Last Updated: February 2026
Wallet software fingerprinting identifies which cryptocurrency wallet applications users employ by analyzing transaction characteristics including distinctive fee calculation algorithms each wallet implements, transaction structure patterns revealing software-specific transaction creation logic, address generation schemes following wallet-specific derivation paths, timing precision indicating automated versus manual operations, and version-specific behaviors that change when developers release software updates. Investigators leverage these fingerprints to attribute addresses to specific wallet implementations – knowing an address uses Wasabi Wallet indicates privacy-consciousness requiring different investigation approaches than addresses using Coinbase Wallet, while identifying Electrum usage helps predict user behaviors based on wallet functionality and typical user profiles.
At Crypto Trace Labs, our team applies wallet fingerprinting across hundreds of blockchain forensics and cryptocurrency investigation cases. This guide draws on that decade of transaction analysis experience to explain wallet fingerprinting methodologies, detection accuracy, and investigative applications.
Key Takeaways
- Fee calculation algorithms create wallet-specific signatures – Electrum’s dynamic estimation differs measurably from Bitcoin Core’s optimization, enabling identification through statistical fee pattern analysis
- Transaction version numbers reveal wallet software – different wallets implement specific version preferences (version 1 vs. 2), creating immediate classification signals
- Address derivation paths follow wallet-specific standards – BIP44, BIP49, and BIP84 implementations vary by wallet, visible through HD wallet address generation patterns
- Locktime usage patterns distinguish implementations – some wallets set locktime to current block height, others use zero, creating binary classification opportunities
- Script type preferences indicate wallet generation – Legacy P2PKH, SegWit P2WPKH, or Nested SegWit P2SH-P2WPKH usage correlates strongly with specific wallet software
- Change address placement reveals transaction creation logic – position of change outputs (first vs. last) follows wallet-specific conventions enabling software attribution
What On-Chain Characteristics Reveal Wallet Software?
Bitcoin transactions contain numerous technical parameters wallet software must specify. Developers make implementation choices about fee estimation, transaction structure, address types, and timing that create distinctive patterns. While functionally equivalent, specific parameter choices reveal which software created them.
Fee calculation methodology represents the most reliable fingerprint. Each wallet implements proprietary algorithms analyzing mempool conditions. Electrum queries external fee estimation APIs. Bitcoin Core calculates fees using internal mempool analysis with conservative bias. Wasabi implements privacy-focused randomization. These algorithmic differences create measurable statistical distributions enabling wallet identification.
Transaction structure parameters include version numbers, locktime settings, input/output ordering, and script types. Bitcoin Core typically uses version 2 with locktime set to current block height. Electrum often uses version 1 with zero locktime. These choices create binary classification signals.
Address generation schemes follow wallet-specific derivation path standards. Hardware wallets implement BIP44, BIP49, or BIP84 based on firmware versions. Software wallets make different choices. Observing which address types addresses generate reveals underlying wallet software.
Temporal characteristics include transaction timing precision, fee adjustment frequency, and UTXO selection patterns. Automated wallets execute with microsecond precision. Manual usage shows natural variance. These temporal signatures complement structural fingerprints.
How Do Investigators Fingerprint Wallet Software?
Comparison Table: Wallet Software Fingerprinting Methodologies
| Wallet Software | Fee Algorithm Signature | Transaction Version | Locktime Pattern | Address Type Preference | Change Position | Overall Confidence |
| Bitcoin Core | Internal mempool analysis, conservative | Version 2 | Current block height (anti-fee-sniping) | Native SegWit P2WPKH | Last output | 90-95% |
| Electrum | External API query (percentile-based) | Version 1 or 2 | Typically 0 | Configurable, often Legacy or SegWit | Variable | 85-92% |
| Wasabi Wallet | Privacy randomization, intentional variance | Version 2 | Random values | Native SegWit P2WPKH | Randomized | 88-94% |
| Ledger Live | Conservative premium (15-25% above optimal) | Version 2 | Current block or 0 | User-configurable SegWit | Typically last | 80-88% |
| Exodus Wallet | Moderate fees, API-derived | Version 2 | Varies | Native SegWit P2WPKH | Last output | 75-85% |
| Coinbase Wallet | Exchange-optimized batching algorithms | Version 2 | Current block height | Native SegWit P2WPKH | Variable | 85-90% |
Fee estimation API analysis identifies wallets querying external services versus internal calculation. Investigators monitor public fee estimation APIs logging which addresses request fee data, then correlate API query timing with subsequent transaction broadcasts. When addresses consistently broadcast transactions 30-90 seconds after API queries with fees matching API recommendations, external fee estimation usage is confirmed.
