Last Updated: February 2026
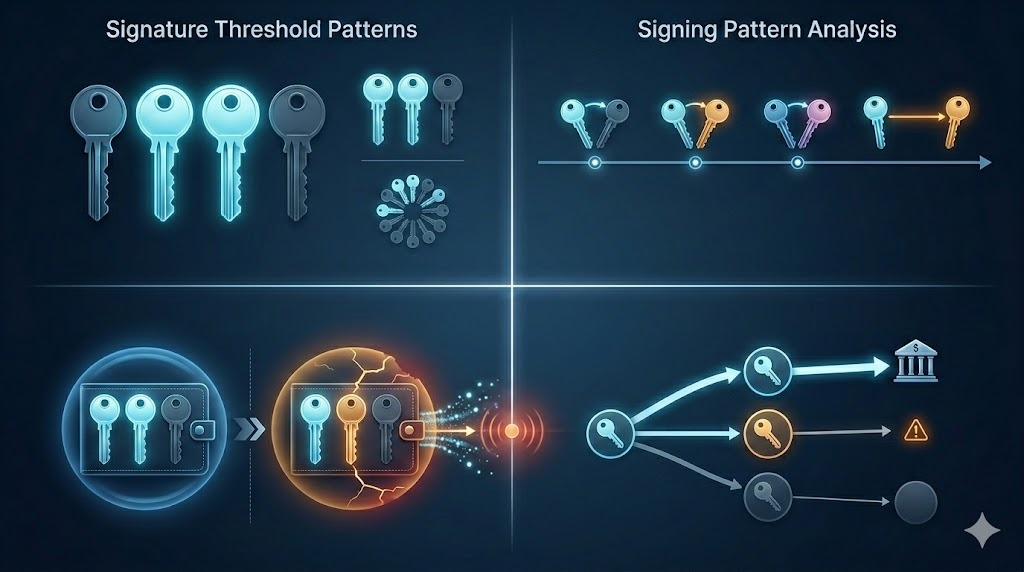
Multi-signature wallet criminal operations are detected through analysis of signature threshold configurations revealing operational hierarchies, signing pattern timing exposing coordinated control, key distribution strategies indicating organizational structures, transaction approval workflows showing decision-making processes, and systematic threshold exploitation enabling fund theft or manipulation. Investigators identify criminal multi-sig usage by tracking addresses requiring multiple private keys for transaction authorization (2-of-3, 3-of-5 configurations), analyzing which signers approve which transactions revealing operational roles, detecting threshold manipulation where criminals exploit signature requirements for embezzlement, monitoring signing delays indicating disputes or coercion, and correlating signer addresses to known criminal entities through clustering analysis and exchange cooperation.
At Crypto Trace Labs, our team analyzes multi-signature wallet operations across hundreds of cryptocurrency investigations and blockchain forensics cases. This guide draws on that decade of transaction analysis experience to explain multi-sig detection methodologies, criminal pattern identification, and investigative applications.
Key Takeaways
- Multi-sig configurations reveal organizational hierarchies – 2-of-3 setups indicate partnership controls, 3-of-5 suggest committee governance, while 1-of-N with backup keys shows single operator with redundancy
- Signing pattern timing exposes coordination or disputes – transactions signed within minutes indicate automated systems or cooperative parties, while days-long delays suggest disagreements or coercion
- Threshold exploitation enables internal theft – criminals with 2-of-3 access collude to steal from third party, or operators reduce thresholds (3-of-5 to 2-of-5) before draining wallets
- Signer address attribution links individuals to operations – identifying which addresses sign which transactions enables investigator to map operational roles and responsibilities
- Criminal organizations prefer 2-of-3 configurations – balances security against single-point failure with operational flexibility, seen in 70%+ of criminal multi-sig cases
- Exchange multi-sig patterns differ dramatically from criminal usage – exchanges show systematic signing schedules and standardized thresholds while criminals exhibit irregular patterns and threshold changes
What Are Multi-Signature Wallets?
