Last Updated: February 2026
You are investigating an Ethereum wallet linked to a suspected fraud operation. The address has sent 14,000 transactions over six months with no activity gap longer than 45 minutes in any 24-hour period, and every transaction targets the same decentralized exchange router contract. You do not need to trace a single fund flow to know what you are looking at – the nonce pattern alone tells you this is an automated bot, not a human operator. That behavioral classification, derived entirely from how the nonce counter incremented over time, narrows the investigation before traditional transaction graph analysis even begins.
Ethereum’s account-based nonce – a sequential counter starting at zero that increments with every confirmed transaction – creates a forensic record that Bitcoin’s UTXO model does not produce. The nonce provides a complete, ordered timeline of every transaction an address has ever sent. Its velocity distinguishes bots from humans. Its gaps reveal dropped or replaced transactions. And a separate but critically important concept – the ECDSA cryptographic nonce used in transaction signatures – has led to documented private key extractions when implemented incorrectly.
At Crypto Trace Labs, our forensic team analyzes Ethereum nonce patterns as part of every investigation involving EVM-compatible chains. This guide explains what nonces reveal, how investigators extract behavioral intelligence from them, and where the signals reach their limits.
How Do Ethereum Nonces Create a Forensic Record?
Every Externally Owned Account on Ethereum maintains a nonce that starts at zero and increments by one with each confirmed transaction. Unlike Bitcoin, where transaction ordering requires reconstructing UTXO spending chains, Ethereum’s nonce provides an explicit chronological index. Nonce 0 is the account’s first transaction. Nonce 500 means the account has sent exactly 501 transactions. The sequence is gapless on-chain – every integer between zero and the current nonce corresponds to exactly one confirmed transaction.
This sequential property makes timeline reconstruction straightforward. An investigator querying an Ethereum address on Etherscan can sort all outgoing transactions by nonce and see, in exact order, every action the account has ever taken. Combined with block timestamps, each nonce creates a time-stamped event in the wallet’s operational history. For fraud investigations, this ordered record establishes when specific transfers occurred relative to other events – victim reports, exchange freezes, or market movements.
The nonce also enforces transaction ordering in the mempool. If an account’s confirmed nonce is 100, only the transaction with nonce 100 can be processed next. Transactions with nonce 101 or higher sit queued until their predecessors confirm. Investigators monitoring the mempool can observe pending transaction queues and infer operational intent – a wallet queuing dozens of sequential transactions is preparing a batch operation, not making ad hoc transfers.
What Do Nonce Velocity Patterns Reveal About Wallet Operators?
The rate at which a wallet’s nonce increments over time – its nonce velocity – is one of the most reliable signals for classifying whether an address is operated by a human or an automated system. Research published at the ACM Web Conference in 2024 by Niedermayer established a taxonomy of seven categories of financial bots on Ethereum, finding that time-based features including transaction frequency and inter-activity gaps were among the most informative detection signals. Classification models achieved 83% accuracy distinguishing bot wallets from human-operated ones.
