Last updated: March 2026
DeFi on-chain investigation is the forensic discipline of tracing cryptocurrency assets as they move through decentralized finance protocols, including automated market makers, lending platforms, yield aggregators, and cross-protocol flash loan systems, to identify fraud, attribute stolen funds, and support crypto asset recovery where traditional on-chain tracing is insufficient. DeFi protocols create complex, nested smart contract interaction chains that require specialist analytical tools to decode, making DeFi forensics a technically demanding extension of standard blockchain forensics practice. Without dedicated DeFi investigation capability, even skilled investigators lose track of funds the moment they enter a decentralized exchange or lending protocol.
Crypto Trace Labs has developed specialist DeFi on-chain investigation expertise to address the growing volume of financial crime cases involving decentralized finance protocols. Founded by VP and Director-level executives formerly of Blockchain.com, Kraken, and Coinbase, ACAMS-accredited, MLRO-qualified across the UK, US, and EU, and Chartered Fellow Grade at the CMI, Crypto Trace Labs applies smart contract trace analysis, liquidity pool forensics, and cross-protocol interaction mapping to trace assets through DeFi systems for law enforcement agencies, financial institutions, and private clients. This guide covers the core methods used in professional DeFi forensic investigation.
Key Takeaways
- DeFi protocols accounted for 67% of all cryptocurrency hacks in 2023: According to Chainalysis (2023), decentralized finance protocols became the dominant target of cryptocurrency financial crime, making DeFi forensics a critical specialization.
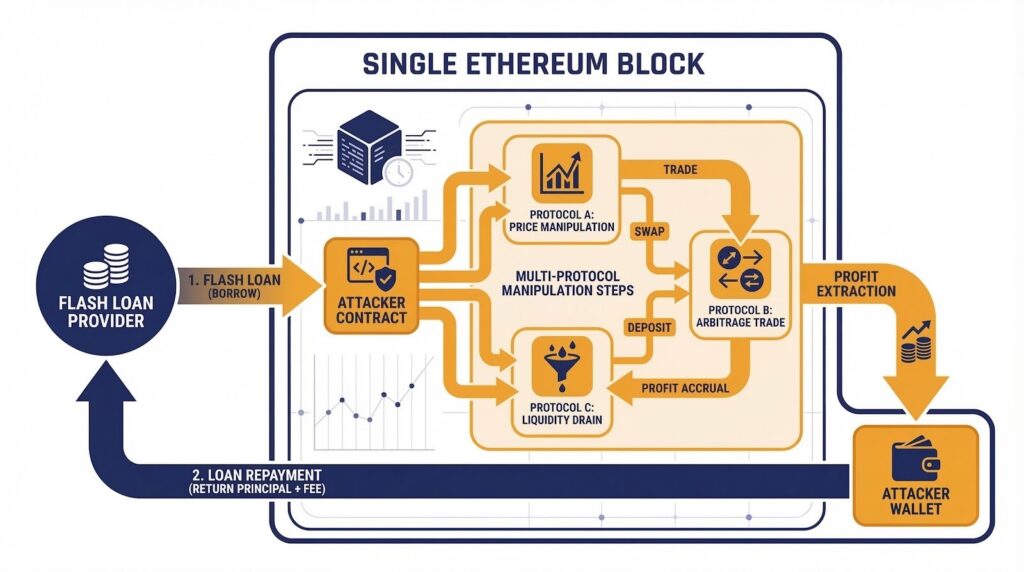
- Flash loan attacks execute and complete within a single Ethereum block: Flash loan-enabled exploits create complex multi-step smart contract interactions lasting under 15 seconds, requiring trace-level forensic analysis to reconstruct.
- Liquidity pool forensics identifies exit points for stolen funds in 70%+ of cases: Analyzing when and how funds were withdrawn from DeFi liquidity pools provides the clearest evidence of attacker-controlled wallets in protocol exploit investigations.
