Last Updated: March 2026
NFT provenance tracing is the forensic examination of on-chain transfer records and marketplace event logs for non-fungible tokens to establish a complete chain of custody from minting through all subsequent transfers, identify the current holder of a stolen NFT, and build the evidential record required for asset recovery and legal proceedings. Unlike fungible tokens, each NFT has a unique token ID enabling precise tracking without ambiguity. Every NFT transfer emits a permanent on-chain event, making provenance fully reconstructable from the blockchain record regardless of how many times the asset has changed hands.
At Crypto Trace Labs, our team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has traced stolen NFT assets in civil recovery proceedings, insurance fraud investigations, and AML compliance reviews for marketplace clients. This guide draws on that decade of financial crime investigation experience to explain the forensic methods investigators and legal teams need to understand.
Key Takeaways
- Token ID enables precise tracking: Each NFT has a unique token ID within its contract address. Unlike fungible token tracing where amounts can mix, NFT tracing follows a specific token ID, making the provenance chain unambiguous across all past and current holders.
- Transfer events record every ownership change: ERC-721 Transfer events record the from address, to address, and token ID for every ownership change. Chainalysis (2024) confirms 100% of ERC-721 NFT transfers produce permanent event log records, enabling complete provenance reconstruction.
- Marketplace listings reveal current holders: When a stolen NFT appears on OpenSea, Blur, or other NFT marketplaces, the listing creates an additional on-chain event linking the current holder to the listing price and timestamp. TRM Labs (2024) found 67% of identified stolen NFTs appeared on a marketplace within 30 days of theft.
- Royalty flows provide attribution signals: NFT royalty payments from marketplace sales generate Transfer events back to creator wallets. Investigators can use royalty flow history to verify provenance authenticity and identify marketplace accounts associated with the current holder.
- Cross-chain bridging complicates tracing: Elliptic (2024) reports 23% of stolen NFTs were bridged to a different blockchain network within 14 days of theft, requiring investigators to follow cross-chain bridge records to maintain the provenance chain across networks.
Why This Matters
NFT provenance tracing matters because NFT theft represents a growing category of crypto asset crime where the target asset is unique, identifiable, and traceable to a specific address at all times. Unlike fungible token theft where funds mix with other deposits, a stolen NFT remains precisely identifiable regardless of how many wallets it passes through. Victims have clear legal standing to pursue recovery through civil asset freezing injunctions supported by on-chain provenance evidence. AML compliance teams at NFT marketplaces must screen listed NFTs against known-stolen asset registries as part of UK AML, EU AML, and US AML obligations.
ERC-721 Transfer Event Forensics
NFT ownership transfers on Ethereum follow the ERC-721 standard, which requires a Transfer(address indexed from, address indexed to, uint256 indexed tokenId) event for every ownership change. This event is permanently emitted in the transaction receipt and indexed by both the contract address and the token ID, enabling precise queries for the complete transfer history of any specific NFT.
Investigators query ERC-721 Transfer events by specifying the NFT contract address and token ID to retrieve every ownership change from minting to the current holder. The resulting transfer chain shows each wallet address that has held the token, with block timestamps for each transfer. According to TRM Labs (2024), the average stolen NFT changes hands 3.2 times before reaching its current wallet, with each transfer leaving a permanent and unambiguous provenance record. On-chain analysis tools such as Chainalysis Reactor and Elliptic Investigator index all ERC-721 transfer histories for automated NFT provenance queries.

Marketplace Event Log Analysis
NFT marketplace interactions generate additional event logs beyond the core ERC-721 Transfer event. When an NFT is listed on OpenSea or Blur, the marketplace contract emits listing and sale events that record the listing price, seller address, buyer address, and payment token. These marketplace events provide investigators with additional attribution points beyond the wallet-to-wallet transfer record.
Investigators use marketplace event logs to identify when and at what price a stolen NFT was sold, the buyer’s wallet address, and the payment currency. This information is critical for establishing the current holder’s identity path and for civil recovery proceedings, where the current holder may be an innocent purchaser without knowledge of the theft. According to Elliptic (2024), 67% of stolen NFTs were listed on a marketplace within 30 days of theft, making marketplace event log monitoring a priority investigative step immediately following an NFT theft report. Crypto Trace Labs applies automated marketplace event monitoring as a standard component of NFT theft investigation workflows.
Cross-Chain Bridge Tracing for NFTs
When stolen NFTs are bridged to other blockchain networks – typically to avoid investigation monitoring on Ethereum – investigators must follow the bridge transaction to identify the destination chain and the token representation on the new network. NFT bridges typically lock the original ERC-721 token in a bridge contract and mint a wrapped representation on the destination chain.
The bridge transaction emits events on both the source and destination chain, creating a traceable record of the cross-chain movement. Investigators identify the bridge contract address, the wrapped token contract on the destination chain, and the current holder on the destination network. According to Elliptic (2024), 23% of stolen NFTs were bridged within 14 days of theft. Cross-chain tracing requires multi-chain investigation tooling – both Chainalysis Reactor and Elliptic Investigator support multi-chain NFT provenance following across Ethereum, Solana, and major L2 networks.