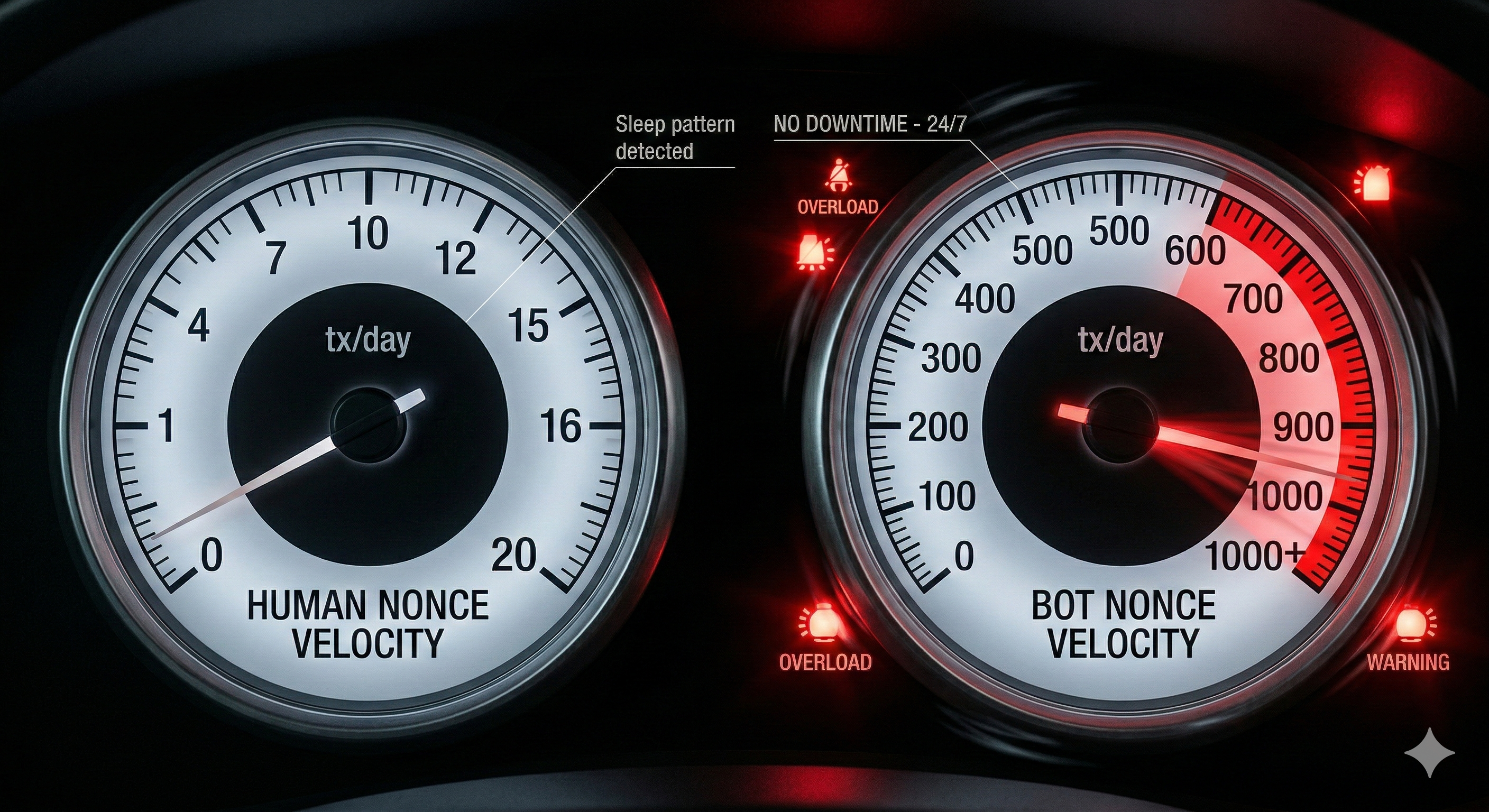
Human wallets typically produce 1 to 10 transactions per day with irregular timing that reflects work schedules, sleep cycles, and manual decision-making. Active traders may reach 10 to 50 daily transactions. Bot wallets operate at entirely different scales – hundreds or thousands of transactions per day with machine-regular intervals and no sleep period.
The MEV bot known as jaredfromsubway.eth illustrates the extreme end. In its first three months of operation in 2023, the bot generated $34 million in profit from sandwich attacks, consumed 7% of all Ethereum gas fees in a single 24-hour period, and executed over 238,000 attacks against more than 106,000 victims. The nonce velocity alone – thousands of transactions daily with sub-minute intervals – immediately identifies this as automated infrastructure. In Crypto Trace Labs investigations, nonce velocity is the first filter applied when classifying unknown Ethereum addresses. A nonce incrementing faster than once per minute, sustained over hours, eliminates human operation from consideration before a single transaction destination is examined.
