Last Updated: February 2026
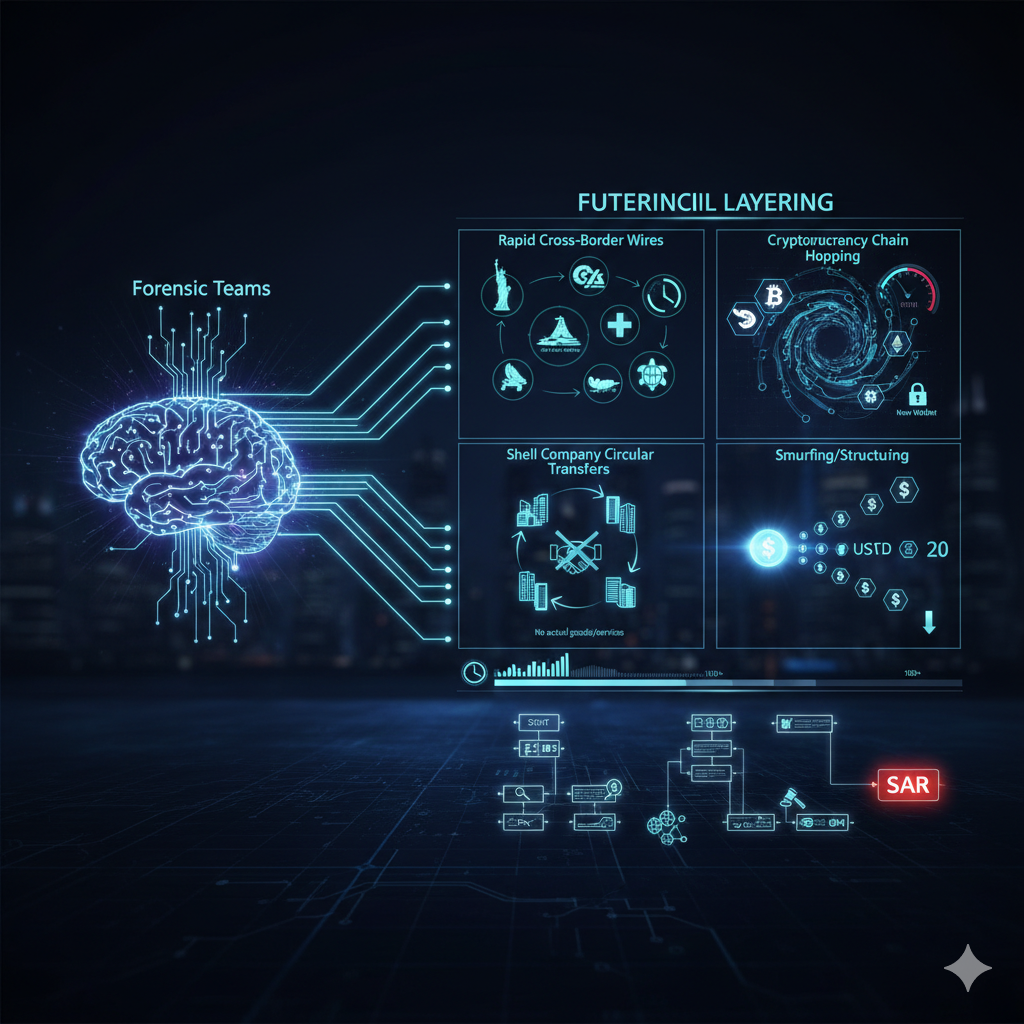
Layering transactions are the deliberate movement of illicit funds through multiple complex transfers designed to obscure the original source and create investigative confusion. This second stage of money laundering separates criminal proceeds from their illegal origins through rapid cross-border wires, cryptocurrency conversions, shell company transfers, and strategic placement across dozens or hundreds of accounts. Forensic teams identify layering through velocity analysis detecting unusually rapid fund movement, pattern recognition revealing systematic circular transfers between related entities, anomaly detection flagging accounts with transaction volumes inconsistent with stated business purposes, and network mapping exposing hidden relationships between seemingly unconnected wallets or accounts.
