Last Updated: March 2026
Atomic swap forensics is the discipline of reconstructing peer-to-peer cross-chain trades using Hash Time-Locked Contract (HTLC) analysis. Because atomic swaps execute without a centralized exchange, they produce no custodial record, no KYC data, and no deposit address that can be subpoenaed. However, the cryptographic mechanism that makes atomic swaps trustless also makes them traceable: the shared hash preimage revealed on both blockchains creates an immutable, public cryptographic link between the two sides of every completed swap.
Crypto Trace Labs specializes in cross-chain and multi-blockchain investigation, including atomic swap forensics, HTLC contract analysis, and asset tracing across networks where no centralized intermediary exists.
Key Takeaways
- 1. The hash preimage revealed when an atomic swap completes is publicly broadcast on both blockchains, providing a cryptographically verifiable link between the two sides of every trade.
- 2. HTLC forensic analysis extracts the hash, preimage, wallet addresses, amounts, timestamps, and timelock parameters from both chain A and chain B transactions.
- 3. Investigators search chain B for HTLC contracts containing the same hash discovered on chain A, using cross-chain graph databases or block explorer APIs.
- 4. Expired HTLC refunds also carry forensic value, identifying wallets that attempted but did not complete a cross-chain swap.
- 5. HTLC-derived evidence is cryptographically immutable and, when documented by a qualified expert, is suitable for legal proceedings.
Why This Matters
Atomically swapped assets have historically been described as forensically opaque because no exchange holds records. This characterization is incorrect. Every completed atomic swap leaves a cryptographic fingerprint on both blockchains in the form of the hash preimage, and every failed swap leaves the original HTLC lock and refund. As privacy-preserving cross-chain techniques become more accessible to retail users, investigators who understand HTLC mechanics can reconstruct asset flows that compliance teams and courts would otherwise accept as untraceable. The methodological gap between what is technically possible and what most forensic practitioners actually apply is where cross-chain investigations are won or lost.
How HTLC Contracts Create Traceable Cross-Chain Links
Hash Time-Locked Contracts are the cryptographic primitive underlying atomic swaps. An HTLC locks funds behind two conditions: the correct preimage to a hash (the hashlock) or the expiry of a timelock. Party A creates an HTLC on chain A locking Bitcoin behind hash H. Party B creates a mirroring HTLC on chain B locking ETH behind the same hash H. When Party A reveals the preimage P (where SHA-256(P) = H) to claim the ETH, the preimage becomes publicly visible in the chain B transaction. Party B then uses P to claim the Bitcoin on chain A. Both preimage references are permanently recorded on their respective blockchains.
The forensic consequence is direct: any investigator who observes the preimage P on chain B can compute H and search chain A for the matching HTLC. The link is cryptographic, not inferential. There is no probabilistic clustering required, only deterministic hash matching.

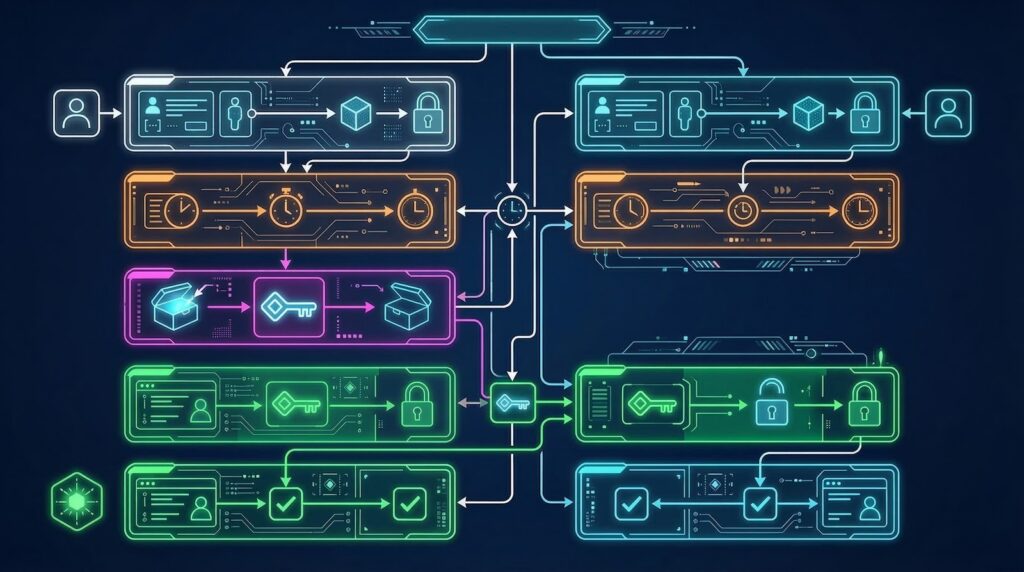
The Step-by-Step HTLC Forensic Extraction Process
Atomic swap forensic analysis follows a structured extraction sequence regardless of which chains are involved.
