Last Updated: February 2026
Vanity addresses are cryptocurrency addresses containing deliberate, human-readable patterns – branded prefixes, personal names, or repeating character sequences – generated through brute-force computation until the desired characters appear. For blockchain forensic investigators, these addresses represent some of the strongest attribution signals on any chain, because the generation process reveals the tools used, the computational resources involved, and frequently the identity or organization behind the wallet. The Profanity tool vulnerability enabled over $160 million in thefts including the Wintermute hack, while address poisoning attacks – which use vanity generators to create lookalike addresses at industrial scale – caused $83 million in confirmed losses through early 2026.
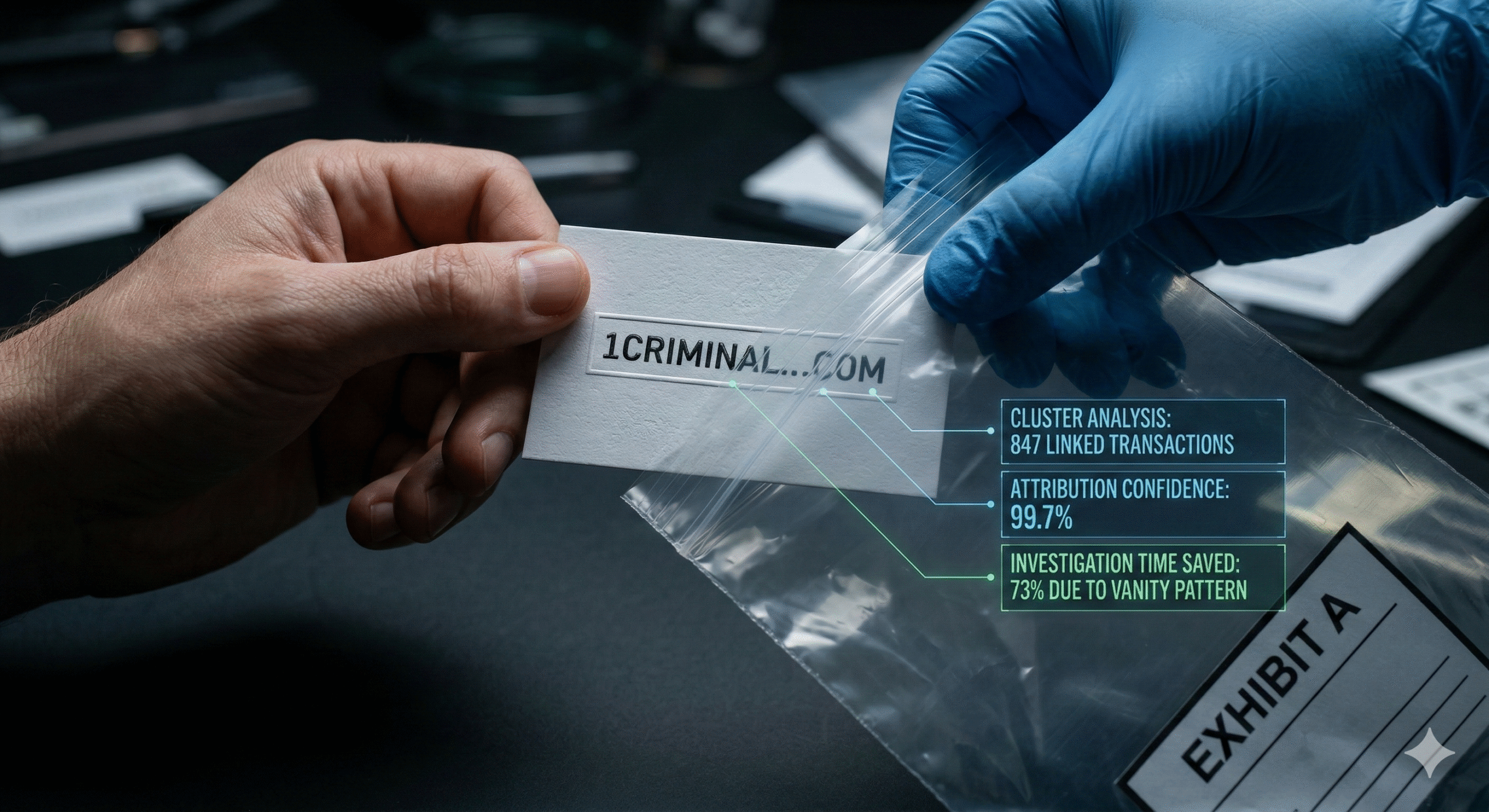
At Crypto Trace Labs, our team has analyzed vanity address patterns across hundreds of blockchain forensics investigations, including cases involving address poisoning scams and wallet attribution through on-chain fingerprints. This guide explains how vanity addresses create forensic opportunities, what real exploits reveal about their risks, and how investigators trace criminal activity through these patterns.