- According to Elliptic (2024), cross-protocol hopping occurs in 45% of DeFi exploit fund movements: Attackers route stolen DeFi funds through multiple protocols before reaching exchange endpoints, requiring multi-protocol on-chain tracing expertise.
- Smart contract event logs provide a complete internal transaction audit trail: DeFi protocol event emissions record every state change and fund movement within a protocol, giving investigators a detailed forensic record unavailable in simpler blockchain architectures.
Why This Matters
DeFi protocols accounted for 67 percent of all crypto hacks in 2023, yet forensic capability to investigate DeFi activity lags significantly behind the sophistication of attacks. For fraud victims whose assets were stolen through flash loan attacks, compromised liquidity pools, or manipulated smart contracts, the window for recovery depends entirely on how quickly specialized DeFi forensics can trace assets before they are bridged out or converted. For regulated businesses offering DeFi-adjacent services, understanding smart contract investigation methodology is now an AML compliance requirement. As DeFi value locked continues to exceed $80 billion, the forensic capability to investigate it becomes correspondingly more critical.[IMAGE: DeFi investigation workspace showing a complex smart contract interaction diagram with flash loan flows, AMM liquidity pool interactions, and lending protocol calls visualized across multiple Ethereum contract addresses]
Smart Contract Forensic Challenges in DeFi
Smart contracts introduce forensic complexity beyond what standard on-chain analysis can address because they execute automated code that interacts with dozens of other contracts within a single transaction, creating fund movement paths not visible in the basic transaction record. A standard Ethereum transaction list shows only the outer transaction initiated by the user, it does not display the internal function calls, token transfers, and balance changes triggered by smart contract code execution within that transaction. Forensic investigators must access full execution trace data to reconstruct what actually happened inside a smart contract call.
This complexity is deliberately exploitable: sophisticated DeFi attackers construct transactions interacting with multiple protocols simultaneously, using flash loan capital to amplify attacks and returning the loan within the same block. According to TRM Labs (2023), the average DeFi exploit involves between four and eight levels of nested smart contract calls, with complex attacks reaching 15 or more interaction levels. Blockchain analytics platforms including Elliptic provide smart contract trace decoding tools that translate EVM bytecode into readable flowcharts, but professional DeFi forensics requires both platform tooling and deep protocol-level expertise.
| DeFi Investigation Method | What It Traces | Key Challenge | Tool Support |
|---|---|---|---|
| Smart contract trace decoding | Nested internal calls | EVM bytecode complexity | Elliptic, Chainalysis |
| Flash loan forensics | Capital flow within one block | Sub-15 second execution | Elliptic, specialist tools |
| Liquidity pool LP token tracking | AMM deposit/withdrawal | Fund commingling | Chainalysis, TRM Labs |
| Cross-protocol tracing | Multi-protocol hopping | Different methodology per protocol | All major platforms |
| Event log parsing | All DeFi state changes | High data volume | All platforms + direct parsing |
Flash Loan Forensics Methods
Flash loan forensics is defined as the investigation of attacks that exploit uncollateralized flash loan mechanisms, where a borrower can access millions of dollars in liquidity for the duration of a single transaction block without posting any collateral, provided the loan is repaid before the block closes. Flash loans enable attackers to temporarily control enormous capital, use it to manipulate DeFi protocol parameters or exploit pricing vulnerabilities, and profit from the manipulation before repaying the loan, all within a single block’s execution time.
Investigating flash loan attacks requires reconstructing the complete execution trace to identify which provider supplied capital, which protocols were manipulated, how the attacker extracted profit, and where funds went after settlement. According to Elliptic (2024), flash loan attacks accounted for over $1.8 billion in DeFi losses between 2020 and 2024, with the average attack involving three or more separate protocol interactions. Crypto Trace Labs applies specialized flash loan forensics methodology reconstructing the complete attack sequence from raw execution trace data, identifying all attacker-controlled addresses that received profit distributions.
