Last Updated: February 2026
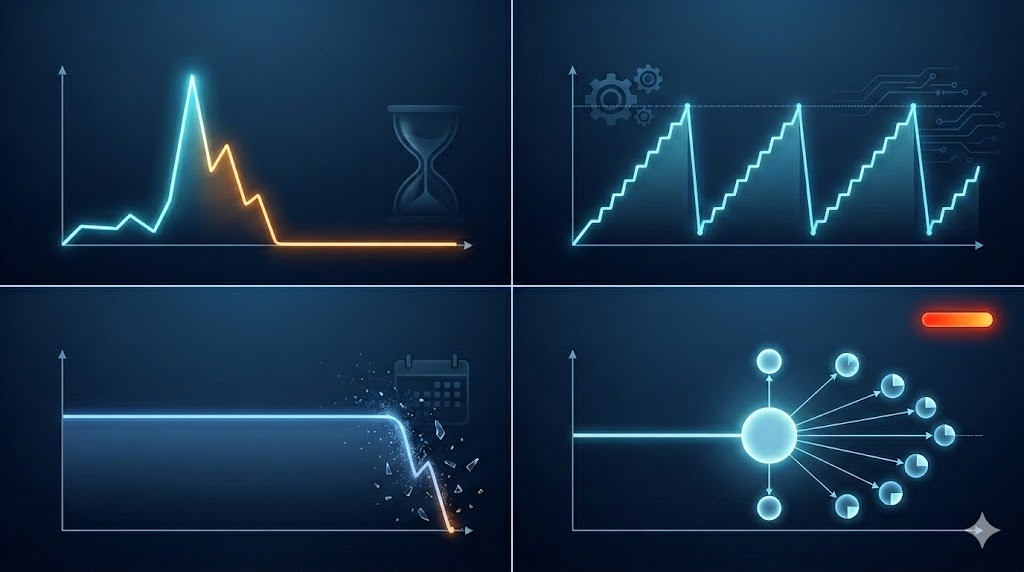
Wallet balance behavior patterns reveal criminal intent through systematic monitoring of balance fluctuations, threshold-triggered movements, rapid depletion cycles, dormancy periods, panic liquidation signals, and fragmentation strategies that distinguish criminal operations from legitimate business or personal cryptocurrency usage. Investigators analyze how criminals maintain operational balances (keeping minimal amounts preventing asset seizure), execute threshold-based transfers (moving funds immediately when balances exceed specific amounts), demonstrate urgency behaviors (complete wallet drainage within hours of receipt), employ dormancy tactics (leaving funds untouched for months avoiding detection), exhibit panic patterns (sudden liquidation during law enforcement activity), and implement fragmentation strategies (systematically splitting balances across numerous wallets). These behavioral signatures enable attribution because legitimate users maintain stable balances for actual usage, businesses show predictable operational patterns, while criminals reveal themselves through balance management prioritizing asset protection over operational efficiency.
At Crypto Trace Labs, our team analyzes wallet balance behaviors across hundreds of cryptocurrency investigations and blockchain forensics cases. This guide draws on that decade of transaction analysis experience to explain balance behavior analysis, criminal pattern detection, and investigative applications.
Key Takeaways
- Rapid depletion cycles indicate criminal urgency – wallets receiving large amounts ($50K-$500K) then depleting to near-zero within 24-48 hours signal laundering operations versus legitimate holdings
- Threshold-triggered movements reveal automated controls – addresses consistently transferring funds when balances reach specific amounts ($10,000, $50,000) expose systematic operational thresholds
- Extended dormancy followed by sudden activity suggests strategic timing – wallets inactive for 6+ months then rapidly liquidating indicate criminals waiting for investigation cooling-off periods
- Minimal operational balances prevent asset seizure – criminal operations maintaining $500-$2,000 working balances versus $50K+ holdings in offline storage demonstrate asset protection strategies
- Panic liquidation patterns correlate with law enforcement events – simultaneous wallet draining across criminal networks within 24-72 hours of arrests or seizures reveals coordinated responses
- Systematic fragmentation below reporting thresholds – maintaining multiple wallets each under $10,000 (FINCEN reporting threshold) indicates deliberate regulatory evasion
What Balance Patterns Distinguish Criminal Operations?
