Last Updated: February 2026
Investigators track cryptocurrency through smart contracts by analyzing transaction logs, decoding function calls, monitoring token transfers, and mapping wallet interactions with deployed contract addresses. Professional forensic teams trace DeFi protocol flows, identify exploit patterns, and reconstruct transaction sequences through Ethereum event logs and internal transactions. According to Chainalysis 2025 research, smart contract-based fraud accounts for $4.3 billion in cryptocurrency losses annually, requiring specialized tracing techniques beyond traditional UTXO analysis.
At Crypto Trace Labs, our team – featuring VP and Director-level executives from Blockchain.com, Kraken, and Coinbase – has traced billions in cryptocurrency through complex smart contract interactions during blockchain forensic investigations. This guide draws on that decade of DeFi forensics and Ethereum investigation experience.
Key Takeaways:
- Event logs provide complete transaction histories – Ethereum smart contracts emit events recording every token transfer, enabling investigators to reconstruct fund flows even when direct transaction analysis proves insufficient
- Internal transactions reveal hidden fund movements – Smart contract-to-contract interactions create internal transactions invisible in standard block explorers but critical for tracking DeFi protocol flows
- Function call analysis identifies exploit patterns – Decoding smart contract function inputs and outputs reveals attack vectors, reentrancy exploits, and flash loan manipulation schemes
- Token approval tracking exposes wallet drain attacks – Monitoring ERC-20 token approvals identifies malicious contracts with unlimited spending permissions enabling systematic theft
- Cross-contract tracing requires specialized tools – Following assets through multiple DeFi protocols, bridges, and wrapped tokens demands automated platforms combining transaction graphs with contract-specific logic
What Technical Characteristics Define Smart Contract Tracing?
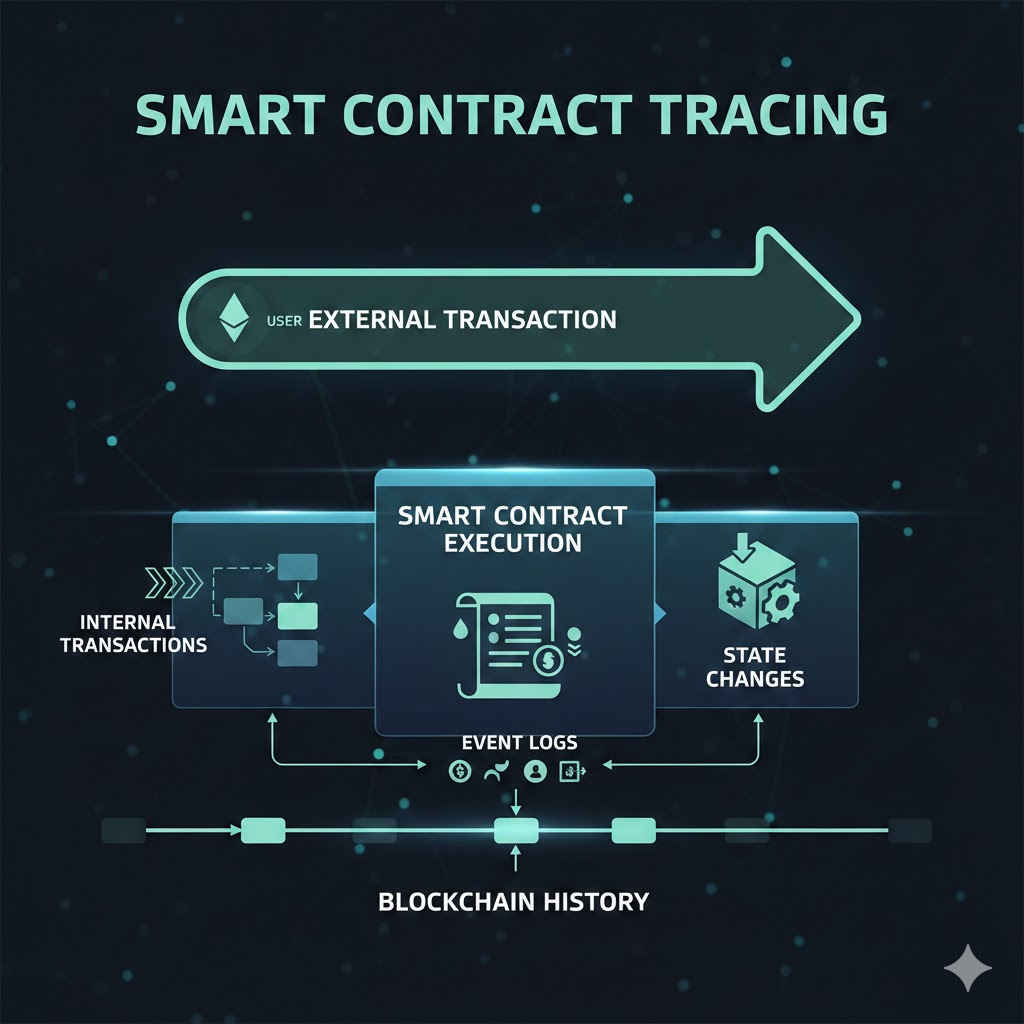
Smart contract tracing differs fundamentally from Bitcoin UTXO analysis because Ethereum uses an account-based model where contracts execute code modifying blockchain state. Investigators analyze transaction receipts containing event logs, internal transactions, and state changes rather than focusing solely on input/output value flows.
