Last Updated: February 2026
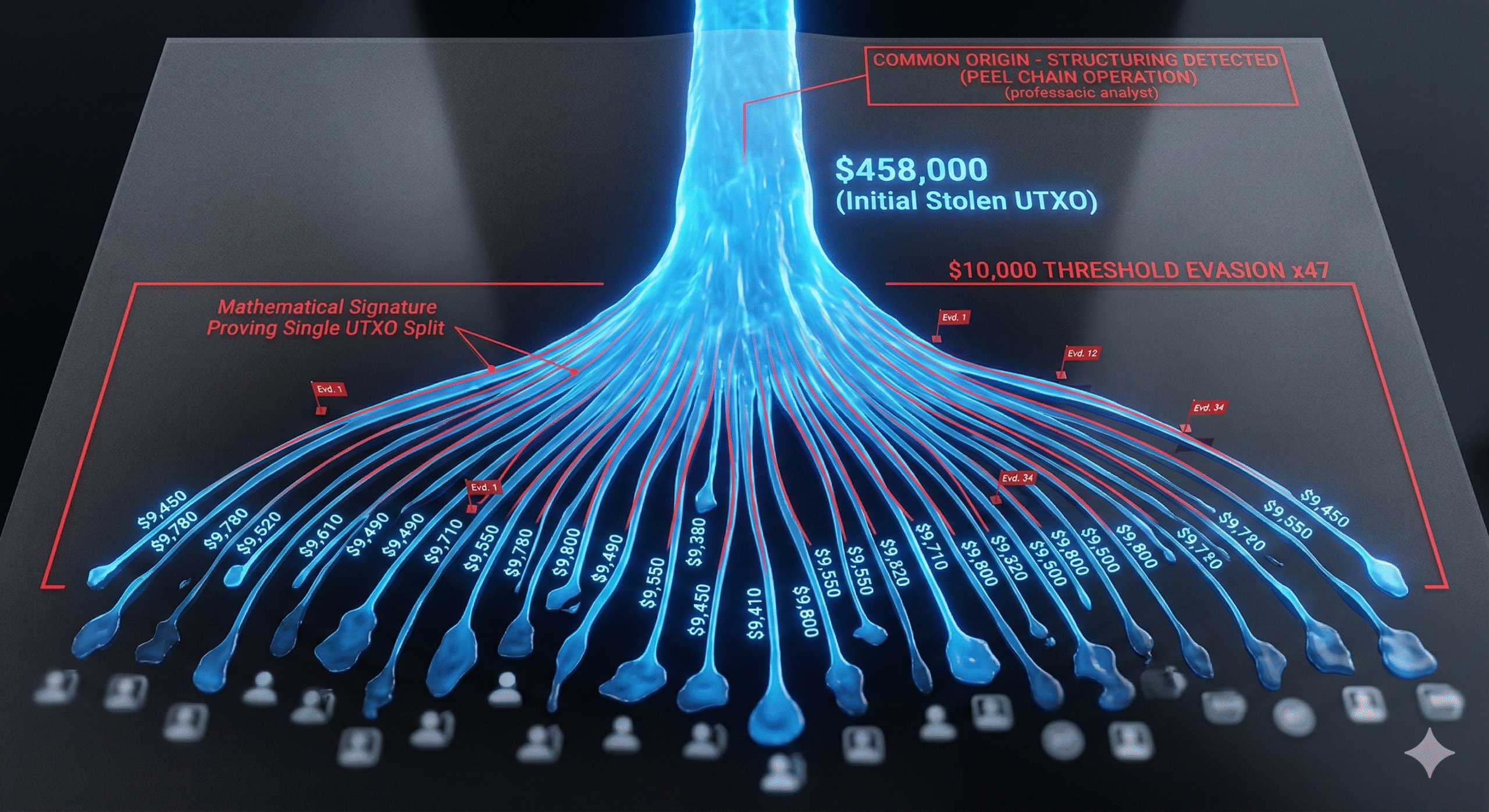
A compliance analyst at a mid-tier exchange notices something in the morning alert queue. Over the past 72 hours, 47 separate deposits have arrived from different wallet addresses – each between $9,400 and $9,800. The amounts vary just enough to look unrelated. The wallets have no transaction history before the deposits. And every one of the 47 wallets received its funding from the same parent address six hours before sending to the exchange. The total across all deposits: $458,000. No single transaction triggered a Currency Transaction Report. That is smurfing – and on a blockchain, every step of it is permanently recorded.