Step 1 – Identify the HTLC on chain A. The investigator locates a suspicious transaction locking funds into a script containing OP_HASH256 (Bitcoin) or calling an HTLC contract (Ethereum). Bitcoin HTLCs are identifiable by their non-standard P2SH or P2WSH output scripts; Ethereum HTLCs call a known HTLC contract ABI.
Step 2 – Extract the hash H. Decoding the HTLC script or contract call reveals the 32-byte hash committed to by the swap initiator.
Step 3 – Search chain B for H. Cross-chain graph databases index all HTLC deployments by their committed hash. The investigator queries chain B’s HTLC contract registry for entries where hashlock == H.
Step 4 – Extract wallet addresses and amounts. Both the chain A sender and the chain B recipient addresses are extracted, along with amounts on each side, establishing the complete swap record.
Step 5 – Confirm with timestamp correlation. Chain A lock, chain B lock, chain B claim, and chain A claim timestamps are compared against the HTLC timelock window. Valid swaps complete within the timelock; the four timestamps form a predictable sequence.
Atomic Swap Tracing vs. Bridge Forensics
Atomic swaps and blockchain bridges both enable cross-chain asset movement, but their forensic profiles are entirely different. Understanding the distinction prevents investigators from applying the wrong methodology.
| Factor | Atomic Swap (HTLC) | Blockchain Bridge |
|---|---|---|
| Tracing mechanism | Shared cryptographic hash preimage | Bridge contract + custodian records |
| On-chain link | Deterministic (hash matching) | Inferential (deposit/mint correlation) |
| Centralized record | None | Bridge operator often maintains logs |
| Forensic data richness | Both wallets, amounts, timestamps on both chains | Depends on bridge architecture |
| Failed trade evidence | HTLC refund visible on chain | Typically no partial record |
| Legal subpoena potential | N/A (decentralized) | Bridge operator may be subpoenable |
| Tool support | Specialized cross-chain HTLC indexers | Standard address graph tools |
| Complexity | Moderate (requires script decoding) | Variable by bridge type |
Atomically swapped assets leave more forensically rich on-chain data than many bridged transfers, particularly when the bridge relies on centralized custodians whose records investigators cannot access.
Challenges in Bitcoin-Ethereum Atomic Swap Forensics
Bitcoin and Ethereum use fundamentally different scripting paradigms, which creates specific challenges for cross-chain HTLC analysis.
Bitcoin HTLCs use Script opcodes, specifically OP_IF, OP_HASH256, OP_EQUALVERIFY, OP_ELSE, OP_CHECKLOCKTIMEVERIFY, and OP_ENDIF. These are decoded from the witness or redeem script of P2SH/P2WSH inputs. Investigators must decode raw Bitcoin Script bytecode, which is not natively parsed by most forensic platforms.