At Crypto Trace Labs, our team tracks layering schemes across hundreds of cryptocurrency fraud investigations and asset recovery cases. This guide draws on that decade of blockchain forensics and financial crime experience to explain layering mechanics, detection methodologies, and investigative strategies.
Key Takeaways
- Layering creates investigative complexity through volume (100+ transactions), velocity (hours not days), and jurisdictional fragmentation across multiple countries
- Cryptocurrency amplifies effectiveness – blockchain transactions settle in minutes enabling 50+ address hops before traditional banking alerts trigger
- Six advanced techniques dominate criminal operations: velocity layering, casino integration, mirror trading, digital asset conversion, real estate laundering, and mixer evasion
- Detection success rates vary significantly – velocity analysis (75-85%), network mapping (80-90%), ML anomaly detection (90-95%), beneficial ownership tracing (60-75%)
- Investigation timelines depend on complexity – domestic cases (2-4 months), multi-jurisdiction (6-12 months), cryptocurrency with offshore (6-12 months)
- Each layering transaction constitutes separate criminal offense under 18 USC 1956/1957 enabling prosecutors to charge hundreds of individual counts
What Makes Layering the Most Complex Money Laundering Stage?
Layering creates investigative difficulty through volume, velocity, and jurisdictional fragmentation. Criminals execute dozens of transactions within hours, moving funds through offshore accounts in multiple countries. Each transaction layer adds complexity requiring additional documentation requests and timeline reconstruction.
The stage exploits financial system weaknesses including delayed reporting and jurisdictional gaps. When funds move from US banks to Cayman trusts to Hong Kong companies to Dubai real estate within 48 hours, investigators face four legal jurisdictions with different cooperation protocols.
Cryptocurrency amplifies layering effectiveness. Blockchain transactions settle in minutes, enabling criminals to layer through 50+ addresses across multiple chains before traditional banking alerts trigger. Pseudonymous addresses combined with decentralized exchange fragmentation create attribution gaps taking months to resolve.
How Do Different Layering Techniques Operate?
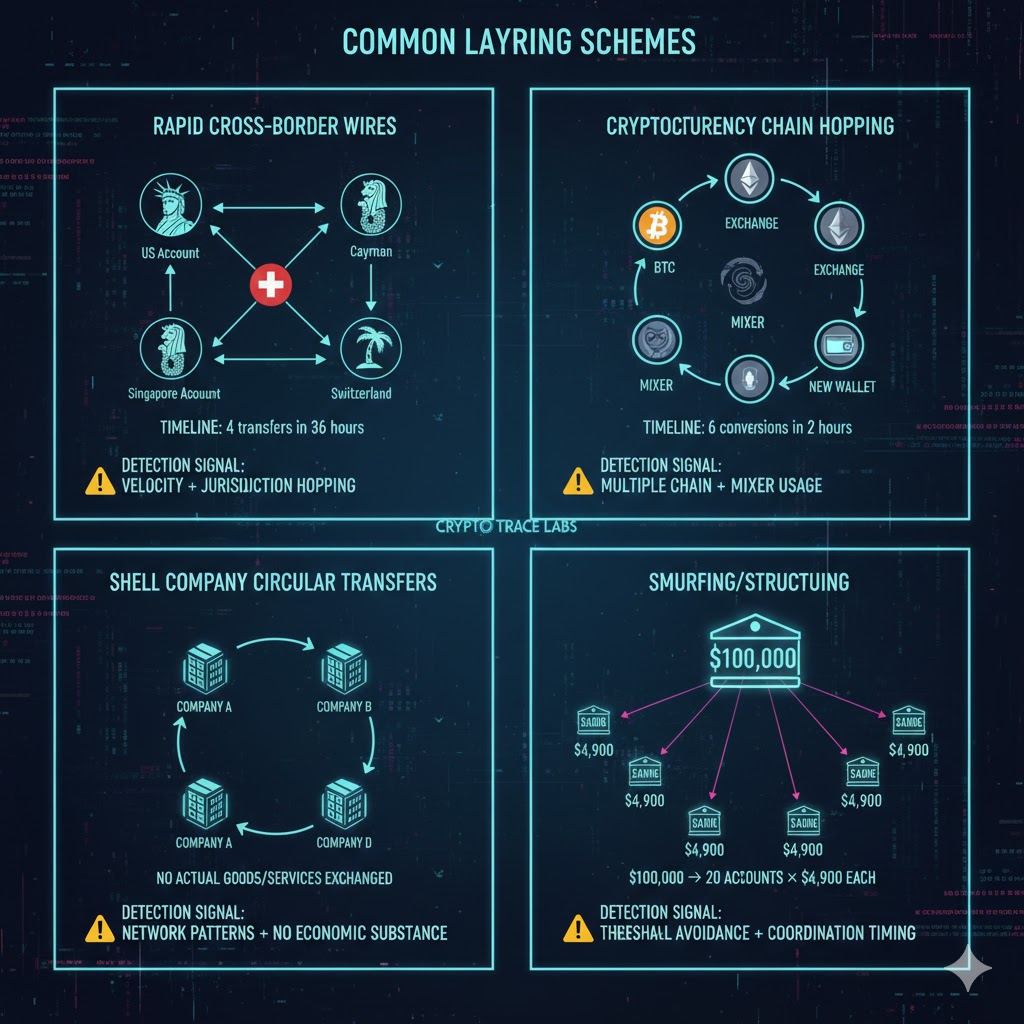
Rapid-fire wire transfers move funds through multiple accounts in quick succession. Criminals receive $500,000, wire it to Account B within hours, transfer to C the next day, continuing through D, E, and F before initial compliance reviews complete.
Shell company networks create false commercial justification. Money moves between five companies controlled by the same network with fabricated invoices suggesting legitimate trade without actual goods or services exchanging hands.
