Last Updated: February 2026
Most cryptocurrency structuring goes undetected at the time it occurs. Exchange compliance systems flag individual transactions that breach thresholds, but structuring is designed specifically to stay below those thresholds. The real detection happens afterward – when a forensic team receives a referral, pulls months or years of blockchain data, and applies statistical analysis that reveals what real-time monitoring missed. The gap between what compliance teams see in the moment and what forensic analysts reconstruct after the fact is where structuring cases are built or lost.
A companion guide on smurfing patterns explains what structuring looks like on-chain – the threshold clustering, fan-out structures, and peel chains that characterize the technique. This guide focuses on the investigative side: how forensic teams actually identify, prove, and present structuring evidence in cases that reach prosecution. The methodology matters because two landmark court rulings in 2024 – United States v. Sterlingov and United States v. Ahlgren – established for the first time that blockchain forensic analysis meets the Daubert standard for admissibility, setting precedent for every crypto structuring case that follows.
At Crypto Trace Labs, structuring investigations are among our most technically detailed forensic engagements. This guide walks through the process from initial referral to court-ready report.
How Does a Structuring Investigation Begin?
Forensic structuring investigations originate from three primary channels, each producing different starting data and different analytical challenges.
SAR referrals are the most common trigger. When an exchange’s compliance team detects unusual transaction patterns – repeated deposits clustering below reporting thresholds, rapid-fire transactions from multiple wallets to the same account – they file a Suspicious Activity Report with FinCEN or the relevant Financial Intelligence Unit. US regulations require SARs to be filed within 30 calendar days of detecting suspicious activity. FinCEN has clarified that institutions are not required to file structuring SARs absent affirmative indication that transactions are designed to evade reporting – proximity to a threshold alone is not sufficient. But when the pattern is clear, the SAR referral provides investigators with an identified subject, a timeframe, and the exchange’s internal transaction records as a starting point.
Exchange alert systems provide a more granular entry point. Platforms like Chainalysis KYT generate real-time alerts within seconds of on-chain transactions, covering typologies including structuring patterns, mixer interactions, sanctioned address exposure, and darknet market connections. KYT gives compliance teams control over alert thresholds, rules, and typologies, allowing calibration to specific regulatory obligations. When an alert escalates beyond compliance into a law enforcement referral, the forensic team inherits the alert history, the exchange’s internal risk scoring, and often months of monitored transaction data.