This classification matters because it determines the investigative approach. Bot wallets require analysis of their contract interactions and deployment patterns. Human wallets benefit from address clustering and behavioral profiling – timezone inference from activity hours, transaction patterns that suggest the operator’s sophistication level, and spending behaviors that correlate with known entity types.
How Do Nonce Gaps Expose Operational Failures?
While the on-chain nonce sequence is always gapless, the path to confirmation is not always smooth. When a transaction is broadcast with nonce N but fails to confirm – due to insufficient gas, network congestion, or deliberate cancellation via replacement – every subsequent transaction from that account is blocked until nonce N is resolved. These gaps, observable in the mempool and in transaction replacement patterns, produce their own forensic signals.
A wallet that frequently replaces pending transactions with same-nonce, higher-gas alternatives indicates an operator actively managing transaction throughput – typical of automated trading systems and institutional operations. A wallet where nonce gaps cause long delays suggests simpler software that does not handle congestion well. During the March 2020 Black Thursday crash, Blocknative’s mempool forensics proved that attackers deployed “Hammerbots” to flood the Ethereum mempool with strategically priced transactions. Legitimate liquidation bots could not process their queued transactions because nonce gaps and congestion left their bids stuck. The result: 1,462 of 3,994 liquidation auctions were won with bids of zero ETH, and attackers claimed $8.32 million in MakerDAO collateral for effectively nothing.
Nonce gap patterns also reveal intentional transaction cancellation. When a wallet repeatedly sends zero-value transactions to its own address at a previously used nonce with higher gas, it is deliberately canceling pending operations. The frequency and timing of these cancellations indicate how the operator responds to changing conditions – whether they cancel quickly when market conditions shift or let failed transactions expire on their own.
How Does Ethereum’s Account Model Change the Investigative Playbook?
Investigators working across both Bitcoin and Ethereum encounter fundamentally different forensic surfaces. The table below summarizes the key differences that affect how nonce-based and structural analysis applies to each chain.
| Forensic Dimension | Bitcoin (UTXO Model) | Ethereum (Account Model) |
| Transaction ordering | No account-level sequence – requires UTXO graph reconstruction | Sequential nonce provides explicit chronological order per address |
| Primary clustering heuristic | Common-input-ownership – multiple inputs imply same controller | Deposit address patterns, airdrop participation, token approval behavior |
| Change output analysis | Core technique – 6+ heuristics identify which output returns to sender | Not applicable – no change outputs in account-based transfers |
| Balance visibility | Requires summing all unspent UTXOs across addresses | Current balance directly queryable per address |
| Bot detection | Limited – UTXO chains lack per-account transaction counters | Nonce velocity directly profiles automated vs. human operation |
| Smart contract complexity | Minimal scripting – transactions are primarily value transfers | Internal transactions, token events, and contract calls create multi-layered graphs |
| Privacy baseline | Higher – each UTXO can use a different address | Lower – full transaction history visible per account |
Research on Ethereum address clustering found that 17.9% of all active EOA addresses could be grouped into multi-address entities, identifying over 340,000 distinct entities controlling multiple wallets. The deposit address heuristic – linking exchange deposit addresses to the parent exchange entity – proved the most effective method, differing from Bitcoin where UTXO-based co-spending analysis dominates. Crypto Trace Labs applies chain-specific heuristics when tracking funds across multiple blockchains, because a technique that works on Bitcoin may have no equivalent on Ethereum and vice versa.
Why Is the ECDSA Nonce a Critical Security Vulnerability?
The term “nonce” appears twice in Ethereum with entirely different meanings. The transaction nonce is the sequential account counter discussed above – visible on-chain and non-sensitive. The ECDSA nonce is the random value (conventionally called k) used internally during transaction signature generation. It is never published on-chain – only the resulting signature components (r, s, v) appear in the transaction data.