Cryptocurrency mixing services obscure transaction trails by pooling funds from multiple users and redistributing to destination addresses with no direct blockchain connection to sources.
Asset conversion sequences transform money across different forms to defeat single-asset tracking. Criminals convert cash to crypto, trade for gold, sell for wire funds, purchase real estate, creating break points where investigators lose trails.
What Advanced Layering Techniques Do Criminals Use?
Numbered Listicle: 6 Advanced Layering Techniques Criminals Use
1. Velocity Layering – Overwhelming Investigation Teams Through Speed
Criminals execute 100+ transactions within 72 hours across multiple institutions and jurisdictions, creating more work than compliance teams can process in real-time. By the time investigators reconstruct the first 20 transfers, funds have moved through 80 additional hops and reached final destinations. This technique exploits the reality that human investigators cannot match machine-speed execution, especially when layering spans financial systems requiring separate legal processes.
2. Casino and Gaming Integration – Creating Legitimate Documentation
Launderers exchange $250,000 cash for casino chips, conduct minimal gambling, then cash out for casino checks appearing as gambling winnings. The casino provides documentation treating funds as legitimate gaming proceeds, creating defensible source-of-funds explanations. Sophisticated operations use multiple casinos across jurisdictions, varying amounts and timing to avoid pattern detection.
3. Mirror Trading – Simultaneous Offsetting Positions
Criminals execute matched trades through coordinated brokers – buying securities in one country while simultaneously selling identical positions in another. The “losing” side generates capital flight justification while the “winning” side receives apparently legitimate investment returns. Both positions are controlled by the same network but appear as independent activity.
4. Digital Asset Layering – Exploiting Blockchain Anonymity
Cryptocurrency layering leverages chain-hopping (Bitcoin to Ethereum to Monero), decentralized exchange fragmentation, and privacy coin integration to create attribution gaps. Each hop requires separate blockchain analysis, creating 4-6 week investigation delays even for experienced forensic teams.
5. Real Estate Layering – Creating Legitimate Asset Holdings
Launderers purchase properties through shell companies, hold briefly establishing ownership records, then sell or mortgage generating apparently legitimate proceeds. Transactions create multiple layers of real estate documentation obscuring criminal origins while providing defensible explanations for large fund movements.