Smurfing – the practice of breaking large transactions into smaller amounts to avoid regulatory detection thresholds – has been a money laundering technique since long before cryptocurrency existed. But blockchain has transformed both the execution and the detection of the pattern. Criminals can generate unlimited wallets, automate thousands of structured transactions, and operate across borders without a bank teller to question the activity. Investigators, in turn, can analyze every transaction on a permanent public ledger, apply clustering algorithms to link wallets under common ownership, and detect statistical patterns that no human compliance officer could spot manually across millions of transactions.
At Crypto Trace Labs, smurfing detection is a core component of our AML investigations for exchanges, payment processors, and law enforcement agencies. This guide explains what smurfing looks like on-chain, how investigators identify the patterns, and what recent enforcement actions reveal about how the technique is evolving.
How Does Crypto Smurfing Differ from Traditional Smurfing?
The underlying principle is identical: break large amounts into smaller ones to avoid triggering regulatory reporting requirements. But the mechanics diverge significantly between traditional banking and cryptocurrency. Understanding these differences is essential for investigators who need to adapt legacy AML detection frameworks to blockchain environments.
| Dimension | Traditional Smurfing | Crypto Smurfing |
| Actors required | Multiple human “smurfs” physically visiting bank branches | A single operator controlling hundreds of programmatically generated wallets |
| Speed | Days to weeks – limited by branch hours and physical travel | Minutes to hours – automated scripts can execute thousands of transactions in a single session |
| Geographic reach | Limited to local bank branches; cross-border requires correspondent banking | Global and instant – any wallet can send to any other wallet on any chain, 24/7 |
| Detection gatekeepers | Bank tellers, branch managers, relationship officers who may notice suspicious patterns | No human gatekeeper – only automated monitoring systems at on-ramp/off-ramp points |
| Record permanence | Bank records subject to retention periods; internal records may be incomplete | Every transaction permanently recorded on a public, immutable ledger |
| Retroactive analysis | Limited to records retained by financial institutions | Any analyst can apply new detection techniques to the full historical blockchain at any time |
| Key thresholds | $10,000 CTR threshold (BSA); €15,000 (EU) | $10,000 CTR equivalent at exchanges; $3,000 Travel Rule threshold (US); €1,000 Travel Rule (EU/FATF) |
The net effect is that cryptocurrency makes smurfing dramatically easier to execute but also dramatically easier to detect after the fact – provided the investigator has the right tools and knows what patterns to look for.
What Patterns Do Investigators Use to Detect Crypto Smurfing?
Smurfing produces distinct statistical and structural signatures on-chain. Investigators at Crypto Trace Labs and across the blockchain forensics industry look for five primary patterns.
Threshold clustering
The most obvious signal. Transactions consistently kept just below regulatory reporting thresholds – $9,500 to $9,900 for BSA limits, under $3,000 for Travel Rule limits, or below exchange-specific internal thresholds – indicate deliberate structuring. The FATF’s Virtual Assets Red Flag Indicators report specifically identifies “structuring VA transactions in small amounts, or in amounts under record-keeping or reporting thresholds” as a primary red flag. In the January 2025 NoOnes exchange hack, attackers kept hundreds of withdrawal transactions just under an artificial $7,000 threshold to mimic legitimate trading behavior, extracting $7.9 million before the pattern was flagged.
Fan-out and fan-in structures
Fan-out (scatter) patterns occur when a single wallet distributes funds to many wallets in quick succession – the distribution phase of a smurfing operation. Fan-in (gather) patterns occur when many wallets consolidate funds into a single destination – the collection phase where smurfed funds are reassembled. The combination of fan-out followed by fan-in, often called a scatter-gather pattern, is the structural signature of a complete smurfing cycle. Transaction graph analysis detects these patterns by measuring the in-degree and out-degree centrality of addresses in the transaction network.