Legitimate cryptocurrency users maintain balances reflecting actual operational needs. Businesses keep working capital for expenses, traders maintain trading balances for market opportunities, long-term holders accumulate savings. These patterns show stability – balances fluctuate gradually reflecting genuine economic activity with predictable income/expense cycles.
Criminal operations exhibit artificial balance management prioritizing asset protection and detection evasion over operational efficiency. Stolen funds move immediately upon receipt rather than accumulating. Laundering operations maintain minimal working balances transferring excess immediately. Ransomware operators fragment collections across numerous addresses rather than consolidating efficiently.
Threshold-based movements create distinctive signatures. Criminals program automated systems transferring funds when balances exceed specific amounts – addresses receiving deposits consistently transfer everything above $10,000 within minutes. This systematic behavior reveals predetermined operational thresholds rather than organic financial decision-making.
Dormancy periods indicate strategic waiting. Criminals leave stolen funds untouched for months or years allowing investigation attention to diminish before attempting liquidation. When dormant addresses suddenly activate showing rapid balance depletion, investigators recognize strategic timing rather than forgotten wallet recovery.
Panic behaviors expose network-wide coordination. When law enforcement arrests operators or seizes infrastructure, connected addresses across criminal networks simultaneously drain balances within 24-72 hours. This coordinated panic liquidation reveals operational relationships invisible through transaction graph analysis alone.
How Do Investigators Analyze Balance Behaviors?
Comparison Table: Balance Behavior Analysis Methodologies
| Analysis Method | Technical Approach | Criminal Detection Rate | Investigation Value | False Positive Risk | Typical Applications |
| Rapid Depletion Detection | Flag wallets depleting >80% balance within 24-48 hours of receipt | 85-92% | Very High | Low (5-10%) | Stolen fund tracking, laundering detection |
| Threshold Pattern Analysis | Identify consistent transfer amounts or balance triggers | 90-95% | Very High | Very Low (2-5%) | Automated operation detection, bot identification |
| Dormancy-Activity Correlation | Track wallets inactive 90+ days then suddenly active | 75-85% | High | Medium (15-20%) | Strategic timing detection, cold storage differentiation |
| Balance Velocity Calculation | Measure balance turnover rate (total transferred ÷ average balance) | 80-88% | Medium-High | Medium (10-15%) | Business classification, operational profiling |
| Panic Pattern Detection | Identify coordinated balance liquidation across address groups | 88-94% | Very High | Low (3-8%) | Network mapping, law enforcement event correlation |
| Fragmentation Threshold Analysis | Detect systematic balance distribution below regulatory limits | 82-90% | High | Low (5-10%) | Regulatory evasion detection, sophisticated operator identification |
Rapid depletion detection flags addresses receiving large amounts then depleting to near-zero within 24-48 hours. Automated systems scan blockchain identifying wallets showing this pattern. While legitimate users occasionally empty wallets (closing accounts, consolidating holdings), consistent rapid depletion across multiple addresses indicates systematic criminal operations prioritizing quick movement over balance retention.
Threshold pattern analysis identifies wallets consistently transferring at specific balance levels. Machine learning models detect when addresses repeatedly transfer everything above $10,000, or always move funds when balances reach round numbers ($25,000, $50,000, $100,000). These precise thresholds indicate automated programmatic control rather than human decision-making.
Dormancy-activity correlation tracks wallets inactive for extended periods then suddenly liquidating. Investigators maintain watch lists of dormant addresses containing significant balances from known criminal sources. When addresses inactive for 6-24 months suddenly show activity, alerts trigger immediate investigation – criminals often wait for statute of limitations or investigation cooling before accessing funds.