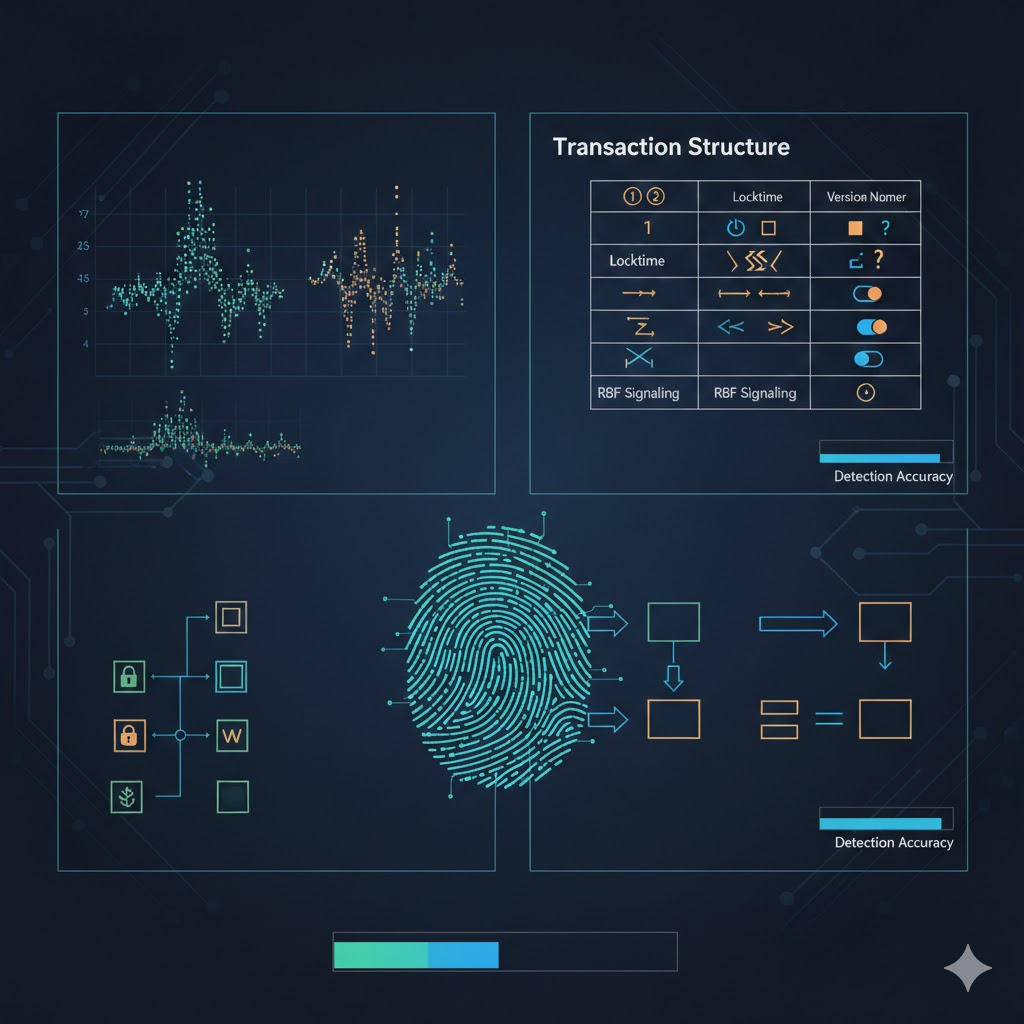
Transaction structure parsing examines every transaction parameter building statistical profiles. Automated systems extract version numbers, locktime values, input/output counts, RBF signaling, and script types for millions of transactions. Machine learning models trained on labeled datasets (transactions from known wallet software) learn parameter combinations characteristic of specific implementations, then classify unknown transactions based on learned patterns.
