Last updated: March 2026
On-chain analysis without enterprise tools refers to blockchain investigation using open-source software, public blockchain explorers, and free-tier APIs rather than commercial platforms such as Chainalysis Reactor or Elliptic Forensics. Open-source methods can produce meaningful investigative insights for a wide range of cases, particularly in the early stages of an investigation, on chains with good public explorer support, and for analysts who understand the methodological limitations involved. The critical distinction is that open-source analysis cannot substitute for enterprise tool outputs in court proceedings, where platform version, attribution database, and audit trail documentation are required.
Crypto Trace Labs uses enterprise tools as the primary investigation platform for all court-bound work, but incorporates open-source methods for preliminary analysis, chain verification, and supplementary investigation across chains not covered by commercial platforms. This guide is for security researchers, OSINT analysts, law enforcement officers in resource-constrained environments, and compliance professionals who need to understand open-source investigation capabilities and their limits.
Key Takeaways
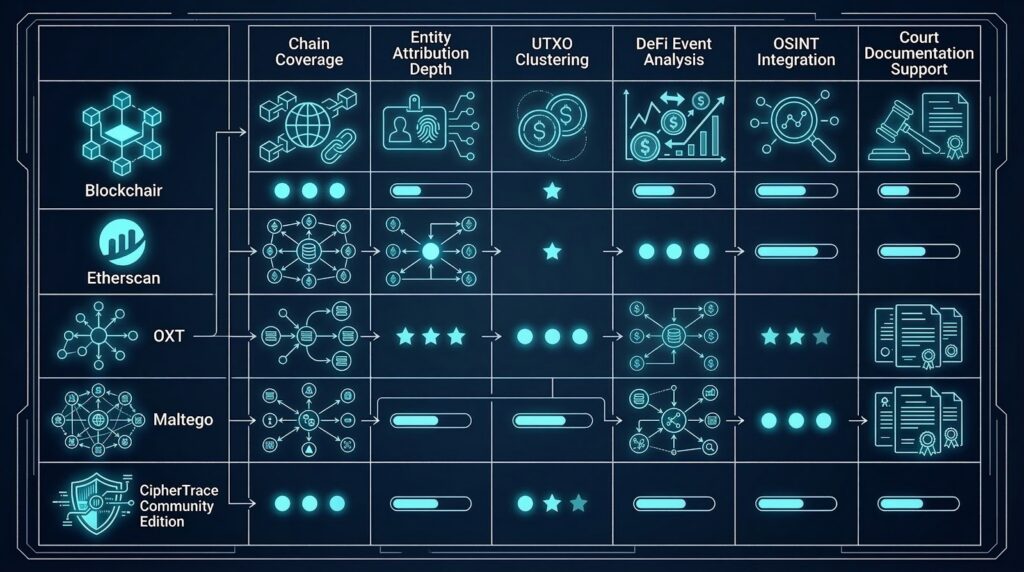
- Blockchain explorers including Etherscan, Blockchair, and OXT provide free on-chain data access for Bitcoin, Ethereum, and many other chains without requiring commercial licences
- Maltego is the most widely used open-source investigation platform for combining on-chain data with OSINT and social graph analysis, with blockchain-specific transforms available
- Open-source methods work best for preliminary analysis, transaction verification, and chains with limited commercial tool coverage
- Entity attribution without enterprise databases is significantly weaker – open-source tools have no access to exchange cooperation data, confirmed KYC-linked address clusters, or proprietary heuristic databases
- Court admissibility limitations are significant – open-source analysis lacks the documented methodology, platform audit trails, and attribution confidence standards required for most court proceedings
Why This Matters
Not every investigation has the budget for enterprise blockchain analytics licences, and not every investigation needs them. Security researchers, small law enforcement units, compliance teams at smaller regulated firms, and OSINT analysts conducting preliminary investigations benefit from understanding what open-source methods can achieve. The FATF (2024) has noted that open-source investigation capability is uneven across member states, with under-resourced agencies in some jurisdictions conducting cryptocurrency investigations without access to commercial tools. Understanding the capability ceiling of open-source methods – and when that ceiling requires escalation to enterprise tools – is essential knowledge for any blockchain investigator.