Law enforcement referrals arrive when federal agencies – IRS Criminal Investigation, FBI, DEA, HSI – initiate cases based on intelligence from other investigations, informant tips, or cross-referencing blockchain data with existing criminal cases. In United States v. Ahlgren, IRS-CI initiated the investigation after identifying discrepancies between Ahlgren’s reported income and his cryptocurrency trading activity – a lead that came from tax analysis, not blockchain monitoring.
What Is the Step-by-Step Forensic Workflow?
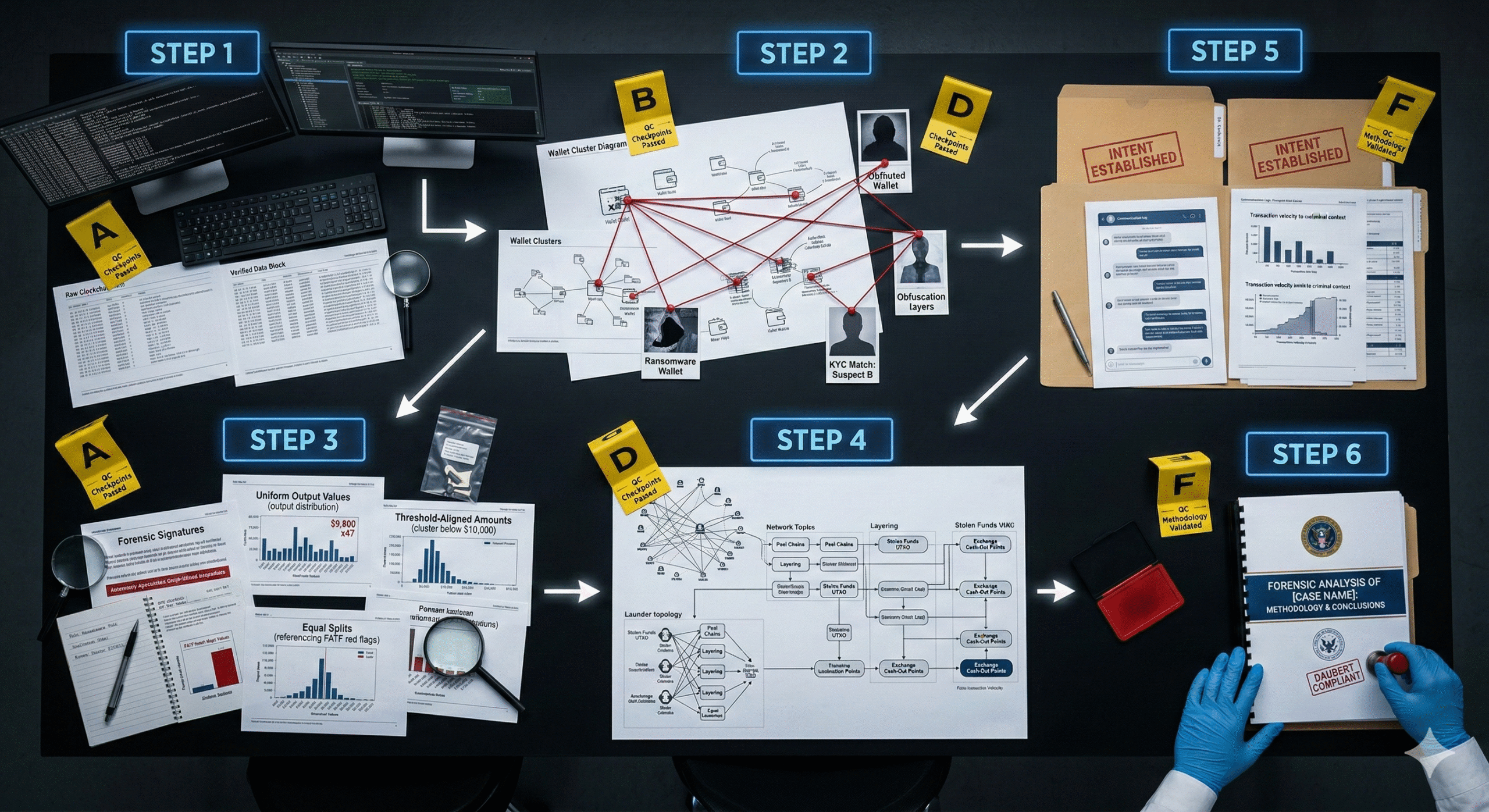
Once a structuring investigation is opened, forensic teams follow a systematic process that moves from data collection through analysis to report production. Each step must be documented with sufficient rigor to survive Daubert challenge and cross-examination.
Step 1: Data collection and preservation
The first phase involves assembling data from multiple sources. Blockchain data – transaction hashes, block timestamps, input/output addresses, amounts, fees, and for UTXO chains the full UTXO lineage – is publicly accessible and does not require a warrant. The Fifth Circuit has held that individuals have no legitimate expectation of privacy in Bitcoin transaction records voluntarily broadcast to a public network. Exchange records obtained via subpoena or court order include account identifiers, KYC documents, deposit/withdrawal logs, IP addresses, and device fingerprints. Digital forensics from seized devices may yield wallet files, private keys, seed phrases, browser history, and communications. In the Helix investigation, investigators recovered cryptocurrency storage devices from residences in Ohio and Belize, and discovered an accounting spreadsheet in Google Drive indicating ownership of over $56 million in Bitcoin.
Step 2: Entity resolution through clustering
The forensic team uses address clustering techniques to group all wallets controlled by the subject into a single entity profile. The common-input-ownership heuristic – when multiple input addresses appear in the same transaction, a single entity likely controls all of them – remains the backbone of Bitcoin clustering, with accuracy approaching 100% in straightforward cases. Change address detection extends the cluster by identifying where unspent outputs return to the sender. UTXO pattern analysis and wallet software fingerprinting provide additional linking signals. The goal is a complete map of every address the subject controls – the foundation for quantifying the total structured amount.