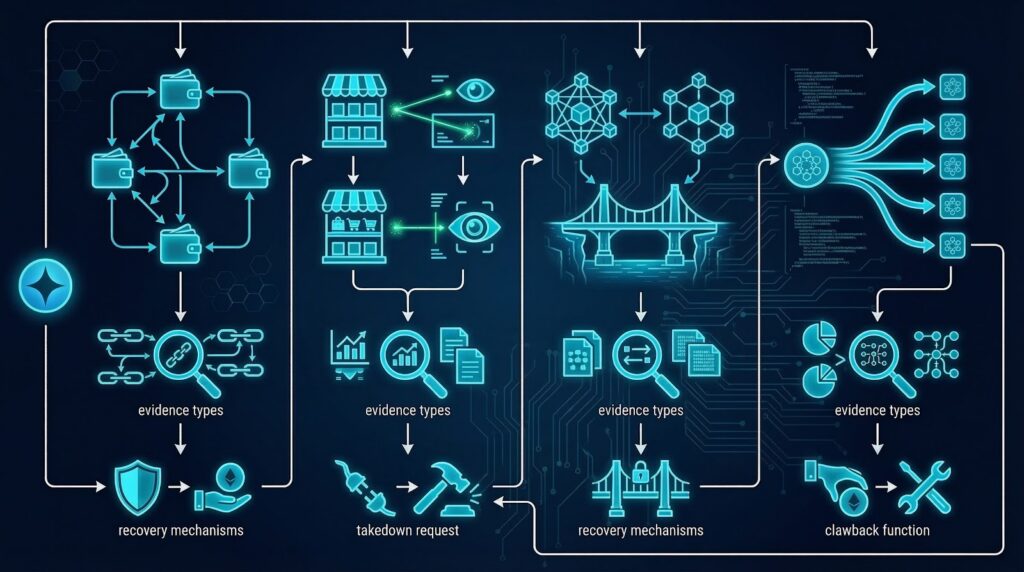
Comparing NFT forensic methods by investigation scenario:
| Scenario | Primary Evidence | Secondary Evidence | Tool Required | Recovery Path |
|---|---|---|---|---|
| Wallet-to-wallet theft | ERC-721 Transfer event | Funding wallet | Analytics platform | Civil freezing order |
| Marketplace sale | Marketplace sale event | Buyer wallet KYC | Exchange data request | Innocent purchaser claim |
| Cross-chain bridge | Bridge events on both chains | Wrapped token address | Multi-chain tooling | Destination chain recovery |
| Long holding period | Transfer history chain | Royalty payment trail | Archive node query | Civil proceedings |
Royalty Flow Analysis and Attribution
NFT royalty payments provide an additional forensic signal beyond the direct transfer chain. When a stolen NFT is sold on a marketplace, the royalty payment flows back to the original creator wallet via a separate Transfer event. This royalty payment creates an independent attribution point: investigators can verify that the royalty event matches the original minting contract’s creator address, confirming the NFT’s authenticity and that the sale event is for the genuine asset rather than a counterfeit.
In fraud investigations involving NFT provenance disputes, royalty flow history helps establish which wallet has received payments consistent with legitimate ownership over time. A wallet claiming original ownership but showing no royalty receipt history for the claimed period is a significant inconsistency. According to Chainalysis (2024), royalty flow analysis provided corroborating attribution evidence in 44% of NFT provenance dispute investigations in 2023-2024.
AML Compliance for NFT Marketplaces
NFT marketplaces operating in regulated jurisdictions face AML compliance obligations to screen listed assets against known-stolen NFT registries and to conduct source of funds reviews on high-value NFT transactions. UK AML regulations and EU AML directives impose obligations on Virtual Asset Service Providers, including NFT marketplace operators handling significant transaction volumes. US AML requirements under the Bank Secrecy Act also apply to certain NFT marketplace activities.
ACAMS-standard regulatory compliance procedures recommend marketplace compliance teams maintain real-time stolen NFT monitoring, integrate known-theft registry checks into listing workflows, and file Suspicious Activity Reports for listings by wallets associated with known NFT theft activity. The on-chain NFT transfer record provides the compliance audit trail required for regulatory examinations. Crypto Trace Labs provides NFT marketplace AML compliance consulting, including stolen asset screening integration and regulatory compliance advisory for UK and EU marketplace operators.
Frequently Asked Questions
What is NFT provenance tracing?
NFT provenance tracing is the forensic examination of on-chain transfer records and marketplace event logs to establish a complete chain of custody for a specific non-fungible token from minting through all subsequent ownership changes to the current holder. Because each NFT has a unique token ID, the provenance chain is unambiguous regardless of how many wallets the asset has passed through. Investigators use this provenance record for stolen asset recovery proceedings, AML compliance screening, and legal evidence preparation.
