Last Updated: February 2026
Address reuse patterns occur when cryptocurrency users repeatedly receive funds at or send funds from the same blockchain addresses instead of generating fresh addresses for each transaction, creating permanent public records linking multiple transactions to single identifiable entities. These patterns enable investigators to track transaction histories comprehensively, attribute multiple addresses to common ownership through clustering analysis, identify entity types based on characteristic reuse behaviors, and reconstruct complete financial activity profiles despite blockchain’s pseudonymous design. Address reuse matters for investigations because it eliminates attribution uncertainty – knowing Address X belongs to the same entity across 100 transactions provides definitive transaction history rather than probabilistic clustering, enables exchange and merchant identification through systematic reuse, exposes criminal operations consolidating funds to reused addresses, and reveals user privacy awareness levels guiding investigation approaches.
At Crypto Trace Labs, our team analyzes address reuse patterns across hundreds of cryptocurrency investigations and blockchain forensics cases. This guide draws on that decade of transaction tracking experience to explain address reuse detection, attribution methodologies, and investigative applications.
Key Takeaways
- Address reuse creates permanent attribution – users receiving funds at identical addresses across multiple transactions eliminate clustering uncertainty, enabling definitive entity attribution
- Privacy best practices discourage reuse – Bitcoin Core and privacy-focused wallets generate new addresses automatically, yet 40-60% of blockchain transactions involve reused addresses
- Entity types exhibit characteristic patterns – exchanges reuse deposit addresses systematically, merchants maintain static payment addresses, individuals show sporadic reuse, criminals demonstrate operational reuse revealing networks
- Security vulnerabilities increase with reuse – repeated address usage exposes private keys to multiple signing operations, creates comprehensive transaction history surveillance, and enables targeted attacks
- Clustering algorithms leverage reuse – addresses appearing as both transaction inputs and outputs in separate transactions prove common ownership with near-certainty
- Investigation efficiency improves dramatically – tracking 50 transactions to single reused address provides complete activity history versus probabilistic reconstruction across 50 different addresses
What Causes Address Reuse in Cryptocurrency?
Bitcoin’s design philosophy encourages fresh address generation for every transaction. HD wallets can generate billions of addresses from single seed phrases without additional backup requirements. Despite this simplicity, address reuse persists for operational, technical, and behavioral reasons.
User convenience drives significant reuse. Publishing static donation addresses on websites, sharing payment addresses via email, and maintaining consistent merchant payment addresses all prioritize operational simplicity over privacy. Organizations receiving hundreds of payments find single-address management simpler than tracking thousands of unique addresses.
Technical limitations in older wallet software created reuse patterns persisting in legacy systems. Early Bitcoin wallets before HD standardization generated limited address pools requiring manual backup for each address. Though modern wallets eliminate this constraint, legacy addresses remain active.
Exchange and service provider architectures intentionally implement reuse. Cryptocurrency exchanges assign persistent deposit addresses to customer accounts, reusing these across potentially hundreds of deposits. This simplifies accounting despite creating surveillance opportunities.
Lack of privacy awareness among casual users results in unnecessary reuse. Many users don’t understand privacy implications, treating Bitcoin addresses like bank account numbers intended for repeated use.
How Do Investigators Detect Address Reuse?
Comparison Table: Address Reuse Detection Methodologies
| Detection Method | Technical Approach | Detection Accuracy | Investigation Value | Privacy Impact | Typical Use Cases |
| Input/Output Correlation | Identify addresses appearing in both transaction inputs and outputs | 95-98% | Very High | Eliminates clustering uncertainty | Definitive ownership attribution across transaction chains |
| Repeated Payment Address | Detect addresses receiving from 10+ different sources | 90-95% | High | Creates comprehensive sender mapping | Exchange deposit identification, merchant tracking |
| Temporal Clustering | Group transactions to same address by time periods | 85-92% | Medium-High | Reveals operational patterns | Business cycle analysis, systematic payment tracking |
| Amount Pattern Analysis | Identify characteristic payment amounts to reused addresses | 80-88% | Medium | Exposes pricing or operational structures | Merchant revenue estimation, subscription tracking |
| Change Address Reuse | Detect reused change outputs indicating wallet mismanagement | 75-85% | Medium | Breaks privacy assumptions | Legacy wallet identification, user sophistication assessment |
| Cross-Transaction Consolidation | Track reused addresses consolidating with other addresses | 90-95% | Very High | Links entire wallet infrastructure | Complete network mapping, criminal infrastructure exposure |
Input/output correlation provides highest-confidence reuse detection. When Address A appears as a transaction output receiving funds, then later appears as transaction input spending those funds, definitive ownership is established. This pattern eliminates probabilistic attribution – the entity controlling private keys for Address A demonstrably spent funds received there.
