Last Updated: February 2026
Sybil transaction patterns are coordinated blockchain activities executed across multiple seemingly independent addresses that are actually controlled by a single entity attempting to create false impressions of organic network activity, manipulate protocol rewards, or obscure criminal operations. Detection relies on identifying behavioral correlations including synchronized transaction timing across addresses, identical fee calculation methodologies suggesting shared wallet software, coordinated UTXO spending patterns revealing common control, and network-level fingerprints exposing addresses connecting through shared IP addresses or nodes. These patterns appear in cryptocurrency fraud schemes, DeFi protocol exploitation, airdrop farming operations, and money laundering networks where criminals create illusions of distributed activity while maintaining centralized control.
At Crypto Trace Labs, our team detects Sybil patterns across hundreds of cryptocurrency fraud investigations and blockchain forensics cases. This guide draws on that decade of on-chain analysis experience to explain Sybil pattern detection, investigative methodologies, and real-world applications.
Key Takeaways
- Sybil attacks create false network diversity by operating 100-1,000+ addresses that appear independent but are actually controlled by single entities
- Detection accuracy reaches 85-95% when combining timing correlation analysis, behavioral fingerprinting, network topology examination, and transaction graph clustering
- Common applications include airdrop farming (creating fake users for token distributions), DeFi manipulation (inflating protocol metrics), and money laundering (obscuring fund flows)
- Timing precision reveals coordination – when 50 addresses execute transactions within 3-second windows repeatedly, single-operator control becomes evident
- Fee pattern consistency exposes shared infrastructure – addresses using identical fee calculation algorithms (within 0.1% variance) indicate common wallet software or automation
- Graph clustering algorithms identify networks by analyzing transaction flows detecting when seemingly independent addresses exhibit coordinated funding sources, consolidation destinations, or systematic interaction patterns
What Defines Sybil Transaction Patterns?
Sybil attacks derive their name from a psychiatric case study involving multiple personality disorder – one individual creating multiple identities. In blockchain contexts, single operators control numerous addresses presenting them as independent entities to achieve objectives requiring apparent network diversity.
The fundamental characteristic distinguishing Sybil patterns from legitimate multi-address usage is coordinated behavior inconsistent with independent operation. Legitimate users exhibit natural variance – different transaction timing, varied fee preferences, inconsistent UTXO management. Sybil operations exhibit systematic coordination – synchronized actions, identical methodologies, correlated patterns suggesting centralized control.
Criminal applications exploit protocol assumptions about user independence. DeFi platforms reward unique participation, airdrop distributions allocate to diverse holders, governance systems weight independent votes. Sybil attacks undermine these assumptions creating false diversity enabling disproportionate rewards, voting manipulation, or metric inflation.
Detection complexity varies with sophistication. Basic Sybil operations create obvious signatures – identical transaction structures, synchronized timing, shared funding sources. Advanced operations use multiple wallet implementations and randomized timing. However, even sophisticated networks exhibit detectable coordination patterns.
How Do Different Sybil Patterns Operate?