Step 3: Statistical pattern analysis
With the entity profile established, analysts examine the statistical distribution of transaction amounts across the clustered wallets. The core question is whether the distribution is consistent with legitimate behavior or shows anomalous clustering below regulatory thresholds. A wallet whose transactions distribute normally around business-relevant amounts looks fundamentally different from one whose transactions cluster at $9,400-$9,900 with no amounts exceeding $10,000. Analysts apply statistical tests to quantify the improbability of the observed pattern occurring by chance.
Temporal analysis adds a second dimension. Timestamp patterns reveal whether transactions were executed in rapid succession (suggesting deliberate splitting), at regular automated intervals (suggesting scripted execution), or in bursts followed by long dormancy (suggesting disposable wallet operations). Integrating temporal sequencing with flow volume metrics enhances anomaly detection precision.
Step 4: Graph topology analysis
The investigator models the transaction flow as a directed graph and measures structural properties. Fan-out degree measures how many distinct addresses a single source distributes to – high fan-out from one address indicates the distribution phase of a structuring operation. Fan-in degree measures consolidation – many addresses converging to one destination indicates the collection phase. Transaction graph analysis using betweenness centrality identifies intermediary wallets that act as bridges in the structuring network. Graph Convolution Networks have achieved accuracy rates of 98.5% in predicting illicit transactions in research settings.
Step 5: Establishing intent
This is the most legally consequential step. The government must prove the accused acted “knowingly and willfully” – that structuring was done with specific intent to evade reporting requirements, not coincidentally. Forensic teams establish intent through multiple converging lines of evidence:
- Statistical improbability – demonstrating that the observed transaction pattern is inconsistent with any legitimate business purpose
- Behavioral evidence – communications discussing threshold avoidance, internet search history about reporting limits, or witness testimony about the subject’s knowledge of BSA requirements
- Elimination of alternatives – showing no plausible business or personal reason for the specific amounts and timing
- Deliberate obfuscation – evidence that the subject used mixers, newly created wallets, multiple exchanges, or cross-chain laundering alongside the structuring, indicating consciousness of guilt
- Financial sophistication – the subject’s demonstrated knowledge of reporting thresholds, prior compliance training, or previous SARs filed on their activity
In Ahlgren, intent was established through a combination of blockchain tracing, exchange records, witness interviews, and evidence that Ahlgren provided false information to his tax preparer. The convergence of multiple evidence types – not blockchain analysis alone – built the prosecution’s case.
Step 6: Quantification and reporting
The forensic report documents the complete transaction flow from inception to disposition, with dates, counterparties, and valuations at each step. In Ahlgren, Chainalysis experts traced 493 of 640 sold BTC through multiple wallets to Coinbase accounts and the remaining 147 BTC to a “Granny Wallet” and ShapeShift. The report separates facts from inferences and inferences from hypotheses – a structure that helps prosecutors understand what is chargeable and helps meet defense challenges with evidence rather than argument.
How Did Two Landmark Cases Establish Daubert Precedent?
Before 2024, no federal court had conducted a full Daubert hearing specifically on blockchain forensic methodology. Two cases changed that – and their rulings now anchor the admissibility framework for every crypto structuring prosecution.
United States v. Sterlingov – the Bitcoin Fog Daubert hearing
Roman Sterlingov was convicted in March 2024 of money laundering conspiracy for operating Bitcoin Fog, the darknet’s longest-running mixer, which processed over $400 million in cryptocurrency. The defense challenged Chainalysis Reactor as an opaque “black box” unsuitable for legal proceedings, arguing the software had not been peer reviewed and had no known error rate.
Judge Randolph Moss of the D.C. District Court ruled the methodology admissible, finding that Chainalysis employs deterministic clustering – identical inputs consistently produce identical outputs – and attributes addresses only when possessing “directly observable, empirical evidence” of ownership. The court noted that while Reactor was important to the case, it was not the sole basis for prosecution. Other evidence included materials found in Sterlingov’s possession, online forum posts, IP analyses, and traditional blockchain tracing.
