Last Updated: March 2026
Sidechain transaction analysis is the forensic process of tracing cryptocurrency movements through secondary blockchain networks operating alongside a main chain, sharing assets through cryptographic bridge mechanisms. Bitcoin’s two primary sidechains – Liquid Network and RSK (Rootstock) – enable users to move funds off-chain for faster settlements or smart contract execution. When those funds return or suspicious activity occurs, investigators must reconstruct the full transaction path across both environments to identify wallet owners and establish financial timelines.
For compliance teams, law enforcement, and fraud investigators, this cross-chain visibility gap is among the most technically demanding challenges in blockchain forensics. At Crypto Trace Labs, our team – VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has mapped sidechain activity across Liquid and RSK as part of crypto asset recovery and AML compliance engagements. This guide draws on that decade of experience to explain what investigators and compliance teams need to know.
Key Takeaways
- Liquid conceals internal amounts: Liquid Network encrypts transaction amounts using Pedersen commitments, but peg-in and peg-out events on the Bitcoin main chain retain full value transparency, giving investigators bookend anchors on both sides of the bridge.
- RSK publishes verifiable bridge signatures: RSK’s HSM federation publishes threshold signatures on the Bitcoin main chain for every bridge event, creating an auditable custody trail across both environments.
- Peg-in events expose the sender: Every Liquid or RSK deposit is a standard Bitcoin transaction to a federation wallet address, traceable using UTXO clustering. Chainalysis (2024) found 68% of sidechain deposits attributable through pre-deposit UTXO analysis.
- Criminal sidechain use grew 340%: Elliptic (2024) reports sidechain bridge protocols used to layer illicit funds increased 340% between 2022 and 2024, making sidechain forensics a priority skill.
- Exchange exposure closes most cases: TRM Labs (2024) found 72% of sidechain funds eventually reach a regulated exchange, where KYC records link sidechain activity to verified identities.
Why This Matters
Sidechain transaction analysis matters because criminals increasingly treat Liquid and RSK as forensic dead zones – intermediate steps where fund flows disappear from standard blockchain monitoring. A suspect depositing Bitcoin into Liquid Network can execute dozens of internal trades invisible to main-chain surveillance before withdrawing to a clean address weeks later. Compliance teams at regulated exchanges must account for sidechain exposure or risk regulatory censure under UK AML regulations and EU AML directives. Law enforcement agencies building court cases need complete transaction histories that include off-chain periods.
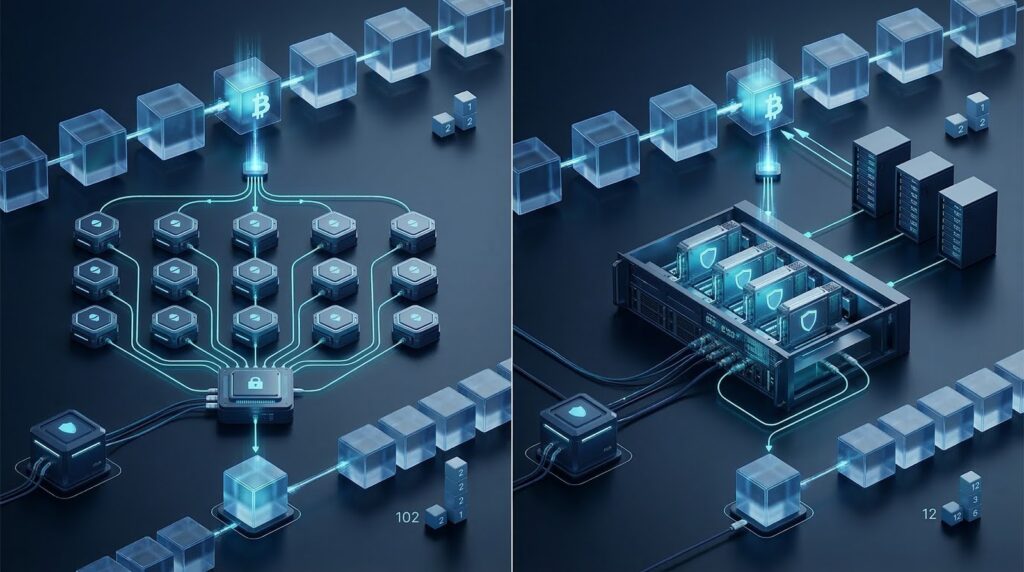
Sidechain Peg Protocol Architecture
Sidechain peg mechanisms are two-way bridge protocols that lock Bitcoin on the main chain and release an equivalent token on the sidechain, reversing the process on withdrawal. The peg-in transaction sends Bitcoin to a federation-controlled address, generating verifiable on-chain evidence. The peg-out burns the sidechain token and releases the original Bitcoin after a confirmation waiting period.