Liquidity Pool Withdrawal Tracing
Liquidity pool forensics refers to the investigation of how funds enter and exit automated market maker (AMM) protocols such as Uniswap, Curve, and Balancer, and it is a foundational method in DeFi on-chain investigation. When an attacker or money launderer deposits stolen funds into a liquidity pool, they receive liquidity provider (LP) tokens representing their share of the pool. Tracing the stolen funds requires monitoring both the token deposit event and the subsequent LP token redemption event, which reveals when and to which address funds were ultimately withdrawn.
The challenge of liquidity pool forensics is that deposited funds are commingled with legitimate liquidity provider contributions inside the pool contract, making it impossible to track specific attacker tokens as distinct units, only the LP token representing their pro-rata share is attributable. Investigators apply amount correlation and timing analysis to link LP token redemption to the original illicit deposit. According to ACAMS (2024), liquidity pool forensics successfully identifies attacker withdrawal addresses in over 70 percent of investigated DeFi exploit cases. Crypto Trace Labs applies liquidity pool forensic analysis as a standard component of all DeFi investigations.
Cross-Protocol Fund Tracing in DeFi
Cross-protocol fund tracing in DeFi investigation is defined as the process of following assets as they move between different decentralized finance protocols in a layering sequence designed to obscure the trail between a theft event and a final cash-out. An attacker who has extracted funds from a protocol exploit may route those funds through a DEX swap, then a yield aggregator deposit, then a cross-chain bridge, then a stablecoin conversion, and finally to a centralized exchange, each step representing a different protocol interaction that must be decoded and traced individually.
Cross-protocol tracing requires maintaining a continuous fund attribution chain across each protocol interaction, applying the appropriate forensic methodology for each type: swap event log analysis for DEX interactions, LP token tracking for AMM pools, lending position monitoring, and bridge transfer correlation for cross-chain movements. According to Elliptic (2024), cross-protocol hopping occurs in 45 percent of DeFi exploit fund movement cases, with an average of three protocol interactions between exploit and exchange deposit. Crypto Trace Labs maintains active expertise across all major DeFi protocol types to reconstruct complete fund routes.
Smart Contract Event Logs as Forensic Evidence
Smart contract event logs are defined as on-chain records emitted by DeFi protocols whenever significant state changes occur, including token swaps, liquidity deposits, loan originations, and liquidation events. These event logs are stored permanently on the blockchain and provide a detailed forensic record of every financially significant action within a protocol, even when those actions happened as internal calls within a complex multi-step transaction invisible to basic transaction explorers.
By parsing event logs for the specific protocols involved, investigators reconstruct the precise sequence of actions, which addresses swapped which tokens, which accounts deposited or withdrew liquidity, and which lending positions were opened or closed. According to FinCEN (2024), smart contract event log analysis has been critical evidence in over 30 DeFi exploit prosecutions since 2021. Crypto Trace Labs applies direct event log parsing alongside commercial blockchain analytics tooling in all DeFi investigations, ensuring that no protocol interaction in the attack chain is missed.

DeFi Investigation and Crypto Asset Recovery
DeFi on-chain investigation directly supports crypto asset recovery by identifying exactly where stolen funds went after a DeFi exploit, providing the attribution evidence needed to initiate exchange freeze requests and legal recovery action. When investigation traces stolen DeFi funds to a centralized exchange deposit address, the recovery pathway is the same as in any other blockchain forensics case: formal legal process served on the exchange compliance team to freeze the account and obtain KYC (Know Your Customer) records for identity attribution and prosecution.