Peel chain patterns
A peel chain is a specialized form of structuring where funds move through a sequence of wallets, with a small amount “peeled off” at each step and sent to an exchange or cash-out point, while the remaining balance passes to the next wallet in the chain. The amounts progressively decrease across each hop. Research published in Forensic Science International: Digital Investigation demonstrated that improved detection methods can identify at least 12.3% more one-time change addresses used in peel chains than standard heuristics, with a 5.7% improvement in address clustering performance. Chainalysis now excludes peel chains from its illicit transaction volume metrics, reflecting how common and analytically significant the pattern has become.
Time-based anomalies
Multiple high-value transactions in short succession – particularly within a 24-hour window – are a FATF-identified red flag. Smurfing scripts often execute transactions at regular intervals (every 30 seconds, every 2 minutes) that produce a statistically detectable cadence no human would maintain. Investigators also flag staggered deposit patterns followed by long periods of wallet inactivity – consistent with disposable wallets created for a single smurfing operation and abandoned afterward.
Wallet lifecycle indicators
Smurfing wallets share common characteristics: they are newly created, receive a single funding transaction from a parent address, execute one or a small number of transactions to the target (typically an exchange deposit address), and then go permanently dormant. The combination of no prior history, single-purpose activity, and immediate dormancy – especially when observed across dozens or hundreds of wallets funded by the same source – is strong evidence of coordinated structuring. UTXO analysis on Bitcoin and similar chains can further connect these wallets through shared input patterns that reveal common ownership.
What Does the Legal Framework Look Like for Crypto Structuring?
Structuring financial transactions to evade reporting requirements is a federal crime in the United States under 31 U.S.C. Section 5324, regardless of whether the underlying funds are legitimate or illicit. This is a critical point: a person who breaks a $50,000 legitimate payment into five $9,900 transactions specifically to avoid CTR filing has committed a crime even though the money itself is clean.
Penalties escalate with scale. Structuring less than $100,000 within 12 months carries up to 5 years in prison and a $250,000 fine. Structuring more than $100,000, or structuring in connection with another criminal offense, carries up to 10 years and the same fine. These penalties apply equally to cryptocurrency transactions processed through regulated exchanges and money service businesses.
The regulatory framework is tightening. FinCEN’s August 2025 notice on cryptocurrency kiosk fraud specifically identified smurfing at crypto ATMs as an emerging threat, citing FBI data showing 10,956 complaints and $246.7 million in losses through CVC kiosks in 2024 alone – a 99% increase in complaints year-over-year. Under the EU’s Transfer of Funds Regulation, effective December 30, 2024, crypto-asset service providers must collect and transmit identifying information for all crypto transfers regardless of amount, eliminating the threshold-based avoidance that smurfing exploits.
Three Cases That Demonstrate How Crypto Smurfing Is Prosecuted
United States v. Ahlgren – first standalone crypto tax structuring case
In December 2024, Frank Richard Ahlgren III was sentenced to 24 months in federal prison for filing false tax returns and structuring cash deposits to evade CTR requirements. Ahlgren had purchased approximately 1,366 BTC in 2015 at roughly $495 each. In 2017, he sold 640 BTC for approximately $3.7 million and bought a home in Park City, Utah. To obscure the proceeds, he structured cash deposits below the $10,000 BSA threshold, used CoinJoin mixing through Wasabi Wallet, and conducted peer-to-peer cash exchanges for approximately 13 BTC. IRS Criminal Investigation used Chainalysis Reactor to trace multi-wallet hops, mixer usage, and cross-reference blockchain data with exchange records – reconstructing the full structuring pattern despite the layering attempts.
FinCEN CVC kiosk notice – smurfing at crypto ATMs
FinCEN’s August 2025 notice documented a specific smurfing typology targeting cryptocurrency ATMs (kiosks). Scam operators direct victims to split payments across multiple CVC kiosks, separating deposits into multiple lower-value transactions to evade CTR filing requirements. The FBI’s Internet Crime Complaint Center recorded $246.7 million in victim losses through CVC kiosks in 2024, with a 31% increase in dollar losses over the prior year. FinCEN required kiosk operators to use the SAR key term “FIN-2025-CVCKIOSK” when filing suspicious activity reports related to this typology – an indication that the agency considers crypto ATM smurfing a distinct and growing enforcement priority.
