Last Updated: February 2026
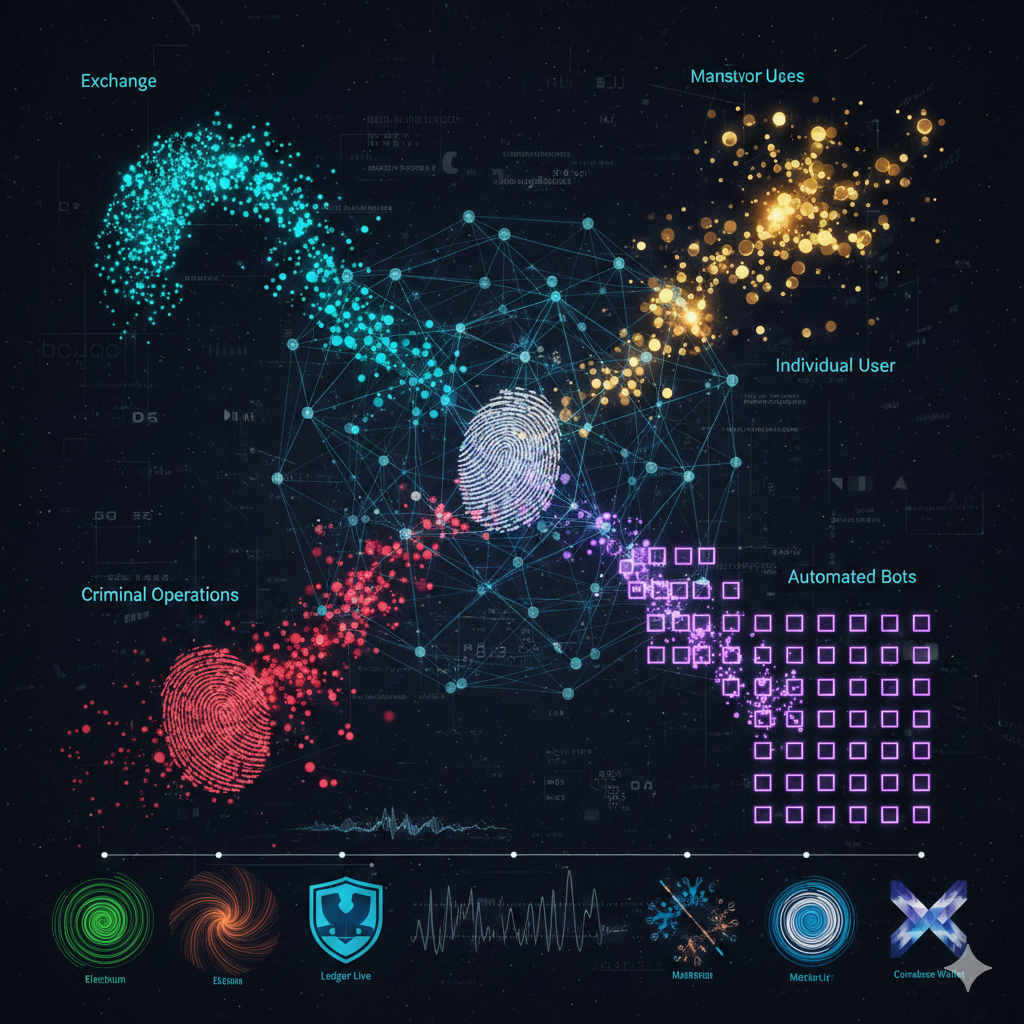
Transaction fee patterns reveal wallet owner identities, operational sophistication, and behavioral fingerprints through consistent fee selection strategies, priority preferences, timing correlations, and software-specific algorithms. Cryptocurrency users exhibit distinctive fee behaviors – exchanges batch transactions using algorithmic fee calculations, individual users make sporadic manual selections, criminal operations prioritize speed over cost, and automated systems generate mathematically consistent fee structures. Forensic investigators analyze these patterns to attribute addresses to specific entities, distinguish between human and automated operations, identify wallet software types, and correlate seemingly unrelated transactions through shared fee calculation methodologies.
At Crypto Trace Labs, our team analyzes transaction fee patterns across hundreds of blockchain forensics and cryptocurrency investigation cases. This guide draws on that decade of on-chain analysis experience to explain fee pattern analysis, attribution methodologies, and investigative applications.