Event log analysis provides the foundation for smart contract forensics. Every significant contract action emits events including Transfer events for ERC-20 tokens, Approval events for spending permissions, and custom events specific to protocol logic. Professional investigators decode these logs reconstructing complete transaction histories showing which addresses received tokens, what amounts transferred, and when movements occurred.
Internal transaction tracking reveals fund movements between contracts invisible in standard transaction analysis. When smart contracts call other contracts, those interactions create internal transactions recorded separately. The 2021 Poly Network hack required tracing internal transactions through six DeFi protocols before identifying final destination addresses.
How Do Investigators Decode Smart Contract Event Logs?
Event logs contain structured data recording contract state changes during transaction execution. Each event includes indexed parameters allowing efficient filtering and non-indexed parameters providing detailed context. Professional forensic analysts parse these logs extracting transaction sequences and wallet interaction patterns.
Transfer event analysis forms the core of token tracking through smart contracts. ERC-20 and ERC-721 tokens emit Transfer events recording sender addresses, recipient addresses, and transfer amounts. Investigators filter blockchain data for Transfer events building complete token flow histories similar to cryptocurrency tracking methods.
Custom event decoding requires understanding protocol-specific logic:
- Swap Events – Decentralized exchanges emit Swap events recording token pair exchanges, amounts swapped, and liquidity pool interactions enabling tracking through DEX protocols
- Deposit Events – DeFi lending protocols record Deposit events showing collateral positions, borrowed amounts, and interest accrual for investigations involving leveraged positions
- Withdrawal Events – Protocol withdrawals emit events documenting redemption amounts, fees paid, and destination addresses critical for exit point identification
- Liquidation Events – Forced liquidations generate events revealing collateral seizures, liquidation penalties, and beneficiary addresses in DeFi protocol investigations
- Bridge Events – Cross-chain bridges emit events tracking asset locks on source chains and mints on destination chains essential for multi-chain investigations
Event timestamp correlation links related contract interactions. When multiple events occur within same transaction or block, that temporal relationship reveals coordinated operations. The 2023 Euler Finance exploit investigation correlated flash loan events with liquidation events occurring microseconds apart proving the attack methodology.
What Role Do Internal Transactions Play in Fund Tracking?
Internal transactions represent contract-to-contract interactions occurring during transaction execution. These movements don’t appear as separate blockchain transactions but create value transfers between addresses that investigators must track for complete fund flow analysis.
Standard block explorers often miss internal transactions requiring specialized tools like Etherscan or Chainalysis for comprehensive visibility. When smart contracts forward funds to other contracts, internal transactions document those movements. Professional investigations analyzing only external transactions miss critical fund flow paths.
Recursive call patterns indicate sophisticated protocol interactions or potential exploits. Reentrancy attacks exploit recursive calls executing malicious code before state updates complete, as demonstrated in the 2016 DAO hack where attackers drained $60 million.
Smart Contract Tracing vs Traditional Bitcoin Analysis
| Analysis Method | Bitcoin (UTXO) | Smart Contracts (Ethereum) | Key Differences |
| Transaction Model | UTXO inputs/outputs | Account state changes | Smart contracts modify state vs consuming/creating outputs |
| Fund Flow Tracking | Trace UTXO chains | Parse event logs + internal txs | Requires decoding contract logic vs following outputs |
| Hidden Movements | Change addresses | Internal transactions | Contract-to-contract calls invisible in external txs |
| Tool Requirements | UTXO clustering algorithms | Event log parsers + ABI decoders | Protocol-specific knowledge essential |
| Complexity Level | Medium (address clustering) | High (contract logic understanding) | Smart contract forensics requires programming knowledge |
Multi-hop tracing through DeFi protocols requires following internal transactions across multiple contracts. When users interact with aggregators like 1inch or Paraswap, single transactions trigger dozens of internal transactions routing through optimal liquidity sources. The 2024 investigation of laundered Axie Infinity hack proceeds traced funds through 47 internal transactions across eight DeFi protocols before identifying cash-out addresses at centralized exchanges.