Balance velocity calculation measures how rapidly funds cycle through wallets. Velocity = Total Amount Transferred ÷ Average Balance over time period. Legitimate businesses show velocity ratios of 2-5 (slow turnover). Criminal operations show ratios of 50-200+ (extremely rapid cycling). High velocity indicates wallets serving as pass-through infrastructure rather than genuine holdings.
What Specific Patterns Indicate Criminal Intent?
Numbered Listicle: 7 Balance Behaviors Exposing Criminal Operations
1. Complete Wallet Drainage Within Hours of Receipt
Ransomware operators and cryptocurrency thieves exhibit immediate depletion patterns. Addresses receive stolen funds ($100K-$1M), then within 2-6 hours transfer complete balances to mixing services or exchanges leaving exactly $0 remaining. This urgency reveals criminals prioritizing rapid movement over operational efficiency. Investigators at Crypto Trace Labs track these depletion cycles identifying laundering infrastructure through systematic rapid liquidation.
2. Round-Number Balance Thresholds Triggering Automated Transfers
Criminal operations employ automated systems transferring funds at predetermined thresholds. Addresses consistently holding maximum balances of exactly $10,000 or $50,000 before automatic transfers reveal programmatic controls. The mathematical precision (balances of $9,999.87, never exceeding $10,000.00) proves automated threshold enforcement enabling bot operation detection.
3. Strategic Dormancy Periods Followed by Coordinated Activation
Sophisticated criminals leave stolen funds dormant 6-24 months before liquidation attempts. During dormancy, addresses show zero activity. Sudden coordinated activation across multiple dormant addresses – 10 wallets inactive 18 months all activating within the same week – indicates criminal network coordination rather than coincidental forgotten wallet recoveries.
4. Minimal Hot Wallet Balances With Offline Cold Storage
Professional criminal operations maintain minimal balances in active “hot” wallets ($500-$5,000) while holding majority funds in offline “cold” storage addresses. This separation protects assets from seizure. Observing address groups with consistently low operational balances while related addresses hold $500K+ in cold storage reveals sophisticated asset protection strategies.
5. Systematic Fragmentation Below $10,000 FINCEN Threshold
FINCEN regulations require reporting transactions exceeding $10,000. Sophisticated criminals fragment holdings across numerous addresses each maintaining balances below $9,999. When networks show 20+ wallets each holding $7,000-$9,900 but never exceeding $10,000, deliberate threshold evasion becomes evident.
6. Panic Liquidation Correlating With Law Enforcement Activity
When law enforcement arrests operators, connected criminal networks exhibit coordinated panic liquidation. Within 24-72 hours of public arrests, dozens of addresses simultaneously drain balances transferring to exchanges or mixing services. This synchronized behavior reveals operational relationships through panic responses.
7. Balance Accumulation Followed by Mixing Service Deposits
Criminal addresses gradually accumulate proceeds over days ($500 daily reaching $10,000 total), then transfer entire balances to known mixing services in single transactions. This accumulation-then-mix pattern distinguishes criminal laundering from legitimate privacy users who employ mixing continuously rather than accumulating then mixing in obvious batches.
How Does Balance Analysis Enable Investigation?
Criminal network mapping exploits coordinated balance behaviors. When 15 addresses all maintain identical $9,900 thresholds and drain simultaneously during law enforcement activity, investigators map them as coordinated network members despite lacking direct transaction relationships. Balance synchronization reveals operational control relationships invisible through traditional transaction graph analysis.
Operational phase identification tracks criminal activity cycles through balance patterns. Accumulation phases show gradual balance increases from criminal proceeds. Layering phases show rapid balance fluctuations as funds move through mixing infrastructure. Cash-out phases show final balance depletions to exchange deposit addresses. Understanding which phase operations currently occupy guides investigation strategy and intervention timing.
