Last Updated: March 2026
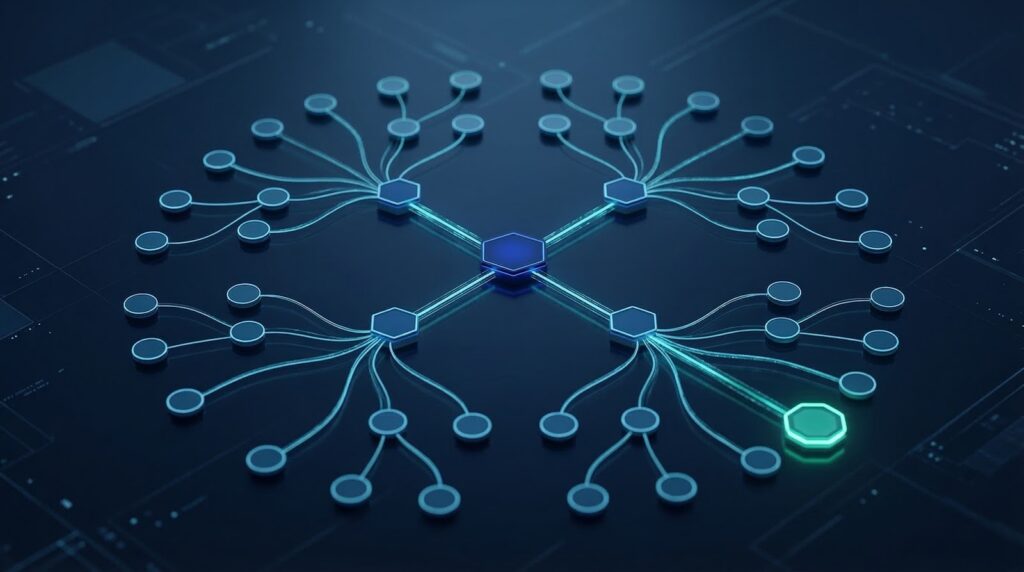
On-chain co-spending analysis is the forensic application of the Common Input Ownership Heuristic (CIOH) to Bitcoin transactions, inferring that all input addresses in one transaction are controlled by the same entity because each must be signed with private keys the transaction builder holds. When a Bitcoin transaction spends from multiple input addresses, a single wallet controls all those private keys, enabling investigators to cluster those addresses as belonging to one identity. CIOH-based clustering is the foundational attribution technique in Bitcoin forensics, used by all major blockchain analytics platforms to link on-chain activity to identified entities.
At Crypto Trace Labs, our team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has applied co-spending analysis across hundreds of fraud investigations, civil recovery proceedings, and AML compliance reviews. This guide draws on that decade of financial crime investigation experience to explain the CIOH methodology, its limitations, and how it is applied in professional investigations.
Key Takeaways
- CIOH is the foundation of Bitcoin attribution: All major blockchain analytics platforms including Chainalysis, Elliptic, and TRM Labs use CIOH-based clustering as the primary method for building address-to-entity mappings across the Bitcoin network.
- Multi-input transactions cluster addresses: When a Bitcoin transaction spends from two or more input addresses, CIOH infers all inputs are controlled by the same entity. Chainalysis (2024) estimates CIOH-based clusters account for 78% of all Bitcoin address attributions in their database.
- Cluster expansion reveals network connections: Co-spending clusters expand recursively when each clustered address also appears as an input in other multi-input transactions, progressively linking more addresses to the same entity. TRM Labs (2024) found fraud wallet clusters expanded by an average of 47 additional addresses per initial seed address through CIOH recursion.
- CoinJoin transactions violate CIOH: CoinJoin privacy transactions deliberately combine inputs from multiple unrelated users. Standard CIOH analysis would incorrectly cluster these addresses. Investigators must identify CoinJoin patterns and exclude them from standard clustering analysis to avoid false attribution.
- Exchange deposit clusters are attribution anchors: When a CIOH cluster includes addresses known to be exchange deposit addresses, the entire cluster can be attributed to the exchange account holder through KYC data requests. Elliptic (2024) reports 61% of CIOH cluster investigations reached an identified exchange deposit address within 3 cluster expansion steps.