Comparison Table: Sybil Detection Methodologies
| Detection Method | Technical Approach | Detection Accuracy | Computational Cost | Evasion Difficulty | Best Application |
| Timing Correlation Analysis | Identify addresses executing transactions within suspicious time windows | 85-92% | Low | Medium | Automated Sybil operations, bot networks |
| Behavioral Fingerprinting | Detect identical patterns in fee selection, UTXO management, transaction structure | 80-88% | Medium | High | Shared wallet software, systematic operations |
| Network Topology Analysis | Map transaction graphs identifying systematic funding/consolidation patterns | 90-95% | High | Very High | Large-scale Sybil networks, airdrop farming |
| IP Address Correlation | Identify addresses broadcasting transactions from shared network nodes | 75-85% | Medium | Low | Basic Sybil operations lacking VPN/Tor usage |
| Statistical Clustering | Apply machine learning to group addresses exhibiting correlated behaviors | 88-94% | High | High | Complex patterns across multiple dimensions |
| Cross-Protocol Correlation | Detect addresses interacting with multiple protocols in coordinated patterns | 82-90% | Medium | Medium | DeFi manipulation, governance attacks |
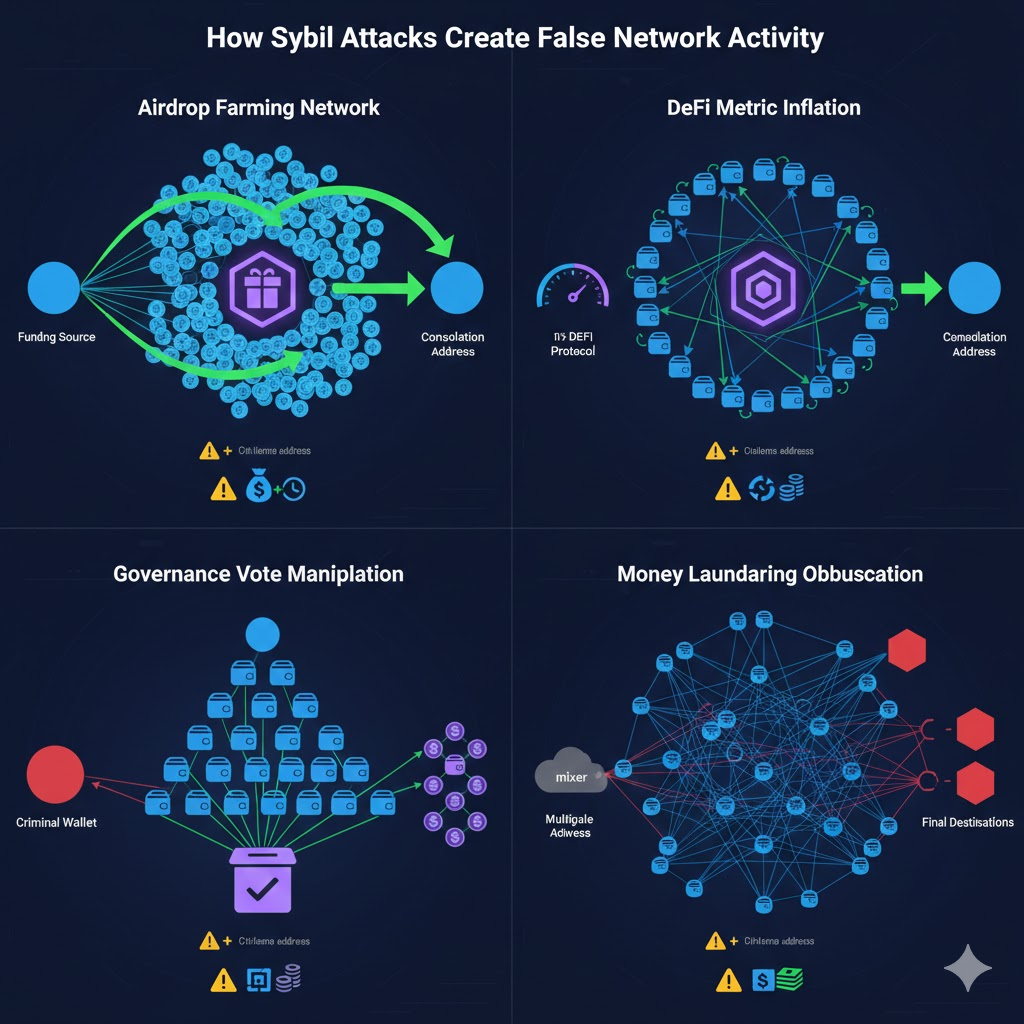
Airdrop farming Sybil networks create hundreds of addresses meeting token distribution criteria to claim disproportionate allocations. Operators fund addresses from common sources, execute minimum transactions, claim airdrops simultaneously, then consolidate tokens for sale.
DeFi protocol manipulation employs Sybil addresses inflating metrics protocols use to attract investment. Operators cycle funds across dozens of addresses repeatedly interacting with protocols, inflating Total Value Locked (TVL), transaction volumes, and unique user counts.
Governance vote manipulation distributes governance tokens across numerous addresses to circumvent voting power limitations. When protocols implement one-address-one-vote systems, operators split holdings across hundreds of addresses maximizing influence while creating illusions of community consensus.
Money laundering obfuscation fragments stolen funds across extensive Sybil networks creating investigative complexity. Rather than moving $1M through 10 addresses, criminals split across 500 addresses each processing $2,000, overwhelming manual analysis capabilities.