Address type progression tracking observes how addresses evolve over time. Early Bitcoin Core versions generated Legacy P2PKH addresses. Later versions defaulted to Native SegWit. Observing when addresses transition between types reveals software updates or wallet migrations. Users switching from Electrum to Bitcoin Core show characteristic address type transitions detectable through temporal analysis.
Change address fingerprinting analyzes transaction outputs identifying patterns in change output placement and characteristics. Some wallets always place change as the first output, others as the last output, while privacy implementations randomize position. Change outputs typically match input address types (spending from SegWit creates SegWit change), though wallet-specific exceptions create additional fingerprints.
What Wallet-Specific Patterns Enable Attribution?
Numbered Listicle: 7 Wallet Software Signatures Investigators Detect
1. Bitcoin Core’s Anti-Fee-Sniping Locktime
Bitcoin Core implements anti-fee-sniping protection by setting transaction locktime to current blockchain height minus 1-2 blocks. This prevents miners from reorganizing blocks to steal fees. Transactions with locktime values matching recent block heights indicate Bitcoin Core implementations. Combined with version 2 transactions and conservative fee estimation, this pattern enables 90%+ identification confidence.
2. Electrum’s External Fee API Dependency
Electrum queries external fee estimation servers rather than calculating fees internally. Addresses using Electrum broadcast transactions 30-90 seconds after fee API queries, with fee values precisely matching API percentile recommendations. Investigators monitoring fee API logs identify Electrum users through timing correlation and fee matching, achieving 85-92% attribution accuracy.
3. Wasabi Wallet’s CoinJoin Coordination Patterns
Wasabi implements privacy-focused CoinJoin transactions with distinctive characteristics. CoinJoin rounds combine inputs from 20-100 participants creating equal-value outputs. Wasabi-specific patterns include coordinator fee structures (0.003%), hourly coordination timing, and deterministic output amounts. These patterns enable Wasabi identification even when individual user de-anonymization remains infeasible.
4. Hardware Wallet Derivation Path Conventions
Ledger and Trezor hardware wallets implement standard BIP derivation paths with manufacturer-specific variations. Observing address generation sequences reveals derivation implementations – addresses following m/84’/0’/0’/0/X sequential patterns indicate BIP84. Combined with conservative fees and specific transaction structures, investigators attribute hardware wallet usage with 80-90% confidence.
5. Mobile Wallet Battery Optimization Patterns
Mobile cryptocurrency wallets implement battery optimization affecting transaction timing and fee selection. Mobile wallets batch transaction creation to minimize battery drain, creating clustered timing – multiple transactions within 2-5 minute windows. Fee selection shows mobile API dependency. These patterns distinguish mobile from desktop wallet usage.
6. Exchange Hot Wallet Batch Processing
Cryptocurrency exchanges implement sophisticated hot wallet management creating distinctive patterns. Batch withdrawal processing combines 50-200+ customer withdrawals into single transactions executed hourly. These batches exhibit high input counts, varied output amounts, systematic timing, and exchange-specific fee optimization. Investigators identify exchange hot wallets with 95%+ confidence.
7. Privacy Wallet Randomization Signatures
Privacy-focused wallets implement intentional randomization attempting to defeat fingerprinting. However, the randomization itself creates signatures. Samourai Wallet randomizes change positions, adds fee variance, and implements custom structures. The randomization follows detectable statistical distributions – fees varying ±15% around optimal, uniformly distributed change positions. Machine learning models detect these patterns achieving 75-85% accuracy.
How Accurate Is Wallet Software Attribution?
Single-signal fingerprinting achieves 65-85% accuracy depending on distinctiveness. Fee patterns alone correctly identify Bitcoin Core versus Electrum 75-80% of cases. Transaction version alone provides 65-70% accuracy. Address type preference achieves 80-85% accuracy for clear-cut cases (Legacy vs. Native SegWit).
