Last Updated: March 2026
Smart contract event log analysis is the forensic process of querying and interpreting event logs emitted by Ethereum smart contracts to reconstruct on-chain activity, identify the parties involved in specific transactions, and build evidential chains for fraud investigations and legal proceedings. Every interaction with an Ethereum smart contract that triggers a defined event produces a permanent indexed log in the transaction receipt. These event logs are more granular than standard transfer records, capturing state changes, parameter values, and actor addresses that enable investigators to reconstruct exactly what happened in a DeFi protocol, token contract, or exchange interaction.
At Crypto Trace Labs, our team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has applied smart contract event log analysis across DeFi fraud investigations, civil asset recovery proceedings, and AML compliance reviews for regulated exchanges. This guide draws on that decade of financial crime investigation experience to explain the forensic methods investigators and compliance teams need to understand.
Key Takeaways
- Event logs are the primary DeFi evidence source: Chainalysis (2024) confirms smart contract event logs are the primary data source for 78% of DeFi-related fraud investigations on Ethereum, because they capture protocol-specific state changes not visible in standard transaction data.
- Indexed parameters enable direct address queries: Events with indexed address parameters allow investigators to query all events involving a specific address across all contracts in one query, enabling rapid network reconstruction without manual transaction inspection.
- Custom events reveal protocol-specific intelligence: DeFi protocols define custom events for governance, liquidity management, and reward distribution. Forensic analysis of custom events can reveal flash governance attacks, liquidity manipulation, and protocol-specific fraud patterns not detectable from Transfer events alone.
- Event signatures identify contract interactions: Each event type has a unique 32-byte signature (Keccak256 hash of the event name and parameters). Investigators use known event signatures to identify which protocol functions were invoked in complex multi-contract transactions.
- Log data can be deleted by contract upgrades: Elliptic (2024) warns that upgradeable proxy contracts can change event implementations, potentially creating gaps in future queries. Investigators working on cases involving upgradeable contracts must verify event log continuity.
Why This Matters
Smart contract event log analysis matters because DeFi protocols generate transaction activity that is fundamentally different from standard cryptocurrency transfers and requires protocol-specific forensic methods to interpret correctly. A compliance team examining a wallet’s transaction history without analysing the event logs it generated will miss the actual DeFi activity – the swaps, liquidity additions, governance votes, and reward claims that reveal how the wallet was used. Legal proceedings involving DeFi fraud require event log evidence to establish what actions were taken in specific protocol contracts by identified wallet addresses.
Event Log Structure and Forensic Data Points
Every Ethereum event log contains four types of data that investigators query for forensic purposes. The contract address identifies which smart contract emitted the log. The event signature (topic[0]) identifies which specific event was emitted. The indexed parameters (topic[1], topic[2]) are the address or value fields declared as indexed in the event definition, enabling fast lookups. The non-indexed data field contains additional parameter values not available for direct queries.
Investigators access event log data through archive node queries using the eth_getLogs RPC method, or through enterprise analytics platforms such as Chainalysis Reactor and Elliptic Investigator, which index all event logs across active contracts. According to TRM Labs (2024), investigators querying a single suspect address’s indexed event log history across all contracts typically reconstruct 94% of the address’s DeFi activity within 30 minutes using automated platform queries, compared to days of manual transaction inspection.
Swap Event Analysis in DEX Investigations
Uniswap, SushiSwap, and other DEX protocols emit Swap events that record the amounts of each token exchanged, the pool address, and the initiating wallet address. Forensic investigators use Swap events to reconstruct the complete trading history of a suspect wallet across all DEX pools, establishing profit/loss figures and identifying potentially manipulative trading patterns such as wash trading or front-running.
Each Swap event contains the sender and recipient addresses, the token amounts in and out, and the pool’s reserve state at the time of the swap. Investigators correlating Swap event sequences across multiple blocks can identify coordinated trading patterns that would not be apparent from individual transaction records. According to Chainalysis (2024), Swap event analysis identified coordinated wash trading in 23% of DeFi manipulation investigations in 2023-2024, where multiple wallets traded the same token pair in circular patterns to inflate volume metrics.
Governance Event Forensics
DeFi governance protocols emit events for proposal creation, voting, and execution. These events create a complete audit trail of governance participation that is forensically significant in cases involving governance manipulation or flash governance attacks. A wallet that votes on a proposal immediately after acquiring governance tokens – as evidenced by Transfer events – demonstrates coordinated governance attack behaviour.
Investigators use governance event logs to establish the timeline of proposal creation, the wallets that voted, the voting weights applied, and whether the proposal was executed in the same block as the vote. This pattern – same-block proposal creation, vote, and execution – is the signature of a flash governance attack using borrowed tokens. According to TRM Labs (2024), flash governance attacks identified from event log analysis accounted for 12% of governance-related DeFi losses in 2023-2024.
