Cross-chain cryptocurrency tracking involves following asset movements as they transfer between different blockchains through bridges, wrapped tokens, and cross-chain swap protocols. Professional investigators use timing correlation analysis, bridge address monitoring, validator tracking, and wrapped token attribution to maintain investigative continuity when criminals exploit the natural attribution gaps created by moving funds from Bitcoin to Ethereum to Binance Smart Chain to Polygon. These multi-blockchain investigations require specialized tools that can correlate transaction patterns across different ledger structures and address formats.
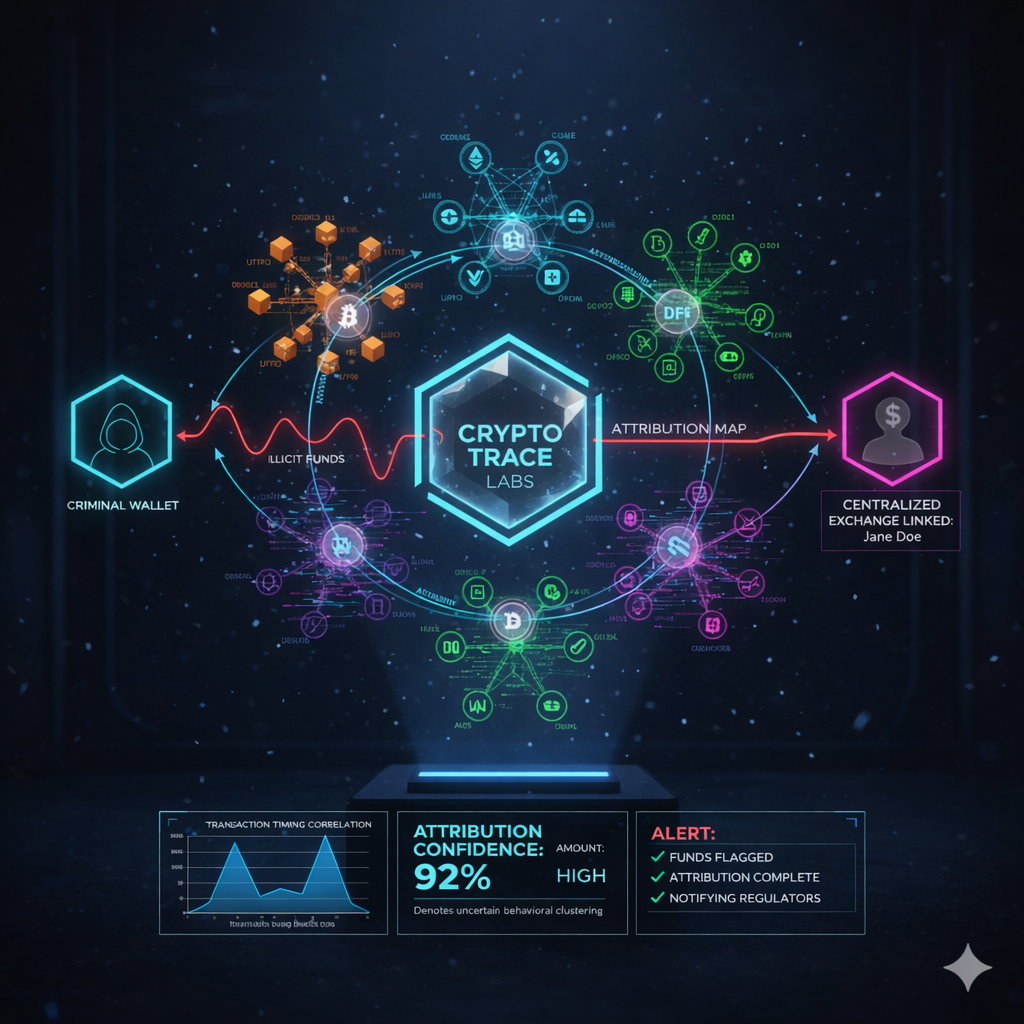
At Crypto Trace Labs, our team – featuring VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has tracked illicit funds across multiple blockchain ecosystems in hundreds of cryptocurrency fraud investigations. This guide draws on that decade of operational experience to explain the forensic methodologies that law enforcement, compliance teams, and institutional investigators need to understand.
What Creates Attribution Gaps in Cross-Chain Transfers?
