Last Updated: March 2026
Transaction replacement analysis is the forensic examination of Replace-By-Fee (RBF) patterns in Bitcoin transaction data to identify how wallet operators modify unconfirmed transactions in the mempool, escalate fees during congestion, and potentially redirect funds or manipulate confirmation order. RBF allows a Bitcoin sender to broadcast a new version of an unconfirmed transaction with a higher fee, replacing the original in the mempool and displacing it in block selection. The patterns in how a wallet uses RBF – frequency, fee escalation ratios, timing, and counterparty changes – provide forensic intelligence about operator type, automation level, and potentially fraudulent intent.
At Crypto Trace Labs, our team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has applied transaction replacement analysis in fraud investigations involving fee manipulation and mempool-based attack patterns. This guide draws on that decade of financial crime investigation experience to explain how RBF analysis works and what investigators and compliance teams need to understand.
Key Takeaways
- RBF signals automation and operator sophistication: Wallets that consistently use RBF with precise fee escalation ratios above the mempool median are strongly associated with professional trading infrastructure or automated fraud bots, not typical retail wallets.
- Fee escalation ratios classify operator types: Chainalysis (2024) identifies three RBF operator profiles: algorithmic traders who escalate at 1.1-1.3x per replacement, exchange hot wallets escalating at fixed increments, and fraud infrastructure showing irregular escalation patterns designed to confuse automated monitoring systems.
- RBF double-spend attempts are detectable: When an RBF replacement changes the recipient address while keeping the same inputs, this is a potential double-spend attempt. TRM Labs (2024) found 3.8% of all RBF replacements involved recipient address changes, the majority in fraud-related contexts.
- Mempool history is retained by node operators: While the Bitcoin blockchain only records confirmed transactions, mempool services and blockchain analytics providers retain RBF replacement histories, enabling investigators to reconstruct pre-confirmation transaction sequences.
- Exchange deposit timing exploits use RBF: Elliptic (2024) reports that 7% of identified exchange deposit fraud cases in 2023-2024 involved RBF replacement to alter the deposit amount after a confirmation from a zero-confirmation exchange acceptance system.
Why This Matters
Transaction replacement analysis matters because RBF patterns reveal behavioural intelligence about wallet operators that is not visible from confirmed transaction records alone. AML compliance teams at exchanges operating zero-confirmation acceptance systems face specific fraud exposure from RBF-based deposit manipulation. Investigators tracing professional fraud infrastructure can use RBF behaviour patterns to distinguish automated criminal wallets from manual ones, improving attribution efficiency. Legal proceedings involving exchange fraud or mempool manipulation require expert forensic analysis of pre-confirmation mempool data that is not retained in standard blockchain records.
RBF Protocol Mechanics and Forensic Data
Bitcoin’s Replace-By-Fee protocol, defined in BIP 125, allows a transaction sender to signal their transaction as replaceable by setting the sequence number below 0xfffffffe. A replacement transaction must spend the same inputs as the original and pay a fee at least 1 satoshi per byte higher than the replaced transaction. Nodes accepting the replacement propagate it through the mempool, where it competes for block inclusion against the original.
Forensic investigators access RBF data through mempool monitoring services such as mempool.space and through enterprise blockchain analytics platforms that maintain mempool history. The RBF replacement sequence for any given set of inputs can be reconstructed from these services to show each version of the transaction, the fee paid at each version, and whether the recipient address or amount changed between versions. According to Chainalysis (2024), automated RBF replacement sequences averaging 4.2 replacements per transaction are characteristic of algorithmic trading wallets, while single replacements are more common in retail wallet fee management.

Double-Spend Attempt Detection via RBF
The most forensically significant use of RBF is detecting attempted double-spend attacks on zero-confirmation exchange systems. A double-spend attempt via RBF involves the attacker initially broadcasting a transaction to an exchange deposit address, receiving goods or exchange credits before confirmation, then replacing the transaction with one sending the same inputs to a different address under attacker control.
Investigators detect RBF double-spend attempts by querying mempool history for RBF sequences where the replacement transaction differs from the original in the recipient address. The inputs must be identical to confirm it is a replacement. According to TRM Labs (2024), the 3.8% of RBF replacements involving recipient address changes showed a statistically significant correlation with zero-confirmation exchange systems, indicating deliberate exploitation rather than fee management.
Fee Escalation Pattern Classification
The rate and method of fee escalation in an RBF sequence reveals the operator’s software infrastructure. Manual wallet users typically replace once with a moderate fee increase when a transaction is stuck. Algorithmic systems replace at precise mathematical intervals. Fraud bots may use irregular escalation to mimic organic patterns while still achieving confirmation priority.