How Do Function Call Analysis Methods Identify Exploits?
Smart contract function calls contain input data specifying which contract functions execute and what parameters are passed. Investigators decode this data identifying normal protocol usage versus exploit attempts. Function signature analysis reveals whether transactions called legitimate swap functions or triggered malicious vulnerability-exploiting operations.
ABI (Application Binary Interface) decoding translates raw transaction input data into human-readable function calls. Professional forensic teams maintain ABI databases for major DeFi protocols enabling automated decoding. The 2023 BNB Chain bridge exploit analysis decoded validator signatures proving attackers forged authorization messages.
Reentrancy exploit detection examines recursive function call patterns. When transactions show external calls occurring before state updates and those calls recursively invoke original functions, that indicates potential reentrancy exploitation.
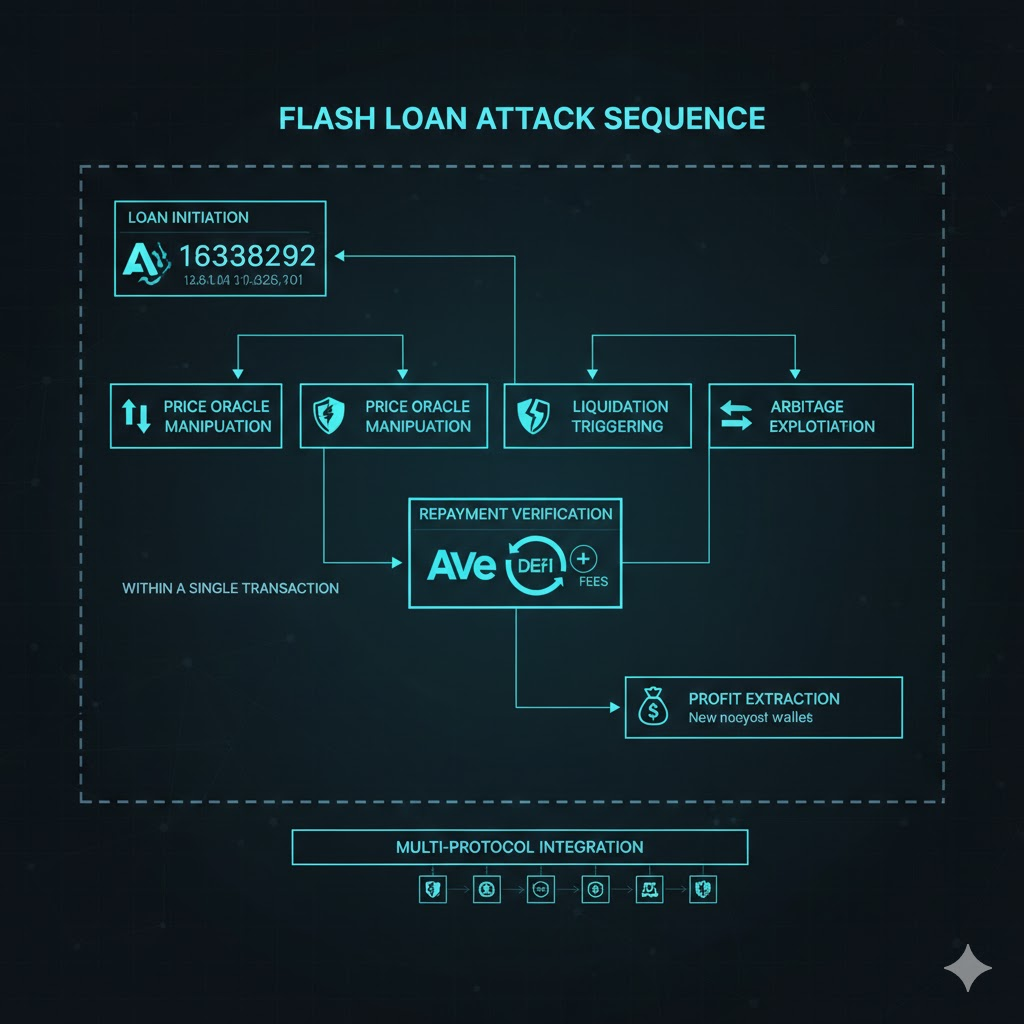
Flash loan attack identification requires correlating large borrowing operations with exploit executions and repayments within single transactions:
- Loan Initiation Detection – Identifying function calls to flash loan providers (Aave, Uniswap V2, Balancer) requesting large token amounts for single-transaction usage
- Manipulation Operation Analysis – Decoding intermediate function calls showing price oracle manipulation, liquidation triggering, or arbitrage exploitation during loan active period
- Repayment Verification – Confirming loan repayment with fees within same transaction proving flash loan methodology versus traditional funded attacks
- Profit Extraction Tracking – Following excess tokens beyond loan repayment identifying attacker profit destinations for asset recovery efforts
- Multi-Protocol Integration – Mapping interactions across multiple DeFi protocols within single atomic transaction revealing sophisticated attack choreography
Parameter analysis identifies malicious inputs. When function parameters include unusual addresses, extreme values, or unexpected token combinations, those anomalies flag potential exploits. The 2022 Nomad Bridge hack investigation identified malicious root hash parameters allowing unauthorized withdrawals proving the vulnerability exploitation method.