How Are Vanity Addresses Generated?
Standard cryptocurrency addresses are random alphanumeric strings generated from public-private key pairs. A Bitcoin address like 1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa carries no human-readable meaning. Vanity addresses change that by introducing recognizable patterns – a business might generate an address starting with 1CryptoTrace to brand their receiving wallet, or a user might want their name at the start for personal identification.
The generation process is brute-force computation. Tools like Vanitygen, Profanity, and VanitySearch generate millions of random key pairs per second until one produces an address matching the desired prefix or pattern. A four-character prefix requires roughly 4.3 million attempts on average. A seven-character prefix demands approximately 58 trillion attempts – requiring days of GPU processing even on powerful hardware.
This computational intensity is what makes vanity addresses forensically significant. Generating one is a deliberate act. The tools used, the computational resources required, and the patterns chosen all narrow the attribution field in ways that random addresses never can.
What Makes Vanity Addresses Valuable for Attribution?
Random cryptocurrency addresses tell investigators almost nothing about who created them. Vanity addresses tell investigators several things at once.
The pattern itself reveals intent. An address starting with 1Exchange or 1Donation signals organizational use. An address containing a name suggests personal ownership. Addresses with strings of zeros – like 0x000000 – often indicate gas optimization for DeFi protocols, which is exactly how Wintermute’s compromised address was later identified.
Vanity addresses also reduce the anonymity set dramatically. Instead of searching across billions of possible addresses, investigators narrow their scope to addresses with specific patterns. Address clustering techniques become more effective when one address in a cluster is a vanity address, because the deliberate pattern provides an anchor point for attribution across related wallets.
The generation tool itself becomes a forensic lead. Blockchain analytics platforms like Chainalysis and Elliptic maintain databases of known vanity address patterns and the tools that produced them. When investigators identify that an address was created using Profanity, they immediately know that address may be vulnerable to private key extraction – and that the owner was using Ethereum-specific tooling during a specific time period.
Entities that use vanity addresses also tend to reuse them across multiple transactions for branding purposes, creating longer transaction histories than disposable addresses. This extended exposure gives investigators more on-chain data to work with – transaction timing, counterparty patterns, fund flow direction, and behavioral signatures that support attribution.
What Happened With the Profanity Vulnerability?
The Profanity exploit remains the most consequential vanity address security failure in cryptocurrency history, and it demonstrates why generation methods matter to forensic investigators long after an address is created.
Profanity was a popular open-source Ethereum vanity address generator. In September 2022, DEX aggregator 1inch published a security disclosure revealing a critical flaw in how the tool generated private keys. Profanity seeded its random number generator with an unsigned 32-bit integer, meaning only 4.3 billion possible seed values existed for generating 256-bit private keys. That gap collapsed the cryptographic security model entirely.
The math was straightforward. Researchers demonstrated that a cluster of 1,000 GPUs could brute-force the private key of any seven-character Profanity-generated vanity address within approximately 50 days. Shorter prefixes fell much faster.
Days after the disclosure, attackers drained $3.3 million from Profanity-generated addresses. Then came the bigger target. Wintermute, the London-based crypto market maker, lost $160 million from its DeFi operations through a compromised admin address. That address contained a string of leading zeros – generated through Profanity not for vanity purposes, but for gas optimization. Wintermute CEO Evgeny Gaevoy confirmed the connection publicly.
For forensic teams, the Profanity case created a permanent dataset. Every address generated using the tool’s flawed entropy carries identifiable characteristics. Crypto Trace Labs and other blockchain forensics firms cross-reference addresses against known Profanity generation patterns to identify potentially compromised wallets – even years after creation. The vulnerability does not expire.
