Last Updated: February 2026
Transaction velocity patterns measure the frequency, timing, and volume of financial transfers to identify automated criminal operations that execute transactions faster than humanly possible. Sophisticated money laundering networks, cryptocurrency theft operations, and fraud schemes employ automated scripts and bots processing hundreds of transactions per minute across thousands of accounts – creating distinctive mathematical signatures investigators detect through velocity threshold analysis, timing pattern recognition, and statistical deviation modeling. These automated operations reveal themselves through impossibly rapid sequential transfers, identical transaction timing across unrelated accounts, microsecond-precise execution patterns, and transaction volumes exceeding human cognitive and physical limitations.
At Crypto Trace Labs, our team analyzes velocity patterns across hundreds of cryptocurrency fraud investigations and blockchain forensics cases. This guide draws on that decade of financial crime and AML compliance experience to explain velocity detection methodologies, automated operation indicators, and investigative strategies.
What Makes Velocity Analysis Critical for Detecting Automation?
Human transaction processing has inherent limitations. Even experienced professionals require 30-90 seconds to review account details, verify recipients, and execute single transfers. When investigators observe accounts completing 50 transactions in 10 minutes, the mathematical impossibility proves automation.
Automated criminal operations prioritize speed over security because velocity creates investigative overwhelm. By executing 200 transactions across 50 accounts within one hour, criminals generate more work than compliance teams can process in real-time. While investigators reconstruct the first 20 transfers, automated systems complete 180 additional hops.
Cryptocurrency amplifies automation effectiveness. Blockchain transactions execute in seconds, enabling criminals to split $10 million across 1,000 addresses in under 5 minutes – a task requiring weeks manually.
Machine learning algorithms excel at velocity detection because automated operations create mathematically consistent signatures human activity cannot replicate. When transactions occur at precisely 1.3-second intervals or amounts follow algorithmic progressions, statistical analysis identifies automation with 95%+ accuracy.
How Do Different Automated Criminal Operations Function?
Automated cryptocurrency mixers execute rapid-fire transactions distributing funds across dozens of addresses faster than human coordination. A criminal deposits 50 BTC into an automated tumbler which immediately fragments into 247 outputs, sends each through 3-7 intermediate addresses, then reassembles at destinations – completing in under 12 minutes.
Bot-driven exchange arbitrage exploits price differences through automated high-frequency trading. Criminal scripts simultaneously monitor 15 exchanges, execute buy/sell orders within milliseconds, moving $500,000+ through 200+ trades daily while appearing as legitimate market-making.
Smart contract automated layering employs blockchain code executing complex sequences when triggered. Criminals program contracts to split funds, swap cryptocurrencies, interact with DeFi protocols, and distribute to destinations – executing 40+ operations in under 90 seconds.
What Velocity Metrics Reveal Automated Activity?
Comparison Table: Velocity Detection Metrics
| Velocity Metric | Human Baseline | Automated Threshold | Detection Accuracy | Investigation Priority |
| Transactions Per Minute | 0.5-2 TPM | >10 TPM sustained | 90-95% | Immediate high-priority alert |
| Sequential Transfer Speed | 30-90 seconds between transfers | <5 seconds between transfers | 85-92% | High-priority investigation |
| Timestamp Precision | Variable (seconds granularity) | Millisecond/microsecond precision | 95-98% | Automated operation confirmed |
| Cross-Account Synchronization | Random timing variance | Identical timing within 3 seconds | 88-94% | Network mapping required |
| Daily Transaction Volume | 5-50 transactions/day | >200 transactions/day | 75-85% | Medium-priority review |
| Amount Pattern Consistency | Natural variation | Mathematical sequences | 92-97% | Script-generated confirmed |
Transaction-per-minute analysis establishes baseline expectations. Retail accounts average 2-5 monthly transactions. When accounts suddenly process 1,200 transactions in 8 hours, the velocity spike indicates automation.