Blockchain Explorers as Primary Data Sources
Blockchain explorers are the foundational open-source data source for on-chain analysis, providing free public access to transaction data, address balances, and block information. The key explorers by chain are: Blockchair (multi-chain, supports Bitcoin, Ethereum, Litecoin, Dash, Zcash, and 18 other chains), Etherscan (Ethereum and EVM-compatible chains with full ERC-20 and smart contract event log access), OXT (Bitcoin-specific with advanced clustering visualisation), Mempool.space (Bitcoin mempool and transaction fee analysis), Solscan (Solana), and Tronscan (Tron). Each explorer provides slightly different data views and search capabilities, and investigators often cross-reference multiple explorers for the same address to ensure complete data.
For Bitcoin UTXO-based investigation, OXT provides the most useful visualisation of transaction graphs and UTXO clustering patterns without requiring a commercial licence. For Ethereum and ERC-20 investigations, Etherscan provides complete smart contract event log access, making it the primary tool for NFT tracing and DeFi event analysis.
Maltego for Open-Source Blockchain Investigation
Maltego is a graph-based investigation and visualisation platform widely used by law enforcement, OSINT analysts, and security researchers to combine data from multiple sources into a unified investigation graph. For blockchain investigation, Maltego provides blockchain-specific transforms through partners including Etherscan, Blockchain.com, and third-party transform hubs. Investigators can pivot from a wallet address to its transaction history, connected addresses, associated IP addresses from public node data, and social media profiles where addresses have been published. Maltego’s strength is in combining on-chain data with off-chain OSINT – connecting blockchain addresses to social media usernames, forum posts, exchange profiles, and domain registration data.
Maltego does not provide enterprise-level entity attribution and cannot access the proprietary databases used by Chainalysis or Elliptic. Its value is in OSINT correlation and visualisation rather than blockchain-specific heuristic analysis.
Common Input Ownership Analysis Without Enterprise Tools
Common input ownership heuristic analysis – the foundational clustering technique used by all enterprise blockchain forensic platforms – can be performed manually using blockchain explorer data and scripting. The method groups Bitcoin addresses that appear as inputs in the same transaction, inferring they are controlled by the same wallet. For small investigations involving a limited number of transactions, this can be done manually using Blockchair data exports or the OXT clustering visualisation. For larger investigations, Python scripts using the Bitcoin RPC API or Blockchair’s bulk data API can automate co-spend analysis across larger transaction sets.
The limitation of manual common input ownership analysis compared to enterprise tools is the absence of the broader clustering database. Enterprise tools cross-reference each cluster against billions of previously identified address groups, providing entity attribution that manual analysis cannot replicate. For address clustering techniques in depth, see our dedicated guide on how investigators group wallet addresses.
Open-Source Tools for Ethereum and DeFi Analysis
For Ethereum and DeFi investigation without enterprise tools, the primary resources are Etherscan, The Graph (a decentralised indexing protocol providing GraphQL query access to on-chain event data), Dune Analytics (SQL-based on-chain data querying for advanced users), and DeBank (DeFi portfolio and protocol interaction history for any address). Etherscan provides complete transaction history, ERC-20 token transfers, internal transactions, and smart contract event logs for any Ethereum address. The Graph and Dune Analytics allow analysts to query specific protocol interactions across large data sets that would be impractical to examine manually through Etherscan.
For smart contract event log analysis related to NFT theft or DeFi investigation, Etherscan’s event log viewer is sufficient for most preliminary analysis, though enterprise tools are required for the entity-level attribution of counterparty wallets.
Limitations for Court Proceedings
The most significant limitation of open-source blockchain analysis for court proceedings is the absence of the documentation, audit trails, and attribution confidence standards required for forensic evidence. Enterprise platforms such as Chainalysis Reactor maintain version-controlled attribution databases, investigation audit trails, and documented methodology frameworks that courts can evaluate. Open-source analysis using Etherscan data lacks a comparable documentation standard. Additionally, the entity attribution available through open-source tools is limited to labelled addresses published on explorers or in OSINT databases – there is no equivalent to the exchange cooperation data that underlies enterprise attribution.