Comparing event types by forensic application:
| Event Type | Protocol Examples | Forensic Use | Key Indexed Parameter | Investigation Scenario |
|---|---|---|---|---|
| Transfer | ERC-20 tokens | Fund flow tracing | from, to addresses | Fraud proceeds tracing |
| Swap | Uniswap, Curve | Trading pattern analysis | sender, recipient | Wash trading, front-running |
| Vote | Compound, Aave | Governance attack detection | voter address | Flash governance attacks |
| Borrow / Repay | Aave, Compound | Lending fraud | user address | Undercollateralised borrowing |
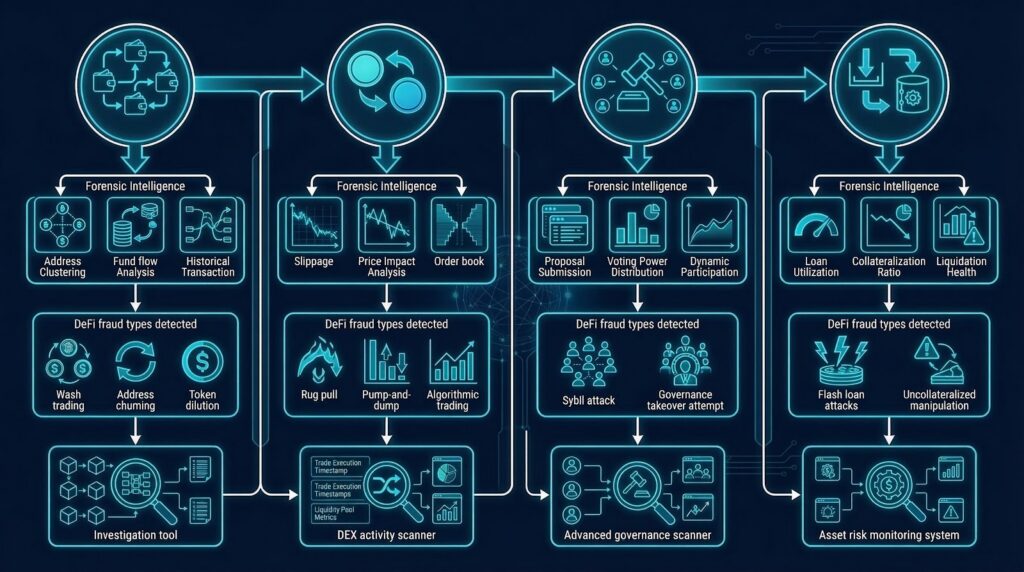
Reconstructing Multi-Contract Attack Sequences
Complex DeFi fraud often involves sequences of interactions across multiple contracts within a single transaction or across multiple blocks. Smart contract event log analysis can reconstruct these sequences by correlating events across contracts by transaction hash and block timestamp.
Investigators build the attack sequence by querying all event logs emitted within the attack transaction hash, then ordering them by their log index within the transaction receipt. Each event represents one step in the protocol interaction sequence. Correlating these steps with external reference data – such as token price oracles and DEX reserve states – allows investigators to calculate the exact financial impact of each step. According to Elliptic (2024), multi-contract attack sequences are fully reconstructable from event log data in 89% of DeFi fraud cases involving known protocol contracts, enabling exact victim loss quantification for legal proceedings.
AML Compliance and Legal Applications
Smart contract event log analysis supports AML compliance by providing the protocol-level interaction history required to assess the true risk profile of incoming DeFi-sourced deposits. UK AML regulations and EU AML directives require exchanges to conduct source of funds verification for deposits with DeFi origins. US AML requirements similarly apply to crypto platform deposits. Regulatory compliance teams must go beyond confirmed transaction records and query the event log history of source wallets to identify DeFi protocol interactions with known fraud or manipulation patterns.
For legal proceedings, event log evidence is admissible in UK and EU courts when presented by court-qualified expert witness professionals with ACAMS or MLRO qualifications. The immutable and complete nature of the Ethereum event log record means the underlying data cannot be disputed. Crypto Trace Labs – ACAMS-accredited, MLRO-qualified across UK, US, and EU, and Chartered Fellow Grade at the CMI – has provided court-recognized expert witness testimony in DeFi fraud cases using smart contract event log analysis.
Frequently Asked Questions
What is smart contract event log analysis?
Smart contract event log analysis is the forensic process of querying and interpreting the event logs emitted by Ethereum smart contracts to reconstruct on-chain activity and build evidential chains. Every smart contract interaction that triggers a defined event produces a permanent indexed log in the transaction receipt, capturing state changes, parameter values, and actor addresses. Forensic investigators use this data to reconstruct DeFi protocol interactions, identify parties to specific transactions, and support fraud investigations and legal proceedings.
How are smart contract event logs structured?
