Peel chains are a money laundering technique where criminals transfer cryptocurrency through a series of wallets while systematically removing small amounts at each step. The bulk of stolen funds continues moving forward through change addresses while smaller portions are peeled off to exchanges or cash-out endpoints. For blockchain investigators, peel chains represent one of the most common obfuscation methods, appearing in approximately 70% of Bitcoin theft cases.
At Crypto Trace Labs, our team has tracked peel chains in hundreds of crypto asset recovery cases involving exchange hacks, ransomware payments, and organized crime. This guide draws on that decade of on-chain analysis experience to explain the forensic techniques that identify these laundering patterns.
What Makes Peel Chains Effective for Money Laundering?
Peel chains exploit transaction threshold limitations in AML systems at cryptocurrency exchanges. Most automated compliance platforms flag large single transfers as suspicious, triggering enhanced due diligence or mandatory reporting to FinCEN, the FCA, or other regulatory authorities.
By fragmenting a large sum into dozens or hundreds of smaller transactions, criminals process the same total value while avoiding automated alerts. A $1 million theft might generate immediate scrutiny in one transaction, but 200 transfers of $5,000 each slip through systems configured to flag only amounts exceeding $10,000.
Peel Chain Tactical Advantages:
- Threshold Evasion – Individual transaction amounts stay below AML reporting requirements that trigger enhanced scrutiny at exchanges and money services businesses
- Alert Fatigue – High transaction volumes overwhelm compliance teams, making it difficult to distinguish criminal activity from legitimate patterns
- Investigation Delays – Complex transaction webs require significant analyst time to untangle, allowing criminals to reach cash-out points before exchange freezes coordinate
- Cost-Benefit Calculation – Small transaction fees across hundreds of peels remain economically viable for large-scale thefts
- Pattern Camouflage – Mixing peel chains with legitimate activity complicates automated detection
Research from Chainalysis and Elliptic indicates that peel chain operations have become increasingly sophisticated, with criminals varying amounts and timing while routing through decentralized exchanges.
How Do Criminals Execute Peel Chain Operations?
Peel chain execution uses Bitcoin’s UTXO (Unspent Transaction Output) model. Criminals controlling stolen cryptocurrency initiate a transaction sending a small portion to a cash-out address while directing remaining funds to a newly generated change address. This creates the first link. The process repeats from the change address – peel another amount, bulk continues forward. After dozens or hundreds of iterations, the original large balance fragments into many small outputs dispersed across wallets.
Blockchain analytics tools show a characteristic pattern: a main chain of diminishing-value addresses with small branches extending to terminal endpoints. Professional investigators recognize this signature structure even when criminals attempt timing variations or amount randomization.
Automated scripts execute most peel chains because manual processing would be prohibitively time-consuming. Law enforcement seizures have revealed Python and JavaScript implementations processing thousands of transactions with minimal human oversight. Criminals typically peel amounts between $2,000 and $10,000, balancing detection risk against fee efficiency while staying below common AML thresholds.
What Detection Methods Identify Peel Chain Activity?