Ethereum HTLCs use Solidity contracts. The investigator must decode the ABI-encoded newContract() call to extract the hashlock bytes32 parameter. Multiple competing HTLC contract implementations exist on Ethereum, including Hashed Timelock Agreements (HTLAs) and ERC-20 HTLC variants, each with slightly different ABI signatures.
Cross-chain matching requires knowing the hash function used on each side. Bitcoin typically uses SHA-256 twice (OP_HASH256); Ethereum contracts may use SHA-256 or Keccak-256. The investigator must confirm which hash function applies before attempting to match H from chain A to H on chain B.
How Expired HTLC Refunds Identify Failed Swap Attempts
Not every atomic swap completes. When a swap fails, the HTLC timelock expires and funds refund to the original sender. From a forensic perspective, these failed swaps are not invisible – they are documented by two transactions: the initial HTLC lock and the timelock refund.
Expired HTLC refunds identify:
- The wallet address that attempted the cross-chain swap
- The asset and amount the wallet intended to swap
- The approximate time window of the attempted trade
- Whether the failure was a dry run, a coordination failure, or a deliberate abort
Investigators analyzing wallets implicated in illicit activity should inspect all HTLC-type transactions, including those that refunded. A pattern of frequent HTLC initiations with high refund rates may indicate a wallet testing swap infrastructure before executing a successful cross-chain transfer.
Producing Court-Ready Atomic Swap Evidence
HTLC forensic findings must be documented to legal evidence standards to be admissible in court proceedings. A court-ready atomic swap forensic report includes:
Transaction identifiers. Both the chain A and chain B transaction hashes for every HTLC involved in the swap, including lock and claim (or refund) transactions.
Cryptographic evidence. The hash H, the preimage P, confirmation that SHA-256(P) = H, and which hash function was applied on each chain.
Wallet addresses. All sending and receiving addresses on both blockchains, with derivation documentation explaining how each address was extracted from the HTLC contract or script.
Amounts and timestamps. Asset quantities on each chain, block heights, and Unix timestamps for all four HTLC transaction events.
Methodology statement. A clear explanation of the tools used (with version numbers), the queries performed, and the logical steps connecting chain A to chain B evidence.
This documentation package allows opposing experts to independently reproduce the findings, which is a requirement for forensic evidence in most legal jurisdictions.
Frequently Asked Questions
What is an atomic swap in blockchain forensics?
An atomic swap is a peer-to-peer cross-chain trade executed using Hash Time-Locked Contracts (HTLCs). Both sides complete simultaneously or neither does, with no exchange intermediary. For forensic investigators, atomic swaps create a tracing gap between blockchains that must be bridged using cryptographic secret correlation and timestamp analysis.
How do HTLC contracts work in atomic swaps?
HTLCs lock funds on each blockchain behind a cryptographic hash preimage. Party A locks Bitcoin with hash H; Party B locks ETH with the same hash H. When Party A reveals the preimage to claim ETH, Party B sees the revealed secret on-chain and uses it to claim Bitcoin. Both preimage reveal transactions are publicly visible and linkable.
Can atomic swaps be traced by investigators?
Yes. The shared cryptographic preimage revealed on both blockchains is the primary tracing link. Investigators locate the hashlock address on chain A, identify the preimage reveal transaction, then search chain B for transactions using the identical preimage. Timing correlations within the HTLC timelock window provide secondary confirmation of the swap pair.
What data does HTLC analysis extract from atomic swap transactions?
HTLC forensic analysis extracts: the cryptographic hash used to lock both sides, the preimage (secret) revealed during claim, transaction timestamps and block heights on both chains, the sending and receiving wallet addresses, asset amounts exchanged, and the timelock expiry parameters. Together these reconstruct the complete cross-chain trade record.
What blockchains support atomic swaps?
Atomic swaps work between any blockchains that support HTLC scripting: Bitcoin, Litecoin, Decred, and Ethereum-compatible networks. Cross-chain swaps between Bitcoin and Ethereum require additional protocol layers since Ethereum uses ERC-20 token HTLC contracts rather than native Bitcoin Script opcodes. Each combination has distinct forensic extraction approaches.