Open-source analysis is appropriate for: generating investigative leads for further investigation with enterprise tools, preliminary triage to determine whether a case warrants enterprise tool investment, secondary verification of enterprise tool findings, and investigation of chains with limited or no commercial tool coverage.
| Use Case | Open-Source Sufficient | Enterprise Tools Required |
|---|---|---|
| Preliminary address triage | Yes | No |
| Transaction flow mapping | Partially | For complex cases |
| Entity attribution | No | Yes |
| Court-admissible reporting | No | Yes |
| DeFi protocol tracing | Partially (Etherscan) | For attribution |
| Privacy coin investigation | Very limited | Yes (heuristics) |
| Cross-chain bridge tracing | Very limited | Yes |
| OSINT correlation | Yes (Maltego) | Supplementary |
Frequently Asked Questions
What blockchain explorer is best for Bitcoin investigation?
OXT is the most capable free blockchain explorer for Bitcoin investigation, providing transaction graph visualisation, UTXO clustering displays, and address reuse analysis without requiring a commercial licence. Blockchair provides multi-chain coverage and bulk data export functionality useful for larger investigations. Blockchain.com provides basic address and transaction lookup. For investigators needing to verify specific transaction hashes and follow Bitcoin flows without enterprise tools, OXT combined with Blockchair provides the most complete free-tier capability. Neither substitutes for enterprise tool entity attribution on complex cases.
Can Etherscan be used for forensic investigation?
Yes. Etherscan provides complete transaction history, ERC-20 token transfer logs, internal transaction data, and smart contract event logs for any Ethereum address, making it a valuable forensic tool for preliminary analysis, transaction verification, and NFT theft investigation. Etherscan does not provide entity attribution beyond its own labelling of known addresses – it cannot access the proprietary exchange cooperation data that Chainalysis and Elliptic use for entity attribution. For court-bound work, Etherscan data should be corroborated by enterprise tool analysis and is not sufficient as a standalone forensic evidence source.
What is Maltego used for in blockchain investigation?
Maltego is a graph-based investigation platform that combines blockchain data with OSINT sources including social media, domain records, IP address data, and forum posts. In blockchain investigation, Maltego uses transforms to pivot from wallet addresses to transaction data, connected addresses, associated identities published alongside addresses online, and node IP data from public P2P network records. Its primary value is in correlating on-chain data with off-chain identity indicators rather than blockchain-specific heuristic analysis. Maltego does not provide enterprise-level entity attribution and cannot replicate the exchange cooperation data underlying commercial forensic platforms.
What is the difference between open-source and enterprise blockchain analysis?
Open-source blockchain analysis uses public blockchain explorers, free APIs, and open-source software without access to proprietary entity attribution databases, exchange cooperation data, or documented forensic methodology frameworks. Enterprise blockchain analysis using Chainalysis Reactor or Elliptic Forensics provides access to attribution databases containing billions of clustered addresses with entity-level labelling drawn from exchange partnerships, darknet monitoring, and heuristic databases built over years of use. Enterprise tools also provide documented audit trails and court-format reporting that open-source tools do not replicate. Open-source methods are suitable for preliminary investigation and research; enterprise tools are required for court proceedings.
Can open-source blockchain analysis be used as evidence in court?
Open-source blockchain analysis has significant limitations as court evidence. The primary issues are the absence of documented methodology frameworks, version-controlled attribution databases, and audit trail records that courts require for forensic evidence. Transaction data from explorers like Etherscan is admissible as documentary evidence since it reflects immutable public blockchain records. However, entity attribution conclusions reached through open-source analysis cannot meet the methodology documentation standards required by CPR Part 35 without supplementary enterprise tool support. Open-source findings are more appropriate as investigative leads that are then developed using enterprise tools for court-bound investigation.
What open-source tools work for Ethereum DeFi investigation?
For Ethereum DeFi investigation without enterprise tools, Etherscan provides complete transaction and event log data. The Graph provides GraphQL query access to specific DeFi protocol data across Uniswap, Aave, and other protocols. Dune Analytics enables SQL queries across on-chain DeFi data for analysts with SQL experience. DeBank displays complete DeFi portfolio and protocol interaction history for any address. These tools provide transaction-level data but lack the entity attribution that enterprise tools apply to DeFi counterparties. For attributing DeFi swap counterparties to known exchanges or illicit services, Elliptic Forensics or TRM Labs are required.
Is Blockchair free to use for investigation?