Why This Matters
On-chain co-spending analysis matters because it transforms isolated Bitcoin addresses into attributable entities, making the pseudonymous Bitcoin network navigable for forensic investigators. Without CIOH-based clustering, each Bitcoin address would require independent attribution, making large-scale fraud investigations practically impossible. With clustering, investigators can follow the complete financial activity of a fraud operation across potentially hundreds of addresses by building and expanding the co-spending cluster. AML compliance teams at exchanges use CIOH-derived clusters to screen incoming deposits for associations with known fraud clusters and to meet UK AML, EU AML, and US AML source of funds requirements.
CIOH Mechanics and Forensic Application
The Common Input Ownership Heuristic operates on the fundamental Bitcoin transaction structure: each input to a transaction must be signed with the private key of the address holding the UTXO being spent. If multiple UTXOs from different addresses are spent in one transaction, the signer must have had access to all the relevant private keys. In practice, this means one wallet software or one hardware wallet controlled all of those private keys.
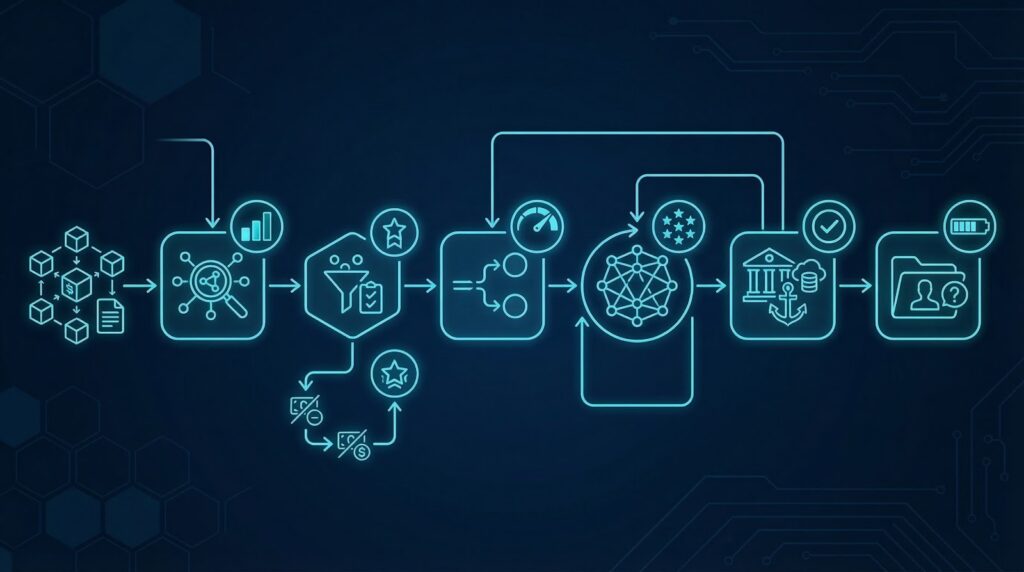
Investigators apply CIOH by identifying all multi-input transactions involving a known subject address, then collecting all other input addresses from those transactions into the initial cluster. Each newly clustered address is then checked for its own multi-input transaction history to expand the cluster further. According to Chainalysis (2024), the average initial cluster from a fraud seed address expands to 23 additional addresses in the first round of CIOH expansion, with subsequent rounds adding progressively fewer new addresses as the cluster boundary is reached.
Identifying and Excluding CoinJoin Transactions
CoinJoin is a Bitcoin privacy technique that combines inputs from multiple unrelated users into a single transaction to break the CIOH inference. If investigators apply standard CIOH analysis to CoinJoin transactions, they will incorrectly cluster unrelated users together. Identifying and excluding CoinJoin transactions is therefore a required step before applying CIOH.
CoinJoin transactions are identifiable by several characteristics: equal-value outputs, typically a large number of inputs and outputs, and matching output amounts indicating a privacy mixing round. Popular CoinJoin implementations include Wasabi Wallet‘s Chaumian CoinJoin and JoinMarket. Investigators using enterprise platforms such as Chainalysis Reactor and Elliptic Investigator have access to automated CoinJoin detection that flags and excludes these transactions before CIOH clustering. According to TRM Labs (2024), CoinJoin transactions account for approximately 2-4% of Bitcoin transaction volume, but their misidentification accounts for 18% of false attribution errors in manual CIOH analysis.