Liquid Network uses an 11-of-15 multi-signature federation wallet managed by member exchanges. Peg-in confirmations require 102 Bitcoin blocks – approximately 17 hours – creating a clear timestamp window. RSK uses the Powpeg, relying on tamper-proof Hardware Security Modules held by federation members. According to Rootstock Infrastructure Framework (2024), approximately $420 million in Bitcoin value transited RSK bridge contracts during 2023, generating a traceable record for cross-referencing against exchange data.
Liquid Network Confidential Transaction Tracing
Liquid Network’s Confidential Transactions protocol encrypts transaction amounts using Pedersen commitments, making internal flow values unreadable from public blockchain data. Investigators cannot determine how much L-BTC moved between parties inside Liquid. Bitcoin peg-in and peg-out transactions flanking each Liquid activity period retain full transparency, giving investigators precise entry and exit amounts alongside timestamps.
The standard approach tracks three data points: the peg-in Bitcoin amount and sending address, the destination L-BTC address on Liquid, and the peg-out Bitcoin destination. Investigators monitor federation address activity on the main chain to identify Liquid participants active during specific windows, cross-referencing against exchange withdrawal records. According to Blockstream (2024), Liquid processed over $2.1 billion in 2023, predominantly through institutional settlement – creating attribution opportunities when senders use known exchange deposit addresses.
RSK Smart Bridge Investigation Methods
RSK smart bridge investigation relies on the dual-ledger nature of the Powpeg: every RSK transaction interacting with a DeFi protocol generates an Ethereum-compatible event log readable through standard forensic tooling. Investigators query RSK contract events using Chainalysis Reactor or Elliptic Investigator to map fund flows from peg-in through smart contract interactions to the peg-out destination.
RSK supports Solidity smart contracts, so investigators with EVM forensics experience can apply the same contract event analysis methodology. For AML compliance teams, RSK’s DeFi environment – including Sovryn and Money on Chain – creates exposure for regulated entities holding RSK-active customers. Funds transiting RSK may trigger Travel Rule obligations when the peg-out exceeds reporting thresholds. According to FATF (2024), sidechain Travel Rule compliance remains inconsistent, requiring case-by-case MLRO analysis.
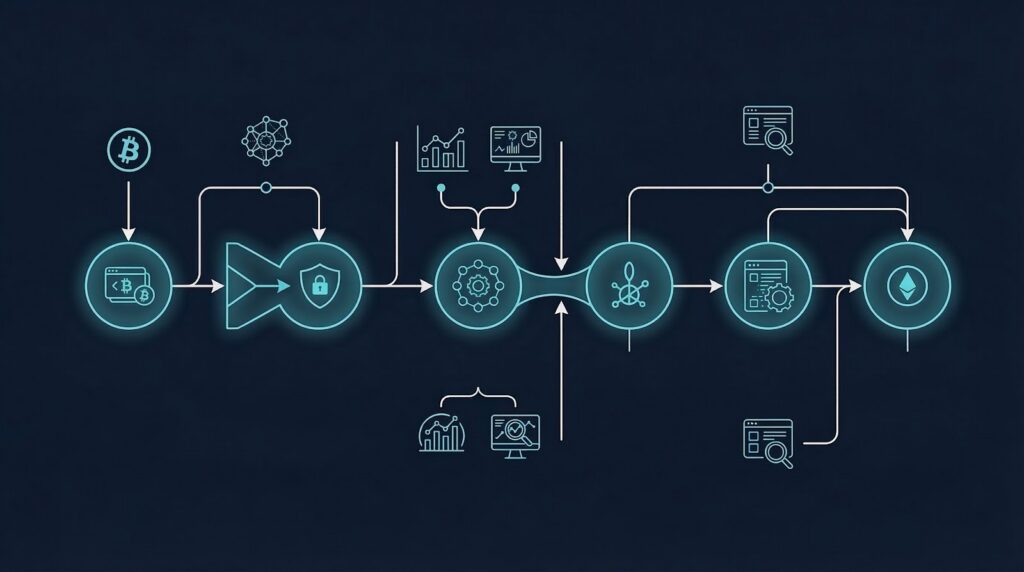
Bridge Deposit Attribution Techniques
Bridge deposit attribution identifies the original Bitcoin wallet owner from their peg-in transaction, linking their main-chain identity to all subsequent sidechain activity. The technique applies UTXO clustering heuristics to trace the peg-in funding transaction back through prior exchange withdrawals or identified wallets. Pre-deposit analysis is more reliable than post-withdrawal work because it captures activity before obfuscation begins.