Multi-signal analysis combining 4-6 fingerprints increases accuracy to 88-95% for well-characterized wallets. When fee patterns, transaction structure, address types, change behavior, and temporal characteristics all indicate Bitcoin Core, attribution confidence exceeds 90%. Machine learning models trained on labeled transaction datasets achieve 92-95% accuracy on test sets when sufficient fingerprints are available.

Version-specific accuracy varies – recent wallet versions with distinctive features achieve higher accuracy than older implementations with generic patterns. Wasabi Wallet’s CoinJoin coordination enables 88-94% identification. Generic wallet implementations using standard libraries achieve only 60-70% accuracy lacking distinctive fingerprints.
False positive rates remain 5-15% across methodologies. Similar wallet implementations using shared libraries create overlapping fingerprints causing misattribution. Sophisticated users deliberately mimicking different wallet signatures can defeat automated classification, though such evasion requires significant technical knowledge.
What Investigation Applications Exist?
Criminal profiling benefits from wallet identification revealing operational sophistication. Criminals using Wasabi demonstrate privacy-consciousness requiring enhanced investigation techniques. Basic mobile wallet usage suggests lower sophistication enabling different approaches. Wallet attribution guides investigation strategy allocation.
Exchange identification through hot wallet fingerprinting enables targeted KYC requests. When investigators identify Coinbase, Kraken, or Binance hot wallets through batch withdrawal signatures, cooperation requests target specific platforms. This focused approach accelerates investigations.
Money laundering network mapping uses wallet fingerprints to identify infrastructure tiers. Criminal operations often employ different software at various stages – basic wallets for initial receipt, privacy wallets for layering, exchange wallets for cash-out. Tracking wallet transitions reveals operational structure.
Privacy practice assessment determines whether addresses employ intentional privacy techniques. Detecting Wasabi or CoinJoin usage signals deliberate privacy-consciousness. Conversely, basic wallet identification suggests limited privacy awareness enabling simpler tracking methodologies.
Frequently Asked Questions
How do wallet software updates affect fingerprinting?
Wallet developers modify fee algorithms, transaction structures, and default settings in software updates, changing fingerprints over time. Bitcoin Core 24.0 implements different locktime behavior than Bitcoin Core 22.0. Electrum 4.x uses different fee APIs than Electrum 3.x. Investigators maintain version-specific fingerprint databases documenting changes across releases. Address histories showing fingerprint transitions (Bitcoin Core 22 patterns shifting to Bitcoin Core 24 patterns) reveal software update timing. This temporal analysis enables not just wallet identification but version attribution, providing 70-85% accuracy for version-level classification when sufficient transaction history exists.
Can users deliberately spoof wallet fingerprints?
Technically sophisticated users can manually construct transactions mimicking different wallet software fingerprints. Custom transaction creation tools enable arbitrary parameter specification – setting locktime values, choosing specific version numbers, calculating fees matching target algorithms. However, spoofing requires consistent application across all transactions. Missing single fingerprint (forgetting to randomize change position while mimicking Wasabi) breaks the deception. Most users lack technical knowledge for effective spoofing. Investigators detect spoofing attempts through inconsistency analysis – fingerprints that don’t correlate properly across multiple dimensions indicate manual construction rather than organic wallet usage.
How does wallet fingerprinting work on Ethereum?
Ethereum’s account-based model eliminates UTXO-specific fingerprints like input selection and change addresses. However, wallet-specific patterns remain detectable through gas price estimation algorithms, nonce management patterns, transaction data field usage, and contract interaction sequences. MetaMask implements different gas estimation than Coinbase Wallet. Hardware wallets show characteristic contract interaction patterns. Mobile wallets exhibit timing signatures distinct from desktop implementations. While methodologies differ from Bitcoin analysis, behavioral fingerprinting principles apply achieving 70-85% wallet identification accuracy on Ethereum when sufficient transaction history exists.
What privacy wallets are most difficult to fingerprint?