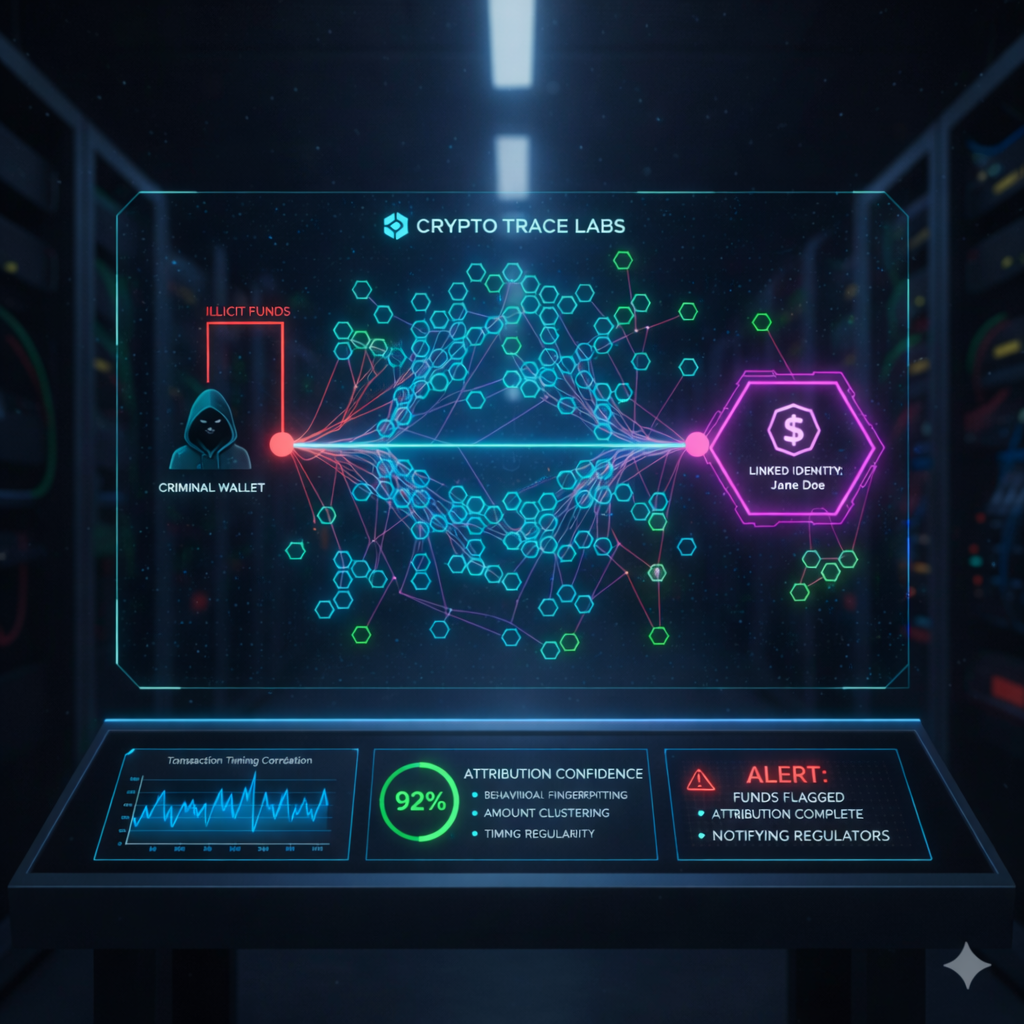
Blockchain investigators use transaction graph analysis to map complete fund flows from known theft addresses through successive hops. Peel chains create distinctive visual patterns – long main chains with regular small-value branches.
Behavioral pattern recognition analyzes transaction timing, amount distribution, and address generation to identify peel chain characteristics. Amount clustering analysis identifies when multiple small transactions from different addresses converge at a single exchange deposit address, revealing the consolidation phase where criminals regroup fragmented funds.
Peel Chain Detection Techniques:
| Technique | Methodology | Detection Accuracy | Implementation Complexity | Primary Use Case |
| Graph Pattern Recognition | Visual identification of diminishing-value main chains with regular branches | 85-90% for classic patterns | Low – standard blockchain explorer tools | Initial triage and manual investigation |
| Timing Correlation Analysis | Identifies regular interval patterns between successive peel transactions | 70-75% for automated peels | Medium – requires transaction timestamp analysis | Distinguishing automated from manual operations |
| Amount Distribution Modeling | Statistical analysis of peel size consistency and randomization | 80-85% for poorly randomized operations | High – requires statistical modeling capabilities | Identifying sophisticated criminal operations |
| Change Address Clustering | Links addresses based on UTXO common input heuristics | 75-80% on Bitcoin, lower on privacy-enhanced chains | Medium – standard clustering algorithms | Building complete transaction graphs |
| Terminal Address Analysis | Identifies exchange deposit addresses receiving peel outputs | 90-95% when exchanges cooperate | Low – entity database lookups | Tracking cash-out endpoints |
| Behavioral Fingerprinting | Machine learning classification based on transaction characteristics | 70-90% depending on training data | High – requires ML infrastructure and labeled datasets | Automated detection at scale |
Chainalysis and Elliptic combine these methods with proprietary algorithms, achieving higher accuracy than single techniques alone. Effectiveness depends on criminal sophistication – poorly executed peel chains with regular timing are easily identified, while advanced operations require machine learning pattern recognition.
How Do Different Platforms Handle Peel Chain Detection?