6. Cryptocurrency Mixing and Chain Analysis Evasion
Professional launderers use cryptocurrency mixers like Tornado Cash combined with chain hopping and time delays creating compound obfuscation. This requires investigators to bridge multiple analysis gaps simultaneously, significantly extending investigation timelines.
What Tools and Techniques Identify Layering?
Comparison Table: Forensic Detection Methodologies
| Detection Method | Technical Approach | Data Sources Required | Detection Success Rate | Investigation Timeline |
| Velocity Analysis | Calculate transaction frequency and timing patterns across accounts | Transaction logs, timestamps, account relationships | 75-85% for rapid layering | 1-3 days initial detection |
| Network Graph Analysis | Map money flow relationships between entities using graph algorithms | Account ownership data, transaction history, corporate registries | 80-90% for shell company networks | 1-2 weeks comprehensive mapping |
| Behavioral Fingerprinting | Identify transaction patterns inconsistent with stated business purpose | Business profiles, industry benchmarks, historical activity | 70-80% with sufficient baseline data | 3-7 days pattern establishment |
| Cross-Chain Analysis | Track asset movements across multiple blockchain networks | Blockchain transaction data, exchange deposit addresses, bridge protocols | 85-95% for documented chains | 2-4 weeks multi-chain reconstruction |
| Anomaly Detection ML | Machine learning models flag statistical outliers in transaction behavior | Historical transaction data, peer group comparisons, risk indicators | 90-95% with trained models | Real-time to 24 hours |
| Beneficial Ownership Tracing | Investigate true controllers behind shell companies and nominee accounts | Corporate registries, shareholder records, KYC documents | 60-75% depending on jurisdiction | 2-8 weeks due to legal delays |
Chainalysis and Elliptic implement specialized blockchain layering detection tracking funds through mixing services, decentralized exchanges, and cross-chain bridges. Their platforms maintain databases of known mixer addresses and exchange deposit wallets enabling investigators to identify layering techniques.
Machine learning models trained on millions of transaction patterns identify subtle layering signatures human analysts miss, detecting timing characteristics and counterparty relationships statistically inconsistent with declared business activities.
How Do Investigators Reconstruct Layering Schemes?
Timeline reconstruction forms the foundation. Analysts create chronological transaction maps showing every fund movement with timestamps, amounts, accounts, and jurisdictional locations. This reveals patterns invisible when examining individual transactions.
Beneficial ownership investigation determines who controls accounts and entities involved. Investigators examine corporate registries, shareholder records, and KYC documentation discovering that seemingly unrelated companies share common ultimate beneficial owners, exposing coordinated network structures.
Cross-jurisdiction cooperation requests gather documentation from foreign institutions. When layering spans multiple countries, investigators submit mutual legal assistance requests to each jurisdiction. Response times range from weeks to months depending on bilateral agreements.