How Do Token Approvals Create Investigation Opportunities?
ERC-20 token approvals grant smart contracts spending permissions on behalf of token holders. Investigators monitor approval transactions identifying wallets that granted unlimited allowances to malicious contracts. These approvals often precede wallet drainer attacks where victims unknowingly authorize malicious contracts.
Approval event analysis reveals wallet drain attack patterns. When addresses approve unknown contracts for maximum token amounts (2^256-1), that indicates potential phishing victims. Professional investigations scan for approval events followed by Transfer events from different addresses.
Revocation timing analysis identifies victim awareness. When users revoke malicious contract approvals, that demonstrates threat discovery. The time delay between approval and revocation indicates detection speed.
Multi-token approval patterns fingerprint specific phishing campaigns. When dozens of addresses approve identical contracts for multiple tokens simultaneously, that reveals coordinated phishing operations. The 2023 Permit2 phishing campaign identified 147 victims through correlated approval patterns.
What Specialized Tools Handle Smart Contract Forensics?
Professional blockchain forensics platforms provide smart contract-specific analysis capabilities beyond basic block explorers. These tools combine transaction graph visualization with contract logic understanding enabling comprehensive DeFi investigation workflows.
Enterprise platforms including Chainalysis Reactor and Elliptic Investigator implement smart contract tracing modules. These systems automatically decode protocol interactions, visualize DeFi fund flows, and identify suspicious deployment patterns.
Smart Contract Forensics Platform Comparison
| Platform | Event Log Analysis | Internal Transaction Support | DeFi Protocol Coverage | ABI Database Size | Best Use Case |
| Chainalysis Reactor | Automated parsing | Full support | 200+ protocols | 10,000+ contracts | Law enforcement investigations with court evidence requirements |
| Elliptic Investigator | Custom filters | Full support | 150+ protocols | 8,000+ contracts | Exchange compliance and risk assessment workflows |
| TRM Labs | Real-time alerts | Full support | 180+ protocols | 7,500+ contracts | Transaction monitoring and sanctions screening |
| Etherscan API | Manual parsing | Available | N/A (raw data) | Community-sourced | Custom investigation tooling and research analysis |
| Dune Analytics | SQL queries | Limited support | User-defined | N/A (on-demand) | Statistical analysis and pattern identification research |
Open-source tools supplement commercial platforms for specialized analysis. Investigators use Etherscan APIs for raw event log data, Foundry for contract interaction simulation, and custom Python scripts for pattern analysis. The combination of commercial and open-source tools provides comprehensive investigation capabilities.
Transaction simulation identifies contract behavior before execution. Tools like Tenderly and Blocknative allow investigators to replay historical transactions understanding exact contract state changes and internal call sequences. This capability proves essential analyzing sophisticated exploits where multiple protocols interact in non-obvious ways.
How Do Cross-Chain Investigations Track Bridge Movements?
Cross-chain bridge tracking represents the most complex smart contract investigation scenario. Assets moving between blockchains through bridges create discontinuous transaction trails requiring correlation across multiple chains using bridge-specific event analysis.
Bridge lock event identification on source chains reveals when assets enter bridge contracts. Investigators monitor bridge addresses for deposit events recording locked amounts, destination chains, and recipient addresses. These events provide starting points for cross-chain analysis similar to multi-chain tracking methods.
Mint event correlation on destination chains completes bridge tracing. Bridge contracts emit mint events creating wrapped tokens equivalent to locked source assets. Professional investigators correlate lock and mint events through timing analysis and amount matching. The 2022 Wormhole Bridge hack required correlating Ethereum lock events with Solana mint events proving $320 million theft path.
Bridge oracle analysis reveals validator signatures authorizing transfers. Multi-signature bridges require multiple validators approving transfers. Investigators decode signatures identifying which validators authorized transfers and whether signatures were legitimate or forged.