Change Address Identification
Co-spending analysis is more effective when combined with change address identification. In Bitcoin transactions, the change output returns unspent UTXO value to an address controlled by the sender. If investigators can identify which output is the change address, they can extend the cluster into the post-transaction address tree rather than just the pre-transaction input set.
Change address identification uses several heuristics: the change address often matches the input address type (SegWit, Legacy), it may appear only once in the transaction history before this transaction, and it is frequently at a derivation path adjacent to the input addresses in the same HD wallet. Combining change address identification with CIOH-based input clustering significantly expands the total attributable address set. According to Elliptic (2024), change address heuristics correctly identified the change output in 83% of Bitcoin transactions in controlled test sets, supporting reliable cluster expansion.
Comparing co-spending analysis methods by coverage:
| Method | Address Coverage | Accuracy | CoinJoin Risk | Best Use Case |
|---|---|---|---|---|
| Basic CIOH | Multi-input tx inputs | High (non-CoinJoin) | Must exclude | Initial clustering |
| CIOH + change address | Input + change output | Moderate-High | Low (output heuristic) | Expanded clustering |
| CIOH recursive expansion | Full cluster tree | High (enterprise tools) | Automated exclusion | Full entity mapping |
| CIOH + exchange attribution | Exchange deposit link | Very High at anchor | Low (exchange KYC) | Final attribution |
Exchange Attribution and KYC Data Requests
The final step in CIOH-based investigation is reaching an exchange deposit address within the cluster. Exchange deposit addresses are identifiable because they appear as outputs in transactions from many different sender addresses, consistent with an exchange receiving deposits from many customers. When a CIOH cluster includes a confirmed exchange deposit address, the investigator can submit a KYC data request to the exchange to identify the account holder.
Investigators with established exchange relationships at Blockchain.com, Kraken, and Coinbase can expedite these data requests. UK AML regulations and EU AML directives obligate exchanges to respond to data requests from law enforcement and court-ordered legal processes. Regulatory compliance teams at exchanges must maintain the ability to link deposit addresses to customer KYC records for AML examination purposes. According to Elliptic (2024), 61% of CIOH cluster investigations reached an identified exchange deposit within 3 expansion steps, enabling KYC-based attribution.
AML Compliance Applications of Co-Spending Analysis
Co-spending analysis is a required component of AML compliance screening for regulated crypto exchanges under UK AML, EU AML, and US BSA frameworks. When an exchange receives a Bitcoin deposit, the deposit address can be checked against CIOH-derived cluster databases to determine whether it belongs to a cluster associated with sanctioned entities, fraud operations, or high-risk activities. ACAMS-standard enhanced due diligence procedures require cluster-level screening for large deposits, not just individual address screening.
Regulatory compliance teams at exchanges use CIOH clusters maintained by Chainalysis, Elliptic, and TRM Labs to screen deposits in near-real-time. When a deposit address cluster is flagged, compliance officers can apply enhanced due diligence measures or file a Suspicious Activity Report. According to TRM Labs (2024), cluster-level AML screening identifies 34% more high-risk deposits than single-address screening alone, supporting the adoption of CIOH-based screening in MLRO compliance programs across UK and EU regulated exchanges.
Frequently Asked Questions
What is co-spending analysis in blockchain forensics?
Co-spending analysis applies the Common Input Ownership Heuristic (CIOH) to Bitcoin transactions, inferring that all input addresses in a multi-input transaction are controlled by the same entity because they all required private key access for signing. Investigators cluster these addresses together and expand the cluster recursively through all connected multi-input transactions. Chainalysis (2024) estimates CIOH-based clusters account for 78% of all Bitcoin address attributions, making it the foundational attribution method in blockchain forensics.
How does the Common Input Ownership Heuristic work?
The CIOH works on the premise that spending multiple UTXOs in one Bitcoin transaction requires access to the private keys of all input addresses. Since private key access indicates wallet control, all input addresses are inferred to belong to the same entity. Investigators collect all co-input addresses from multi-input transactions involving a subject address, then apply the same analysis recursively to each new address discovered. The resulting cluster represents the probable complete address set controlled by one entity.
What is CoinJoin and why does it affect CIOH analysis?