The defense also raised a specific evidentiary concern: a typographical error in the original arrest warrant (blockchain address “1KWMex” should have read “1KWMcx”) that was corrected by trial but never disclosed to the defense. While this did not overturn the conviction, it underscores the importance of meticulous documentation in blockchain forensic investigations.
United States v. Ahlgren – structuring meets crypto tax fraud
The Ahlgren case was the first criminal tax evasion prosecution centered solely on cryptocurrency. The court found Chainalysis expert testimony admissible under Daubert, noting that “substantial evidence supports the government’s submission that the software is highly reliable – and, if anything, conservative – in clustering and then attributing bitcoin addresses.” This ruling explicitly addressed the structuring dimension: the forensic methodology that traced Ahlgren’s structured cash deposits, CoinJoin mixing through Wasabi Wallet, and peer-to-peer exchanges was accepted as meeting federal evidence standards.
Together, these rulings establish that blockchain forensic analysis – when properly documented, transparently described, and corroborated by additional evidence – satisfies the reliability requirements of Federal Rule of Evidence 702 as amended in 2023.
How Do Forensic Teams Distinguish Structuring from Legitimate Behavior?
The false positive question is the most contested area in blockchain forensics, and it directly affects structuring investigations where the difference between criminal conduct and coincidental transaction patterns determines whether someone goes to prison.
DeFi activity routinely generates many small transactions that can superficially resemble structuring. Yield farming, liquidity provision, and automated rebalancing create high-frequency, low-value transaction patterns. Forensic analysts distinguish these by confirming that transactions interact with known smart contracts (Uniswap, Aave, Compound), involve token operations rather than fiat on/off-ramps, and follow patterns dictated by protocol mechanics rather than threshold avoidance.
Legitimate order splitting by traders using TWAP or VWAP execution strategies creates many small transactions with algorithmic timing patterns. These interact with known DEX routers, follow consistent counterparty relationships, and are typically executed through smart contract automation rather than manual wallet-to-wallet transfers.
Business payments may cluster near certain amounts coincidentally. Payroll, vendor payments, and recurring subscriptions create regular transaction patterns. Forensic analysts distinguish these by identifying consistent counterparties, predictable intervals aligned with business cycles, and correlation with known payment dates.
The accuracy debate remains active. Chainalysis has published validation studies claiming true positive rates of up to 94.85% with false positive rates below 0.15%. Critics, including competing firm ChainArgos, argue these tests were conducted on “in-sample” data and that real-world accuracy may differ. In the Sterlingov case, Chainalysis’s head of investigations testified she was “unaware of scientific evidence supporting accuracy of Reactor software” and that the company had not gathered comprehensive false positive/negative rates. For investigators at Crypto Trace Labs, this means structuring cases must never rely on blockchain analysis alone – the pattern analysis must be corroborated by exchange records, communications evidence, and circumstantial indicators of intent.
What Emerging Challenges Affect Structuring Forensics?
Privacy coins present the most fundamental challenge. Monero’s ring signatures, stealth addresses, and confidential transactions obscure sender, recipient, and amount. A 2022 academic study concluded that “for now, Monero is untraceable” through on-chain analysis alone, though digital forensic approaches can reveal information through off-chain artifacts such as memory dumps and wallet files on seized devices. The IRS posted a $625,000 bounty in 2020 for tools to trace Monero and Lightning Network transactions, with Chainalysis and Integra FEC winning the contracts – though the resulting capabilities remain largely undisclosed.
Layer 2 structuring adds complexity. Transactions on Lightning Network, Arbitrum, and other Layer 2 systems may not be individually visible on the base chain, reducing the forensic surface area available to investigators. Structuring that occurs entirely within a Layer 2 environment requires specialized tooling that can access L2-specific transaction data.
Smart contract automation enables structuring operations that execute without ongoing human intervention. A smart contract can be programmed to receive a large deposit and automatically distribute it in sub-threshold amounts to a sequence of addresses on a predetermined schedule – creating plausible deniability about whether the structuring was “knowing and willful.” Proving intent when the structuring is embedded in code rather than executed manually requires forensic analysis of the contract’s deployment, its parameters, and who controlled the deployment address.