Major regulated exchanges in the US, UK, and EU deploy blockchain analytics platforms that automatically flag potential peel chain activity. These systems analyze incoming deposits to identify connections to known theft addresses, mixer services, or suspicious patterns. When deposits match peel chain characteristics, compliance officers can freeze funds or file suspicious activity reports.
Smaller exchanges and those in minimal-regulation jurisdictions often lack sophisticated detection. Criminals specifically target these platforms as cash-out endpoints. Decentralized exchanges present unique challenges because they lack centralized compliance and KYC requirements. Criminals frequently route peel outputs through DEX platforms to swap Bitcoin into privacy coins before cash-out attempts.
Peer-to-peer platforms and cryptocurrency ATMs represent the highest-risk endpoints with minimal transaction monitoring, allowing criminals to convert peel outputs to fiat with limited identity verification.
What Real-World Peel Chain Cases Have Been Prosecuted?
In August 2024, Queens District Attorney indicted seven individuals in a peel chain operation targeting a retirement investor. The victim purchased 5.75 Bitcoin in 2017. Hackers compromised his wallet in November 2022 and immediately initiated a peel chain. Blockchain investigators tracked the chain through dozens of transactions, identifying terminal addresses at multiple exchanges. Law enforcement coordinated freezes and identified individuals controlling cash-out accounts.
Chinese-language money laundering networks have elevated peel chains to industrial scale. January 2026 Chainalysis research shows these networks processed $16.1 billion in illicit cryptocurrency during 2025, using peel chains as core infrastructure. These groups operate openly on Telegram, advertising services with cash photographs and client testimonials. Specialized “Black U services” reached $1 billion in processed volume within 236 days, maintaining approximately 1,799 active wallet addresses.
Total cryptocurrency money laundering reached $82 billion in 2025, up from $10 billion in 2020. Investigators report that 70% of Bitcoin theft cases and 15% of overall cryptocurrency laundering utilize peel chain techniques. Stablecoins have become preferred vehicles, accounting for 63% of illicit flows in 2024. Criminals favor USDT and USDC because price stability eliminates value loss risk during extended laundering operations.
What Automated Tools Track Peel Chain Patterns?
Chainalysis Reactor provides automated peel chain detection through graph visualization and pattern recognition. The platform identifies characteristic structures when analysts input source addresses, highlighting main chains and terminal cash-out addresses. Reactor serves over 150 government agencies including FBI, IRS Criminal Investigation, and Europol.
Elliptic Investigator focuses on behavioral fingerprinting and machine learning to detect peel activity at scale. The platform analyzes timing, amounts, and address reuse to identify suspicious activity. Elliptic reports that 75% of investigations now involve tracking across 10+ different cryptocurrencies.
TRM Labs offers risk scoring that quantifies peel chain money laundering likelihood. The platform assigns numerical ratings based on illicit connections, transaction patterns, and behavioral data. Merkle Science Tracker emphasizes real-time monitoring and automated alerting, scanning blockchains continuously to identify emerging peel chains connected to known theft addresses or suspicious transaction patterns.
Peel Chain Tracking Capabilities:
| Platform | Real-Time Detection | Historical Analysis | Cross-Chain Support | Government Use | Entity Database | Risk Scoring |
| Chainalysis Reactor | Limited | Excellent | 10+ blockchains | 150+ agencies | 500M+ addresses | Basic |
| Elliptic Investigator | Good | Excellent | 100+ assets | 100+ agencies | Proprietary clusters | Advanced |
| TRM Labs | Excellent | Good | Multi-chain | Growing adoption | Glass-box attribution | Quantitative |
| Merkle Science Tracker | Excellent | Good | 50+ blockchains | Regional focus | Behavioral patterns | Contextual |
Professional services combine commercial platforms with proprietary methods and direct exchange relationships. Crypto Trace Labs pairs technical analytics with executive-level contacts at major platforms, enabling coordinated responses that freeze peel outputs before criminals complete cash-out operations.
What Challenges Do Investigators Face With Peel Chains?
The primary challenge stems from time-intensive manual transaction tracking. A sophisticated peel chain might involve 100+ transactions across dozens of addresses, with each hop requiring verification. Even with automated tools, investigators must validate classifications and investigate false positive alerts.