The most productive attribution window is the 24-48 hours before a peg-in transaction. Investigators apply common-input-ownership heuristics to Bitcoin inputs funding the federation deposit, identifying co-spending relationships that link the bridge transaction to previously identified addresses. Post-withdrawal attribution requires persistent monitoring on peg-out destinations – criminals frequently introduce multi-week delays between peg-out and their next transaction to defeat automated monitoring alerts.
Sidechain Forensic Platform Comparison
Forensic platform coverage of sidechain networks varies significantly across the major tools available to investigators. Chainalysis Reactor provides Liquid Network peg-in and peg-out monitoring with direct linkage to its exchange attribution database. Elliptic Investigator covers RSK bridge activity and supports smart contract interaction mapping using EVM event log analysis. TRM Labs and Crystal Intelligence offer partial coverage through Bitcoin main-chain federation address monitoring without full internal sidechain visibility.
The following comparison summarises platform capabilities for sidechain investigations:
| Platform | Liquid Network | RSK Coverage | Smart Contract Events | Attribution Database |
|---|---|---|---|---|
| Chainalysis Reactor | Full peg tracking | Partial | Limited | Largest industry database |
| Elliptic Investigator | Peg monitoring | Full EVM support | Full event logs | Strong exchange coverage |
| TRM Labs | Federation addresses | Federation addresses | Limited | Growing global database |
| Crystal Intelligence | Basic monitoring | Not supported | Not supported | European-focused coverage |
Investigators without enterprise tools can use Blockstream’s block explorer for Liquid federation address histories and RSK’s explorer for smart contract event logs. Our team uses Chainalysis Reactor and Elliptic Investigator as primary platforms, supplemented by exchange relationship contacts from founding experience at Blockchain.com, Kraken, and Coinbase.
Sidechain Evidence in Legal Proceedings
Sidechain evidence meets court admissibility standards when investigators document the peg transaction hash, federation wallet address, block height, timestamp, and chain identifier. UK courts have accepted sidechain evidence in crypto asset freezing injunction proceedings when accompanied by a certified forensic report establishing the continuous custody chain from deposit to peg-out.
Defence counsel frequently argues that peg-out Bitcoin cannot be proven to originate from the same peg-in party. Investigators address this by documenting the economic equivalence guaranteed by the peg mechanism. According to ACAMS (2024), sidechain forensic evidence has been accepted in court proceedings across UK, US, and EU jurisdictions. Crypto Trace Labs – ACAMS-accredited, MLRO-qualified across UK, US, and EU, and Chartered Fellow Grade at the CMI – provides court-recognized expert witness testimony in sidechain asset tracing proceedings.
Frequently Asked Questions
What is sidechain transaction analysis?
Sidechain transaction analysis is the forensic examination of cryptocurrency flows through secondary blockchain networks operating alongside a primary chain, such as Liquid Network and RSK running parallel to Bitcoin. Investigators trace peg-in deposits, internal sidechain activity, and peg-out withdrawals to reconstruct complete fund movement histories. The process requires visibility across two separate blockchain environments and knowledge of each sidechain’s bridge architecture to maintain evidence continuity from entry through exit.
How do investigators trace funds on Liquid Network?
Investigators trace Liquid Network funds by monitoring federation wallet addresses on the Bitcoin main chain, where peg-in and peg-out transactions retain full transparency. While Liquid’s internal transactions conceal amounts through Confidential Transactions, entry and exit events on Bitcoin provide value anchors. Investigators cross-reference timing, amounts, and Bitcoin addresses against exchange KYC records. According to Chainalysis (2024), 68% of Liquid peg-ins are attributable through pre-deposit UTXO analysis when at least one input originates from a known exchange withdrawal address.
What makes Liquid Network challenging for forensic investigators?
Liquid Network’s Confidential Transactions protocol conceals transaction amounts and asset types within the sidechain using Pedersen commitments, preventing investigators from reading internal flow values from blockchain data. Additionally, Liquid uses different address formats than Bitcoin, requiring sidechain-specific tooling. The 11-of-15 federation structure means no single party controls internal transaction data without member coordination, limiting cooperation options. Despite these obstacles, peg-in and peg-out events on the Bitcoin main chain remain fully transparent and provide reliable bookend evidence.
How does RSK differ from Liquid Network for forensic purposes?
RSK differs from Liquid Network in three key ways relevant to investigators: RSK operates a full Ethereum Virtual Machine environment, meaning smart contract interactions generate readable event logs; RSK’s Powpeg uses Hardware Security Modules rather than a standard multi-signature federation; and RSK hosts an active DeFi environment creating additional transaction complexity. Liquid is primarily an exchange settlement network with simpler patterns, while RSK investigations require smart contract event analysis using Ethereum-compatible forensic techniques applied alongside standard on-chain tracing.
What are peg-in and peg-out transactions?