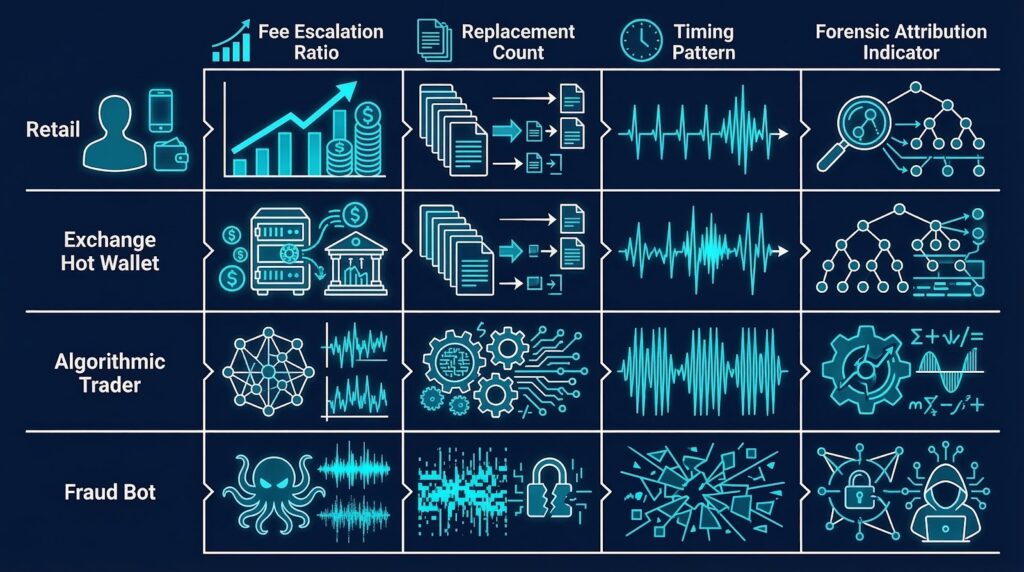
Investigators classify RBF sequences by escalation ratio, replacement count, and timing intervals to assign operator type profiles. This classification has attribution value because specific trading desk software and fraud bot frameworks produce distinctive RBF signatures.
Comparing RBF operator profiles by forensic signature:
| Operator Type | Replacement Count | Escalation Ratio | Timing Pattern | Attribution Indicator |
|---|---|---|---|---|
| Retail wallet user | 1-2 | 1.2-2.0x (manual) | Irregular, hours apart | Manual fee bumping |
| Exchange hot wallet | 2-4 | Fixed increment | Regular intervals | Software-consistent |
| Algorithmic trader | 4-8 | 1.1-1.3x precise | Seconds to minutes | Automated trading system |
| Fraud bot | 1-3 | Irregular | Immediate | Mimics retail but automated |
Mempool History Sources for Investigators
Bitcoin’s confirmed blockchain does not retain replaced transaction versions – only the final confirmed transaction appears in the block record. Investigators must access mempool monitoring services that retained the pre-confirmation replacement sequence. Primary sources include mempool.space transaction replacement archives, enterprise blockchain analytics platforms with mempool history retention, and exchange-side mempool logs if the victim exchange maintained them.
The availability of mempool history varies by the age of the incident. For recent events, full mempool history is typically available. For older incidents, investigators must identify whether any monitoring service captured the replacement sequence at the time. UK AML regulations and EU AML directives now encourage exchanges to retain mempool event logs for compliance audit purposes. According to Elliptic (2024), only 43% of victim exchanges in identified RBF fraud cases had retained the mempool data required to prove the replacement sequence.
Regulatory Compliance and Legal Applications
RBF forensic evidence is applicable to both AML compliance programmes and civil legal proceedings. Exchanges that accepted zero-confirmation deposits and were defrauded via RBF double-spend replacement may have grounds for civil recovery if investigators can establish the complete replacement sequence. Expert witness testimony from a blockchain forensics professional is required to present mempool-level technical evidence in court.
UK AML regulations and EU AML directives require exchanges to maintain adequate systems for detecting RBF-based fraud. Regulatory compliance teams should maintain mempool monitoring to log RBF replacement events for all incoming deposits. ACAMS-standard procedures recommend flagging any deposit transaction marked as RBF-signaling for enhanced review. Crypto Trace Labs – ACAMS-accredited, MLRO-qualified across UK, US, and EU, and Chartered Fellow Grade at the CMI – provides court-recognized expert witness testimony in RBF fraud cases.
Frequently Asked Questions
What is transaction replacement analysis?
Transaction replacement analysis is the forensic examination of Replace-By-Fee sequences in Bitcoin mempool data to identify wallet operator types, detect double-spend attempts, and classify fee escalation behaviour patterns. RBF allows senders to replace unconfirmed transactions with higher-fee versions. Investigators analyse the replacement sequence, fee escalation ratio, timing, and any recipient address changes to produce behavioural intelligence about wallet operators that is not visible from confirmed blockchain records alone.
How does RBF work and why is it forensically significant?