Samourai Wallet – infrastructure enabling structured laundering
In November 2025, Samourai Wallet founders Keonne Rodriguez (5 years) and William Lonergan Hill (4 years) were sentenced for operating an unlicensed money transmitting business. The platform processed over 80,000 BTC (approximately $2 billion) through its Whirlpool mixing and Ricochet transaction-hopping services, with $237 million in traceable criminal proceeds passing through the system. Samourai’s Ricochet feature – which added intermediary hops between the sender and the final destination – was specifically designed to defeat the kind of transaction input pattern analysis that investigators use to trace smurfed funds. The prosecution demonstrated that tools built to facilitate structuring and layering are themselves criminal enterprises.
How Are AI and Machine Learning Changing Smurfing Detection?
The scale of crypto smurfing – potentially thousands of micro-transactions across hundreds of wallets – exceeds what rule-based compliance systems can effectively monitor. The industry is increasingly deploying machine learning to detect patterns that would be invisible to threshold-based alerts.
The Elliptic2 dataset, developed in collaboration with MIT-IBM Watson AI Lab, contains 26 GB of labeled data spanning 122,000 subgraphs within 49 million node clusters and 196 million edge transactions. When researchers trained a machine learning model on this data, the model independently identified peel chains as a laundering pattern – confirming that the statistical signatures of smurfing are detectable even without predefined rules. The research noted that peel chain detection “has an analogy in ‘smurfing’ within traditional finance.”
A 2025 paper introducing the GARG-AML framework demonstrated a graph-based approach that quantifies how closely a wallet’s transaction neighborhood matches known smurfing patterns. By analyzing density-based features in transaction adjacency matrices, the system achieved over 80% detection accuracy on datasets containing scatter-gather and gather-scatter patterns – the structural signatures of fan-out and fan-in smurfing cycles.
An emerging threat compounds the detection challenge. Researchers at the Global Network on Extremism and Technology documented what they call “agentic smurfing” – the use of AI autonomous agents to fragment transactions into micro-amounts ($50-$500), distribute them across thousands of wallets, and execute cross-chain movements without human intervention. Their example described a $100,000 sum fragmented into 2,000 separate transfers spread across days, wallets, and blockchains. Countering agentic smurfing requires detection systems that can identify statistically anomalous spikes in sub-threshold transfers with coordinated timing and cross-chain routing patterns.
What Tools Detect Smurfing on Blockchain?
Chainalysis KYT (Know Your Transaction) provides real-time AML monitoring used by over 100 financial institutions and crypto exchanges. Its alert system flags transactions by severity level based on category, service exposure, direct versus indirect exposure, fund direction, and amount. KYT’s behavioral alerting continuously monitors for structuring patterns including threshold-adjacent deposits, rapid multi-wallet activity, and mixer-first funding chains.
Elliptic Investigator uses automatic behavioral detection to identify wallets engaging in peel chains, mixer-first funding, and cross-chain laundering. The system flags “funds successively sent through multiple wallet addresses, each time peeling a small portion” – the precise signature of structured peel chain laundering. Elliptic notes that results benefit from manual confirmation, positioning the tool as an investigator’s assistant rather than a standalone verdict.
TRM Labs provides multi-chain transaction tracing with entity attribution and risk scoring. TRM’s forensic platform was used alongside IRS Criminal Investigation tools in the Ahlgren prosecution, demonstrating its capability to reconstruct structuring patterns across on-chain data and exchange records.
For investigations at Crypto Trace Labs, these commercial platforms provide the initial detection layer. Complex cases – particularly those involving multi-blockchain smurfing operations – require manual forensic analysis to reconstruct the full scatter-gather cycle, attribute the controlling entity, and produce court-admissible evidence.
Frequently Asked Questions
Is smurfing illegal even if the money is legitimate?