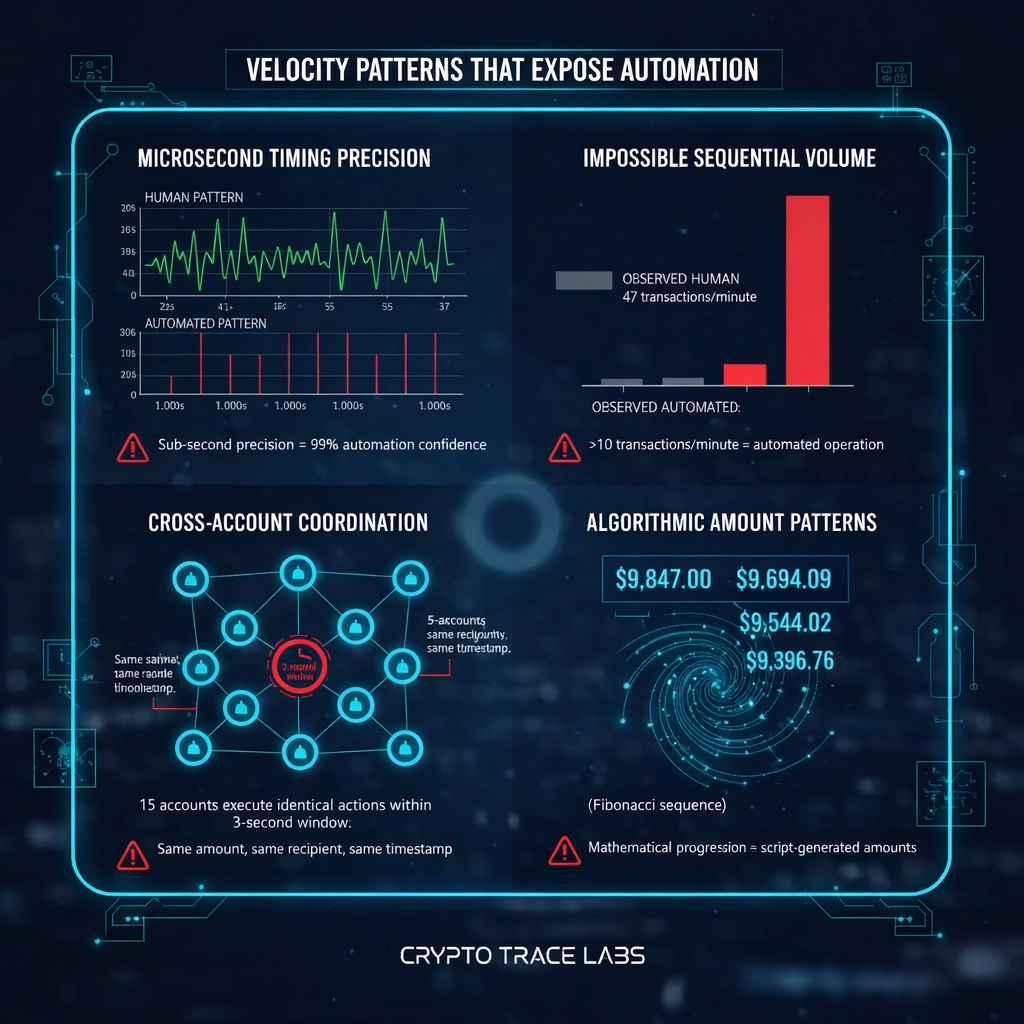
Sequential transfer timing reveals impossible coordination. When Account A sends to B, how quickly does B forward to C? Human operators require 15-30 seconds minimum. Automated systems complete in under 2 seconds.
Timestamp precision identifies automation through mathematical exactness. Human transactions show natural variance – 9:47:23, 9:51:17, 9:58:42. Automated scripts execute at precise intervals – 10:00:00.000, 10:01:00.000, 10:02:00.000.
Cross-account synchronization flags coordinated bot networks. When 20 accounts execute identical actions within 5 seconds, investigators recognize centralized automated control.
Amount pattern analysis identifies script-generated transactions. When amounts show mathematical relationships (Fibonacci sequences, percentage-based calculations) rather than organic commercial values, statistical tests confirm automation.
Numbered Listicle: 7 Velocity Patterns That Expose Criminal Automation
1. Round-Robin Distribution – Systematic Fund Allocation
Automated systems distribute funds using algorithms cycling through recipients in fixed sequences. An operation receives $100,000 and executes 100 transfers of exactly $1,000 each to addresses 1-100 in numerical order over 167 seconds. The mechanical perfection exposes automation requiring transaction tracking analysis.