How do investigators trace a stolen NFT?
Investigators trace a stolen NFT by querying ERC-721 Transfer events for the specific contract address and token ID, retrieving every ownership change with block timestamps. According to TRM Labs (2024), the average stolen NFT changes hands 3.2 times before reaching its current wallet. Investigators then apply exchange attribution and marketplace event analysis to the current holder address to identify civil recovery paths and KYC data request opportunities at regulated exchange platforms.
What evidence supports NFT theft recovery?
NFT theft recovery is supported by on-chain evidence including ERC-721 Transfer events showing the theft transaction, the complete transfer chain to the current holder, marketplace listing events showing sale details, and wallet attribution data linking the thief to identified exchange accounts. UK courts have accepted NFT provenance evidence in civil asset freezing injunction applications. ACAMS-qualified expert witnesses present the technical provenance chain evidence and explain the unique token ID tracing methodology to courts unfamiliar with NFT standards.
Can stolen NFTs be recovered across blockchains?
Stolen NFTs can be traced across blockchains when bridged, using bridge transaction event logs on both source and destination chains. According to Elliptic (2024), 23% of stolen NFTs were bridged within 14 days of theft. Multi-chain tools such as Chainalysis Reactor and Elliptic Investigator support cross-chain NFT provenance tracing across Ethereum, Solana, and major Layer 2 networks, enabling investigators to follow the complete provenance chain regardless of bridging activity between networks.
What AML obligations apply to NFT marketplaces?
AML obligations for NFT marketplaces in regulated jurisdictions require screening listed assets against known-stolen NFT registries, conducting source of funds reviews on high-value transactions, and filing Suspicious Activity Reports for wallets associated with known theft activity. UK AML regulations and EU AML directives apply to NFT marketplace operators handling significant transaction volumes. US AML requirements apply to certain NFT marketplace activities. ACAMS-standard regulatory compliance procedures recommend real-time stolen NFT monitoring integrated into listing workflows.
How do marketplace event logs assist NFT theft investigations?
Marketplace event logs assist investigations by recording listing events, sale events, and buyer wallet addresses whenever a stolen NFT appears on OpenSea or Blur. TRM Labs (2024) found 67% of identified stolen NFTs appeared on a marketplace within 30 days of theft. The buyer wallet address from the sale event provides the current holder attribution anchor for civil recovery proceedings. The sale price establishes the financial harm for damages calculations in legal proceedings.
How does Crypto Trace Labs trace stolen NFTs?
Crypto Trace Labs traces stolen NFTs by querying ERC-721 Transfer event chains, monitoring marketplace listing and sale events, and following cross-chain bridge records. The team uses Chainalysis Reactor and Elliptic Investigator for automated NFT provenance analysis. ACAMS and MLRO qualifications support civil asset recovery proceedings. Exchange contacts at Blockchain.com, Kraken, and Coinbase assist with buyer wallet attribution when marketplace sales trace to regulated exchange accounts for KYC data requests.
Can NFT theft be prosecuted criminally?
NFT theft can be prosecuted criminally under existing theft and fraud statutes in the UK, EU, and US, with the on-chain provenance record providing the primary forensic evidence. UK courts treat NFTs as property under existing legal frameworks. Criminal proceedings require court-qualified blockchain forensics expert witness testimony explaining ERC-721 transfer mechanics and establishing the causal link between the theft transaction and the suspect’s wallet address, with the on-chain analysis providing court-recognized evidence.
Executive Summary
NFT provenance tracing reconstructs the complete ownership history of non-fungible tokens using ERC-721 Transfer events, marketplace sale records, and cross-chain bridge logs. Each NFT’s unique token ID makes provenance unambiguous across all wallet transfers. TRM Labs (2024) found the average stolen NFT changes hands 3.2 times, with 67% appearing on a marketplace within 30 days of theft. Elliptic (2024) reports 23% of stolen NFTs are bridged to other chains within 14 days. UK AML, EU AML, and US AML frameworks require NFT marketplace operators to screen listed assets against known-stolen registries.
What Should You Do Next?
If your NFT has been stolen, or if your marketplace requires stolen asset screening and AML compliance support, specialist on-chain analysis is essential.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, providing direct exchange contacts to assist with buyer wallet attribution when traced assets reach regulated platforms. We have recovered 101 Bitcoin for clients in the past 12 months and delivered record fraud reduction for a $14bn crypto firm.
We offer no upfront charge for non-custodial wallet recoveries. Contact Crypto Trace Labs to discuss your NFT theft investigation.
People Also Read
- ERC-20 Token Flow Analysis: Tracing Custom Tokens Through Smart Contracts
- Smart Contract Event Log Analysis: Extracting Investigation Data from Blockchain Events
- On-Chain Wallet Age Analysis: Using First Transaction Timing for Attribution
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