Peg-in transactions are Bitcoin main-chain transfers to a sidechain federation wallet address, locking funds on Bitcoin while releasing an equivalent token on the sidechain. Peg-out transactions reverse this: the sidechain token is burned and the original Bitcoin value is released to the designated destination address. Both events appear on the Bitcoin blockchain with full transaction detail, providing timestamped, amount-transparent evidence. The period between peg-in and peg-out represents the sidechain activity window requiring chain-specific investigation tools.
Can standard forensics tools trace sidechain activity?
Standard Bitcoin-focused forensics tools provide partial coverage by monitoring federation addresses on the main chain. Full sidechain tracing requires platforms with specific Liquid Network or RSK integration – Chainalysis Reactor for Liquid peg tracking or Elliptic Investigator for RSK smart contract analysis. Investigators without enterprise tool access can use public block explorers for Liquid federation activity and RSK smart contract events. Manual methods remain viable for targeted investigations but require deeper sidechain-specific technical knowledge than automated platform approaches.
How do criminals use sidechains to obscure fund flows?
Criminals use sidechains as intermediate layering steps, depositing Bitcoin into Liquid or RSK, executing multiple internal transactions that break direct on-chain tracing links, then withdrawing to a new Bitcoin address with no connection to the original deposit. Liquid’s confidential transaction feature and RSK’s smart contract complexity raise the technical barrier for investigators. According to Elliptic (2024), illicit sidechain fund layering increased 340% between 2022 and 2024, reflecting criminal awareness of the gap between main-chain monitoring and sidechain visibility.
What sidechain evidence is admissible in UK courts?
Admissible sidechain evidence in UK court proceedings includes the peg-in transaction hash and block height on Bitcoin, the receiving federation wallet address, the Liquid or RSK receiving address, any identifiable internal sidechain transactions, and the peg-out transaction hash with destination address. Investigators must document the continuous custody chain across both chains and establish the cryptographic equivalence of peg-in and peg-out values. Expert witness certification strengthens admissibility, particularly when the evidence type is novel and judges lack prior blockchain exposure.
How does Crypto Trace Labs approach sidechain investigations?
Crypto Trace Labs begins sidechain investigations by establishing main-chain anchors: identifying the Bitcoin peg-in transaction and tracing its funding UTXO history before the bridge deposit. Investigators then map sidechain activity using Chainalysis Reactor and Elliptic Investigator, following the peg-out to its Bitcoin destination. When the peg-out address shows exchange activity, the team uses executive-level relationships at Blockchain.com, Kraken, and Coinbase to expedite KYC data requests. The firm offers no upfront charge for non-custodial wallet recovery cases.
What Travel Rule obligations apply to sidechain transactions?
The Travel Rule requires Virtual Asset Service Providers to transmit originator and beneficiary information for transfers above reporting thresholds. Sidechain peg-in and peg-out transactions transiting regulated exchange infrastructure trigger these obligations when exceeding $1,000 USD equivalent in UK, US, and EU jurisdictions. Compliance teams at exchanges operating Liquid or RSK nodes must monitor federation address activity. According to FATF (2024), sidechain Travel Rule compliance remains inconsistent globally, requiring jurisdiction-specific analysis and policy updates from qualified MLRO advisors.
Executive Summary
Sidechain transaction analysis covers forensic investigation of Bitcoin funds moving through Liquid Network and RSK. The core methodology uses peg-in and peg-out events on the Bitcoin main chain – where full transparency is preserved – to bookend activity within the sidechain. Liquid’s Confidential Transactions and RSK’s smart contract complexity require dedicated tooling, with Chainalysis Reactor and Elliptic Investigator providing broadest coverage. Legal admissibility requires documented custody chains across both chains. According to Elliptic (2024), sidechain-assisted fund obscuration grew 340% between 2022 and 2024.
What Should You Do Next?
If your investigation has reached a sidechain bridge, the forensic trail requires specialists with sidechain-specific tooling and exchange-level relationships.
The team at Crypto Trace Labs holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase, providing direct exchange contacts that accelerate KYC data requests in time-sensitive cases. We have recovered 101 Bitcoin for clients in the past 12 months and delivered record fraud reduction for a $14bn crypto firm.
We offer no upfront charge for non-custodial wallet recoveries – you pay only after successful fund recovery. Contact Crypto Trace Labs to discuss your case in confidence.
People Also Read
- Cross-Chain Forensics: Tracking Assets Through Blockchain Bridges
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- DeFi On-Chain Investigation: Tracking Assets Through Smart Contracts
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm. Founding members held VP and Director positions at Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across UK, US, and EU, and Chartered Fellow Grade at the CMI. With 10+ years in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin in the past 12 months and delivered record fraud reduction for a $14bn crypto exchange. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.