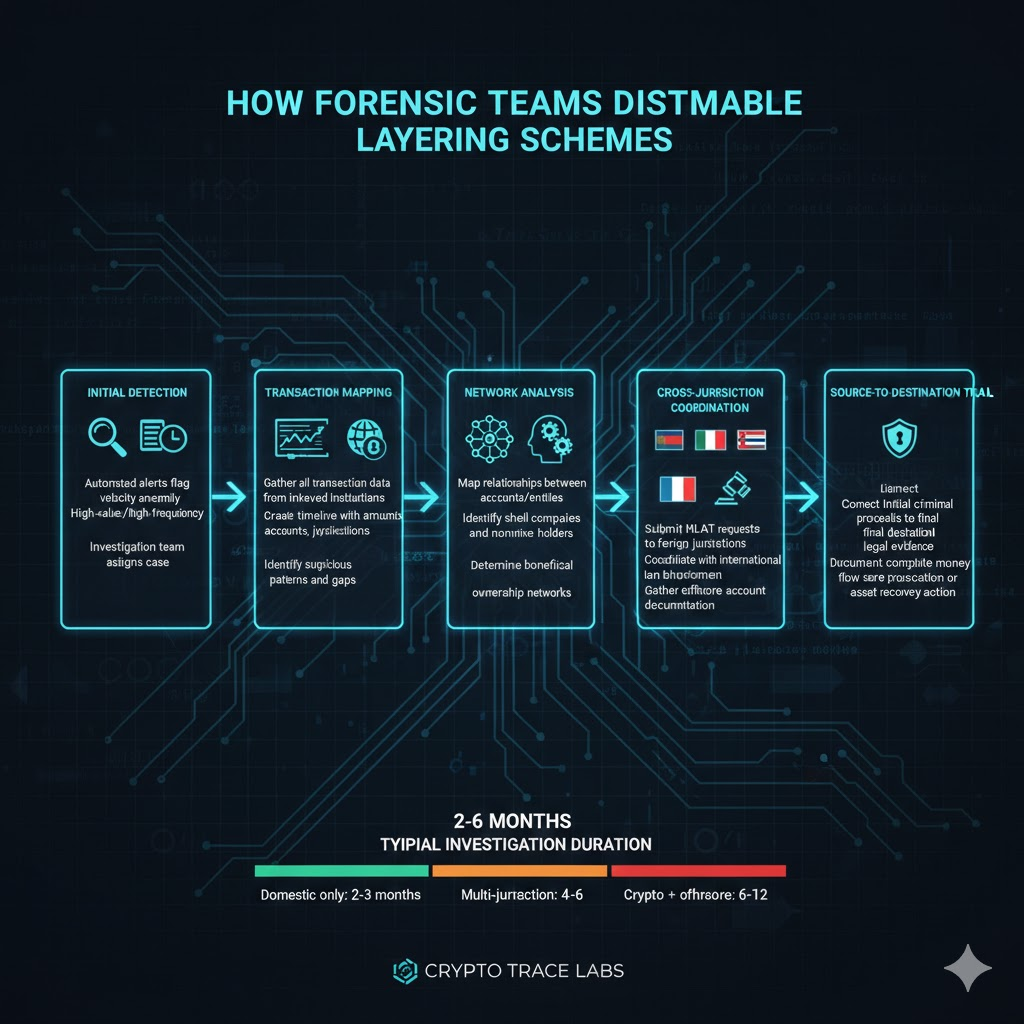
Blockchain analysis for cryptocurrency layering requires specialized expertise. Crypto Trace Labs investigators examine transaction graphs, identify mixer usage, track cross-chain bridges, and correlate exchange deposit addresses with KYC records linking blockchain addresses to real-world identities.
What Legal Frameworks Govern Layering Investigations?
US money laundering statutes (18 USC 1956 and 1957) criminalize conducting financial transactions designed to conceal criminal proceeds. The statutes treat each transaction in a layering sequence as a separate offense punishable by up to 20 years imprisonment and fines up to $500,000.
Bank Secrecy Act reporting requirements mandate institutions report suspicious activity including layering patterns through Suspicious Activity Reports within 30 days. Failure to report constitutes separate criminal violations.
EU Anti-Money Laundering Directives require member states implement robust monitoring systems capable of detecting layering. The sixth directive expands criminal liability to include facilitators and professional advisors who design or implement layering schemes.
Criminal proceeds forfeiture laws allow authorities to seize assets traced through layering schemes. When investigators reconstruct money flows connecting assets to criminal sources despite intermediate layering, courts can order forfeiture.
Frequently Asked Questions
How quickly can forensic teams detect active layering?
Real-time detection requires automated monitoring analyzing transactions as they occur. Advanced platforms flag layering within hours based on velocity thresholds and pattern recognition. However, comprehensive investigation confirming layering rather than legitimate activity typically requires 3-7 days gathering context, reviewing history, and analyzing counterparty relationships. Cryptocurrency layering using privacy techniques may take 2-4 weeks to fully trace across multiple blockchain networks.
Can layering defeat all forensic analysis?