2. Algorithmic Timing Intervals – Clock-Based Execution
Criminal scripts execute at precise intervals – every 60 seconds or exact hourly boundaries (10:00:00, 11:00:00). Analysis reveals median 300.000 seconds with standard deviation 0.003 seconds. Human timing shows median 300 seconds but deviation exceeding 45 seconds.
3. Batch Processing Bursts – Concentrated Activity Windows
Automated operations execute all daily transactions in concentrated bursts. An account processes 847 transactions between 3:17-4:03 AM, then remains dormant for 23 hours. Human-operated accounts show activity during working hours with natural breaks.
4. Multi-Exchange Arbitrage Speed – Impossibly Fast Trading
Cryptocurrency arbitrage bots execute coordinated trades within milliseconds. Account X purchases ETH on Exchange A at 14:23:17.342 and sells on Exchange B at 14:23:17.389 – a 47-millisecond gap impossible for human traders requiring 3-5 seconds minimum.
5. Smart Contract Triggered Cascades – Automatic Sequences
Blockchain smart contracts execute predetermined sequences automatically. A deposit triggers: split across 15 addresses (2s), swap to different cryptocurrencies (8s), route through DeFi (12s), distribute to destinations (5s) – completing 47 operations in 27 seconds total.
6. Identical Amount Cloning – Perfect Replication
Automated systems execute hundreds of identical transactions. Analysis reveals 342 transactions each for exactly $4,873.91 across 89 accounts over 14 days. The mathematical perfection eliminates human coordination possibility.
7. Microsecond Network Synchronization – Coordinated Bot Timing
Bot networks coordinate with microsecond precision. At 09:15:23.847291, accounts in Singapore, London, New York, and Dubai all execute identical actions with variance under 500 microseconds, proving centralized automated control.
How Do Investigators Analyze Velocity Patterns?
Statistical baseline modeling establishes normal transaction velocity ranges. Investigators determine e-commerce merchants average 47 daily transactions with deviation of 12, while consulting firms average 8 monthly with deviation of 4. When accounts exhibit 20+ standard deviations from norms, automated alerts trigger.
Time-series analysis identifies anomalies through historical comparison. Analysts plot frequency over months revealing accounts maintaining 5-10 daily transactions for six months, then spiking to 200+ for 48 hours. The velocity anomaly indicates compromise or deliberate activation.
Network velocity correlation exposes coordinated automation. Investigators examine whether velocity spikes show timing relationships across accounts. Correlated patterns prove coordinated control suggesting bot networks.
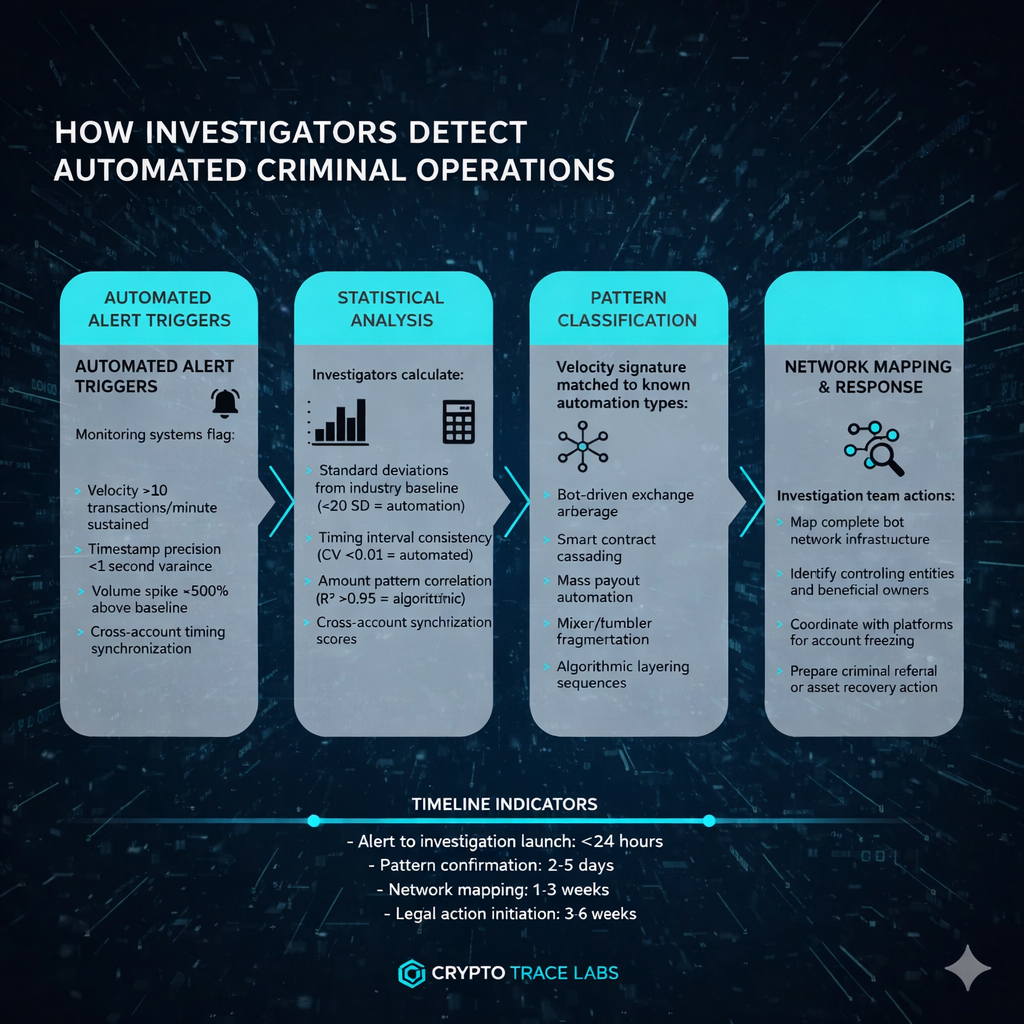
Machine learning models trained on millions of transactions identify subtle automation signatures. These systems detect when velocity patterns exhibit characteristics inconsistent with human cognitive processing speeds or when timing distributions match computational rather than behavioral patterns.
