Last Updated: February 2026
Cross-chain money laundering has surpassed $21.8 billion in cumulative volume through 2025 – a fivefold increase from $4.1 billion in 2022, according to Elliptic’s State of Cross-Chain Crime report. Over a third of all cryptoasset laundering cases now involve activity across more than three blockchains, and one in five spans more than ten. Elliptic has called chain-hopping the defining money laundering method of 2025. The technique works by exploiting a structural reality of blockchain investigations: every time funds cross from one chain to another, the investigator must identify the bridge, match the lock transaction on the source chain to the mint transaction on the destination chain, and re-establish attribution in an entirely different blockchain’s data model. Each hop multiplies the cost and complexity of the investigation. Criminals know this and design their laundering flows accordingly.
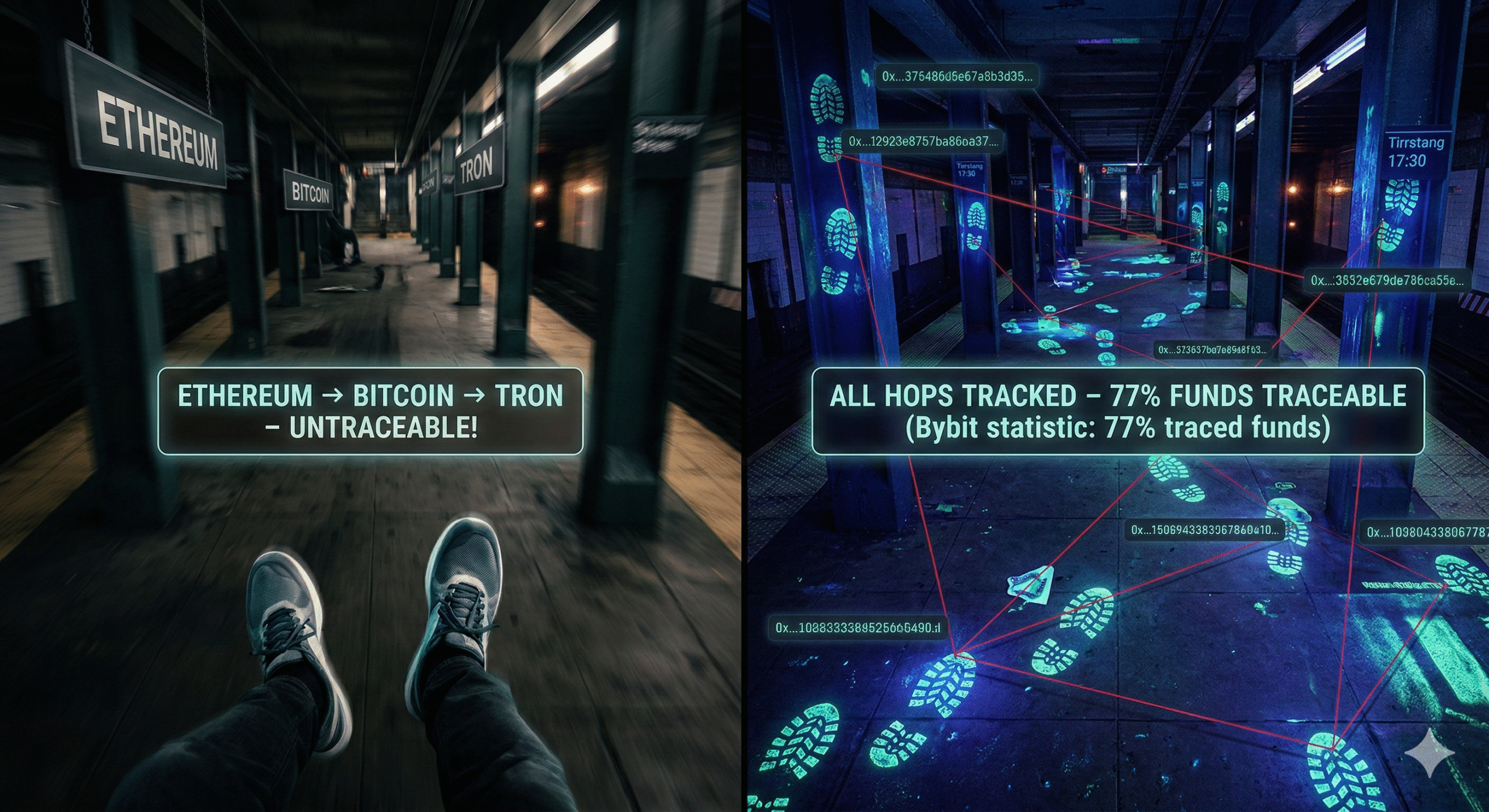
But the same bridge transactions that create investigative friction also create forensic evidence. Every cross-chain hop leaves permanent records on both the source and destination blockchains – vault locks, validator signatures, minting events, and relay transactions that can be reconstructed into a continuous chain of custody. The Bybit hack investigation demonstrated this at unprecedented scale: $1.46 billion stolen, laundered across multiple chains within days, and yet 77% of the funds remained traceable six months later because investigators could follow the bridge forensics faster than the attackers could obscure them.