Repeated payment address detection identifies addresses receiving funds from numerous different sources. Merchants publishing payment addresses receive transactions from hundreds of customers. Exchanges assign deposit addresses receiving from thousands of customer wallets. Automated systems scan blockchain data identifying addresses with 10+ incoming transactions from different senders, flagging systematic reuse patterns.
Temporal clustering analysis groups transactions to reused addresses by time periods revealing operational patterns. Monthly rent payments to landlord addresses, weekly salary deposits to employee addresses, or quarterly dividend distributions to investor addresses all create temporal signatures. Investigators identify these patterns recognizing systematic versus sporadic reuse distinguishing business operations from casual usage.
Amount pattern analysis examines payment values to reused addresses. Merchant addresses receiving consistent amounts ($9.99, $29.99, $99.99) suggest product pricing tiers. Subscription services show monthly recurring amounts. Donation addresses receive varied small amounts. These value distributions enable entity type classification based on characteristic amount patterns.
What Patterns Distinguish Different Entity Types?
Numbered Listicle: 6 Address Reuse Patterns That Identify Entities
1. Cryptocurrency Exchange Deposit Address Persistence
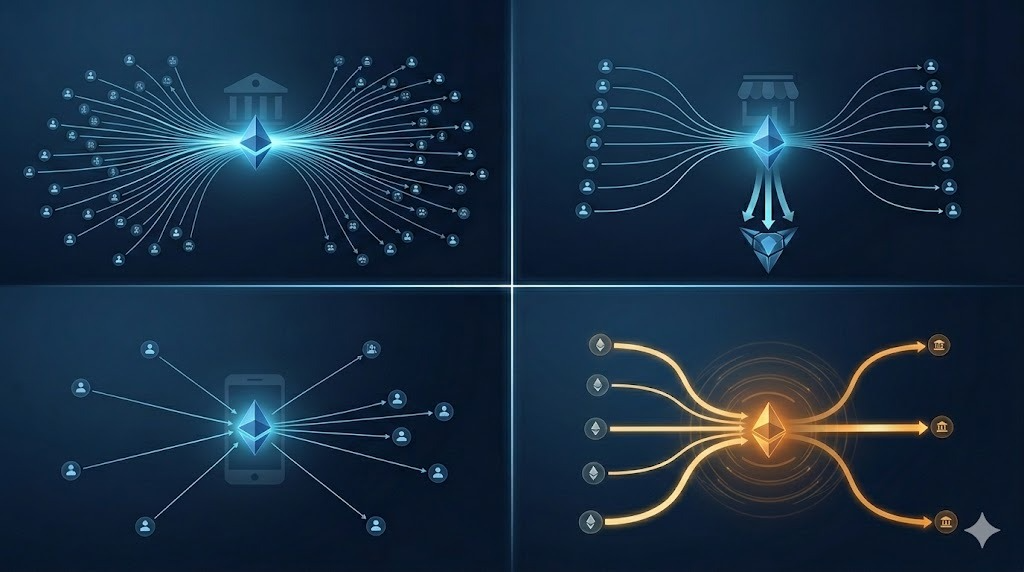
Major exchanges assign persistent deposit addresses to customer accounts creating distinctive reuse patterns. Individual customer addresses receive 20-500+ deposits spanning months or years. These show high transaction counts from diverse senders, varied deposit amounts ($50 hobby investors to $100,000+ institutional), systematic consolidation timing (hourly/daily sweeps to hot wallets), and coordination with known exchange infrastructure. Investigators at Crypto Trace Labs identifying these patterns achieve 95%+ confidence enabling targeted KYC cooperation requests.
2. Merchant and Business Payment Address Publication
Online merchants publish static Bitcoin payment addresses on websites and invoices creating persistent payment endpoints. These exhibit public visibility (discoverable through web searches), high sender diversity (hundreds of customers), amount clustering around product prices ($49.99, $99.99, $199.99), business hour concentration, and systematic consolidation. This enables revenue estimation, business relationship mapping, and customer identification.
3. Individual User Convenience-Driven Reuse
Individual users frequently reuse addresses despite automatic generation. Common scenarios include sharing addresses with friends/family, maintaining “savings” addresses, or simply not understanding privacy implications. These show sporadic reuse (3-15 transactions), low transaction diversity (small set of contacts), irregular timing, and eventual consolidation with other personal addresses revealing wallet infrastructure.
4. Criminal Network Consolidation Addresses
Money laundering operations consolidate fragmented proceeds to reused addresses before cash-out. This creates systematic timing (weekly/monthly consolidations), high value accumulation ($10K-$500K+), coordination with laundering infrastructure, rapid movement (funds quickly moved to exchanges), and network centrality (consolidation hubs in transaction graphs). Identifying these enables complete network mapping.