Yes. Under 31 U.S.C. Section 5324, structuring transactions to evade reporting requirements is a federal crime regardless of whether the underlying funds are legitimate. The offense is the act of structuring itself – deliberately breaking transactions into amounts below the reporting threshold to avoid triggering a Currency Transaction Report. This applies equally to cash deposits at banks and cryptocurrency transactions at regulated exchanges. Penalties range from 5 to 10 years imprisonment depending on the amount structured.
What is the difference between smurfing and structuring?
Structuring is the broader legal term for any manipulation of financial transactions to avoid reporting requirements. Smurfing is a specific form of structuring that involves using multiple actors (“smurfs”) or multiple accounts to disperse transactions. In cryptocurrency, the distinction is less meaningful because a single individual can control hundreds of wallets, effectively playing the role of many smurfs simultaneously. Both are prosecutable under the same federal statute.
What are the reporting thresholds that trigger smurfing?
The primary U.S. threshold is $10,000 for Currency Transaction Reports under the Bank Secrecy Act. The Travel Rule requires originator and beneficiary information for transfers above $3,000 in the United States and above $1,000 or EUR 1,000 in most other FATF-compliant jurisdictions. The EU eliminated threshold-based exemptions for crypto transfers effective December 2024, requiring identifying information for all transfers regardless of amount. Exchanges also maintain internal monitoring thresholds that may trigger suspicious activity reports at lower amounts.
Can investigators trace smurfed cryptocurrency back to its source?
Yes. Unlike traditional banking where smurfing can exploit gaps between institutions’ records, blockchain smurfing leaves a complete transaction trail. Address clustering algorithms can link wallets under common ownership. Transaction graph analysis reveals the fan-out and fan-in structures that characterize smurfing cycles. And because the blockchain is immutable, investigators can apply new analytical techniques retroactively to transactions that occurred years earlier – a capability that does not exist in traditional finance.
What is a peel chain?
A peel chain is a laundering technique where funds are sent through a long sequence of wallets, with a small portion “peeled off” at each step and sent to an exchange or cash-out point. The remaining balance passes to the next wallet in the chain. Each peel reduces the amount slightly, creating a gradually diminishing trail. Peel chains are the blockchain equivalent of physically visiting dozens of bank branches to make small deposits – but automated, faster, and conducted through disposable wallets that are abandoned after a single use.
How is “agentic smurfing” different from traditional crypto smurfing?
Agentic smurfing uses AI autonomous agents to execute the structuring operation without human intervention. Rather than a person scripting transactions, an AI agent independently decides how to fragment amounts, which wallets to create, what timing to use, and which chains to route through. Researchers documented an example where a $100,000 sum was fragmented into 2,000 transfers of $50-$500, spread across days and multiple blockchains. The technique is harder to detect because the AI can introduce randomness into amounts, timing, and routing that defeats pattern-matching rules designed around human-operated smurfing.
Does Your Compliance Program Detect Crypto Smurfing?
If your exchange, payment processor, or financial institution processes cryptocurrency transactions, your AML monitoring system must be capable of detecting structuring patterns – not just individual threshold breaches. FinCEN’s October 2025 SAR guidance clarified that institutions are not required to file suspicious activity reports for transactions near $10,000 solely because they approach that amount. But they are required to file when they have reason to suspect that transactions are designed to evade reporting – and the statistical patterns of smurfing provide exactly that reason. SAR filings surged 51.8% between 2020 and 2024, reflecting increased regulatory scrutiny of structuring across both traditional and crypto channels.
Crypto Trace Labs conducts smurfing detection audits, AML compliance assessments, and forensic investigations for exchanges and financial institutions. Our forensic team – including analysts like D. Hargreaves – holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. Our founders held VP and Director positions at Blockchain.com, Kraken, and Coinbase.
Contact Crypto Trace Labs for a smurfing detection assessment or to discuss an active investigation involving structured cryptocurrency transactions.
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, on-chain analysis, and forensic investigation. Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed vanity address exploitation patterns in hundreds of investigations and provided expert witness testimony on blockchain attribution methodologies in court proceedings.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.