At Crypto Trace Labs, cross-chain tracing is one of the most technically demanding and fastest-growing areas of our forensic practice. This guide explains how chain-hopping laundering works, what forensic evidence it produces, and how investigators reconstruct the trail across blockchains.
What Investigators Need to Know
- Chain-hopping volume has increased fivefold since 2022 – Elliptic documented $21.8 billion in illicit cross-chain transactions through 2025, with criminals increasingly preferring bridges and no-KYC swap services over traditional mixers
- Bridge transactions leave forensic evidence on both chains – lock-and-mint mechanisms create matching vault deposits and token minting events that investigators can correlate across blockchains
- THORChain processed $1.2 billion in Bybit hack laundering – the no-KYC cross-chain protocol handled 85% of the stolen funds, making it the dominant laundering infrastructure of 2025
- Modern chain-hopping investigations routinely span 5-10+ blockchains – tools like Chainalysis Reactor, Elliptic Holistic, and TRM Labs now automate cross-chain attribution across hundreds of bridge protocols
- Speed is the critical variable – Bybit attackers laundered $160 million within 48 hours and 100% of unfrozen funds within 10 days, making rapid cross-chain tracing essential for any recovery effort
How Does Chain-Hopping Laundering Work?
Chain-hopping follows a predictable sequence that investigators have documented across dozens of major cases. The specifics vary – different bridges, different destination chains, different cash-out methods – but the structural pattern is consistent.
Stage 1: Acquisition and fragmentation. The attacker steals cryptocurrency from an exchange, bridge, or DeFi protocol. Within minutes, the funds are split across dozens of intermediary wallets to complicate transaction graph analysis. In the February 2025 Bybit hack, approximately 50 new wallets each received roughly 10,000 ETH within hours of the theft.
Stage 2: Same-chain swapping. Before leaving the source blockchain, attackers swap stolen tokens into more liquid assets using decentralized exchanges that require no identity verification. Uniswap, Curve, and 1inch are the most commonly used. A staggering $1.2 billion has been laundered through DeFi aggregators alone. This step converts identifiable stolen tokens – which exchanges can freeze – into fungible assets like ETH or stablecoins that are harder to blacklist.
Stage 3: Cross-chain bridge hops. The core of the technique. Funds are sent to a cross-chain bridge smart contract on the source blockchain, which locks them in a vault. The bridge protocol then mints equivalent tokens on the destination blockchain. Each hop moves the funds into a different blockchain’s ecosystem, forcing investigators to track the assets across entirely different data structures. The Lazarus Group’s preferred route in 2025 was Ethereum to Bitcoin via THORChain, followed by distribution across thousands of Bitcoin wallets.
Stage 4: Mixing and obfuscation. On the destination chain, funds may pass through coin mixers, CoinJoin transactions, or no-KYC swap services to break the link between bridge output and final destination. After Tornado Cash was sanctioned in 2022, criminals shifted to services like eXch (seized by German authorities in May 2025 after processing approximately $200 million in Bybit proceeds) and Wasabi Wallet’s CoinJoin protocol.
Stage 5: Cash-out. The final conversion to fiat currency typically occurs through OTC brokers, exchanges with weak KYC controls, or peer-to-peer trading platforms. In recent Lazarus Group operations, the cash-out stage involved moving funds to the Tron blockchain, converting to USDT, and exiting through suspected Chinese OTC services connected to Huione Group entities – part of a broader network that Chainalysis identified as funneling $16.1 billion in illicit crypto during 2025.
What Forensic Evidence Do Bridge Transactions Leave?