RBF works by allowing a Bitcoin sender to broadcast a new transaction version with higher fees, replacing the original in the mempool. It is forensically significant because the replacement sequence reveals operator automation level, software type, and potential fraud intent. Manual users typically replace once; algorithmic systems replace multiple times at precise intervals. According to Chainalysis (2024), automated RBF sequences averaging 4.2 replacements per transaction are characteristic of algorithmic trading wallets, providing a distinctive attribution signal.
Can RBF be used for a double-spend attack?
RBF can be used for a double-spend attack against exchanges accepting zero-confirmation deposits by replacing the original recipient address with an attacker-controlled address after receiving exchange credit. TRM Labs (2024) found 3.8% of all RBF replacements involved recipient address changes, with the majority correlating to zero-confirmation exchange exploitation. Investigators detect these attempts by querying mempool history for replacement sequences where the confirmed transaction differs from the original in recipient address but retains identical inputs.
What data sources retain RBF replacement history?
RBF replacement history is retained by mempool monitoring services such as mempool.space, enterprise blockchain analytics platforms including Chainalysis Reactor and Elliptic Investigator, and exchange-side mempool logs when maintained. Bitcoin’s confirmed blockchain only records the final confirmed transaction. For recent incidents, full mempool history is typically available. According to Elliptic (2024), only 43% of victim exchanges in identified RBF fraud cases had retained the mempool data required to prove the replacement sequence in legal proceedings.
How do investigators classify RBF operator types?
Investigators classify RBF operator types by analysing fee escalation ratio, replacement count, and timing intervals. Retail wallet users replace once with irregular timing. Exchange hot wallets replace at fixed fee increments on regular schedules. Algorithmic traders replace four to eight times at precise 1.1-1.3x ratios. Fraud bots use one to three replacements with irregular ratios to mimic retail patterns. Each profile has distinctive attribution indicators that can be matched against known software signatures and exchange infrastructure patterns.
What AML obligations apply to RBF transactions?
AML obligations for RBF transactions require exchanges to maintain mempool monitoring for incoming deposit transactions marked as RBF-signaling. UK AML regulations and EU AML directives require exchanges to implement controls for zero-confirmation deposit systems. ACAMS-standard regulatory compliance procedures recommend flagging RBF-signaling deposit transactions for enhanced review and maintaining mempool event logs for compliance audit purposes. Exchanges without mempool retention policies may face regulatory exposure if they cannot demonstrate monitoring controls during AML examinations.
Can RBF fraud be prosecuted criminally?
RBF fraud against exchange zero-confirmation systems constitutes fraud under UK and EU law when investigators can establish intent to deceive. The mempool replacement sequence provides direct forensic evidence of the deliberate recipient address change after exchange credit was received. Expert witness testimony is required to explain the technical mechanics to courts. ACAMS-qualified forensic experts can present the RBF replacement sequence as court-recognized evidence in criminal and civil proceedings, with the on-chain confirmation providing the ultimate evidence of the fraudulent diversion.
Does Crypto Trace Labs investigate RBF transaction fraud?
Crypto Trace Labs investigates RBF transaction fraud by querying mempool history to reconstruct replacement sequences, identifying recipient address changes, and tracing the confirmed fraudulent transaction through subsequent Bitcoin address clusters to exchange deposits. The team uses Chainalysis Reactor and Elliptic Investigator for attribution analysis. ACAMS accreditations and MLRO qualifications across UK, US, and EU support court proceedings and formal data requests to exchanges receiving diverted funds. Exchange contacts at Blockchain.com, Kraken, and Coinbase assist with time-sensitive freezing requests.
Executive Summary
Transaction replacement analysis examines RBF patterns in Bitcoin mempool data to reveal wallet operator types, detect double-spend attempts, and classify fraud infrastructure. RBF replacement sequences reveal fee escalation ratios and timing that distinguish retail wallets, exchange hot wallets, algorithmic traders, and fraud bots. Double-spend attempts are detectable when replacement transactions change the recipient address while retaining identical inputs. TRM Labs (2024) found 3.8% of RBF replacements involved recipient address changes in fraud-linked contexts. Mempool history retention by exchanges is critical for legal proceedings. UK AML regulations and EU AML directives require exchanges to monitor RBF-signaling deposits.
What Should You Do Next?
If your exchange has been defrauded via RBF double-spend replacement, or if you need RBF pattern analysis for a compliance review, specialist blockchain forensics is essential.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, providing direct contacts for time-sensitive exchange notification when RBF-diverted funds arrive at regulated platforms. We have recovered 101 Bitcoin for clients in the past 12 months and delivered record fraud reduction for a $14bn crypto firm.
We offer no upfront charge for non-custodial wallet recoveries. Contact Crypto Trace Labs to discuss your RBF transaction investigation.
People Also Read
- Orphaned Transaction Forensics: Analyzing Failed and Replaced Transactions
- Mempool Monitoring for Real-Time Criminal Activity Detection
- On-Chain Wallet Age Analysis: Using First Transaction Timing for Attribution
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