Key Takeaways
- Fee patterns create behavioral fingerprints distinguishing exchanges (algorithmic consistency), individual users (manual variability), criminals (speed priority), and automated systems (mathematical precision)
- Wallet software generates distinctive signatures – Electrum, Ledger Live, MetaMask, and Coinbase Wallet each implement unique fee estimation algorithms detectable through pattern analysis
- Priority preferences reveal user sophistication – experienced users optimize fees (5-10 sat/vB), novices overpay (50+ sat/vB), criminals prioritize speed regardless of cost
- Fee timing correlations enable clustering – addresses consistently using identical fee rates during specific time windows indicate common ownership or shared software infrastructure
- Round-number fees signal automation – fees of exactly 100, 200, or 500 satoshis across multiple transactions prove algorithmic generation rather than manual selection
- Privacy-focused users exhibit counter-intuitive patterns – intentionally random fees, deliberately high fees masking as urgent, or custom fee policies avoiding default calculations
What Information Do Transaction Fees Contain?
Bitcoin and Ethereum transactions require fees compensating miners or validators for including transactions in blocks. Users specify fee amounts based on desired confirmation speed – higher fees prioritize transactions during congestion, while lower fees suffice when blocks have space. The fee selection process reveals significant behavioral and operational intelligence.
Fee calculation methodology varies dramatically across user types. Cryptocurrency exchanges employ sophisticated algorithms analyzing mempool conditions and optimizing fees across thousands of daily transactions. Individual users typically accept wallet defaults or manually adjust based on urgency. Criminal operations prioritize speed over cost, often overpaying significantly to ensure rapid confirmations when laundering stolen funds.
Wallet software developers implement proprietary fee estimation algorithms creating distinctive signatures. Electrum calculates fees differently than Ledger Live, which differs from MetaMask. These algorithmic differences produce detectable patterns when analyzing transaction histories.
Temporal fee patterns provide additional attribution signals. Users in specific time zones transact during local daytime hours, creating geographic fingerprints. Automated systems generate transactions at precise intervals regardless of time, revealing bot operations.
How Do Different Entities Generate Fee Patterns?

Comparison Table: Fee Pattern Analysis Methodologies
| Entity Type | Fee Calculation Method | Typical Fee Range (BTC) | Variance Pattern | Detection Accuracy | Primary Indicators |
| Major Exchanges | Algorithmic optimization across batches | 2-8 sat/vB | Very Low (CV <0.15) | 85-92% | Batch transactions, consistent algorithms, optimal rates |
| Individual Users | Wallet defaults with occasional manual adjustment | 5-50 sat/vB | High (CV >0.40) | 70-80% | Sporadic activity, wide variance, timezone correlation |
| Criminal Operations | Speed-priority regardless of cost | 50-200+ sat/vB | Medium (CV 0.20-0.35) | 75-85% | Consistent overpayment, urgency during low-congestion |
| Automated Systems | Fixed or algorithmic with precise execution | Varies by design | Very Low (CV <0.10) | 90-95% | Mathematical precision, timing consistency, round amounts |
| Privacy-Conscious Users | Custom or randomized to avoid fingerprinting | Intentionally varied | Deliberately High (CV >0.50) | 60-70% | Anti-correlation with network conditions, random selection |
| Custodial Services | Standardized across customer withdrawals | 10-20 sat/vB | Low (CV 0.15-0.25) | 80-88% | Uniform customer withdrawal fees, batch processing timing |
Exchange operations exhibit algorithmic consistency optimizing fees across thousands of transactions daily. Platforms like Coinbase implement dynamic fee estimation adjusting to mempool conditions every few minutes, creating tight clustering around optimal rates. When investigators observe addresses consistently using fees within narrow ranges that track network congestion patterns, exchange attribution becomes probable.
Individual users show high variance reflecting manual decision-making and urgency fluctuations. Someone sending cryptocurrency to purchase goods might accept default recommendations (8 sat/vB), while the same user sending urgent payments during price volatility might manually increase fees (45 sat/vB). The behavioral variance creates distinctive patterns distinguishing individuals from algorithmic operations.
Criminal operations prioritize confirmation speed over cost optimization. When laundering stolen funds, criminals pay premium fees ensuring rapid confirmations even during low-congestion periods when such fees are unnecessary. This behavioral pattern – consistently high fees regardless of network conditions – signals urgency-driven operations rather than cost-conscious legitimate use.
What Wallet Software Creates Distinctive Fee Signatures?