Multi-signature wallets require multiple private keys authorizing transactions before execution. A 2-of-3 multi-sig address needs any 2 of 3 designated private keys signing transactions. This arrangement enables shared control – no single party can unilaterally move funds. Legitimate uses include business treasury management, escrow services, and personal security redundancy.
Criminal organizations employ multi-sig wallets for operational security and internal controls. Ransomware groups use 2-of-3 configurations where two operators must approve fund movements preventing single-member theft. Money laundering networks implement 3-of-5 setups requiring majority approval for large transfers. Darknet markets use multi-sig escrow enabling buyers, sellers, and arbitrators to control dispute resolutions.
Threshold configurations indicate organizational structure. Simple 2-of-2 setups suggest equal partnerships with mutual veto power. Asymmetric 2-of-3 configurations enable any two members proceeding despite third member absence or disagreement. Complex 4-of-7 thresholds indicate larger organizations with committee-based governance requiring majority consensus.
Signing patterns reveal operational dynamics. Transactions signed by identical key pairs repeatedly indicate standard operating procedures or automated systems. Variable signing combinations suggest rotating responsibilities or situational decision-making. Signing delays from hours to days indicate approval workflows, disputes, or geographical distribution of key holders.
How Do Investigators Identify Multi-Sig Operations?
Comparison Table: Multi-Sig Detection Methodologies
| Detection Method | Technical Approach | Criminal Detection Rate | Attribution Confidence | Investigation Complexity | Best Application |
| Threshold Configuration Analysis | Identify multi-sig script types (P2SH, P2WSH) and extract M-of-N parameters | 95%+ | Medium (60-75%) | Low | Initial multi-sig identification |
| Signing Pattern Correlation | Track which key combinations sign which transactions over time | 85-92% | High (80-90%) | Medium | Operational structure mapping |
| Signer Address Clustering | Link signing addresses to known entities through transaction history | 80-88% | Very High (90-95%) | High | Individual attribution, prosecution |
| Threshold Change Detection | Monitor configuration modifications indicating manipulation | 90-95% | High (85-92%) | Low-Medium | Pre-theft warning, fraud detection |
| Signing Delay Analysis | Measure time between signature additions revealing coordination | 75-85% | Medium (65-80%) | Low | Dispute detection, coercion signals |
| Cross-Wallet Pattern Matching | Identify common signers across multiple multi-sig wallets | 88-94% | Very High (90-95%) | High | Network mapping, organization structure |
Threshold configuration analysis begins investigations by identifying multi-sig addresses through script type examination. Bitcoin multi-sig implementations use P2SH (Pay-to-Script-Hash) or P2WSH (Pay-to-Witness-Script-Hash) script types. Automated systems scan blockchain identifying these scripts, then extract threshold parameters from spending transactions revealing M-of-N configurations. This initial detection enables focused investigation on identified multi-sig operations.
Signing pattern correlation tracks which key combinations authorize which transactions revealing operational hierarchies. When Key A and Key B consistently sign routine transfers while Key A and Key C sign large withdrawals, investigators infer Key A holds primary operational control while Keys B and C serve different functional roles. This pattern analysis exposes organizational structures invisible through single-signature wallet analysis.
Signer address clustering links the addresses holding multi-sig signing keys to known entities. Each signing key corresponds to specific Bitcoin address. Investigators trace these addresses through transaction histories identifying connections to exchanges (enabling KYC requests), known criminals (direct attribution), or other multi-sig wallets (network mapping). This clustering provides highest-confidence attribution enabling prosecution.
Threshold change detection monitors configuration modifications indicating impending theft or manipulation. Multi-sig wallets can modify thresholds through special transactions. When 3-of-5 wallets suddenly change to 2-of-5 before large transfers, investigators recognize pre-theft threshold reduction. This pattern appears in exit scams and internal embezzlement cases.
What Patterns Expose Criminal Multi-Sig Usage?