The mechanism that makes cross-chain bridges work is the same mechanism that makes them forensically traceable. Understanding the lock-and-mint architecture is essential for investigators.
When a user sends tokens to a bridge, the bridge’s smart contract on the source chain locks those tokens in a vault. This lock transaction is permanently recorded – it shows the sender address, the exact amount, the timestamp, and the bridge contract address. The bridge protocol then communicates with the destination chain (through validator networks, relayers, or oracle systems depending on the bridge design) and mints an equivalent amount of wrapped or proxy tokens to a specified recipient address on the destination chain.
These two events – the vault lock and the destination mint – are the forensic anchors. They occur on different blockchains but are cryptographically linked through the bridge protocol’s internal messaging. An investigator who identifies a vault lock transaction on Ethereum can determine which bridge was used, query that bridge’s event logs, and find the corresponding mint transaction on the destination chain – along with the recipient address that received the funds.
Each bridge hop also generates intermediate forensic artifacts: validator signatures confirming the cross-chain message, relay transactions that carry the message between chains, and protocol-specific event logs that record the routing details. For investigators conducting on-chain analysis, the challenge is not that bridge evidence does not exist – it is that the evidence is distributed across multiple blockchains and multiple protocol layers, requiring specialized tooling to reconstruct.
Additional signals help investigators detect chain-hopping activity even before identifying specific bridge transactions. Cross-chain velocity indicators – rapid sequential transactions involving bridge contracts across multiple chains within short timeframes – flag potential laundering. Unusual bridge transaction sizes that do not match normal user behavior suggest automated systems. And gas price patterns on the source chain can distinguish between human bridge users and automated laundering scripts executing programmatic cross-chain transfers.
How Did Investigators Trace $1.46 Billion Through the Bybit Hack?
The February 21, 2025 Bybit hack is the largest cryptocurrency theft in history and the most extensively documented chain-hopping investigation to date. The Lazarus Group compromised Bybit’s multi-signature cold wallet through a manipulated SafeWallet interface and extracted approximately 500,000 ETH ($1.46 billion).
The laundering operation moved at unprecedented speed. Within 48 hours, at least $160 million had been processed through cross-chain bridges. By February 26 – five days after the theft – over $400 million was laundered. Within 10 days, 100% of unfrozen stolen ETH had been moved through the laundering pipeline.
THORChain was the primary laundering conduit. The no-KYC cross-chain swap protocol processed $1.2 billion of the stolen funds – 85% of the total. On the day of the hack, THORChain recorded $529 million in daily swap volume, its largest trading day ever against a normal average of $80 million per day. The attackers converted ETH to BTC through THORChain and distributed the Bitcoin across 6,954 wallets. Validators and wallet services on THORChain earned over $12 million in fees from Bybit-linked transactions.
The investigation revealed several novel laundering techniques. The “worthless token” method involved creating entirely fictitious tokens, establishing liquidity pools for them on DEXs, swapping stolen USDT through those pools, and converting back to legitimate stablecoins on fresh addresses – laundering at least $24 million through this technique alone. Another innovation exploited refund addresses: during intentionally failed exchange transactions, rejected deposits were routed to completely new wallets rather than back to the originating address, breaking the transaction trail.
Despite the speed and sophistication, investigators maintained attribution. The FBI attributed the hack to North Korea’s Lazarus Group within five days. Six months after the theft, Elliptic reported that 77% of the funds remained traceable, 20% ($280 million) had become untraceable, and 3% had been frozen. The traceable percentage demonstrates that even the most sophisticated chain-hopping operation leaves a recoverable forensic trail when investigators deploy cross-chain tools quickly enough.
Why Did Criminals Shift from Mixers to Cross-Chain Bridges?
The shift from coin mixers to cross-chain bridges as the preferred laundering infrastructure was driven by enforcement pressure. When OFAC sanctioned Tornado Cash in August 2022 for laundering over $1.5 billion (including $455 million from North Korea’s Ronin Bridge hack), it removed the most popular Ethereum mixing service from the criminal toolkit. Subsequent enforcement against mixers Sinbad and YoMix further narrowed the options.
Cross-chain bridges offered several advantages that mixers could not. Mixers obscure the link between sender and receiver within a single blockchain – the funds stay on the same chain, just with a broken transaction trail. Bridges move funds to entirely different blockchains, forcing investigators to work across multiple data environments simultaneously. Mixers also face a liquidity problem: a mixer can only process as much volume as its anonymity set allows, and low-volume mixers provide weak privacy. Bridge protocols like THORChain handle billions in legitimate daily volume, allowing illicit funds to blend with ordinary cross-chain trading activity.