Frequently Asked Questions
How accurate is smart contract tracing compared to Bitcoin tracing?
Smart contract tracing achieves comparable accuracy to Bitcoin UTXO analysis when investigators use proper tools and understand protocol logic. Event logs provide complete on-chain histories enabling precise fund flow reconstruction. However, smart contract complexity increases analysis difficulty requiring specialized technical knowledge. Professional teams achieve 90%+ accuracy tracing DeFi protocol movements using enterprise platforms.
Can privacy protocols on Ethereum obscure smart contract tracking?
Privacy protocols like Tornado Cash complicate but don’t eliminate traceability. Investigators analyze deposit and withdrawal timing patterns, amounts, and gas correlations identifying matches. Advanced statistical analysis achieves partial deanonymization. The 2023 Tornado Cash sanctions demonstrated law enforcement tracking capabilities.
What smart contract forensics tools do investigators use?
Professional teams use Chainalysis Reactor, Elliptic Investigator, and TRM Labs platforms for automated analysis. Investigators supplement with Etherscan, Dune Analytics, and custom Python scripts.
How do investigators track NFT theft through smart contracts?
NFT tracking analyzes ERC-721 and ERC-1155 Transfer events identifying ownership changes. Investigators monitor marketplace contracts and track movements across platforms. Stolen NFT tracking proved successful in Bored Ape investigations where victims recovered assets.
Can smart contract exploits be traced back to specific individuals?
Exploit tracing identifies attacker wallets but not individuals without additional evidence. Combining blockchain analysis with KYC data, IP logs, and traditional investigation achieves individual attribution. The 2022 Ronin Bridge hackers were identified as Lazarus Group.
How long does professional smart contract investigation take?
Simple token theft takes hours using automated platforms. Complex multi-chain investigations require days or weeks. Real-time monitoring provides immediate alerts when flagged addresses interact with contracts.
Do all DeFi protocols emit trackable events?
Reputable protocols emit comprehensive events documenting operations per ERC-20 standards. Poorly-designed or malicious contracts may omit events. Investigators analyze source code identifying whether protocols implement proper emissions.
How do investigators handle upgradeable smart contracts?
Upgradeable contracts use proxy patterns separating logic from storage. Investigators analyze proxy implementation addresses tracking which versions executed at specific times. Historical analysis reveals whether upgrades introduced vulnerabilities.
Can flash loan attacks be prevented through investigation?
Flash loan attacks execute instantaneously making real-time prevention impossible. However, post-attack investigation identifies vulnerabilities enabling similar attacks. Professional security firms use findings improving protocol designs.
What future challenges will affect smart contract forensics?
Layer 2 scaling solutions create new complexity requiring L2-specific tools. Zero-knowledge proof systems may obscure transaction details. However, economic incentives for transparency ensure most DeFi protocols remain traceable.
How does smart contract investigation integrate with enforcement?
Investigations provide evidence for law enforcement actions and exchange freezing. Documented contract interactions prove theft and identify destinations. The 2024 Euler Finance recovery relied on forensics proving attacker addresses.
What technical knowledge do smart contract investigators need?
Investigators require Solidity programming knowledge, EVM operations understanding, and DeFi protocol familiarity. Most have software engineering backgrounds with blockchain specialization.
Conclusion
Smart contract tracing requires specialized tools and technical expertise beyond traditional cryptocurrency investigation. Professional investigators achieve comprehensive fund flow analysis through event log parsing, internal transaction tracking, and function call decoding revealing complete DeFi interaction histories.
This guide was prepared by Crypto Trace Labs drawing on 10+ years Ethereum forensics and DeFi investigation experience. Our founders held VP and Director positions at major cryptocurrency platforms where they investigated smart contract exploits now using those techniques for professional asset recovery.
If you need professional smart contract investigation for DeFi exploit analysis, stolen asset recovery, or fraud investigation, specialized forensic teams trace complex protocol interactions. We offer no upfront charge for non-custodial wallet recoveries.
Contact Crypto Trace Labs for professional smart contract forensic services.
People Also Read
- How to Track Blockchain Transactions: Expert Guide
- How Do Investigators Track Cryptocurrency Through DEXs?
- How Do Investigators Track Cryptocurrency Across Multiple Blockchains?
- How Do Blockchain Bridges Complicate Cryptocurrency Tracing?
About the Author
This article was prepared by Crypto Trace Labs, a London-based blockchain forensics firm founded by VP and Director-level executives from Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS certifications, MLRO qualifications, and Chartered Fellow Grade status with over 10 years DeFi forensics and smart contract investigation experience.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.