How Does Address Poisoning Exploit Vanity Generation?
Address poisoning has become one of the fastest-growing attack vectors in cryptocurrency, and it depends entirely on vanity address generation operating at industrial scale.
The attack exploits human behavior rather than cryptographic weakness. Attackers use vanity generators to create addresses matching the first five and last seven characters of a victim’s legitimate receiving address. They send a tiny transaction – often fractions of a cent – from the lookalike address to the victim’s wallet. This places the fake address in the victim’s transaction history. When the victim later copies an address from their history to send funds, they grab the attacker’s lookalike instead of the real destination.
The scale is extraordinary. Since January 2025, blockchain monitoring has flagged over 65.4 million address poisoning transactions averaging more than 160,000 per day. Of those, approximately 316,000 resulted in victims actually sending funds to poisoned addresses. Roughly 1 in every 200 attempts succeeds.
The damage from successful attacks is severe. In May 2024, a victim lost 1,155 WBTC – approximately $72 million – by copying a poisoned address from their transaction history. In December 2025, another user lost $50 million in USDT through the same mechanism. These are not edge cases. They represent a systematic, scalable attack model.
January 2026 made the problem worse. Ethereum’s Fusaka upgrade in December 2025 reduced transaction fees by roughly 6x, removing the primary economic brake on mass poisoning campaigns. Poisoning attempts surged from 628,000 in November 2025 to 3.4 million in January 2026 – a 5.5x increase in two months.
What Forensic Trails Do Vanity Address Attacks Leave?
Despite their effectiveness against individual users, vanity address attacks create substantial evidence trails that investigators can follow.
Generation infrastructure is traceable. Creating thousands of lookalike addresses requires significant computational resources. Attackers typically use cloud computing or GPU rental services that produce payment records and access logs. When investigators identify a cluster of poisoning addresses, timing analysis and resource consumption patterns can trace the generation infrastructure back to its source.
Dust transactions create permanent records. Every poisoning attempt – successful or not – is permanently recorded on the blockchain. Investigators map the full scope of an attacker’s campaign by identifying all dust transactions originating from related addresses. Transaction graph analysis reveals both the funding source for the poisoning operation and the destination of stolen funds.
Cash-out points expose identity. Stolen funds eventually reach exchanges for conversion to fiat currency. Blockchain analytics platforms including Chainalysis, Elliptic, and TRM Labs track fund flows from poisoned addresses to exchange deposit addresses where Know Your Customer records exist. The $72 million WBTC case demonstrated this clearly – despite the scale of the theft, the on-chain trail remained fully intact.
Behavioral clustering links campaigns. Attackers running large-scale operations show consistent patterns in timing, target selection, dust amounts, and fund consolidation. Crypto Trace Labs applies behavioral analysis and clustering techniques to group poisoning addresses under common control, often revealing that thousands of seemingly independent attacks trace back to a single operation.
Investigators working address poisoning recovery cases typically begin by mapping the full campaign, then tracing fund flows forward to cash-out points where exchange cooperation and regulatory mechanisms enable identity attribution.
How Do Sanctions Frameworks Target Vanity-Linked Crime?
OFAC has included cryptocurrency addresses on its Specially Designated Nationals list since 2018, making blockchain attribution a regulatory compliance requirement – not just an investigative tool. When sanctioned addresses include vanity patterns, identification becomes faster because recognizable characters make them easier to flag in transaction screening systems.
AML compliance teams at exchanges screen incoming and outgoing transactions against sanctions lists continuously. Vanity addresses on the SDN list receive heightened attention because their patterns are more likely to appear in user-facing contexts – donation pages, social media posts, and payment requests.
The regulatory angle matters for cryptocurrency fraud investigations because sanctions violations create additional legal avenues for asset freezing and recovery. When investigators determine that stolen funds touched a sanctioned vanity address, they can pursue regulatory enforcement alongside law enforcement channels – expanding the options for recovering stolen cryptocurrency.
Frequently Asked Questions
Can you brute-force a vanity address private key?