Different blockchains operate as independent networks with no native ability to communicate directly. Bitcoin transactions use UTXO (Unspent Transaction Output) models with specific address formats, while Ethereum uses account-based models with entirely different addressing systems. When cryptocurrency moves between these networks, the direct on-chain link breaks.
Blockchain bridges work by locking assets on one chain and minting equivalent wrapped tokens on the destination chain. A criminal deposits Bitcoin into a bridge contract, the bridge locks that Bitcoin, and issues wrapped Bitcoin (WBTC) on Ethereum. The Bitcoin blockchain shows a deposit to the bridge address. The Ethereum blockchain shows WBTC minting. No direct transaction connects these two events on-chain.
This creates forensic challenges requiring timing correlation and behavioral analysis rather than direct transaction tracing. Investigators must identify when Bitcoin enters a bridge, calculate expected processing time, then locate corresponding wrapped token minting on the destination chain within that timing window. The attribution gap forces reliance on patterns rather than cryptographic proof.
Criminals exploit these gaps intentionally. Moving stolen Ethereum to Binance Smart Chain through a bridge, swapping to different tokens on decentralized exchanges, then bridging again to Polygon creates multiple attribution breaks. Each bridge crossing requires separate investigative reconstruction.
How Do Different Cross-Chain Methods Work?
Understanding cross-chain technical architectures determines which forensic techniques investigators can apply.
Cross-Chain Transfer Methods Comparison:
| Method | How It Works | On-Chain Visibility | Forensic Difficulty | Criminal Adoption | Recovery Success Rate |
| Blockchain Bridges | Lock assets on source chain, mint wrapped tokens on destination | High – both chains show transactions | Medium – timing correlation needed | Very High – largest volume method | 65% – bridges are traceable |
| Wrapped Tokens | Custody provider holds native assets, issues wrapped equivalents | High – minting and burning visible | Medium – requires provider cooperation | High – widely available | 70% – centralized providers cooperate |
| Atomic Swaps | Smart contracts enable trustless cross-chain trades | Low – happens partially off-chain | Very High – minimal on-chain evidence | Low – technically complex | 30% – limited tracing capability |
| Cross-Chain DEXs | Validator networks facilitate direct asset swaps | Medium – validator activity visible | High – distributed across networks | Very High – no KYC requirements | 45% – requires validator analysis |
| Exchange Intermediaries | Centralized platforms convert between chains | None – internal database transfers | Low – exchange records available | Medium – requires KYC | 85% – exchange cooperation works |
The Ronin Bridge hack in March 2022 demonstrated bridge forensic capabilities. Lazarus Group stole $625 million by compromising validator private keys, then attempted laundering through cross-chain movements. Chainalysis tracked the funds despite bridge crossings, enabling law enforcement to recover $30 million and Norwegian authorities to seize an additional $5.9 million.
Wrapped tokens provide stronger forensic continuity because centralized providers like BitGo (WBTC issuer) maintain complete records linking native Bitcoin deposits to Ethereum WBTC minting. Investigators request these records directly, bypassing the need for timing correlation.
Atomic swaps present the greatest challenge. These occur through hash time-locked contracts (HTLCs) that execute cross-chain trades without intermediaries. Minimal on-chain evidence exists beyond the original asset lock and eventual unlock, with no clear connection between chains.
What Forensic Techniques Enable Cross-Chain Tracking?
Professional cross-chain investigations combine multiple forensic methodologies to maintain attribution across blockchain boundaries.
Cross-Chain Tracing Techniques:
- Timing Correlation Analysis – Investigators identify when assets enter bridges on the source chain, then search for corresponding wrapped token minting on destination chains within expected processing windows (typically 5-30 minutes). Matching transaction amounts across chains within timing windows establishes probable links even without cryptographic proof.
- Bridge Address Monitoring – Known bridge contract addresses on major chains get flagged in forensic databases. When investigated addresses interact with bridges, investigators immediately know cross-chain movement is occurring and can prepare to track on destination chains. Chainalysis and Elliptic maintain comprehensive bridge address lists.
- Wrapped Token Attribution – Tracking WBTC, WETH, or other wrapped assets back to their minting events identifies the original bridge transaction. Many wrapped token issuers provide investigators with direct correlation data linking deposits to mints, bypassing on-chain analysis entirely through provider cooperation.