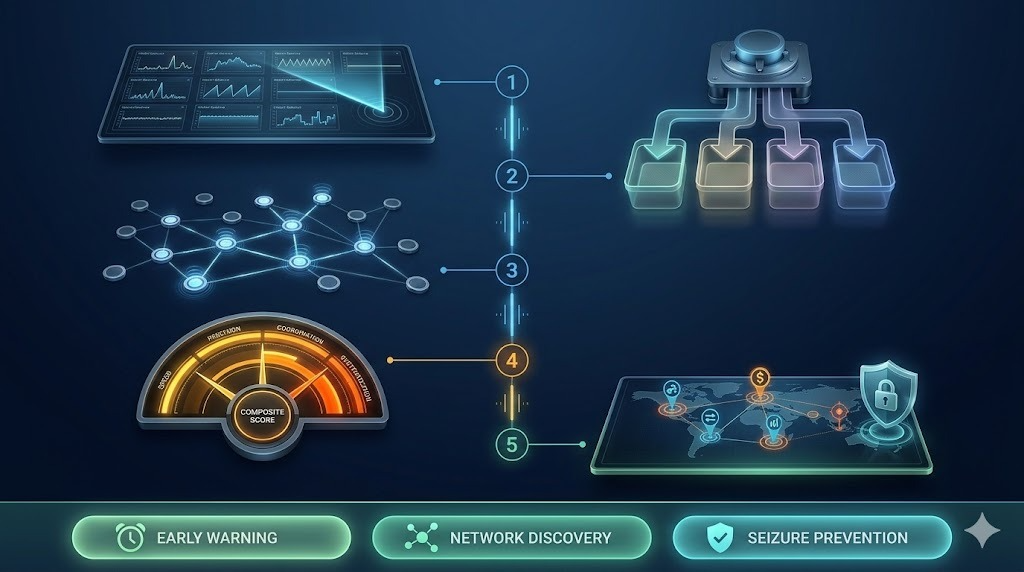
Asset seizure timing optimization prevents fund loss. When investigators identify rapid depletion patterns early (funds received but not yet moved), they can coordinate exchange freezes or seizure warrants before criminals complete transfers. Traditional investigation identifying addresses after funds already moved achieves limited recovery. Balance monitoring enables proactive intervention during critical 24-48 hour windows.
Sophisticated operator identification distinguishes professional criminals from amateurs. Systematic threshold management, strategic dormancy, and fragmentation patterns indicate technically capable operators requiring enhanced investigation resources. Amateur criminals showing simple rapid depletion without sophistication require different approaches. Resource allocation improves through accurate operator profiling.
Predictive monitoring enables proactive tracking. Identifying dormant criminal addresses containing significant balances enables watchlist monitoring. When these addresses activate, automatic alerts trigger immediate investigation preventing funds from moving through multiple layering hops before detection. This predictive capability transforms reactive investigation into proactive interdiction.
What Are Legitimate Balance Patterns?
Long-term holders accumulate cryptocurrency gradually maintaining stable or growing balances over months or years. Addresses show periodic purchases (monthly deposits), minimal outbound activity, and gradual accumulation curves. Balance grows from $10,000 to $50,000 over 24 months through regular additions. This contradicts criminal rapid cycling.
Active traders maintain working balances showing regular bidirectional flows. Trading addresses fluctuate but sustain balances – typical $25,000 balance varying between $20,000-$30,000 weekly without complete depletion. The sustainability differentiates trading from criminal pass-through operations.
Business operations maintain operational capital showing predictable patterns. Merchants accumulate customer payments, consolidate periodically, maintain working balances. Balance patterns align with business cycles – retail shows weekend accumulation, B2B shows monthly cycles. This predictability contrasts criminal irregularity.
Frequently Asked Questions
How do investigators distinguish criminal depletion from legitimate wallet closure?