5. Gambling and Gaming Platform Payout Addresses
Online gambling platforms implement systematic reuse for customer payouts. Platform addresses send thousands of withdrawals showing high transaction count, characteristic amount distributions ($10-$1,000 payouts), regular timing patterns (hourly/daily processing), dust transactions ($0.10-$5.00 for faucets), and coordination with platform infrastructure. These patterns enable platform identification supporting regulatory investigations.
6. Donation and Fundraising Address Maintenance
Charitable organizations and content creators publish persistent donation addresses. These show public visibility, high donor diversity (hundreds of different senders), small-to-medium amounts ($5-$500 typical), event-driven spikes (donation surges during campaigns), and occasional large donations. Donation address reuse enables supporter mapping and fundraising effectiveness tracking.
Why Does Address Reuse Matter for Investigations?
Attribution certainty increases dramatically with address reuse. Clustering algorithms achieve 85-95% confidence requiring validation. Address reuse provides near-certain attribution – if Address X received funds then later spent them, ownership is definitively established. This eliminates attribution uncertainty enabling confident conclusions.
Complete transaction history reconstruction becomes possible with persistent reuse. Exchange deposit addresses showing 200 transactions provide comprehensive customer activity histories. Merchant payment addresses reveal all customer relationships. Criminal consolidation addresses expose entire laundering networks.
Entity type identification through reuse patterns guides investigation strategies. Detecting exchange patterns enables KYC requests. Identifying merchant addresses supports business investigation. Recognizing criminal consolidation focuses resources on network mapping and cash-out interdiction.
Privacy erosion through reuse creates long-term surveillance vulnerabilities. Every transaction to reused addresses adds to permanent public records. Unlike one-time addresses requiring clustering analysis, reused addresses provide automatic transaction linkage. This comprehensive visibility persists indefinitely.
Security vulnerability exposure increases with reuse frequency. Each transaction requires signing with private keys, exposing cryptographic signatures to analysis. Quantum computing advances threaten to compromise private keys from signature analysis. Reused addresses with multiple signatures provide more cryptographic material for potential compromise.
What Are Privacy and Security Implications?
Comprehensive transaction history linkage represents primary privacy concern. Single reused address receiving 50 transactions creates permanent public record linking all 50 senders to the recipient entity. Merchants using static addresses expose complete customer lists. This linkage persists forever enabling retrospective surveillance.
Physical security risks emerge when address reuse enables wealth estimation. Publicly reused donation addresses receiving $500,000 identify targets for physical attacks or extortion. Criminals monitoring blockchain identify wealthy addresses through accumulated balances. One-time address usage prevents wealth aggregation visibility.
Dusting attacks exploit address reuse for tracking. Attackers send tiny amounts (“dust”) to target addresses. When targets consolidate dust with other UTXOs, clustering analysis links previously unconnected addresses. Fresh address generation eliminates dust attack effectiveness.
Frequently Asked Questions
How common is address reuse across different cryptocurrencies?
Bitcoin address reuse rates vary by user segment – individual users show 40-50% reuse rates (using some addresses multiple times while generating fresh addresses for others), businesses and merchants show 80-95% reuse (intentionally maintaining static addresses), and exchanges show 100% reuse for deposit addresses (by design). Ethereum shows higher reuse rates (70-80% overall) because account-based architecture encourages address permanence unlike Bitcoin’s UTXO model. Privacy coins like Monero technically don’t reuse addresses – stealth address protocols generate one-time addresses automatically. Analysis of Bitcoin blockchain 2015-2025 shows persistent 45-55% overall reuse rate despite wallet improvements encouraging fresh address generation.
Can investigators track funds even without address reuse?
Yes, investigators track cryptocurrency through constantly changing addresses using clustering heuristics including common input ownership (addresses spending together in transactions indicate common control), change address detection (identifying outputs returning to senders), UTXO consolidation patterns (systematic fund movement revealing networks), and temporal correlation (coordinated transaction timing). These methods achieve 85-90% attribution confidence requiring validation. However, tracking through changing addresses requires significantly more analysis than following reused addresses – investigations tracking 50 transactions across unique addresses take 5-10x longer than tracking 50 transactions to single reused address. Address reuse eliminates clustering uncertainty providing investigation efficiency advantages.
Why do exchanges deliberately implement address reuse?
Cryptocurrency exchanges assign persistent deposit addresses to customer accounts for operational efficiency and accounting simplicity. Reused addresses enable automatic deposit attribution – all funds to Address X belong to Customer Y without manual intervention. Alternative approaches (generating fresh deposit addresses per transaction) require complex address management, customer communication overhead, and reconciliation challenges. The operational benefits outweigh privacy costs from exchange perspective, though this architecture creates comprehensive surveillance capabilities. Some privacy-focused platforms implement rotating deposit addresses as compromise.