- Validator Activity Analysis – Cross-chain DEXs like THORChain use validator networks to facilitate swaps. Monitoring validator node transactions reveals when assets move between chains. Validators sign both source chain deposits and destination chain releases, creating behavioral links investigators can follow.
- Amount Fingerprinting – Criminals rarely use round numbers. A deposit of 47.382946 BTC to a bridge followed by 47.382946 WBTC minting on Ethereum strongly suggests correlation even without timing match. Investigators search for distinctive amount patterns across chains to establish links.
- Behavioral Pattern Matching – Wallet addresses on different chains controlled by the same entity often exhibit similar behaviors like consistent gas price preferences, transaction timing patterns, or interaction with the same service providers. Crypto Trace Labs uses behavioral fingerprinting to link multi-chain addresses to single criminal operations.
Merkle Science reported that over $7 billion in illicit cryptocurrency was laundered using cross-chain methods in 2024, with estimated final totals potentially exceeding $75 billion once complex investigations mature. The timing delay in attribution means many cross-chain crimes remain undiscovered for months.
What Real-World Cross-Chain Investigations Exist?
The 2022 bridge hack epidemic demonstrated both cross-chain criminal tactics and successful forensic responses. Multiple major incidents revealed how criminals exploit bridge vulnerabilities and how investigators track funds across chains.
Ronin Bridge – March 2022: Lazarus Group compromised five of nine validator private keys controlling the Ronin Network bridge connecting Ethereum to the Axie Infinity sidechain. Attackers stole 173,600 ETH and 25.5 million USDC worth $625 million. The hack remained undetected for six days until a user reported withdrawal issues.
Forensic tracking by Chainalysis revealed the laundering path – stolen USDC swapped to ETH through DEXs, then portions sent to Tornado Cash mixer and attempts to cash out at centralized exchanges. U.S. Treasury sanctioned the attacker’s Ethereum address. Law enforcement recovered $30 million. Norwegian authorities seized an additional $5.9 million through cross-jurisdictional coordination. The case demonstrated that even sophisticated cross-chain laundering leaves traceable patterns.
Wormhole Bridge – February 2022: Attackers exploited signature verification bypass to steal $326 million worth of ETH, USDC, and SOL. The vulnerability came from insecure code pushed to GitHub. Investigators tracked fund movements across Ethereum and Solana blockchains. Jump Crypto provided $320 million to cover losses, enabling bridge resumption. The rapid forensic response prevented significant criminal cashout.
Harmony Horizon Bridge – June 2022: Compromise of two private keys in a 2-of-5 multi-signature scheme enabled $100 million theft. Funds moved between Harmony, Binance Smart Chain, and Ethereum. Investigators used on-chain analysis to track cross-chain flows, recovering approximately 20 percent through exchange freezes and seized wallets.
These cases reveal consistent criminal patterns – exploit bridge security, rapidly move funds across chains to create attribution gaps, attempt conversion through mixers and exchanges. Success depends on investigators maintaining tracking continuity despite chain transitions.
How Do Wrapped Tokens Complicate or Help Investigations?
Wrapped tokens simultaneously create forensic challenges and opportunities depending on issuance mechanisms. Centralized wrapped tokens like WBTC provide strong investigative advantages while decentralized synthetic assets create significant attribution difficulties.
Centralized providers like BitGo maintain custody of native Bitcoin and issue WBTC on Ethereum with complete minting records. When investigators trace WBTC to suspicious addresses, they request BitGo records showing which Bitcoin addresses deposited funds generating that specific WBTC. This provides direct attribution linking Ethereum addresses to Bitcoin addresses through the wrapper service.
The forensic advantage is that centralized wrappers operate as identity bridges between blockchains. BitGo knows exactly which Bitcoin transaction corresponds to each WBTC minting event. Investigators bypass complex timing correlation by simply requesting provider records.
Decentralized bridge protocols create opposite conditions. No central authority maintains correlation records. Investigators must use timing analysis, amount fingerprinting, and behavioral patterns to link wrapped token minting to source chain deposits. The attribution confidence decreases compared to centralized alternatives.
Criminal awareness of this distinction drives tactical choices. Sophisticated actors avoid centralized wrappers specifically because provider cooperation enables easy attribution. They prefer decentralized bridges or cross-chain DEXs that create genuine attribution gaps.
What Multi-Chain Investigation Tools Exist?