Numbered Listicle: 7 Wallet Software Fee Calculation Signatures
1. Electrum Wallet – Target-Based Fee Estimation
Electrum implements target-based fee estimation where users select confirmation time targets (next block, 2-3 blocks, 4-6 blocks) and the wallet calculates appropriate fees. This creates distinctive patterns where fees cluster around specific confirmation thresholds. Investigators identify Electrum usage when fees consistently align with mempool-predicted confirmation times rather than arbitrary manual selections.
2. Ledger Live – Conservative Fee Recommendations
Ledger hardware wallet software generates notably conservative fee recommendations erring toward higher fees to ensure confirmation reliability. Users accepting Ledger defaults consistently overpay 15-30% compared to optimal rates. When addresses show consistent 20-25% premium over prevailing optimal fees across months, Ledger Live usage becomes probable attribution.
3. MetaMask – Gas Price Oracle Integration
MetaMask integrates multiple gas price oracles for Ethereum fee estimation, creating distinctive patterns based on oracle selection preferences. Transaction tracking analysis reveals MetaMask signatures through gas price values matching specific oracle API responses at transaction broadcast times.
4. Coinbase Wallet – Exchange-Optimized Algorithms
Coinbase Wallet implements fee algorithms optimized for exchange deposit/withdrawal patterns, creating signatures distinguishing it from non-exchange wallets. The software prioritizes confirmation reliability for exchange interactions while optimizing fees for peer-to-peer transfers, generating dual-mode fee patterns detectable through transaction purpose analysis.
5. Blockchain.com Wallet – Default Fee Tiers
Blockchain.com wallet offers three default fee tiers (Regular, Priority, Custom) that users select for each transaction. Analysis reveals trimodal fee distributions clustering around the three tier values rather than continuous fee ranges. Fee histograms showing three distinct peaks indicate Blockchain.com usage.
6. Wasabi Wallet – Privacy-Optimized Fee Randomization
Wasabi Wallet implements deliberate fee randomization to prevent behavioral fingerprinting, ironically creating distinctive anti-correlation patterns. The wallet adds random variations to calculated fees preventing exact repetition. Investigators identify Wasabi usage when fee patterns show intentional randomization that doesn’t correlate with network conditions.
7. Hardware Wallet Firmware – Version-Specific Algorithms
Trezor and Ledger hardware wallets implement fee estimation in device firmware, creating version-specific signatures when firmware updates modify algorithms. Multiple addresses controlled by users who update firmware simultaneously exhibit correlated fee pattern shifts at identical timestamps, revealing common ownership through coordinated updates.
How Do Investigators Use Fee Patterns for Attribution?
Fee consistency analysis clusters addresses exhibiting similar fee calculation methodologies across time. When 15 addresses all use fees consistently 5-7% above optimal rates and share transaction timing patterns, investigators attribute common ownership. The clustering confidence increases when fee patterns correlate with other signals including address reuse or UTXO consolidation timing.
Temporal correlation detection identifies coordinated operations through synchronized fee pattern changes. When network congestion doubles and specific address clusters all adjust fees using identical percentage increases within 3-hour windows, centralized control becomes evident.
Urgency fingerprinting distinguishes legitimate operations from criminal activity. Businesses optimize costs maintaining consistent fee policies, while criminals laundering stolen funds prioritize speed generating distinctive overpayment patterns. When addresses consistently pay 3-5x optimal fees during low-congestion periods, investigators flag potential criminal urgency.

Software fingerprinting matches fee patterns to specific wallet implementations. By maintaining databases of wallet-specific fee calculation algorithms, investigators determine which software generated observed transactions. This attribution enables targeted investigation strategies.
Cross-account fee correlation exposes related addresses through shared fee selection behaviors. When analyzing ransomware operations, investigators identify payment collection and laundering addresses through correlated fee patterns – both address sets use identical fee calculation methodologies suggesting common control despite no direct transaction relationships.
What Privacy Techniques Defeat Fee Analysis?
Custom fee policies randomize amounts preventing consistent pattern formation. Privacy-conscious users manually select different fee rates for each transaction avoiding wallet defaults. However, true randomization requires understanding network conditions – poorly implemented “randomization” still creates detectable patterns.
CoinJoin transactions complicate fee analysis by combining inputs from multiple unrelated parties. When 30 users contribute inputs to collaborative transactions, the resulting fee represents collective rather than individual selection. However, CoinJoin coordination services often implement standardized fee policies creating new fingerprints.