Blockchair provides free access to its blockchain explorer for manual lookups across 19 supported chains. For bulk data access, API queries beyond the free tier, and data export functionality suitable for larger investigations, Blockchair offers paid API plans starting at accessible price points significantly below enterprise forensic platform licences. Blockchair does not provide entity attribution beyond its own address labelling. For investigators needing multi-chain transaction data access beyond single address lookups – such as downloading full transaction histories for clustering analysis – Blockchair’s API plans represent good value as a supplementary tool alongside enterprise platforms.
What Python libraries are available for blockchain analysis?
Several Python libraries support open-source blockchain analysis. bitcoin-explorer provides Bitcoin node RPC interface access. web3.py is the standard Ethereum blockchain interaction library, enabling smart contract event log queries and address balance checks. blockchair-python wraps the Blockchair API for multi-chain data access. For graph analysis of transaction networks, NetworkX provides graph algorithms applicable to transaction graph clustering. For visualisation, Gephi (Java-based but Python-accessible) and pyvis provide network graph rendering. These libraries enable investigators to automate transaction data collection and co-spend analysis, but do not provide entity attribution without additional labelled dataset integration.
What are the limitations of manual co-spend analysis?
Manual common input ownership analysis identifies Bitcoin addresses that co-appear as inputs in the same transaction, but it has significant limitations compared to enterprise tools. Manual analysis only captures co-spend relationships visible in the specific transaction set being examined – it has no access to the broader clustering database that enterprise tools maintain across all historical Bitcoin transactions. Large-scale clusters that were built through many transactions over years will not be identified by manual analysis of a limited transaction set. Additionally, manual clustering cannot verify or contradict attributions with exchange-confirmed identity data, making the resulting clusters investigative leads rather than confirmed attributions.
When should investigators upgrade from open-source to enterprise tools?
Investigators should upgrade from open-source to enterprise tools when: the investigation requires entity attribution beyond what open-source labelling can provide, the findings will be used as court evidence requiring documented methodology and attribution confidence standards, the transaction flows involve DeFi protocols or cross-chain bridges that open-source tools cannot trace reliably, the investigation involves privacy coins where heuristic databases are required, or the investigation scope is too large for manual analysis to be practical. Open-source tools are appropriate for preliminary triage, research, and supplementary verification – not for primary investigative conclusions in consequential proceedings.
Executive Summary
Open-source blockchain analysis using tools including Etherscan, OXT, Blockchair, and Maltego can provide meaningful investigative capability for preliminary triage, transaction verification, and OSINT correlation without enterprise tool licences. The fundamental limitations are entity attribution depth and court admissibility – open-source tools cannot access exchange cooperation databases, confirmed KYC-linked cluster data, or produce the documented methodology audit trails required for forensic evidence in court proceedings. Open-source methods are appropriate as a starting point, for resource-constrained environments, and for chains with limited commercial tool coverage. Enterprise tools are required for court-bound work and complex attribution on primary chains.
What Should You Do Next?
Understanding open-source methods and their limitations helps investigators make informed decisions about when to escalate to enterprise tools and specialist forensic firms. For investigations that begin with open-source analysis and develop into court-bound proceedings, the transition to enterprise tools and qualified forensic experts should happen early enough to allow proper methodology documentation from the outset.
Crypto Trace Labs uses enterprise-grade tools across all court-bound investigations and can advise on when open-source preliminary work is sufficient versus when specialist forensic investigation is required. Our ACAMS-accredited team can review open-source investigation findings and advise on the additional work needed for court-admissible outputs. Contact Crypto Trace Labs to discuss your investigation requirements.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- Chainalysis vs Elliptic vs TRM Labs vs Crystal Intelligence: Platform Comparison
- How Do Investigators Use Address Clustering to Link Crypto Wallets?
- What UK Courts Require from Cryptocurrency Tracing Reports
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm founded by VP and Director-level executives formerly of Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across the UK, US, and EU, and Chartered Fellow Grade status at the CMI. With over 10 years of experience in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin for clients in the last 12 months and delivered record fraud reduction for a $14bn crypto exchange. We work with law enforcement agencies, regulated financial institutions, and private clients on crypto asset recovery, blockchain forensics, AML compliance, and expert witness testimony – globally. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