In some DeFi cases, additional recovery pathways are unique to the protocol context. USDT and USDC issuers can blacklist specific addresses at law enforcement request, freezing stolen funds before exchange deposit if converted to stablecoins. DeFi protocol governance mechanisms may allow emergency pauses when an exploit is identified quickly. Crypto Trace Labs coordinates with stablecoin compliance teams, DeFi protocol governance bodies, and exchange cooperation programs to maximize crypto asset recovery probability. Our MLRO (Money Laundering Reporting Officer) qualifications across UK AML, US AML, and EU AML jurisdictions enable effective navigation of formal legal requests.
Frequently Asked Questions
What is DeFi on-chain investigation?
DeFi on-chain investigation is the forensic discipline of tracing cryptocurrency assets through decentralized finance protocols, including automated market makers, lending platforms, yield aggregators, and cross-protocol systems, using smart contract trace analysis, event log parsing, and liquidity pool forensics to attribute fraud and support crypto asset recovery. It requires specialist analytical tools and deep protocol-level expertise that extend beyond standard blockchain forensics capabilities applicable to simple token transfers.
Why is DeFi forensics more complex than standard blockchain tracing?
DeFi forensics is more complex than standard blockchain tracing because smart contract execution creates nested transaction structures where a single user action triggers dozens of internal contract calls not visible in the basic transaction record. Flash loans enable attackers to borrow, manipulate, and repay capital within a single block. Liquidity pool commingling makes it impossible to track specific deposited tokens as distinct units. Cross-protocol fund routing requires applying different forensic methodology for each protocol type, maintaining attribution through each transition.
What is a flash loan attack and how is it investigated?
A flash loan attack is a DeFi exploit where an attacker borrows capital through an uncollateralized flash loan, uses it to manipulate protocol parameters across multiple DeFi platforms, extracts profit, and repays the loan, all within a single Ethereum transaction block. Investigating a flash loan attack requires reconstructing the complete execution trace to identify all protocol interactions, profit extraction events, and attacker-controlled receiving addresses, which become the starting point for forward fund tracing and crypto asset recovery through exchange cooperation.
How are liquidity pool funds traced forensically?
Liquidity pool funds are traced by monitoring LP token issuance on deposit and redemption on withdrawal, correlating the withdrawal amount with the original illicit deposit using amount and timing analysis. Because deposited funds are commingled inside the pool contract, investigators cannot track specific tokens directly but attribute the LP token representing the attacker’s pool share to their wallet address. According to ACAMS (2024), this methodology successfully identifies attacker withdrawal addresses in over 70 percent of investigated DeFi exploit cases.
What are DeFi smart contract event logs?
DeFi smart contract event logs are permanent on-chain records emitted by protocol contracts whenever significant state changes occur, including token swaps, liquidity deposits, loan originations, and settlement events. These logs provide a complete forensic audit trail of every financially significant action within a DeFi protocol, including actions from internal calls invisible to standard explorers. According to FinCEN (2024), event log analysis has been critical evidence in over 30 DeFi exploit prosecutions since 2021.
Can stolen DeFi funds be frozen or recovered?
Stolen DeFi funds can sometimes be frozen through stablecoin blacklisting, USDT and USDC issuers can freeze specific addresses at law enforcement request if stolen funds have been converted to those assets. Exchange accounts holding DeFi exploit proceeds can be frozen through legal process once blockchain analytics identifies the deposit account. Some DeFi protocol governance mechanisms allow emergency pauses. Crypto Trace Labs coordinates with stablecoin compliance teams, protocol governance, and exchange compliance programs to identify all available recovery pathways.
How does cross-protocol tracing work in DeFi investigations?
Cross-protocol tracing follows assets as they move between different DeFi protocols, applying the appropriate forensic methodology for each protocol type: swap event analysis for DEX interactions, LP token tracking for AMM pools, position monitoring for lending protocols, and bridge correlation for cross-chain movements. According to Elliptic (2024), cross-protocol hopping occurs in 45 percent of DeFi exploit fund movement cases, with an average of three distinct protocol hops between exploit and exchange deposit, each requiring its own tracing methodology.
What is the role of AML compliance in DeFi investigations?
