycling patterns show consolidated funds fragmenting again for additional layering cycles. Statistical analysis identifies when consolidation input counts, timing precision, and destination clustering exceed legitimate business operations, indicating probable criminal activity requiring enhanced investigation.
What tools automate input pattern analysis?
Professional blockchain forensics platforms including Chainalysis, Elliptic, and CipherTrace implement automated input pattern analysis maintaining continuously updated cluster databases. These platforms process entire blockchain histories identifying common input relationships, applying transitive clustering, and generating entity attribution reports. Open-source tools like BlockSci enable researchers to implement custom input analysis algorithms. Graph databases (Neo4j, Amazon Neptune) provide infrastructure for transaction relationship mapping. However, effective analysis requires expert interpretation – automated clustering generates attribution hypotheses requiring human validation through behavioral consistency checks, temporal correlation verification, and external intelligence corroboration before treating results as investigation-grade attribution.
Professional Input Pattern Analysis Services
Transaction input pattern analysis requires comprehensive blockchain data processing, sophisticated clustering algorithms, and expert interpretation that most organizations lack. Whether investigating cryptocurrency theft, fraud operations, or compliance violations, professional analysis can attribute addresses to entities and map complete network structures.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We’ve applied input pattern analysis across hundreds of investigations, from individual theft cases to complex money laundering networks coordinating hundreds of addresses.
What we provide:
- Comprehensive common input clustering with transitive relationship mapping
- Coin selection fingerprinting identifying wallet software implementations
- UTXO consolidation analysis exposing criminal network structures
- Temporal correlation detection revealing coordinated address groups
- Exchange identification through batch withdrawal pattern recognition
- Entity classification distinguishing exchanges, individuals, criminals, and automated systems
For investigation services, we provide transparent project-based pricing based on case complexity and analysis requirements.
Schedule a Free Consultation – We’ll review your situation and explain how input pattern analysis can support your investigation or compliance requirements.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- How to Trace Cryptocurrency Through Mixers: Expert Guide
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, transaction analysis, and forensic investigation.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have applied input pattern analysis in hundreds of cryptocurrency investigations, provided expert witness testimony explaining clustering methodologies in court proceedings, and developed proprietary algorithms enhancing attribution accuracy.
For professional blockchain forensics, input pattern analysis, or cryptocurrency investigation services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Investigation methodologies and attribution accuracy vary based on specific circumstances and blockchain ecosystems. Consult qualified professionals regarding your situation.