It depends entirely on the generation tool. Standard vanity generators using proper 256-bit entropy remain cryptographically secure – brute-forcing a correctly generated private key is computationally infeasible with current technology. The Profanity tool was the critical exception because it used only 32-bit entropy for seeding, collapsing the keyspace to 4.3 billion possibilities. Any address generated with Profanity or similarly flawed tools may be vulnerable. Investigators check generation methods as a standard forensic step when analyzing vanity addresses.
How do investigators determine which tool generated a vanity address?
Blockchain analytics platforms maintain databases of addresses produced by known generation tools. Each tool creates addresses with subtly different characteristics based on its algorithm and supported blockchains. Profanity-generated Ethereum addresses show specific structural patterns that distinguish them from VanitySearch-generated Bitcoin addresses. Transaction timing relative to tool release dates and known vulnerability disclosures provides additional attribution context for forensic teams.
What is the difference between address poisoning and a dusting attack?
Dusting attacks send tiny amounts of cryptocurrency to track wallet activity and potentially deanonymize owners through transaction analysis. Address poisoning sends dust specifically from lookalike vanity addresses to trick victims into copying the wrong address when making future transfers. Dusting is surveillance. Poisoning is theft. The forensic approaches differ – dusting investigations focus on identifying who is monitoring the victim, while poisoning investigations focus on tracing where stolen funds went after the victim sent them.
How long does it take to generate a lookalike address for poisoning?
Modern GPU hardware can generate an Ethereum address matching the first five and last seven characters of a target address within seconds. This speed is what makes industrial-scale poisoning possible – attackers produce unique lookalikes for millions of active addresses in automated batch operations. Longer matching sequences require exponentially more time. Matching 10 or more characters from both ends would require days or weeks of computation per target address.
Are vanity addresses legal to create and use?
Generating a vanity address for legitimate purposes – personal identification, business branding, donation transparency – is legal in all major jurisdictions. Legal issues arise from misuse. Creating lookalike addresses for poisoning attacks constitutes fraud. Using vanity generators with stolen computational resources adds additional charges. Holding or transacting with vanity addresses that match sanctioned addresses on the OFAC SDN list creates compliance exposure regardless of intent.
Do hardware wallets like Ledger and Trezor support vanity addresses?
Hardware wallets generate addresses from seed phrases using deterministic derivation paths following BIP32, BIP39, and BIP44 standards. They do not natively support vanity address generation because the derivation process does not allow users to specify desired character patterns. Users who want vanity addresses on hardware wallets must generate the key pair externally and import it – which bypasses the hardware wallet’s key generation security and introduces the same third-party tool risks that led to the Profanity exploit.
Can investigators trace address poisoning across multiple blockchains?
Yes, though complexity increases substantially. Attackers running poisoning campaigns across Ethereum, BNB Chain, and other EVM-compatible networks often reuse funding sources and infrastructure. Cross-chain investigation techniques link campaigns by analyzing shared funding addresses, coordinated timing patterns, and consistent dust amounts across chains. Over 270 million zero-value transfer attempts were identified across Ethereum and BNB Chain through mid-2025, suggesting large operations spanning multiple networks.
How can you protect yourself from address poisoning?
Always verify the complete address character by character before confirming any transaction – not just the first and last few characters. Use the address book feature in your wallet software rather than copying from transaction history. When sending large amounts, send a small test transaction first and confirm receipt with the intended recipient directly. Consider wallets with built-in poisoning detection features that flag suspicious lookalike addresses appearing in your transaction history.
Need Help With a Vanity Address Investigation?
If you have lost cryptocurrency through an address poisoning attack or a compromised vanity address, time matters. The sooner fund flows are traced, the higher the chance of recovery before assets reach irreversible cash-out points. If you are an investigator or legal team that needs vanity address attribution analysis for an active case, our forensic reporting meets court evidentiary standards.
The team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase, with ACAMS certifications, MLRO qualifications across UK, US, and Europe, and Chartered status at Fellow Grade. We have traced vanity address exploitation patterns across hundreds of investigations and provided expert witness testimony on blockchain attribution.
For non-custodial wallet recoveries, we charge no upfront fee – you only pay after successful fund recovery.
Contact Crypto Trace Labs to discuss your case with our forensic investigation team.
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, on-chain analysis, and forensic investigation. Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed vanity address exploitation patterns in hundreds of investigations and provided expert witness testimony on blockchain attribution methodologies in court proceedings.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.