No layering technique provides absolute protection against skilled forensic investigation. Privacy coins like Monero obscure transaction trails, forcing investigators to rely on entry/exit points at exchanges. However, even sophisticated layering leaves breadcrumbs – timing correlations, amount patterns, IP logs, and behavioral consistencies investigators exploit. The question becomes cost-benefit analysis – when investigation costs exceed recoverable values, practical resource constraints may prevent complete trail reconstruction even when technically possible.
What training do investigators need for layering analysis?
Professional investigators require 6-12 months specialized training covering financial crime typologies, blockchain forensics, legal frameworks, and analytical tools. ACAMS certification provides foundational knowledge on money laundering detection. Blockchain-specific training through Chainalysis or Elliptic adds cryptocurrency expertise. Law enforcement agencies provide tactical training on cross-jurisdiction cooperation and prosecution support. Practical experience analyzing dozens of cases develops pattern recognition differentiating sophisticated layering from complex legitimate operations.
How do prosecutors prove layering in criminal trials?
Prosecutors establish layering through expert testimony, transaction timelines, and documentary evidence demonstrating systematic concealment intent. Forensic experts present flow diagrams showing movement patterns inconsistent with legitimate commerce. Bank records and corporate papers establish each layering step. Defendants’ inconsistent explanations or false statements demonstrate consciousness of guilt. Statistical analysis proves transaction patterns’ improbability for legitimate business, while peer comparison shows similar businesses exhibit fundamentally different characteristics.
What happens to funds frozen during layering investigations?
Authorities obtain court orders freezing accounts when investigations identify assets as traceable proceeds. Frozen funds remain in accounts but cannot be accessed or transferred pending legal proceedings. If criminal forfeiture succeeds, assets transfer to government control for victim restitution or law enforcement funds. Civil forfeiture requires proving asset connection to criminal activity by preponderance of evidence. Innocent third parties may claim good-faith defenses, though layering sophistication often negates such claims.
How long do layering investigations typically take?
Timeline varies based on complexity, jurisdictional cooperation, and asset types. Domestic-only layering through traditional banking typically requires 2-4 months for complete investigation. Multi-jurisdiction cases involving offshore accounts extend to 6-12 months due to mutual legal assistance processing times. Cryptocurrency layering investigations average 4-8 months accounting for blockchain analysis complexity and exchange cooperation delays. High-priority cases may receive expedited processing, while resource-limited agencies investigating lower-value cases may experience 12-18 month timelines.
Professional Layering Investigation Services
Layering schemes separate criminal proceeds from their origins through complex transaction networks spanning multiple jurisdictions and financial systems. If you’re dealing with cryptocurrency theft, fraud investigation, or asset tracing, professional forensic analysis can make the difference between recovery and permanent loss.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We hold ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and have reconstructed layering schemes in hundreds of criminal investigations.
What we provide:
- Complete transaction reconstruction across traditional banking and cryptocurrency networks
- Cross-chain blockchain analysis tracking assets through mixers, bridges, and privacy coins
- Beneficial ownership investigation exposing shell companies and nominee arrangements
- International coordination with law enforcement and regulatory bodies
- Court-recognized expert testimony supporting prosecutions and asset recovery
We offer no upfront charge for non-custodial wallet recoveries – you only pay after successful fund recovery. For other services, we provide transparent project-based pricing.
Schedule a Free 30-Minute Case Assessment – We’ll review your situation, explain recovery options, and provide honest guidance on success probability and timeline.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- How to Track Blockchain Transactions: Expert Guide
- How to Trace Cryptocurrency Through Mixers: Expert Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- When Cryptocurrency Transactions Become Suspicious
About the Author
This guide was prepared by the blockchain forensics and financial crime investigation team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, money laundering detection, and asset recovery.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have reconstructed layering schemes in hundreds of criminal investigations, provided expert witness testimony in money laundering prosecutions, and recovered millions in assets for victims of cryptocurrency fraud.
For professional blockchain forensics, cryptocurrency fraud investigation, or AML compliance consulting, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Asset recovery outcomes depend on specific circumstances, criminal cooperation, and jurisdictional factors. Consult qualified professionals regarding your situation.