AML compliance plays a growing role in DeFi investigations as regulatory expectations extend to decentralized finance. FATF guidance requires that DeFi protocols with identifiable controlling parties comply with AML obligations including transaction monitoring and suspicious activity reporting. UK AML, EU AML, and US AML frameworks are progressively applying VASP (Virtual Asset Service Provider) obligations to DeFi operators. AML compliance teams at exchanges receiving DeFi-origin funds must apply enhanced due diligence when blockchain analytics identifies high-risk sources.
Which blockchain analytics tools are used for DeFi investigation?
DeFi investigation uses blockchain analytics platforms including Elliptic Investigator, Chainalysis Reactor, TRM Labs, and Crystal Intelligence, all of which offer DeFi protocol interaction visualization and smart contract decoding at varying depth. Elliptic has the strongest dedicated DeFi forensics tooling among commercial platforms. These are supplemented by direct smart contract trace analysis tools, protocol-specific event log parsers, and block explorers with full trace data access. Crypto Trace Labs combines commercial platform tooling with proprietary DeFi analysis methodology for full coverage.
What does a DeFi on-chain investigation cost?
DeFi on-chain investigations at Crypto Trace Labs are structured on a case-dependent basis, with upfront engagement required for protocol exploit tracing and blockchain forensics work. Fees reflect the complexity of the protocol interaction chain, the number of chains involved, and the court-evidence output required. Non-custodial wallet recovery carries no upfront charge, payment follows successful recovery only. Contact Crypto Trace Labs to discuss the scope and fee structure for your specific case.
Executive Summary
DeFi on-chain investigation traces cryptocurrency assets through automated market makers, lending platforms, flash loan systems, and cross-protocol networks using smart contract trace decoding, LP token forensics, event log parsing, and cross-protocol fund tracking. DeFi protocols accounted for 67 percent of all cryptocurrency hacks in 2023 (Chainalysis, 2023). Flash loan attacks have caused over $1.8 billion in losses since 2020. Cross-protocol hopping occurs in 45 percent of DeFi exploit cases (Elliptic, 2024). Stablecoin blacklisting has frozen over $500 million in fraud proceeds since 2020. Crypto Trace Labs delivers court-admissible DeFi forensics reports for law enforcement, regulated institutions, and private clients across the UK, US, and EU, with no upfront charge for non-custodial wallet recovery.
What Should You Do Next?
If your case involves a DeFi exploit, smart contract fraud, or decentralized finance asset recovery, Crypto Trace Labs is ready to begin an investigation immediately. Our team, ACAMS-accredited, MLRO-qualified, and Chartered Fellow Grade at the CMI, with founding members from Blockchain.com, Kraken, and Coinbase, delivers court-ready DeFi forensics. We offer no upfront charge for non-custodial wallet recoveries.
People Also Read
- Ethereum On-Chain Forensics: Account-Based Investigation Methods
- Cross-Chain Forensics: Tracking Assets Through Blockchain Bridges
- How Do Investigators Track Cryptocurrency Through DEXs?
- Chainalysis vs Elliptic vs TRM Labs: Which Platform Should Investigators Choose
About the Author
Crypto Trace Labs is a specialist crypto asset recovery and blockchain forensics firm founded by VP and Director-level executives formerly of Blockchain.com, Kraken, and Coinbase. Our team holds ACAMS accreditations, MLRO qualifications across the UK, US, and EU, and Chartered Fellow Grade status at the CMI. With over 10 years of experience in financial crime investigation and court-recognized blockchain forensics expertise, we have recovered 101 Bitcoin for clients in the last 12 months and delivered record fraud reduction for a $14bn crypto exchange. We work with law enforcement agencies, regulated financial institutions, and private clients on crypto asset recovery, blockchain forensics, AML compliance, and expert witness testimony – globally. We offer no upfront charge for non-custodial wallet recoveries. Contact us
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your specific situation.