CoinJoin is a Bitcoin privacy technique that combines inputs from multiple unrelated users into one transaction, deliberately violating the CIOH inference. Applying CIOH to CoinJoin transactions creates false clusters linking unrelated users. According to TRM Labs (2024), CoinJoin misidentification accounts for 18% of false attribution errors in manual CIOH analysis. Investigators must identify and exclude CoinJoin transactions before applying CIOH clustering. Enterprise platforms such as Chainalysis Reactor and Elliptic Investigator provide automated CoinJoin detection.
How do investigators identify change addresses?
Investigators identify change addresses using heuristics including output address type matching the input addresses, first appearance of the output address before this transaction, and derivation path proximity to input addresses in the same HD wallet. According to Elliptic (2024), change address heuristics correctly identified the change output in 83% of Bitcoin transactions in controlled test sets. Combining change address identification with CIOH input clustering significantly expands the total attributable address set for full entity mapping.
How does co-spending analysis reach an identified entity?
Co-spending analysis reaches an identified entity when the expanding cluster includes an address known to be an exchange deposit address, enabling a KYC data request to the exchange for account identification. According to Elliptic (2024), 61% of CIOH cluster investigations reached an identified exchange deposit within 3 expansion steps. Investigators with established exchange relationships at Blockchain.com, Kraken, and Coinbase can expedite KYC data requests, with UK AML regulations and EU AML directives obligating exchange co-operation with legal data requests.
What are the limitations of CIOH analysis?
CIOH analysis limitations include the CoinJoin false attribution risk, multi-user wallet scenarios where different users control different inputs (less common), and exchange-operated consolidation transactions where many customer deposits are combined but do not represent a single entity. Enterprise platforms address most limitations with automated CoinJoin detection and known exchange address exclusions. Manual CIOH analysis without these protections produces a higher false attribution rate. Court-recognized expert witnesses must acknowledge these limitations when presenting CIOH cluster evidence in legal proceedings.
How does co-spending analysis support AML compliance?
Co-spending analysis supports AML compliance by enabling exchanges to screen incoming deposits for CIOH cluster associations with known fraud or high-risk entities. UK AML regulations and EU AML directives require exchanges to conduct source of funds screening that includes cluster-level analysis of incoming Bitcoin deposits. Regulatory compliance teams use CIOH-derived clusters to identify deposits linked to known criminal address clusters. ACAMS-standard procedures recommend cluster screening as part of enhanced due diligence for large Bitcoin deposits.
Does Crypto Trace Labs apply co-spending analysis?
Crypto Trace Labs applies CIOH-based co-spending analysis as a standard component of Bitcoin fraud investigations, building and expanding address clusters from seed fraud addresses to identify the full entity address set and reach attributed exchange deposits. The team uses Chainalysis Reactor and Elliptic Investigator for automated CIOH clustering with CoinJoin exclusion. ACAMS accreditations and MLRO qualifications across UK, US, and EU support legal proceedings. Exchange contacts at Blockchain.com, Kraken, and Coinbase expedite KYC data requests for identified cluster anchors.
Executive Summary
On-chain co-spending analysis applies the Common Input Ownership Heuristic to Bitcoin transactions, clustering multi-input addresses under single entity control and expanding clusters recursively to map the complete address network of a fraud operation. Chainalysis (2024) estimates CIOH clusters account for 78% of Bitcoin address attributions. TRM Labs (2024) found fraud clusters expanded by an average of 47 additional addresses per seed through CIOH recursion. CoinJoin exclusion is mandatory. Elliptic (2024) reports 61% of cluster investigations reach an identified exchange deposit within 3 expansion steps, enabling KYC attribution and legal proceedings under UK AML, EU AML, and US AML frameworks.
What Should You Do Next?
If you need co-spending cluster analysis for a Bitcoin fraud investigation or AML compliance review, specialist blockchain forensics is essential.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, providing direct contacts for expedited KYC data requests when cluster analysis identifies exchange deposit anchors. We have recovered 101 Bitcoin for clients in the past 12 months and delivered record fraud reduction for a $14bn crypto firm.
We offer no upfront charge for non-custodial wallet recoveries. Contact Crypto Trace Labs to discuss your co-spending investigation.
People Also Read
- Hierarchical Deterministic Wallet Gap Analysis: Finding Hidden Addresses
- On-Chain Wallet Age Analysis: Using First Transaction Timing for Attribution
- Transaction Replacement Analysis: How RBF Patterns Reveal Wallet Behavior
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