Blockchain-specific velocity analysis examines gas prices, nonce sequencing, and confirmation timing. Crypto Trace Labs investigators identify automation through gas price consistency (bots use algorithmic calculation), sequential nonce usage revealing single-entity control, and timing proving pre-signed batch submission.
What Countermeasures Do Criminals Employ?
Randomization algorithms introduce artificial variance attempting to mimic human behavior. Sophisticated automation adds random delays (15-90 seconds), randomizes amounts ($4,850-$5,150), and staggers execution. However, even randomized automation exhibits statistical signatures – the “random” variance follows computational pseudo-random distributions detectable through chi-squared tests.
Throttling mechanisms deliberately slow execution attempting to stay below velocity thresholds. Criminal scripts limit to 5 transactions per minute or 100 daily. Investigators counter through sustained observation – accounts maintaining precise 5.00 transactions per minute reveal throttled automation.
Distributed bot networks fragment operations across hundreds of accounts keeping individual velocity within normal ranges. Network analysis defeats this by identifying timing correlations and coordinated activity patterns exposing centralized control.
What Legal and Regulatory Frameworks Apply?
Financial institutions must maintain transaction monitoring systems detecting velocity anomalies under Bank Secrecy Act requirements. When automated alerts identify impossible transaction speeds, compliance teams must investigate and file Suspicious Activity Reports. Failure to detect obvious automation constitutes compliance deficiency.
Computer Fraud and Abuse Act (18 USC 1030) criminalizes deployment of automated bots against banking platforms without authorization. Criminals using automation face federal prosecution with penalties up to 20 years.
Wire fraud statutes (18 USC 1343) apply when automated systems execute fraudulent transfers. Each automated transaction constitutes separate wire fraud offense, creating compound sentencing exposure.
Anti-Money Laundering regulations require enhanced due diligence when customers exhibit automation patterns. Accounts failing to provide satisfactory explanations face enhanced monitoring or termination.
Frequently Asked Questions
How fast do automated criminal transactions actually execute compared to human transactions?
Automated criminal systems typically execute transactions in under 2 seconds per transfer, with some bot networks achieving sub-millisecond speeds across multiple exchanges simultaneously. Human operators realistically need 30-90 seconds per transaction to verify details and confirm transfers. This speed differential creates the core detection opportunity, as investigators use statistical analysis to identify accounts operating beyond human processing capabilities. Crypto Trace Labs uses this gap as a primary automation indicator in on-chain tracing investigations.
Can criminals make automated transactions look like normal human activity?