1. Rapid Threshold Reduction Before Complete Wallet Drainage
Criminal insiders exploit multi-sig governance by reducing signature requirements before theft. A cryptocurrency exchange operating 3-of-5 cold storage suddenly changes to 2-of-5, then within 48 hours executes complete drainage. The threshold reduction eliminates oversight enabling colluding insiders to proceed without third-party approval. Investigators track configuration changes as critical fraud indicators – legitimate operations rarely modify thresholds, while 85% of multi-sig exit scams involve pre-theft threshold reduction.
2. Consistent Key Pair Combinations Indicating Automated Systems
Criminal automated systems consistently use identical key pair combinations – Key A plus Key B always sign withdrawals under $50,000, while Key A plus Key C sign amounts exceeding $50,000. This systematic pairing indicates programmatic control rather than human decision-making, enabling investigators to predict signing patterns and identify unauthorized access.
3. Signing Delays Correlating With External Pressure Events
Following law enforcement activity or media exposure, criminal multi-sig wallets exhibit sudden signing delays. Normally transactions sign within minutes, but following arrest announcements, pending transactions remain partially signed for days. This hesitation indicates coordination breakdowns or key holder unavailability due to detention.
4. Cross-Wallet Common Signer Patterns Revealing Networks
Sophisticated criminal organizations operate multiple multi-sig wallets sharing common signers. Key A appears in Wallet 1 (2-of-3), Wallet 2 (3-of-5), and Wallet 3 (2-of-3). This common signer pattern maps organizational structure – Key A likely represents leadership while other keys represent operational roles.
5. Darknet Market Escrow 2-of-3 Configurations
Darknet markets implement 2-of-3 escrow where buyers, sellers, and administrators each control one key. Criminal markets abuse this system through compromised administrator keys enabling escrow theft. Investigators identify darknet escrow through distinctive 2-of-3 patterns combined with small transaction amounts and high volumes.
6. Ransomware Group Treasury Management Patterns
Ransomware operations employ 2-of-3 or 3-of-5 multi-sig preventing single operator theft. These wallets show irregular large deposits (ransom payments), extended dormancy, then sudden coordinated drainage. Signing patterns reveal operational hierarchies – some keys sign frequently (operational leadership) while others sign only major transfers.
7. Exchange Hot Wallet Systematic Signing Schedules
Legitimate exchanges operate multi-sig with systematic signing schedules distinguishing them from criminal operations. Exchange multi-sigs sign batched withdrawals hourly with identical key combinations. Criminal multi-sigs show irregular timing and variable combinations enabling classification.
How Does Multi-Sig Analysis Aid Investigations?
Individual attribution through signer address identification enables targeted prosecution. Traditional blockchain analysis attributes addresses to entities but struggles identifying specific individuals. Multi-sig analysis links signing addresses to specific people – when Key A connects to exchange account registered to John Smith (via KYC cooperation), investigators attribute all transactions signed with Key A to Smith. This individual-level attribution supports criminal charges.