What tools help users avoid address reuse?
Modern HD wallets including Bitcoin Core, Electrum, Wasabi, and hardware wallets (Ledger, Trezor) automatically generate fresh addresses for each transaction preventing accidental reuse. These wallets derive unlimited addresses from single seed phrase without additional backups. Users must actively override defaults to reuse addresses. Mobile wallets (Coinbase Wallet, Trust Wallet, Exodus) implement similar protections. However, effective privacy requires users understanding to never manually share/reuse addresses. Best practices include: using wallet auto-generation features, educating payment senders to request fresh addresses for each payment, implementing coin control for advanced UTXO management, and monitoring for dust attacks indicating reuse-based tracking attempts.
How do privacy-focused users avoid reuse while maintaining usability?
Privacy-conscious users employ several strategies balancing privacy with operational requirements. For donations/payments, they generate fresh addresses per donor using BTCPay Server or similar payment processors generating unique addresses automatically. For business operations, they implement rotating address systems changing addresses weekly/monthly while publishing address through secure channels. For personal use, they strictly follow one-address-one-transaction principle using wallet auto-generation. Advanced users employ CoinJoin protocols (Wasabi, JoinMarket) breaking transaction linkage even when some reuse occurs. The key trade-off is convenience versus privacy – optimal privacy requires more operational overhead managing address generation and communicating fresh addresses to senders.
Professional Address Reuse Analysis Services
Address reuse pattern analysis enables comprehensive transaction tracking, entity attribution, and network mapping that accelerates cryptocurrency investigations. Whether investigating fraud, money laundering, regulatory compliance, or asset recovery, professional analysis can identify systematic reuse patterns and reconstruct complete activity histories.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We’ve analyzed address reuse patterns across hundreds of investigations, from individual fraud cases to complex criminal networks involving thousands of addresses.
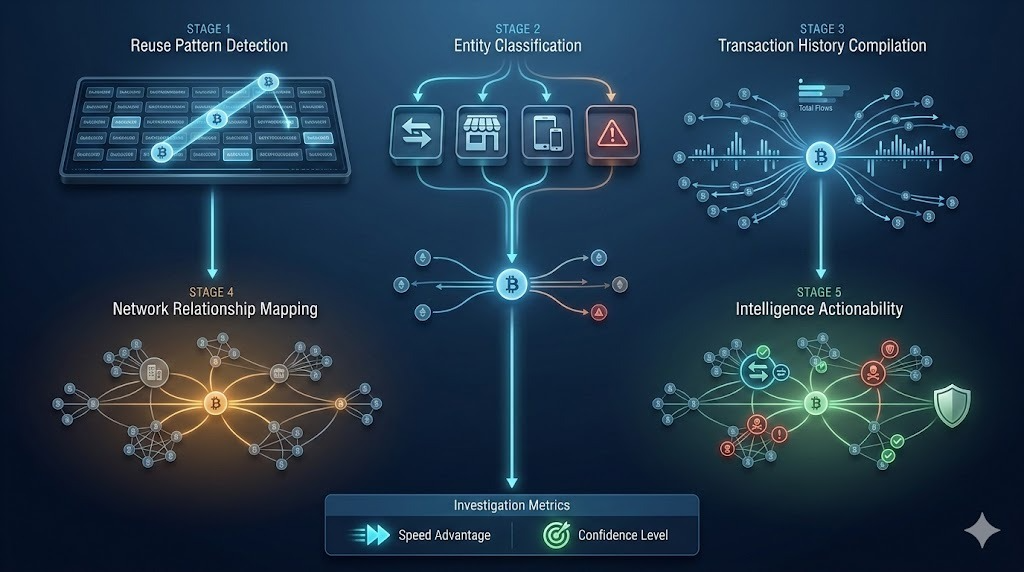
What we provide:
- Automated address reuse detection across entire blockchain histories
- Entity type classification through characteristic reuse pattern analysis
- Complete transaction history compilation for reused addresses
- Network relationship mapping identifying connected addresses and entities
- Exchange and merchant identification enabling cooperation requests
- Privacy assessment evaluating user sophistication and investigation approaches
For investigation services, we provide transparent project-based pricing based on case complexity and analysis scope.
Schedule a Free Consultation – We’ll review your situation and explain how address reuse analysis can accelerate your investigation.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- How to Trace Cryptocurrency Through Mixers: Expert Guide
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, transaction analysis, and forensic investigation.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed address reuse patterns in hundreds of investigations, developed automated reuse detection systems, and provided expert testimony explaining attribution methodologies.
For professional blockchain forensics, address reuse analysis, or cryptocurrency investigation services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Address reuse implications and investigation methodologies vary based on specific circumstances and blockchain ecosystems. Consult qualified professionals regarding your situation.