Sophisticated criminal operations use randomization algorithms that add artificial delays and vary transaction amounts to mimic human behavior. However, even randomized automation generates detectable statistical signatures because computer-generated “randomness” follows pseudo-random distributions rather than true behavioral variance. Chi-squared tests and entropy analysis consistently distinguish algorithmic randomization from genuine human unpredictability. Investigators trained in velocity analysis detect these subtle differences even when criminals invest significant effort in evasion.
What tools do investigators use to detect transaction velocity anomalies?
Investigators combine blockchain analytics platforms such as Chainalysis and Elliptic with custom statistical modeling and machine learning systems trained on millions of transaction records. These tools calculate standard deviations from baseline activity, identify timing interval consistency, and score cross-account synchronization patterns. Blockchain-specific analysis examines gas prices, nonce sequencing, and confirmation timing for additional automation indicators. Specialized forensic teams also develop proprietary algorithms targeting emerging automation techniques.
How quickly can velocity analysis identify an active automated operation?
Once monitoring systems flag a velocity anomaly, initial automation confirmation typically occurs within 24-48 hours. Real-time monitoring can generate alerts within minutes when transactions exceed velocity thresholds such as 10 or more transfers per minute sustained over several minutes. Full network mapping and infrastructure identification requires 1-3 weeks depending on the operation’s complexity, geographic spread, and the number of accounts involved. Early detection dramatically improves crypto asset recovery outcomes.
Do transaction velocity patterns differ across Bitcoin, Ethereum, and other blockchains?
Each blockchain has distinct velocity characteristics based on confirmation times, transaction fees, and smart contract capabilities. Bitcoin transactions typically confirm in 10-minute blocks, creating natural velocity ceilings that shape automation patterns. Ethereum enables faster execution through smart contracts that trigger cascading operations within single blocks. Layer-2 solutions and alternative blockchains with faster finality allow even higher velocity operations, requiring investigators to calibrate detection thresholds for each chain’s technical architecture.
What happens after investigators confirm automated criminal activity?
Following confirmation, investigators map the complete bot network infrastructure, identify controlling entities and beneficial owners, and coordinate with exchanges and platforms to freeze accounts and prevent further fund distribution. The investigation team prepares court-admissible evidence packages documenting velocity patterns with statistical analysis. Simultaneously, they initiate asset recovery actions and file criminal referrals with relevant authorities including filing Suspicious Activity Reports under Bank Secrecy Act requirements.
Can automated velocity analysis detect cryptocurrency mixer and tumbler usage?
Automated mixers and tumblers create highly distinctive velocity signatures because they fragment deposits into hundreds of outputs, route each through multiple intermediate addresses, and reassemble funds at destinations – all within minutes. The fragmentation speed, consistent intermediate hop timing, and mathematical precision of amount splitting reveal mixer automation. Investigators at Crypto Trace Labs track these patterns through on-chain analysis, reconstructing the full transaction chain even when mixers attempt to obscure fund origins.
What is the difference between velocity analysis and traditional transaction monitoring?
Traditional transaction monitoring primarily examines individual transactions against static rules – checking amounts against thresholds, screening counterparties, and flagging geographic risk. Velocity analysis instead examines the relationships between transactions over time, identifying patterns in frequency, timing precision, and cross-account coordination that reveal automated orchestration. This temporal perspective catches automated operations that pass individual transaction checks but exhibit statistically impossible collective behavior when viewed as a sequence.
How do smart contracts enable automated money laundering?
Smart contracts allow criminals to program complex multi-step laundering sequences that execute automatically when triggered by a single deposit. A criminal deploys code that splits incoming funds across dozens of addresses, swaps between cryptocurrencies through decentralized exchanges, interacts with DeFi lending protocols, and distributes to final destinations – completing 40 or more operations in under 90 seconds without any further human involvement. These contract-driven cascades generate distinctive velocity signatures that blockchain forensics teams identify through code analysis and execution tracing.
Are financial institutions legally required to detect automated transaction patterns?
Under Bank Secrecy Act requirements and equivalent UK AML regulations and EU AML directives, financial institutions must maintain transaction monitoring systems capable of detecting velocity anomalies. When automated alerts identify impossible transaction speeds or patterns, compliance teams must investigate and file Suspicious Activity Reports. Failure to detect obvious automation signatures constitutes a compliance deficiency that can result in regulatory penalties, enforcement actions, and reputational damage for the institution.