Smart contract event logs contain four key data fields: the contract address, the event signature (topic[0] as a Keccak256 hash), the indexed parameters (topic[1], topic[2]) enabling fast lookups, and the non-indexed data containing additional parameter values. Indexed parameters include actor addresses and key values declared in the event definition. Investigators query indexed parameters across all contracts to retrieve the complete event history for a specific wallet address without inspecting each transaction manually.
What are the main event types used in DeFi forensics?
The main event types in DeFi forensics are Transfer events for token flow tracing, Swap events for DEX trading pattern analysis, Vote events for governance attack detection, and Borrow or Repay events for lending fraud investigation. Each type captures protocol-specific state changes invisible in standard transaction data. According to Chainalysis (2024), smart contract event logs are the primary data source for 78% of DeFi fraud investigations on Ethereum, providing evidence not available from standard transfer records.
How do investigators use Swap events in DEX fraud cases?
Investigators use Swap events to reconstruct the complete DEX trading history of a suspect wallet, including token amounts exchanged, pool addresses, and initiating wallet addresses. Correlating Swap event sequences across multiple blocks identifies coordinated trading patterns such as wash trading. According to Chainalysis (2024), Swap event analysis identified coordinated wash trading in 23% of DeFi manipulation investigations, where multiple wallets traded the same token pair in circular patterns to inflate volume metrics used for fraudulent marketing.
Can smart contract event logs be used as court evidence?
Smart contract event logs can be used as court evidence when presented by a qualified expert witness with recognised blockchain forensics credentials. The immutable nature of Ethereum event logs means the underlying data cannot be disputed by opposing parties. UK courts have accepted event log evidence in civil asset recovery proceedings and DeFi fraud cases. ACAMS-qualified and MLRO-qualified expert witnesses are required to present DeFi technical event log evidence effectively in UK, US, and EU legal proceedings.
How does event log analysis support AML compliance?
Event log analysis supports AML compliance by providing the DeFi interaction history needed to assess the risk profile of incoming deposits with DeFi origins. UK AML regulations and EU AML directives require source of funds verification for DeFi-sourced deposits. Regulatory compliance teams use event log queries to identify source wallets that interacted with known manipulation contracts, governance attack protocols, or fraud-linked DeFi pools. ACAMS-standard procedures recommend event log screening as part of enhanced due diligence for DeFi deposit workflows.
What tools are used for smart contract event log analysis?
Investigators use Chainalysis Reactor and Elliptic Investigator for automated event log indexing and attribution across all Ethereum contracts. TRM Labs provides additional multi-chain event log coverage. Archive node tools with the eth_getLogs RPC method enable raw event log extraction for custom analysis. According to TRM Labs (2024), automated platform queries reconstruct 94% of a suspect address’s DeFi activity within 30 minutes, making enterprise platform access essential for time-sensitive fraud investigations.
Does Crypto Trace Labs provide smart contract event log analysis?
Crypto Trace Labs provides smart contract event log analysis for DeFi fraud investigations, civil asset recovery proceedings, and exchange AML compliance reviews. The team uses Chainalysis Reactor and Elliptic Investigator to reconstruct complete event log histories, correlate multi-contract attack sequences, and quantify victim losses for legal evidence. ACAMS accreditations and MLRO qualifications across UK, US, and EU support court proceedings. Exchange relationship contacts at Blockchain.com, Kraken, and Coinbase expedite KYC data requests when event-traced funds arrive at regulated platforms.
Executive Summary
Smart contract event log analysis extracts forensic intelligence from the permanent event logs emitted by Ethereum smart contracts, enabling complete reconstruction of DeFi protocol interactions. Transfer events, Swap events, governance events, and custom protocol events each provide different investigation intelligence not visible in standard transaction records. Chainalysis Reactor, Elliptic Investigator, and TRM Labs automate event log analysis with exchange attribution. Elliptic (2024) confirms 89% of multi-contract DeFi attack sequences are fully reconstructable from event logs. UK AML, EU AML, and US AML compliance frameworks require event log analysis for source of funds verification on DeFi-sourced deposits.
What Should You Do Next?
If you are investigating a DeFi fraud case or need smart contract event log analysis for an AML compliance review, specialist blockchain forensics is essential.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, providing direct exchange contacts for KYC data requests when event-traced funds arrive at regulated platforms. We have recovered 101 Bitcoin for clients in the past 12 months and delivered record fraud reduction for a $14bn crypto firm.
We offer no upfront charge for non-custodial wallet recoveries. Contact Crypto Trace Labs to discuss your smart contract investigation.
People Also Read
- ERC-20 Token Flow Analysis: Tracing Custom Tokens Through Smart Contracts
- MEV Bot Transaction Patterns: Identifying Front-Running and Sandwich Attacks
- Stablecoin Blacklist Analysis: How USDT and USDC Freezing Affects Tracing
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