Cross-chain peel chains introduce additional complexity by moving funds between blockchain networks through bridges or exchanges. Criminals might peel Bitcoin through 20 transactions, bridge to Ethereum, execute another peel chain, then move to Binance Smart Chain. Investigators must track activity across multiple blockchains with different architectures, requiring cross-chain forensics expertise.
Privacy coin integration breaks on-chain trails. Criminals increasingly route peel outputs through instant exchanges converting Bitcoin to Monero, then back to different cryptocurrency after obfuscation. This forces investigators to rely on timing correlation rather than direct transaction linkage. Global regulatory fragmentation creates jurisdictional challenges when peel chains span multiple countries, requiring significant diplomatic effort that delays time-sensitive investigations.
What Should Compliance Teams Know About Peel Chains?
Compliance officers must understand that peel chains specifically target transaction threshold algorithms in AML monitoring systems. Criminals research detection capabilities of specific platforms before selecting cash-out endpoints.
Effective detection requires moving beyond simple transaction size monitoring to behavioral pattern analysis. Systems should flag addresses receiving funds from long transaction chains with diminishing value patterns, even when individual deposits remain below reporting thresholds.
Real-time blockchain monitoring provides the most effective defensive posture. By the time criminals complete multi-day peel operations and deposit funds, recovery options become limited. Systems identifying peel activity while funds remain in early stages allow coordination with upstream exchanges to freeze assets.
Industry information sharing enhances detection across the broader ecosystem. When one exchange identifies peel chain operations, sharing intelligence with other platforms enables preemptive blocking. Professional cryptocurrency fraud investigation services provide specialized expertise that internal compliance teams often lack, coordinating multi-platform investigations and providing expert witness testimony.
What Questions Do People Ask About Peel Chain Tracking?
How do investigators distinguish peel chains from legitimate business transactions?
Investigators analyze transaction patterns including consistency of peel amounts, timing regularity, address reuse, and connections to known theft sources. Legitimate businesses show irregular amounts, variable timing based on actual commercial activity, and links to verified entities rather than freshly generated addresses. Professional analysts also consider economic rationality – businesses have no reason to fragment large balances into hundreds of small transactions that incur significant fees, while criminals accept these costs for AML evasion.
What percentage of peel chain operations result in successful fund recovery?
Recovery rates vary significantly based on detection speed, criminal sophistication, and exchange cooperation. Early detection within 24-48 hours can achieve recovery exceeding 60% when funds remain at regulated exchanges. Cases involving cross-chain movement, privacy coins, or unregulated platforms show recovery below 20%. Average recovery across all peel chain cases approximates 35-40%, with higher success involving law enforcement coordination and lower success in purely civil actions.
Can peel chains be executed on all blockchain networks?
Peel chains can be executed on any blockchain that supports standard cryptocurrency transfers, though effectiveness varies by network architecture. Bitcoin’s UTXO model makes peel chains particularly effective because each transaction naturally creates change outputs that facilitate the peeling process. Account-based blockchains like Ethereum require different technical approaches but support equivalent functionality. Privacy-focused blockchains like Monero make peel chain tracking nearly impossible through built-in transaction obfuscation, which is precisely why criminals often route peel outputs through these networks as a secondary laundering layer.
How long does a typical peel chain investigation take?
Investigation duration depends on chain complexity, cross-chain elements, and resources. Simple peel chains with 20-30 transactions and clear terminal addresses at cooperative exchanges can be investigated within 48-72 hours using automated tools. Complex operations involving hundreds of transactions, multiple blockchains, privacy coins, and uncooperative platforms may require weeks or months. Law enforcement investigations with subpoena power generally move faster than private civil investigations relying on voluntary cooperation.
What legal frameworks address peel chain money laundering?
Peel chain operations violate money laundering statutes in virtually all jurisdictions. In the United States, peel chains constitute violations of 18 U.S.C. § 1956 and § 1957. The UK Proceeds of Crime Act 2002 criminalizes similar conduct. International frameworks including FATF recommendations require member countries to criminalize cryptocurrency laundering, though implementation varies. Prosecutors have successfully charged peel chain operators under traditional money laundering statutes without requiring cryptocurrency-specific legislation.
Do cryptocurrency mixers use peel chain techniques?