How do investigators find the matching HTLC on the second blockchain?
The preimage revealed on chain A is publicly broadcast. Investigators compute SHA-256(preimage) = H and search chain B’s mempool and confirmed transaction data for HTLC contracts containing the same hash H. Specialized cross-chain graph tools index HTLC contracts by hash across multiple networks, enabling automated matching within seconds of chain A confirmation.
What happens when HTLC timelocks expire without claim?
If the swap is not completed before the timelock expires, funds refund to the original sender. From a forensic standpoint, expired HTLC refunds are also valuable: the original lock and refund transaction pair still identify the wallet that attempted the swap. Attempted-but-failed swaps can indicate dry runs, failed coordination, or deliberate abort strategies.
How is atomic swap forensics different from bridge forensics?
Atomic swaps are peer-to-peer with on-chain cryptographic linkage through shared hash preimages. Bridges use lock-and-mint mechanisms where a custodian or smart contract on chain A holds assets while wrapped tokens are minted on chain B. Bridge forensics requires tracing the bridge contract’s custodian records, whereas atomic swap forensics uses cryptographic proof visible on both public ledgers.
Can atomic swap forensics support legal proceedings?
Yes. HTLC analysis produces cryptographically verifiable evidence: both the hash preimage and the on-chain transactions referencing it are immutable public records. A forensic report citing the hash, preimage, block heights, and wallet addresses on both chains constitutes evidence admissible in court when prepared by a qualified expert and documented with a reproducible methodology.
What tools are used for atomic swap HTLC forensics?
Forensic investigators combine: Bitcoin Script decoders to parse HTLC opcodes, Ethereum HTLC contract ABI decoders for ERC-20 swaps, cross-chain graph databases indexed by hash preimage, block explorer APIs for both networks, and timestamp correlation tools. Commercial platforms like Chainalysis and Elliptic have added cross-chain tracing modules that include atomic swap detection.
Executive Summary
Atomic swap forensics uses the shared cryptographic hash preimage inherent in HTLC-based cross-chain trades to deterministically link transactions on separate blockchains. Unlike probabilistic clustering, HTLC forensic linkage is mathematically verifiable: the hash preimage is publicly broadcast on both chains during every completed swap. A structured five-step extraction process identifies wallet addresses, asset amounts, timestamps, and timelock parameters on both sides of the trade. Expired HTLC refunds extend forensic coverage to failed attempts. With proper methodology documentation, HTLC-derived evidence meets legal admissibility standards and supports court proceedings involving cross-chain asset movement.
What Should You Do Next?
If you need to trace assets moved through atomic swaps or reconstruct cross-chain transaction histories, the HTLC forensic methodology described here provides a definitive starting point. For investigations requiring expert analysis, legal-standard documentation, or court-ready reporting, Crypto Trace Labs offers specialist cross-chain and multi-blockchain investigation services. Contact our team to discuss the specific chains, swap protocols, and timeframes involved in your case.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- Cross-Chain Forensics: Tracking Assets Through Blockchain Bridges
- How Do Blockchain Bridges Complicate Cryptocurrency Tracing?
- How Do Investigators Track Cryptocurrency Across Multiple Blockchains?
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm founded by VP and Director-level executives formerly of Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across the UK, US, and EU, and Chartered Fellow Grade status at the CMI. With over 10 years of experience in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin for clients in the last 12 months and delivered record fraud reduction for a $14bn crypto exchange. We work with law enforcement agencies, regulated financial institutions, and private clients on crypto asset recovery, blockchain forensics, AML compliance, and expert witness testimony – globally. We offer no upfront charge for non-custodial wallet recoveries. Contact us
Disclaimer: This article is for informational and educational purposes only. Nothing in this article constitutes legal advice. Always consult a qualified legal professional for advice specific to your situation. Crypto Trace Labs does not guarantee specific investigation outcomes.