Mixing service usage obscures fee pattern continuity by fragmenting funds across intermediate addresses. Criminals deposit cryptocurrency to mixers which distribute outputs using service-controlled addresses with distinct fee behaviors. However, mixer entry/exit points still exhibit user-controlled fee patterns enabling partial reconstruction through mixer tracing techniques.
Time-delayed transactions defeat temporal correlation by spacing transactions across extended periods with varied fees. Instead of rapid sequential transfers exhibiting correlated behaviors, sophisticated operators wait hours between transactions, manually selecting divergent fees preventing clustering.
Frequently Asked Questions
How accurate is fee-based wallet attribution?
Fee pattern analysis alone achieves 70-90% accuracy depending on transaction sample sizes and pattern distinctiveness. Individual heuristics like fee consistency or wallet software fingerprinting perform at 60-75% accuracy, while combining multiple signals including temporal correlation, UTXO patterns, and network behaviors increases accuracy to 85-95%. False positives occur when unrelated users coincidentally select similar fees or use identical wallet software with default settings. Investigators verify fee-based attribution through corroborating evidence including address clustering, entity resolution, and behavioral analysis.
Can fee patterns identify individual users versus organizations?
Fee variance analysis reliably distinguishes individual users (high variance, sporadic activity, manual selections) from organizational operations (low variance, algorithmic consistency, high volume). Organizations like exchanges or payment processors generate thousands of transactions weekly using automated fee optimization, creating tight statistical distributions. Individuals make sporadic transactions with highly variable fees reflecting manual decision-making and urgency fluctuations. Coefficient of variation calculations quantify this distinction – organizational operations typically show CV values below 0.20 while individual users exceed 0.40.
How do criminals attempt to evade fee pattern analysis?
Sophisticated criminals implement several evasion techniques: randomizing fees across transactions preventing consistency detection, using multiple wallet software types to fragment fingerprints, deliberately matching network-optimal fees avoiding overpayment patterns, time-delaying transactions preventing temporal correlation, and routing through mixing services breaking fee pattern continuity. However, even sophisticated evasion creates new detectable patterns – intentional randomization exhibits statistical signatures distinguishing it from organic variance, and multi-wallet usage reveals itself through software transition timing correlations.
Can fee analysis work across different cryptocurrencies?
Fee pattern analysis principles apply across Bitcoin, Ethereum, and other cryptocurrencies, though specific implementations vary. Bitcoin uses satoshis per virtual byte (sat/vB), Ethereum uses gwei for gas prices, and other chains implement different fee mechanisms. The fundamental behavioral patterns remain consistent – exchanges optimize algorithmically, individuals show high variance, criminals prioritize speed. Investigators adapt analysis methodologies to chain-specific fee structures while applying universal behavioral fingerprinting principles. Cross-chain correlation becomes possible when users exhibit consistent relative behaviors – someone consistently overpaying on Bitcoin likely overpays on Ethereum, creating attribution signals across multiple blockchains.
Professional Fee Pattern Analysis Services
Transaction fee analysis provides powerful attribution signals that traditional blockchain forensics often overlooks. When combined with address clustering and network analysis, fee patterns significantly improve investigation accuracy and enable attribution in cases where conventional methods fail.
Our team at Crypto Trace Labs applies advanced statistical modeling and machine learning to fee pattern analysis. With VP and Director-level experience from Blockchain.com, Kraken, and Coinbase, we’ve developed proprietary algorithms identifying wallet software signatures, detecting automated operations, and clustering addresses through fee behaviors.
What we provide:
- Fee pattern statistical analysis identifying entity types and wallet software
- Temporal correlation detection revealing coordinated operations and common ownership
- Wallet software fingerprinting determining specific implementations
- Cross-chain fee behavior analysis tracking users across multiple blockchains
- Combined analysis integrating fee patterns with address clustering and entity resolution
We offer no upfront charge for non-custodial wallet recoveries. For investigation services, we provide transparent project-based pricing.
Schedule a Free Case Assessment – We’ll analyze your situation and explain how fee pattern analysis can strengthen your investigation.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- How to Trace Cryptocurrency Through Mixers: Expert Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, transaction analysis, and forensic investigation.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have developed proprietary fee pattern analysis algorithms, provided expert witness testimony in cryptocurrency cases, and recovered millions in assets through advanced forensic techniques.
For professional blockchain forensics, cryptocurrency investigation, or fee pattern analysis services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Investigation outcomes depend on specific circumstances, data availability, and technical factors. Consult qualified professionals regarding your situation.