What Behavioral Patterns Expose Sybil Networks?
Numbered Listicle: 7 Sybil Detection Patterns Investigators Use
1. Synchronized Transaction Timing Across Address Clusters
When 50+ addresses execute transactions within 3-second windows repeatedly, timing precision indicates automated coordination impossible through independent manual operation. Investigators calculate transaction timestamp distributions discovering microsecond-level synchronization proving shared automation. Transaction tracking analysis reveals these temporal signatures enabling Sybil network identification.
2. Identical Fee Calculation Methodologies
Addresses controlled through shared wallet software exhibit identical fee selection algorithms. When 100 addresses calculate fees producing values within 0.1% variance, investigators recognize shared infrastructure. Legitimate users show fee variance exceeding 40% while Sybil networks exhibit variance under 5%.
3. Common Funding Source Patterns
Most Sybil networks require initial funding from centralized sources. Investigators trace backwards identifying when 50+ addresses all received initial funding from common sources, often through systematic distribution patterns (identical amounts, sequential timing, algorithmic splitting).
4. Coordinated UTXO Consolidation
After completing Sybil objectives, operators consolidate funds from distributed addresses back to centralized wallets. This consolidation creates distinctive patterns – dozens of addresses that appeared independent all send funds to common destinations within short timeframes.
5. Behavioral Clone Detection
Sybil addresses often exhibit identical patterns across multiple dimensions – same transaction structures, identical UTXO selection, matching decimal precision. Machine learning models analyzing dozens of behavioral dimensions calculate similarity scores. Address pairs exhibiting 95%+ similarity across 20+ dimensions indicate Sybil relationships.
6. Network-Level Fingerprints
Addresses broadcasting transactions through shared network infrastructure leave detectable fingerprints. When multiple addresses connect through identical IP addresses, shared VPN services, or common node configurations, network analysis reveals coordination.
7. Cross-Protocol Interaction Patterns
When 30 addresses all interact with identical sets of protocols in synchronized sequences – all providing liquidity to Protocol A, then voting in Protocol B, then claiming rewards from Protocol C – the correlated multi-protocol activity indicates coordinated control.
How Do Investigators Analyze Sybil Networks?
Graph clustering algorithms identify address groups exhibiting systematic transaction relationships. Investigators construct transaction graphs where addresses are nodes and transactions are edges, then apply community detection algorithms identifying clusters of addresses showing higher internal connectivity than external connectivity. Sybil networks naturally form dense clusters – addresses within the network transact frequently with each other while maintaining limited connections to external addresses.
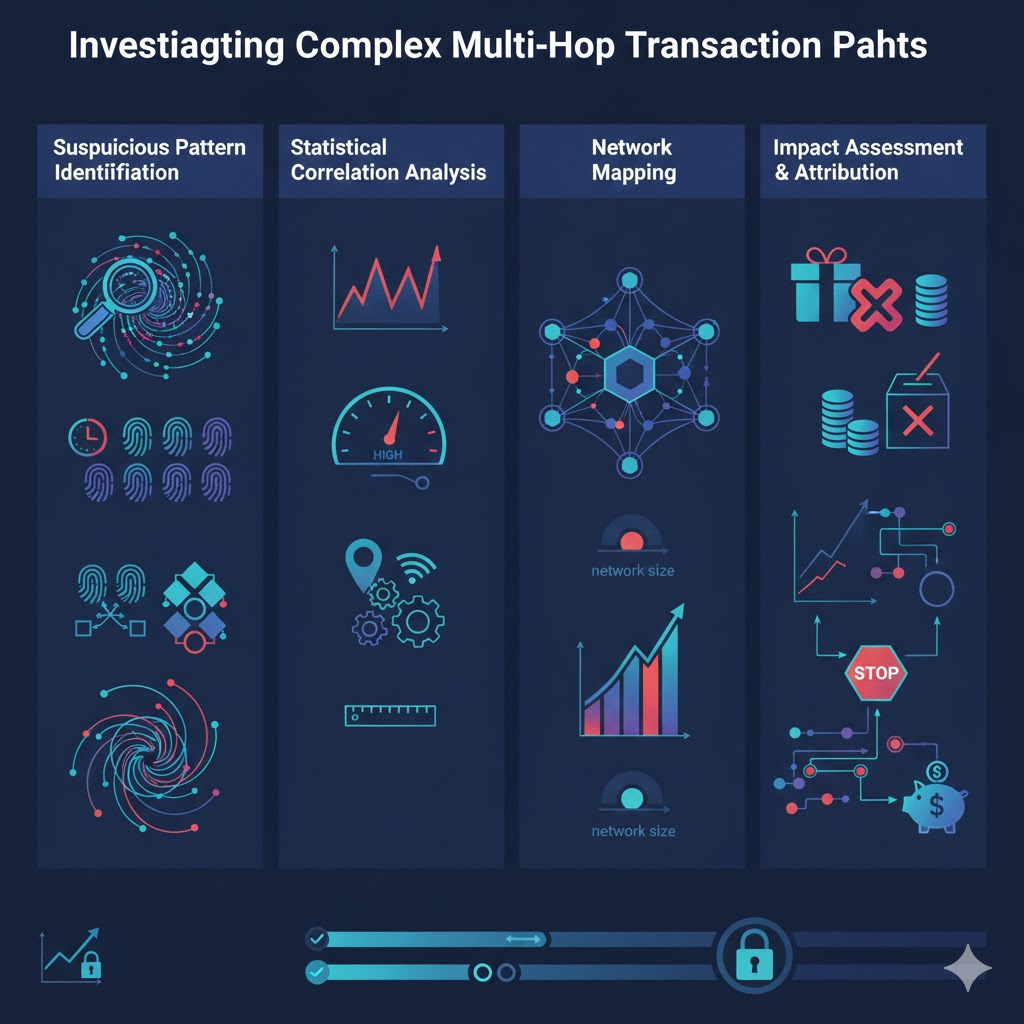