Cryptocurrency mixers employ different technical approaches than standard peel chains, though some operational overlap exists. Traditional mixers pool funds from multiple users and redistribute them through complex transaction patterns that break the direct on-chain link between deposits and withdrawals. Some sophisticated mixing services incorporate peel chain techniques as one component of their broader obfuscation methodology, fragmenting outputs across multiple addresses before final redistribution. Criminals sometimes combine both techniques, using mixers to obfuscate the source of peel chain funds or peeling outputs after mixer withdrawal to add additional tracking complexity.
What role do exchanges play in preventing peel chain money laundering?
Exchanges serve as critical chokepoints where peel operations must interface with regulated systems to convert cryptocurrency to fiat. Effective AML programs include blockchain analytics identifying deposits connected to peel chains, risk-based due diligence scrutinizing high-risk deposits, and information sharing with law enforcement. Exchange decisions to freeze suspected peel outputs directly impact criminal success – rapid freezing enables recovery while delayed action allows withdrawals. Regulatory pressure and reputational risk increasingly motivate sophisticated detection investments.
Can artificial intelligence improve peel chain detection?
Artificial intelligence significantly enhances peel chain detection through automated pattern recognition identifying subtle behavioral characteristics difficult for human analysts to spot consistently. AI systems analyze millions of transactions to identify emerging patterns, classify suspicious activity with confidence scores, and reduce false positives through iterative learning. Current applications focus on supervised learning where algorithms train on labeled peel chain datasets. Effectiveness depends critically on training data quality and ongoing model refinement.
What happens to cryptocurrency seized from peel chain investigations?
Law enforcement agencies that seize cryptocurrency from successful peel chain investigations typically hold assets as evidence during criminal proceedings, then liquidate after conviction to compensate victims or fund operations. The U.S. Marshals Service conducts periodic auctions of seized Bitcoin, with proceeds directed to Treasury or distributed through restitution. Some jurisdictions maintain dedicated victim compensation funds. Civil forfeiture allows seizure and liquidation without convictions when authorities demonstrate probable illicit origin through blockchain evidence.
How do investigators track peel chains that span multiple years?
Historical peel chain investigations use blockchain’s permanent records, which preserve complete transaction histories regardless of age. Investigators can analyze wallets that executed peel chains years earlier using current analytics tools, though older cases face challenges from inactive exchanges and dissolved entities. Cold case investigations benefit from improved analytical capabilities and criminals’ tendency to reactivate old addresses. Money laundering statute of limitations typically extends 5-10 years depending on jurisdiction, providing adequate legal timeframes.
What training do blockchain investigators receive for peel chain analysis?
Professional blockchain investigators complete certification programs including Chainalysis Reactor Certification and Elliptic training. These courses cover transaction graph analysis, peel chain pattern recognition, UTXO clustering, and cross-chain tracking. Law enforcement receives specialized training through FBI’s Virtual Currency Initiative and Europol’s European Cybercrime Centre. ACAMS now incorporates cryptocurrency investigation modules. Practical casework experience provides essential skills complementing formal training, with most professional investigators requiring 6-12 months to develop expert-level capabilities.
Are there legitimate uses for transaction patterns similar to peel chains?
Certain legitimate business operations create superficially similar patterns. Cryptocurrency payment processors handling merchant settlements might fragment large balances into individual payouts. Treasury management at exchanges might redistribute funds across wallets for security or operational reasons. Salary payments, affiliate commissions, and dividend distributions can generate similar patterns. Investigators distinguish legitimate activities through entity identification, economic rationality assessment, and verification of commercial relationships explaining the transaction structure.
What Should You Do Next?
This guide was prepared by the team at Crypto Trace Labs, drawing on 10+ years of cryptocurrency and financial crime experience. Our founders held VP and Director positions at Blockchain.com, Kraken, and Coinbase, and hold ACAMS certifications, MLRO qualifications across UK, US, and Europe, and Chartered status at Fellow Grade. We have tracked peel chain operations in hundreds of asset recovery cases and provided expert witness testimony in criminal prosecutions involving sophisticated money laundering schemes.
If your organization has experienced cryptocurrency theft, needs blockchain forensics support for ongoing investigations, or requires compliance consulting to strengthen peel chain detection capabilities, professional crypto asset recovery services can help. We offer no upfront charge for non-custodial wallet recoveries – you only pay after successful fund recovery.
Contact Crypto Trace Labs for cryptocurrency asset tracing, peel chain investigation, or AML compliance consulting.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.