Professional blockchain forensics platforms have evolved to support cross-chain tracking, though capabilities vary significantly across providers.
Cross-Chain Investigation Platform Capabilities:
- Chainalysis Reactor – Supports investigation across Bitcoin, Ethereum, Binance Smart Chain, Polygon, Avalanche, and 10+ major blockchains. Auto-plotting functionality identifies cross-chain movements through known bridges and visualizes multi-chain transaction flows in unified graphs. Used by 150+ government agencies worldwide.
- Elliptic Investigator – Covers 100+ cryptocurrency assets with cross-chain forensic tools. Single-click auto-complete feature traces pathways between entities across blockchains. Platform includes bridge detection and cross-asset exposure tracking. 75% of investigations involve 10+ distinct cryptoassets according to Elliptic data.
- TRM Labs Graph Visualizer – Preserves investigative integrity across bridge crossings and swap protocols. Glass box attribution system shows confidence scores for each cross-chain link. Integrates off-chain intelligence with on-chain data for comprehensive multi-blockchain analysis.
- Merkle Science Tracker – Specializes in cross-chain analytics with support for 50+ blockchains. Graph database architecture enables efficient entity resolution across chains. Automated detection of cross-chain laundering patterns helps compliance teams identify suspicious flows.
These tools have shortened investigation timelines dramatically. What previously required weeks of manual correlation across blockchain explorers now happens in minutes through automated cross-chain plotting. However, tools remain limited by underlying blockchain architecture – truly decentralized bridges still create genuine attribution gaps no software can fully bridge.
Crypto Trace Labs combines proprietary cross-chain analysis tools with executive-level relationships at major exchanges across multiple blockchains. When criminals attempt fiat conversion after complex multi-chain laundering, our direct contacts enable rapid freezing and recovery regardless of which blockchain the final conversion attempt occurs on.
What Challenges Persist in Multi-Blockchain Forensics?
Despite tool improvements, cross-chain investigations face persistent technical and operational challenges that require specialized expertise.
Cross-Chain Attribution Challenges:
- No Universal Address Format – Bitcoin uses Base58Check addresses starting with 1 or 3, Ethereum uses hexadecimal addresses starting with 0x, Solana uses Base58 addresses with different encoding. No standard exists linking the same user’s addresses across chains. Investigators must use behavioral analysis rather than cryptographic proof.
- Timing Windows Create Uncertainty – Bridge processing times vary from minutes to hours depending on network congestion. Wide timing windows allow multiple potential matches for any given cross-chain transfer. Amount fingerprinting helps narrow possibilities but rarely provides definitive attribution.
- Different Blockchain Architectures – UTXO-based chains like Bitcoin require different analysis methodologies than account-based chains like Ethereum. Tools must interpret fundamentally different transaction structures and apply appropriate clustering heuristics for each chain type.
- Validator Anonymity – Cross-chain protocols using validator networks often have anonymous operators. Investigators cannot compel cooperation from unknown validators, limiting ability to trace through validator-mediated transfers unless behavioral patterns reveal identities.
- High Investigation Complexity – Tracking across 3+ chains requires simultaneous analysis of multiple blockchain explorers, correlation of timing across chains with different block times, and synthesis of evidence from separate ledgers into coherent narratives suitable for legal proceedings.
- Emerging Chain Proliferation – New Layer 1 and Layer 2 blockchains launch constantly. Investigators must continuously expand tool support and develop expertise in novel chain architectures. Coverage gaps create blind spots criminals exploit.
The fundamental challenge is that blockchain transparency only exists within individual chains. Cross-chain transparency requires investigative reconstruction rather than direct observation. As Merkle Science research indicates, illicit actors exploiting cross-chain methods create attribution delays that push discovery months into the future, allowing more time for successful laundering.
Frequently Asked Questions About Cross-Chain Tracking
Can investigators actually trace funds across different blockchains?
Yes, but with lower confidence than single-chain tracing. Investigators use timing correlation between bridge deposits and wrapped token minting, amount fingerprinting for distinctive transaction sizes, and behavioral pattern analysis linking addresses across chains. Chainalysis successfully tracked $625 million Ronin Bridge theft across multiple chains, enabling $36 million in recoveries. However, true cryptographic proof rarely exists for cross-chain links – investigators establish probable attribution through circumstantial on-chain evidence.