The regulatory landscape reinforced this shift. While OFAC sanctioned Tornado Cash, the Fifth Circuit ruled in November 2024 that immutable smart contracts are not sanctionable “property” under IEEPA. OFAC delisted Tornado Cash in March 2025. But by then, the Lazarus Group had already built its infrastructure around THORChain and no-KYC swap services – a pipeline that proved even more effective than mixers for high-volume laundering.
The Ronin Bridge hack in March 2022 illustrates the transition. When the Lazarus Group stole $620 million in ETH and USDC from Axie Infinity’s Ronin network, they initially laundered over $455 million through Tornado Cash. After the sanctions, their subsequent operations – including the $308 million DMM Bitcoin theft (May 2024), the $235 million WazirX attack (July 2024), and the Bybit hack – relied primarily on cross-chain bridges and DEX swapping. Investigators who had built expertise in mixer analysis had to rapidly develop new capabilities for cross-chain forensics.
What Tools Do Investigators Use for Cross-Chain Tracing?
The commercial blockchain analytics industry has invested heavily in cross-chain capabilities as chain-hopping became the dominant laundering method.
Chainalysis Reactor traces transactions across 27+ blockchains and 40 million+ assets. Its Transaction Explorer follows funds through 325 million+ recorded swaps across 300+ bridges and DEXs. The tool played a direct role in the Ronin hack recovery, enabling the seizure of $30 million in stolen funds – the first-ever recovery of cryptocurrency stolen by a North Korean hacking group.
Elliptic Holistic, powered by the Nexus analytics engine, introduced the concept of Virtual Value Transfer Events (VVTEs) – technology that establishes direct, verifiable links between source and destination transactions across 300+ bridging protocol combinations. In a documented North Korean case, Elliptic traced 48 transactions across 5 blockchains automatically in seconds – an investigation that would have taken hours manually.
TRM Labs uses machine learning models to detect laundering typologies and reconstruct multichain transaction paths. TRM’s analysis of the Bybit hack coined the “flood the zone” description of the Lazarus Group’s tactic of overwhelming compliance teams with rapid, high-frequency transactions across multiple platforms simultaneously.
Arkham Intelligence uses a proprietary AI engine called ULTRA to process data from multiple blockchains alongside public records and social media, maintaining over 350 million labeled addresses across 200,000+ profiled entities. Its core capability – linking real-world identities to blockchain addresses – supports the final attribution step in cross-chain investigations.
For investigators at Crypto Trace Labs, the choice of tool depends on the investigation’s requirements. Commercial platforms excel at automated cross-chain attribution, but complex cases still require manual bridge-by-bridge tracing combined with address clustering, input pattern analysis, and timing correlation to build the complete evidentiary picture.
How Has THORChain Become the Center of the Chain-Hopping Problem?
THORChain is a decentralized cross-chain liquidity protocol that allows cryptocurrency swaps between Bitcoin, Ethereum, BNB Chain, Avalanche, Cosmos, Dogecoin, and other networks without intermediaries or identity verification. Its design explicitly prioritizes permissionless access – any user can swap assets by simply sending a transaction with the appropriate routing memo.
This design made THORChain the infrastructure of choice for the largest state-sponsored laundering operation in cryptocurrency history. Beyond the $1.2 billion in Bybit proceeds, Elliptic documented over a dozen additional DPRK-attributed thefts in 2025 totaling $1.75 billion that also used THORChain as part of the laundering chain.
The protocol’s response to the Bybit situation exposed tensions between decentralization principles and legal obligations. When the FBI contacted THORChain on February 27, 2025, urging private entities to block DPRK-linked addresses, three validators voted to halt Ethereum swaps on the protocol. The halt was overturned within 30 minutes following community opposition. THORChain founder JP Thor recommended nodes continue trading, claiming no OFAC-listed addresses directly interacted with THORChain. A core developer known as “Pluto” resigned in protest, stating he would no longer contribute to the project.