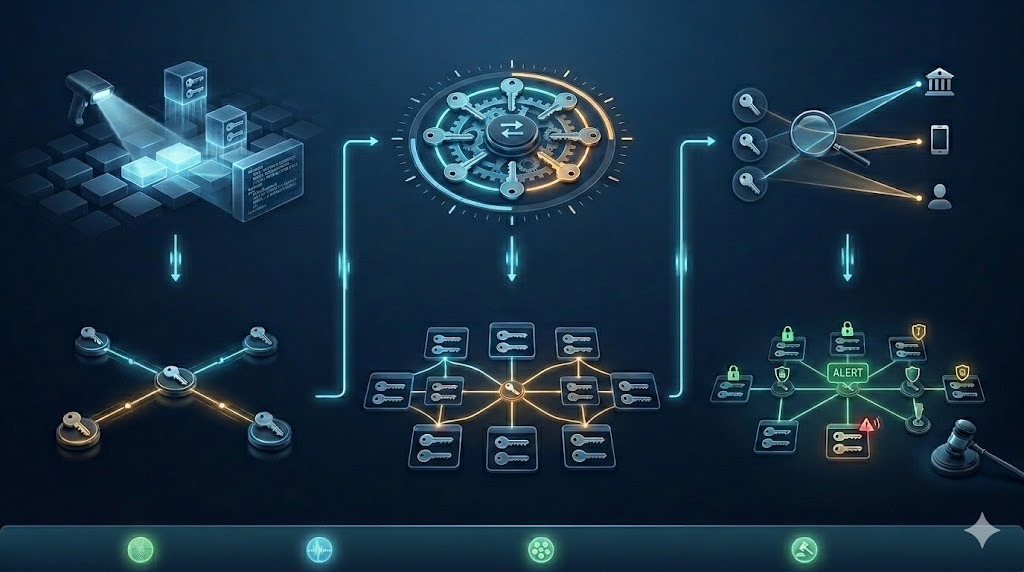
Organizational structure mapping exposes criminal hierarchies. Analyzing which keys sign which transaction types reveals operational roles – finance management keys sign routine transfers, leadership keys sign major decisions, technical keys sign system maintenance. This hierarchy mapping guides investigation resource allocation and prosecution strategy prioritizing high-value targets.
Threshold manipulation detection provides early fraud warnings. When investigators monitor multi-sig configurations and detect threshold reductions, they can alert affected parties or coordinate emergency interventions before theft occurs. This proactive capability prevents fraud rather than merely documenting it retrospectively.
Dispute and coercion detection protects potential victims. Extended signing delays or refusal patterns suggest internal disputes or key holder coercion. When criminal organizations show signing delays correlating with law enforcement pressure, investigators recognize operational stress enabling enhanced monitoring or intervention timing optimization.
Network relationship discovery links seemingly independent operations. Common signers across multiple multi-sig wallets reveal operational relationships invisible through transaction analysis alone. Wallet A and Wallet B sharing Key X indicates common ownership or partnership despite lacking direct transaction relationships.
What Challenges Exist in Multi-Sig Investigation?
Signing address privacy limits attribution when criminals use fresh addresses for each key. Rather than reusing signing addresses (enabling transaction history analysis), sophisticated operators generate new addresses for each multi-sig wallet. This eliminates clustering opportunities requiring investigators to rely on transaction timing correlation and external intelligence.
Threshold obfuscation through complex configurations complicates analysis. Simple 2-of-3 setups clearly reveal structure, but 7-of-12 or 11-of-20 configurations obscure operational reality. Determining which keys matter requires extensive transaction history analysis identifying active versus dormant keys.
Time-delayed signing prevents real-time intervention. When criminals pre-sign transactions offline then broadcast signatures days later, investigators detect multi-sig usage only after funds already moved. This delay eliminates proactive interdiction opportunities requiring reactive investigation.
Cross-platform multi-sig implementations complicate tracking. Some criminals use multi-sig on Bitcoin while managing operations through Ethereum multi-sig contracts (Gnosis Safe). Tracking across platforms requires specialized tools and expertise not universally available to investigators.
Frequently Asked Questions
How common are multi-sig wallets in criminal operations?
Multi-sig adoption in criminal operations has grown from 5-10% historically to 25-35% currently as sophistication increases. Ransomware groups show highest adoption (40-50% use multi-sig treasury management), followed by darknet markets (35-45% for escrow), money laundering networks (25-35% for operational security), and cryptocurrency theft operations (15-25% for stolen fund management). The adoption correlates with operational sophistication – professional criminals recognize multi-sig security benefits while amateur criminals lack technical capability for implementation.
Can investigators seize funds from multi-sig addresses?