Behavioral fingerprinting compares addresses across dozens of transaction characteristics identifying systematic similarities. Investigators calculate similarity scores examining fee selection patterns, transaction timing distributions, UTXO management behaviors, decimal precision preferences, and smart contract interaction patterns. Addresses exhibiting 90%+ similarity across multiple dimensions indicate probable Sybil relationships requiring deeper investigation.
Machine learning models trained on confirmed Sybil networks and legitimate address groups predict Sybil probability for new address sets. These models learn subtle correlation patterns human analysts overlook, identifying when address groups exhibit statistical signatures consistent with coordination despite operators attempting randomization. Neural networks achieve 88-94% accuracy classifying address groups as Sybil or legitimate when trained on sufficient examples.
Funding source analysis traces backwards from suspected Sybil addresses to identify common origins. Even when operators introduce multiple intermediate hops between funding sources and operational addresses, systematic analysis reveals when address groups share funding origins or consolidation destinations. The funding/consolidation pattern often provides highest-confidence Sybil attribution because it demonstrates concrete financial relationships rather than purely behavioral correlations.
What Protocols Are Most Vulnerable?
Airdrop distributions represent primary Sybil attack targets due to economic incentives – free token distributions create profit opportunities justifying operational costs. Successful airdrops now implement anti-Sybil measures including social verification, proof-of-personhood systems, or retroactive distribution based on organic historical usage.
DeFi governance systems using one-address-one-vote enable Sybil manipulation. Operators split governance token holdings across addresses circumventing concentration limits. Modern governance implements quadratic voting, delegation mechanisms, or identity verification.
Proof-of-stake consensus employing stake distribution face Sybil risks when operators split stake across validators creating false decentralization. Advanced protocols implement stake-weighted selection or slashing conditions.
NFT minting and whitelist processes allocating limited supplies to wallet addresses incentivize Sybil attacks. Projects now implement wallet verification, social account linking, or proof-of-humanity requirements.
Frequently Asked Questions
How do investigators distinguish Sybil networks from legitimate multi-address usage?
Legitimate users controlling multiple addresses exhibit natural behavioral variance – different wallets use different fee algorithms, transactions occur at varied times based on actual needs, and addresses serve distinct purposes (savings, spending, trading). Sybil networks exhibit systematic coordination – addresses show identical fee selection patterns, synchronized transaction timing beyond coincidence probability, and behavioral cloning across multiple dimensions. Investigators calculate correlation coefficients across 20+ behavioral dimensions. Independent addresses typically score below 40% correlation while Sybil networks exceed 85%. Statistical significance testing determines whether observed correlations could occur through chance or prove coordination.