U.S. Treasury officials warned that anyone earning fees from transactions involving hacked funds potentially faces OFAC liability. THORChain validators and wallet services collectively earned over $12 million from Bybit-linked transactions. The Asgardex wallet alone earned $1 million; the Vultisig wallet reported $200,000. No sanctions or enforcement actions had been taken against THORChain itself or its node operators as of mid-2025, but the precedent set by Tornado Cash sanctions – and the subsequent legal reversal – leaves the regulatory status of decentralized bridge protocols unresolved.
Frequently Asked Questions
What is chain hopping in cryptocurrency?
Chain hopping is the practice of rapidly moving cryptocurrency across multiple blockchains using cross-chain bridges, decentralized exchanges, and swap services to obscure the origin of funds. Criminals exploit the fact that each blockchain maintains its own separate ledger – by moving funds from Ethereum to Bitcoin to Tron to BNB Chain, they force investigators to trace the same funds across entirely different data environments. Elliptic’s research shows that over a third of laundering cases now involve more than three blockchains, and 20% span more than ten.
Can cross-chain bridge transactions be traced by law enforcement?
Yes. Bridge transactions leave permanent forensic evidence on both the source and destination blockchains. The lock transaction on the source chain and the corresponding mint transaction on the destination chain can be matched through bridge protocol event logs. Commercial tools like Chainalysis Reactor and Elliptic Holistic automate this matching across 300+ bridge protocol combinations. The Bybit hack investigation demonstrated that 77% of $1.46 billion in chain-hopped funds remained traceable six months after the theft.
How much cryptocurrency has been laundered through chain hopping?
Elliptic’s 2025 report documented $21.8 billion in cumulative cross-chain crime – a fivefold increase from $4.1 billion in 2022. Chainalysis’s 2026 report found that illicit cryptocurrency addresses received a record $154 billion in 2025, with stablecoins accounting for 84% of illicit transaction volume. North Korean hackers alone stole over $2 billion in 2025, primarily using chain-hopping laundering methods.
Why did criminals shift from mixers to cross-chain bridges?
The OFAC sanctions against Tornado Cash in August 2022 removed the most popular Ethereum mixer from criminal use. Cross-chain bridges offered advantages that mixers could not: they move funds to entirely different blockchains rather than just obscuring links within one chain, they handle billions in legitimate daily volume that provides cover for illicit transactions, and decentralized protocols like THORChain operate without the centralized control points that made Tornado Cash sanctionable.
What is a Virtual Value Transfer Event (VVTE)?
VVTEs are a cross-chain attribution technology developed by Elliptic that establishes direct, verifiable links between source and destination transactions across different blockchains. When funds move through a bridge, the VVTE framework automatically matches the deposit on the source chain to the corresponding withdrawal on the destination chain, converting what would be a multi-hour manual investigation into a single-click automated trace. The technology covers 300+ bridging protocol combinations.
How quickly do criminals launder stolen cryptocurrency through chain hopping?
Speed has increased dramatically. In the February 2025 Bybit hack, attackers laundered $160 million within 48 hours and 100% of unfrozen funds within 10 days. This represents an acceleration from earlier cases: the 2022 Ronin Bridge laundering via Tornado Cash took weeks to months. The Lazarus Group now employs a “flood the zone” strategy – overwhelming compliance teams with rapid, high-frequency transactions across multiple platforms simultaneously – that requires investigators to deploy real-time monitoring tools within hours of a theft to maximize the chance of freezing funds before they exit to fiat.
Is Your Organization Exposed to Cross-Chain Laundering Risk?
If your exchange, DeFi protocol, or custodial service processes cross-chain transactions, you are a potential entry or exit point in a chain-hopping laundering flow. The speed of modern chain-hopping operations – $160 million in 48 hours in the Bybit case – means that every hour between a theft and the initiation of cross-chain tracing reduces the percentage of recoverable funds. Exchanges that credited Lazarus Group deposits after insufficient confirmations lost millions before the chain-hop was even detected.
Crypto Trace Labs conducts cross-chain forensic investigations for exchange fraud cases, bridge exploit recovery, and regulatory enforcement actions involving multi-blockchain laundering. Our forensic team – including analysts like D. Hargreaves – holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. Our founders held VP and Director positions at Blockchain.com, Kraken, and Coinbase.
Contact Crypto Trace Labs immediately if you suspect your platform has been used in a chain-hopping laundering operation or if you need cross-chain tracing for an active investigation.
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, on-chain analysis, and forensic investigation. Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed vanity address exploitation patterns in hundreds of investigations and provided expert witness testimony on blockchain attribution methodologies in court proceedings.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.