If an attacker can determine k for any single signature, they can algebraically compute the private key. If the same k is used for two different signatures – nonce reuse – both signatures share the same r value, and the private key can be extracted using basic algebra. A Trail of Bits analysis documented the mathematics and cataloged the implementation pitfalls that lead to weak ECDSA nonce generation in practice.
The vulnerability is not theoretical. A scan of the Bitcoin blockchain up to January 2018 found 1,068 distinct r values that appeared at least twice across 4,433 keys, enabling the recovery of 416 private keys holding a combined 26.85 BTC. Researchers at Kudelski Security demonstrated at DEF CON 31 in 2023 that even polynomial relationships between successive nonces – the kind produced by weak pseudorandom number generators – allow private key extraction from as few as four signatures. They confirmed successful attacks against keys found on both Bitcoin and Ethereum in the wild.
Automated “blockchain vultures” now continuously scan both networks for repeated r values and immediately drain any funds from compromised addresses. The ECDSA nonce vulnerability is largely historical for modern wallets using RFC 6979 deterministic nonce generation, but Crypto Trace Labs still encounters it in investigations involving older wallet software, custom implementations, and hardware wallet firmware that predates current standards. Modern wallets eliminated this risk by deriving the k value deterministically from the private key and message hash, ensuring it is unique per signature without requiring a random number generator.
How Do Contract Deployment Nonces Aid Attribution?
When an Ethereum account deploys a smart contract using the CREATE opcode, the new contract’s address is derived from just two values: the deployer’s address and the deployer’s current nonce. This means deployment order is encoded in the addresses themselves. If an investigator knows the deployer, they can compute the expected address for each sequential deployment and verify which contracts that entity created – useful when attributing contract infrastructure to specific actors in criminal network mapping.
The CREATE2 opcode, introduced in 2019, removes the nonce from the address derivation formula entirely – replacing it with a user-chosen salt value and the hash of the initialization code. This enables deterministic cross-chain deployment but also enables metamorphic contracts: a contract can be deployed at an address, self-destructed, and redeployed at the same address with entirely different code. Check Point Research documented CREATE2 as a security risk, noting that attackers deploy malicious contracts at addresses that previously hosted benign code, bypassing allowlists and security screening. Crypto Trace Labs flags any contract that has undergone self-destruct and redeployment cycles as a potential metamorphic contract requiring deeper forensic review.
Nonce-Based Wallet Investigation Workflow
The Crypto Trace Labs forensic team applies the following structured workflow when analyzing Ethereum wallets through nonce patterns. Each stage builds on the previous one.
Stage 1: Baseline classification. Query the wallet’s current nonce and transaction history. A nonce under 100 with irregular timing suggests a personal wallet. A nonce in the thousands with regular intervals indicates automated infrastructure. A nonce of zero with only incoming transactions identifies a receive-only address – potentially an exchange deposit address or a dead drop in a laundering chain.
Stage 2: Velocity profiling. Calculate the average, median, and peak transaction rates across different time windows. Compare against known baselines: 1-10 daily for human wallets, 100+ daily for bots. Look for 24/7 operation versus timezone-correlated activity windows. Flag any sustained period where the nonce increments faster than once per minute.
Stage 3: Gap and replacement analysis. Identify nonce positions where transaction replacement occurred (same nonce, different transaction hash). Classify replacements as fee bumps (same destination, higher gas), cancellations (zero-value self-send), or destination changes (potential fraud signal). Map replacement frequency against network congestion data to distinguish routine gas management from panic behavior.
Stage 4: Contract interaction mapping. For each nonce, identify the destination contract and function called. Cluster transactions by interaction type – DEX swaps, token approvals, contract deployments, bridge transactions. This reveals the wallet’s operational purpose: trading bot, yield farming automation, NFT minting operation, or general-purpose wallet.