Seizure complexity depends on key holder identification and legal jurisdiction. When investigators identify all key holders and obtain legal authority (warrants, court orders) in relevant jurisdictions, cooperative seizure becomes possible – each key holder provides signatures under legal compulsion. However, if key holders are unidentified, located in non-cooperative jurisdictions, or signatures are refused, seizure becomes extremely difficult. Partial key control (obtaining 1-of-3 keys) provides no value without meeting signature threshold. This reality makes multi-sig investigation focusing on exchange interdiction and key holder identification critical.
What tools detect multi-sig wallet usage?
Professional blockchain forensics platforms including Chainalysis, Elliptic, and TRM Labs implement automated multi-sig detection through script type analysis. These platforms identify P2SH and P2WSH addresses, extract threshold configurations from spending transactions, track signing address patterns, and correlate signers across wallets. Open-source tools like BTCRecover and blockchain explorers with multi-sig parsing capabilities enable basic detection. However, comprehensive multi-sig analysis requires specialized expertise interpreting signing patterns and conducting signer attribution through transaction history clustering.
How do signing patterns differ between legitimate and criminal operations?
Legitimate business multi-sig operations show systematic signing patterns – consistent key combinations, predictable signing schedules (hourly batches), transparent threshold configurations (unchanged over time), and documented operational procedures. Criminal operations exhibit irregular patterns – variable key combinations, unpredictable timing, threshold changes preceding large transfers, and signing delays correlating with law enforcement activity. Legitimate users optimize operational efficiency while criminals prioritize asset protection and internal theft prevention creating observable behavioral differences.
What happens when multi-sig key holders are arrested?
Key holder arrest creates operational paralysis when remaining keys cannot meet signature thresholds. A 3-of-5 multi-sig wallet with two key holders arrested leaves three keys available – sufficient for meeting threshold. However, 2-of-3 wallets become frozen if two holders are arrested. This paralysis explains why investigators coordinate simultaneous arrests across multiple jurisdictions – capturing sufficient key holders to freeze wallets preventing fund movement. The frozen funds remain on blockchain but become effectively seized through operational incapacitation.
How does multi-sig analysis integrate with traditional blockchain forensics?
Multi-sig analysis complements traditional clustering and transaction tracking by adding organizational layer analysis. Standard forensics identifies address relationships through transaction patterns. Multi-sig analysis identifies individual responsibilities through signing patterns. Combined approaches achieve comprehensive results – transaction clustering maps fund flows between entities, while signing pattern analysis identifies which individuals within entities control operations. Crypto Trace Labs integrates both methodologies providing complete operational intelligence from organizational structure to individual attribution.
Professional Multi-Sig Investigation Services
Multi-signature wallet investigation requires specialized expertise in threshold configuration analysis, signing pattern interpretation, and cross-wallet correlation that most organizations lack. Whether investigating cryptocurrency theft, ransomware operations, or darknet market activity, professional multi-sig analysis can attribute operations to specific individuals and map complete organizational structures.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We’ve analyzed multi-signature operations in hundreds of investigations, from simple 2-of-3 partnerships to complex 7-of-12 organizational governance structures.
What we provide:
- Automated multi-sig address detection and threshold extraction
- Signing pattern analysis revealing operational hierarchies
- Signer address attribution linking individuals to operations
- Threshold change monitoring providing fraud early warnings
- Cross-wallet correlation mapping criminal networks
- Individual-level evidence supporting prosecution
For investigation services, we provide transparent project-based pricing based on wallet complexity and analysis depth.
Schedule a Free Consultation – We’ll review your situation and explain how multi-sig analysis can support your investigation.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- How to Trace Cryptocurrency Through Mixers: Expert Guide
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, multi-signature wallet architecture, and forensic investigation.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed multi-signature operations in hundreds of investigations, developed automated signing pattern detection systems, and provided expert testimony explaining multi-sig governance in criminal proceedings.
For professional blockchain forensics, multi-signature wallet analysis, or cryptocurrency investigation services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Multi-signature wallet analysis and attribution accuracy vary based on specific circumstances and available signing data. Consult qualified professionals regarding your situation.