Samourai Wallet and Wasabi Wallet implement the most sophisticated anti-fingerprinting measures including intentional randomization, custom transaction structures, and deliberate variance injection. However, the anti-fingerprinting behaviors themselves create signatures – intentional randomization follows detectable statistical distributions, custom structures differ from standard implementations, and CoinJoin coordination requires observable coordination. The paradox is that privacy wallets become identifiable precisely through their privacy implementations, though individual user de-anonymization remains difficult. Crypto Trace Labs achieves 88-94% accuracy identifying Wasabi usage while respecting that individual CoinJoin participant attribution requires additional analysis.
How do investigators validate wallet fingerprinting results?
Validation combines multiple approaches. Cross-referencing against known addresses with confirmed wallet software provides ground truth verification. Temporal consistency checking ensures fingerprints remain stable across transaction histories – inconsistent fingerprints suggest mixed wallet usage or spoofing attempts. External intelligence correlation validates classifications through exchange cooperation, seized device analysis, or user statements. Machine learning confidence scores quantify attribution certainty – scores below 75% trigger manual review while scores above 90% receive high confidence. Multi-investigator review validates findings before using wallet attribution in legal proceedings or asset recovery actions.
What future developments will affect wallet fingerprinting?
Privacy-preserving technologies like Taproot, MAST, and Schnorr signatures reduce fingerprint distinctiveness by standardizing transaction structures. Taproot makes complex scripts appear identical to simple payments eliminating script-based classification. Widespread adoption will reduce fingerprinting accuracy requiring investigators to develop new methodologies. However, wallet implementation differences in Taproot adoption timing, fee estimation during transition periods, and version migration patterns create new temporary fingerprints. Lightning Network adoption adds layer-2 fingerprints including channel opening patterns, routing preferences, and on-chain settlement behaviors. The fingerprinting cat-and-mouse game continues as privacy technology advances and investigators adapt methodologies.
Professional Wallet Fingerprinting Services
Wallet software identification requires comprehensive transaction analysis, pattern recognition expertise, and continuously updated fingerprint databases that most organizations lack. Whether investigating cryptocurrency theft, fraud operations, or compliance violations, professional wallet attribution can reveal user sophistication levels and guide investigation strategies.
Our team at Crypto Trace Labs brings VP and Director-level experience from Blockchain.com, Kraken, and Coinbase. We maintain proprietary wallet fingerprint databases covering 50+ wallet implementations, updated continuously as developers release new versions.
What we provide:
- Multi-signal wallet fingerprinting combining fee patterns, transaction structure, and temporal analysis
- Version-level attribution identifying specific wallet software releases
- Privacy wallet detection including Wasabi, Samourai, and CoinJoin usage
- Exchange hot wallet identification enabling targeted KYC cooperation requests
- Behavioral profiling assessing user technical sophistication
- Machine learning classification achieving 88-95% attribution accuracy
For investigation services, we provide transparent project-based pricing based on case complexity and analysis depth.
Schedule a Free Consultation – We’ll review your situation and explain how wallet fingerprinting can support your investigation or compliance requirements.
People Also Read
- How Does Blockchain Forensics Work? Expert Methods Explained
- What Is On-Chain Analysis? Complete Guide to Blockchain Data
- How to Track Blockchain Transactions: Expert Guide
- What Is Cryptocurrency Fraud Investigation? Complete Guide
- Can Stolen Cryptocurrency Actually Be Recovered?
- What Is Cryptocurrency AML Compliance?
- How to Trace Cryptocurrency Through Mixers: Expert Guide
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, wallet software development, and forensic investigation.
Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have developed proprietary wallet fingerprinting algorithms, maintained comprehensive fingerprint databases, and applied wallet attribution in hundreds of cryptocurrency investigations.
For professional blockchain forensics, wallet fingerprinting, or cryptocurrency investigation services, visit cryptotracelabs.com or schedule a consultation.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Wallet fingerprinting methodologies and attribution accuracy vary based on specific circumstances and available transaction data. Consult qualified professionals regarding your situation.