Stage 5: Cross-reference and attribution. Compare nonce-derived behavioral profiles against known entity databases and labeled address sets. Cross-reference with blockchain forensic platforms that maintain attribution data. Verify findings against on-chain evidence – deployment nonces, funding source patterns, and wallet software fingerprints derived from gas limit choices and transaction formatting.
Frequently Asked Questions
What is the difference between a transaction nonce and a mining nonce?
An Ethereum transaction nonce is a sequential counter per account that ensures transaction ordering and prevents replay attacks, incrementing by one with each confirmed transaction starting at zero. A mining nonce (used in Bitcoin’s proof-of-work) is a value that miners vary to find a block hash meeting the difficulty target. They serve entirely different purposes – transaction nonces enforce account-level ordering, while mining nonces enable block production.
Can nonce analysis identify which wallet software someone is using?
Nonce analysis alone cannot identify wallet software, but it contributes to a broader fingerprinting approach. Different wallets set gas limits, gas prices, and transaction parameters in characteristic ways. When combined with nonce velocity patterns and contract interaction methods, these signals help classify the wallet type. On Bitcoin, nLockTime and nSequence values provide stronger wallet fingerprinting signals, but Ethereum’s transaction formatting offers its own identifying features.
How do investigators detect MEV bots using nonce patterns?
MEV bots show distinctive nonce characteristics: extremely high total nonce values (tens or hundreds of thousands), uniform inter-transaction timing with no sleep gaps, burst patterns where multiple sequential nonces appear within the same block (sandwich attacks require two transactions in one block), and 24/7 continuous operation. These patterns are immediately distinguishable from human wallet behavior through velocity analysis.
What happens to forensic evidence when transactions are replaced?
When a pending transaction is replaced via a same-nonce submission with higher gas, the original transaction is discarded from the mempool. Only investigators with mempool monitoring infrastructure capture both versions. The confirmed blockchain shows only the replacement. This is why Crypto Trace Labs maintains continuous mempool capture – the original transaction may reveal different destination addresses, amounts, or gas parameters that are forensically significant.
Can ECDSA nonce vulnerabilities still compromise modern wallets?
Modern wallets implementing RFC 6979 deterministic nonce generation are not vulnerable to nonce reuse attacks. The risk persists in older wallet implementations, custom cryptographic code, and hardware wallet firmware predating current standards. Automated scanners continuously monitor both Bitcoin and Ethereum for signatures with repeated r values and immediately drain any exposed funds.
Does Ethereum’s account model make investigations easier or harder than Bitcoin?
It depends on the task. Ethereum’s sequential nonces make timeline reconstruction trivial, and the account model provides direct balance visibility. However, Ethereum lacks Bitcoin’s powerful co-spend clustering heuristic, and smart contract interactions create multi-layered transaction graphs that are more complex to trace. Investigators working cross-chain cases must apply chain-specific techniques to each network independently.
Is Your Ethereum Security Model Accounting for Nonce-Based Risks?
Ethereum’s nonce mechanics create both forensic opportunities and security exposure. If your exchange or DeFi platform relies on nonce management for transaction processing, a nonce gap during network congestion can stall operations entirely – the same vulnerability that cost MakerDAO participants $8.32 million on Black Thursday. If your smart contract infrastructure uses CREATE2 for deployment, metamorphic contract risks may expose your users to code substitution attacks that bypass security reviews.
Crypto Trace Labs conducts Ethereum security assessments that include nonce management auditing, MEV exposure analysis, and smart contract deployment pattern review. Our forensic team – including analysts like D. Hargreaves – holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. Our founders held VP and Director positions at Blockchain.com, Kraken, and Coinbase.
Contact Crypto Trace Labs for an Ethereum security assessment or to discuss an active investigation involving EVM-based transaction analysis.
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, on-chain analysis, and forensic investigation. Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed vanity address exploitation patterns in hundreds of investigations and provided expert witness testimony on blockchain attribution methodologies in court proceedings.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.