Cross-chain structuring – distributing structured amounts across multiple blockchains simultaneously – forces investigators to conduct parallel analyses across different data environments. On-chain analysis tools are increasingly capable of cross-chain attribution, but structuring that spans five or ten blockchains with bridge hops between each multiplies the investigative complexity exponentially.
Frequently Asked Questions
Is blockchain forensic evidence admissible in court?
Yes. The Sterlingov and Ahlgren rulings in 2024 established that blockchain forensic analysis meets the Daubert standard for admissibility when the methodology is transparent, reproducible, and corroborated by additional evidence. The blockchain itself provides inherent tamper-evidence through its immutable structure. Investigators must document when they accessed blockchain data, which tools they used, and how they preserved results. Screen captures, tool exports, and raw transaction data should be hashed and stored with timestamps to maintain chain of custody.
How do prosecutors prove structuring intent for cryptocurrency?
Intent is established through converging evidence: the statistical improbability of the transaction pattern occurring by chance, communications showing knowledge of reporting thresholds, absence of any legitimate business rationale for the amounts and timing, use of obfuscation tools alongside the structuring, and the defendant’s financial sophistication. No single factor is sufficient – prosecution requires demonstrating that the totality of evidence supports deliberate threshold avoidance.
What is the difference between real-time monitoring and forensic investigation?
Real-time monitoring operates at the exchange level, generating alerts within seconds based on predefined rules and risk thresholds. It uses a single exchange’s data and serves a compliance function. Forensic investigation operates after the fact, assembling data from multiple exchanges, multiple blockchains, and law enforcement sources over weeks or months. Forensic analysis can apply computationally intensive techniques – full graph analysis, machine learning on complete datasets, cross-referencing with intelligence from other investigations – that are impossible in real time. The forensic product is a court-ready report, not a compliance alert.
Can structuring be proven if the funds are legitimate?
Yes. Under 31 U.S.C. Section 5324, the offense is the act of structuring itself – deliberately breaking transactions into amounts below reporting thresholds to avoid triggering Currency Transaction Reports. Whether the underlying funds are legitimate or illicit is irrelevant to the structuring charge. A person who structures $50,000 in clean money into five $9,900 deposits has committed a federal crime punishable by up to 5 years in prison.
What certifications qualify forensic analysts for structuring cases?
The most relevant certifications include ACAMS (Association of Certified Anti-Money Laundering Specialists) for AML expertise, CAMS (Certified Anti-Money Laundering Specialist) for compliance methodology, and blockchain-specific credentials such as Chainalysis’s Cryptocurrency Fundamentals Certification and CCI (Certified Cryptocurrency Investigator). For digital forensics components, SANS GIAC certifications and IACIS credentials validate evidence handling procedures. Courts assess expert qualifications based on the combination of credentials, practical experience, and prior testimony record.
How accurate are blockchain forensic tools for structuring detection?
Accuracy remains contested. Chainalysis has published validation studies claiming 94.85% true positive rates. Critics argue these tests used in-sample data that may not reflect real-world conditions. In court testimony, a Chainalysis representative acknowledged not having gathered comprehensive false positive/negative rates for the software overall. This is why forensic best practice – and the standard Crypto Trace Labs follows – requires that blockchain analysis be corroborated by independent evidence sources rather than treated as standalone proof.
Does Your Organization Need Structuring Forensics?
If your compliance team has flagged potential structuring activity, or if law enforcement has contacted your exchange about a customer’s transaction patterns, the quality of the forensic analysis determines whether the case advances or stalls. The Daubert precedent established in 2024 means courts now have clear expectations for what constitutes admissible blockchain forensic evidence – and forensic work that falls short of those standards risks exclusion at trial.
Crypto Trace Labs conducts structuring forensic investigations for exchanges, law enforcement agencies, and legal teams. Our forensic team – including analysts like D. Hargreaves – holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. Our founders held VP and Director positions at Blockchain.com, Kraken, and Coinbase.
Contact Crypto Trace Labs to discuss a structuring investigation or to engage our team as forensic experts for an active case.
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, on-chain analysis, and forensic investigation. Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed vanity address exploitation patterns in hundreds of investigations and provided expert witness testimony on blockchain attribution methodologies in court proceedings.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.