How effective is velocity analysis at recovering stolen cryptocurrency?
Velocity analysis significantly improves recovery outcomes because automated operations leave mathematical evidence trails that are difficult to erase from blockchain records. By identifying bot network infrastructure quickly, investigators can coordinate with exchanges such as Coinbase, Kraken, and others to freeze funds before automated distribution completes. Speed matters enormously – operations that begin velocity analysis within 24-48 hours of theft achieve substantially higher recovery rates than delayed investigations. Non-custodial wallet recovery cases particularly benefit from rapid velocity pattern identification.
What training do compliance professionals need for velocity pattern detection?
Effective velocity analysis requires statistical literacy, blockchain technology understanding, and familiarity with automation techniques used by criminal operations. ACAMS-certified professionals receive foundational training in transaction monitoring, while specialized courses in blockchain analytics and computational forensics address velocity-specific detection methods. Compliance teams benefit from regular exposure to real case studies, hands-on practice with detection platforms, and collaboration with experienced forensic investigators who understand both the mathematical and operational aspects of automated criminal systems.
Don’t Let Automated Criminals Steal Your Assets – Act Now
Automated criminal operations move faster than traditional investigations. While compliance teams review documentation and investigators request records, sophisticated bots have already distributed your stolen cryptocurrency across 500 addresses in 37 countries. Every minute of delay reduces recovery probability.
Why Velocity Analysis Expertise Matters:
Traditional investigators lack tools and training to detect automated operations. They analyze transactions individually rather than identifying the velocity signatures proving coordination. Our team uses specialized blockchain forensics platforms and velocity detection algorithms that standard compliance departments don’t have access to.
Crypto Trace Labs Automated Operation Detection:
Our investigators don’t just identify automation – we reverse-engineer criminal infrastructure. With VP and Director-level experience from Blockchain.com, Kraken, and Coinbase, we’ve dismantled sophisticated bot networks, traced smart contract automated layering, and recovered assets from high-frequency laundering operations.
What We Deliver:
- Real-time velocity monitoring detecting automated operations within hours, not weeks
- Bot network mapping exposing complete criminal infrastructure and control points
- Smart contract analysis reconstructing automated transaction sequences across DeFi protocols
- Cross-chain velocity tracking following high-speed operations across Bitcoin, Ethereum, and privacy coins
- Exchange coordination leveraging executive relationships to freeze accounts before automated distribution completes
- Evidence packages documenting velocity patterns with court-admissible statistical analysis
Our Automation Detection Track Record:
- Identified and disrupted automated mixer operations processing $8M+ weekly
- Recovered assets from smart contract automated theft within 72 hours of deployment
- Mapped bot networks controlling 200+ accounts across 15 exchanges
- Average 60% faster automation detection versus industry standard compliance teams
Time-Sensitive Opportunity:
Automated operations complete in hours. We start velocity analysis immediately upon engagement, often identifying bot signatures and distribution patterns within 24-48 hours. Our team works around the clock when automation is active, maximizing asset recovery probability.
No Upfront Fees for Non-Custodial Wallet Recovery – You only pay after we successfully recover your funds. For velocity analysis and automation detection services, we offer transparent project-based pricing with no hidden costs.
Get Immediate Velocity Analysis – Free 30-Minute Assessment
Tell us what happened. We’ll analyze velocity patterns, explain automation indicators we detect, and provide honest recovery probability assessment. No obligation. No sales pressure. Just expert analysis from investigators who’ve tracked hundreds of automated criminal operations.
Why wait and lose more? Automated criminals don’t sleep. Neither do we.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- When Cryptocurrency Transactions Become Suspicious
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- How to Trace Cryptocurrency Through Mixers: Expert Guide
About the Author
This guide was prepared by the blockchain forensics and automated operation detection team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, automated fraud detection, and high-frequency transaction monitoring.
Our team holds ACAMS certifications (Certified Anti-Money Laundering Specialists), MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed velocity patterns in thousands of criminal investigations, identified and disrupted automated bot networks, and developed proprietary algorithms detecting automation signatures standard compliance systems miss.
For professional blockchain forensics, automated operation detection, or velocity pattern analysis, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Automated operation detection and asset recovery outcomes depend on specific circumstances, criminal sophistication, and response timing. Consult qualified professionals regarding your situation.