Investigators apply multiple validation criteria. Criminal depletion shows systematic patterns across related addresses (10+ wallets depleting within 48 hours), suspicious timing (immediately following criminal activity), destination analysis (funds to mixing services), and coordination with criminal indicators. Legitimate closures show isolated incidents, reasonable timing (account consolidation), transparent destinations (known personal addresses), and lack of criminal history. False positive rates remain 5-10% requiring manual validation.
Can balance analysis work for privacy coins like Monero?
Privacy coins obscure transaction amounts making traditional balance tracking impossible. However, investigators can analyze timing patterns and activity frequency even without amount visibility. Monero addresses showing sudden activity after long dormancy create suspicious timing signals. Exchange integration points where Monero converts to/from transparent cryptocurrencies enable partial balance reconstruction. While privacy coins reduce effectiveness from 90% to 40-50% accuracy, timing correlation provides residual investigative value.
What balance thresholds most commonly indicate criminal automation?
Criminal operations most frequently implement thresholds around regulatory limits and round numbers. $10,000 USD (FINCEN threshold) appears most common, followed by $50,000, $100,000, and $25,000. Bitcoin-denominated thresholds cluster around 1 BTC, 10 BTC, and 100 BTC. Sophisticated operators employ random threshold variation ($9,200-$9,800) attempting evasion, but narrow variance itself proves automation. Investigators detecting thresholds within ±5% variance across multiple transactions classify as automated systems.
What intervention strategies exist when detecting criminal balance patterns?
Investigators employ several approaches depending on pattern type. For rapid depletion, exchange coordination enables asset seizure before funds exit. For threshold patterns, identifying next predicted transfer enables preemptive monitoring. For dormancy cases, long-term monitoring combined with address prediction enables intervention upon reactivation. For panic liquidation, timing correlation identifies network members. For fragmentation, regulatory enforcement compels exchange cooperation identifying beneficial owners.
How do balance patterns differ between ransomware, theft, and fraud operations?
Ransomware shows multiple small payments ($5K-$50K) from victims accumulating before periodic consolidation. Cryptocurrency theft exhibits immediate large receipts ($100K-$10M) followed by rapid fragmentation within hours. Fraud operations demonstrate gradual accumulation from many victims ($500-$5,000 each), periodic withdrawals for expenses, and eventual complete depletion as operators exit. These signatures enable crime type classification guiding investigation approach.
Professional Balance Behavior Analysis
Wallet balance behavior analysis requires continuous blockchain monitoring, pattern recognition expertise, and statistical modeling capabilities that most organizations lack. Whether investigating cryptocurrency theft, money laundering, or fraud operations, professional balance analysis can detect criminal intent, predict operational phases, and enable proactive intervention.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We’ve analyzed balance behaviors across hundreds of investigations, from individual theft cases to sophisticated criminal networks employing multi-wallet fragmentation and strategic dormancy.
What we provide:
- Real-time balance monitoring detecting rapid depletion and threshold patterns
- Criminal intent scoring through multi-dimensional behavioral analysis
- Predictive modeling forecasting next operational phases
- Coordinated panic detection revealing network relationships
- Dormancy watchlists tracking high-value inactive addresses
- Asset seizure timing optimization enabling proactive intervention
For investigation services, we provide transparent project-based pricing based on monitoring scope and analysis complexity.
Schedule a Free Consultation – We’ll review your situation and explain how balance behavior analysis can support your investigation.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- How to Trace Cryptocurrency Through Mixers: Expert Guide
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, behavioral analysis, and forensic investigation.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed wallet balance behaviors in hundreds of investigations, developed automated pattern detection systems, and provided expert testimony explaining criminal intent through balance analysis.
For professional blockchain forensics, balance behavior analysis, or cryptocurrency investigation services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Balance behavior analysis and criminal intent determination vary based on specific circumstances and jurisdictional standards. Consult qualified professionals regarding your situation.