Can Sybil detection work across privacy-enhanced blockchains?
Privacy coins like Monero and Zcash obscure transaction graphs preventing direct address relationship analysis. However, Sybil detection remains possible through timing analysis (synchronized shielded transaction creation), amount pattern correlation (distinctive value distributions despite encryption), network-level fingerprints (shared transaction broadcast origins), and exchange interaction patterns (coordinated deposits/withdrawals). Privacy enhancement reduces detection accuracy from 90%+ on transparent blockchains to 65-75% on privacy chains, but sophisticated analysis combining multiple signals still identifies coordination patterns. Entry/exit points where privacy coins interface with transparent cryptocurrencies provide additional detection opportunities.
What false positive rates exist in Sybil detection?
False positive rates vary by methodology – timing correlation alone generates 15-25% false positives as coincidental synchronization occurs naturally, behavioral fingerprinting produces 8-12% false positives when users share popular wallet software, while combined analysis incorporating 5+ detection methods reduces false positives to 2-5%. Investigators mitigate false positives through multi-signal confirmation requiring addresses to trigger multiple independent detection methods before Sybil classification. Machine learning models trained on labeled datasets (confirmed Sybil networks and verified legitimate addresses) optimize decision boundaries minimizing false positives while maintaining high true positive rates.
How do criminals evade Sybil detection?
Sophisticated operators implement several evasion techniques: randomizing transaction timing across wide windows preventing correlation detection, using multiple wallet software implementations fragmenting behavioral signatures, introducing time delays between funding and operational phases obscuring source connections, routing through mixing services breaking transaction graph relationships, and coordinating activities across protocols and timeframes preventing pattern recognition. However, evasion introduces operational costs and inefficiencies. True randomization across dozens of addresses requires significant management overhead, time delays reduce operation profitability, and mixing services charge fees. The operational constraints limit evasion effectiveness enabling detection through second-order patterns.
How does Crypto Trace Labs detect Sybil patterns?
Our team applies multi-dimensional analysis combining automated detection with expert manual investigation. We maintain proprietary databases of confirmed Sybil network signatures enabling pattern matching against new address groups. Machine learning models trained on our investigation history predict Sybil probability with 88-94% accuracy. Network-level analysis correlates blockchain transaction data with IP address intelligence identifying shared infrastructure. Our investigators hold ACAMS certifications bringing financial crime expertise recognizing criminal operational patterns beyond purely technical signatures. We’ve successfully identified Sybil networks in airdrop fraud cases, DeFi manipulation investigations, and money laundering operations involving 500+ coordinated addresses.
Professional Sybil Pattern Detection Services
Sybil attack detection requires sophisticated analysis tools, behavioral expertise, and comprehensive blockchain data access that most organizations lack. Whether investigating airdrop fraud, DeFi manipulation, governance attacks, or criminal money laundering networks, professional forensic analysis can identify coordinated operations and quantify their impact.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We’ve detected Sybil networks across hundreds of investigations, from small-scale airdrop farming operations to sophisticated money laundering networks coordinating thousands of addresses.
What we provide:
- Multi-dimensional behavioral analysis across timing, fees, UTXO patterns, and network signatures
- Machine learning classification models achieving 88-94% Sybil detection accuracy
- Transaction graph analysis mapping complete network structures and funding relationships
- Cross-protocol correlation detecting coordinated activity across multiple DeFi platforms
- Network topology investigation identifying shared infrastructure and control points
- Impact quantification documenting attack objectives and financial consequences
For investigation services, we provide transparent project-based pricing based on network complexity and analysis requirements.
Schedule a Free Consultation – We’ll review your situation and explain how Sybil pattern detection can support your investigation or platform security.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- When Cryptocurrency Transactions Become Suspicious
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, fraud detection, and network analysis.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have identified Sybil attack networks in airdrop fraud investigations, DeFi manipulation cases, and criminal money laundering operations, working with protocol teams, law enforcement, and private investigators.
For professional blockchain forensics, Sybil pattern detection, or cryptocurrency fraud investigation services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Detection methodologies and legal frameworks vary by jurisdiction and context. Consult qualified professionals regarding your specific situation.