What makes blockchain bridges vulnerable to exploitation?
Bridges create single points of failure controlling large asset pools. The Ronin hack compromised 5 of 9 validator keys to steal $625 million. Bridges require complex smart contracts and multi-signature schemes that introduce security risks. Unlike individual wallets, bridge exploits affect all users simultaneously. Over $2.3 billion was stolen from bridges in 2022 alone according to forensic analysis.
How do wrapped tokens help or hurt investigations?
Centralized wrapped tokens like WBTC help investigations significantly – providers maintain complete records linking source deposits to wrapped token minting. Investigators request BitGo records showing exactly which Bitcoin address deposited funds for any WBTC address. Decentralized bridge protocols hurt investigations by creating attribution gaps with no central records. Criminals prefer decentralized wrappers specifically to avoid provider cooperation.
What percentage of cross-chain cryptocurrency is illicit?
Precise measurement is extremely difficult due to attribution delays. Merkle Science estimates over $7 billion in confirmed illicit cross-chain transactions in 2024, with potential final estimates exceeding $75 billion once complex investigations mature. The sophistication of chain-hopping significantly delays attribution, often pushing discovery quarters or years after initial transactions. Most cross-chain volume remains legitimate DeFi and arbitrage activity.
Can law enforcement recover stolen crypto after cross-chain laundering?
Recovery success depends on eventual fiat conversion attempts at regulated exchanges. Ronin hack investigators recovered $36 million despite complex cross-chain laundering because criminals had to touch KYC exchanges eventually. Norwegian authorities seized $5.9 million through international cooperation. However, recovery rates drop significantly when criminals successfully convert to fiat through peer-to-peer markets or non-KYC platforms before detection. Professional crypto asset recovery requires rapid response.
What tools do professional investigators use for multi-chain tracking?
Chainalysis Reactor supports 10+ major blockchains with auto-plotting across chains. Elliptic Investigator covers 100+ assets with single-click cross-chain pathfinding. TRM Labs provides graph visualization preserving integrity across bridge crossings. Merkle Science specializes in 50+ blockchain cross-chain analytics. These tools shortened investigation timelines from weeks to minutes by automating timing correlation and bridge detection.
How long does cross-chain investigation typically take?
Simple bridge crossings with clean timing correlation can be tracked in hours. Complex multi-hop laundering across 5+ chains with multiple DEX swaps, mixer usage, and decentralized bridge crossings requires weeks to months for comprehensive reconstruction. The Ronin investigation took months despite sophisticated tools because criminals used advanced obfuscation. Real-time monitoring can flag suspicious patterns within minutes but attributing to real-world identities requires additional legal process.
What compliance challenges do exchanges face with cross-chain deposits?
Compliance teams must determine whether deposited wrapped tokens originated from legitimate sources or illicit activity that crossed chains before arriving. Blockchain analytics platforms assign risk scores based on cross-chain exposure and historical bridge interactions. Deposits from known bridge addresses trigger enhanced due diligence. Compliance teams must correlate activity across multiple chains simultaneously to assess true risk.
Why do criminals prefer cross-chain laundering methods?
Cross-chain movements create natural attribution gaps that force investigators to use circumstantial timing correlation rather than cryptographic proof. Each bridge crossing requires separate investigative reconstruction. Moving funds across 3-4 chains creates multiple attribution breaks. Combined with DEX swaps and mixers, criminals create layered obfuscation that delays detection and reduces recovery likelihood compared to single-chain movements.
Conclusion
Cross-chain cryptocurrency tracking requires different methodologies than single-blockchain analysis, emphasizing timing correlation, behavioral pattern recognition, and provider cooperation over direct transaction tracing. Professional investigations succeed by identifying bridge interactions early, maintaining parallel analysis across multiple chains, using wrapped token provider records, and exploiting inevitable fiat conversion touchpoints at regulated exchanges.
This guide was prepared by the team at Crypto Trace Labs, drawing on 10+ years of crypto and financial crime experience from executive roles at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS certifications, MLRO qualifications across UK, US, and Europe, and Chartered status at Fellow Grade. We offer no upfront charge for non-custodial wallet recoveries – you only pay after successful fund recovery.
Contact Crypto Trace Labs for professional cross-chain investigation, multi-blockchain forensics consulting, or expert analysis of complex bridge-related cases.