Last Updated: February 2026
In October 2024, the FBI announced something unprecedented in financial enforcement history: it had created its own cryptocurrency token. NexFundAI, an Ethereum-based ERC-20 token built by federal agents, was designed from inception as a trap. The sting – dubbed Operation Token Mirrors – targeted professional market manipulation firms that inflate token prices through coordinated wash trading and pump-and-dump tactics. Within months, 18 individuals and entities across four countries faced criminal charges, over $25 million in cryptocurrency was seized, and the founders of Gotbit, CLS Global, and ZM Quant were in custody or under indictment. The operation did not just produce indictments. It produced a forensic blueprint for how pump-and-dump schemes operate on-chain – and precisely how investigators dismantle them.
Pump-and-dump manipulation is the most prevalent form of market fraud in cryptocurrency. Chainalysis data from 2024 and 2025 shows that tokens designed to extract value from buyers through artificial price inflation generated billions in losses across decentralised exchanges. On Solana’s pump.fun platform alone, over 7 million tokens were launched by early 2025, with fewer than 2% ever achieving meaningful market capitalisation. The rest followed a predictable pattern: launch, inflate, extract, abandon. But because every step of this process executes on a public ledger, investigators who track cryptocurrency through DEXs can reconstruct the entire scheme – from token creation to final cash-out – with a precision impossible in traditional markets.
What Makes Pump-and-Dump Different on the Blockchain
Traditional pump-and-dump schemes – penny stock manipulation via boiler rooms and fabricated press releases – took weeks or months to execute. Email spam campaigns in the 2000s shortened cycles to days. Cryptocurrency has compressed them further, to hours or even minutes.
Three characteristics distinguish blockchain-based pump-and-dump from its predecessors. First, token creation has become trivially easy. Platforms like pump.fun on Solana allow anyone to deploy a tradeable token in under sixty seconds for less than $2 in fees. No securities registration, no exchange listing application, no corporate formation required. This near-zero barrier has industrialised token fraud at a scale traditional markets never experienced.
Second, the manipulation infrastructure is professionalised. As Operation Token Mirrors revealed, dedicated market-making firms like Gotbit offered volume support packages – wash trading services priced between $2,000 and $20,000 per month – that could make any worthless token appear actively traded. These firms used algorithmic bots to generate fake volume, manipulate order books, and create the illusion of organic demand that attracted genuine buyers.
Third, and most consequentially for investigators, every manipulation step produces permanent on-chain evidence. The deployer wallet, the initial token allocation, every coordinated purchase, every liquidity addition and removal, every sale – all are immutably recorded. Unlike traditional pump-and-dump cases where prosecutors must subpoena broker records and reconstruct phone call logs, blockchain forensic teams analysing smart contract activity can access the complete transaction history of any token from the moment of its creation.
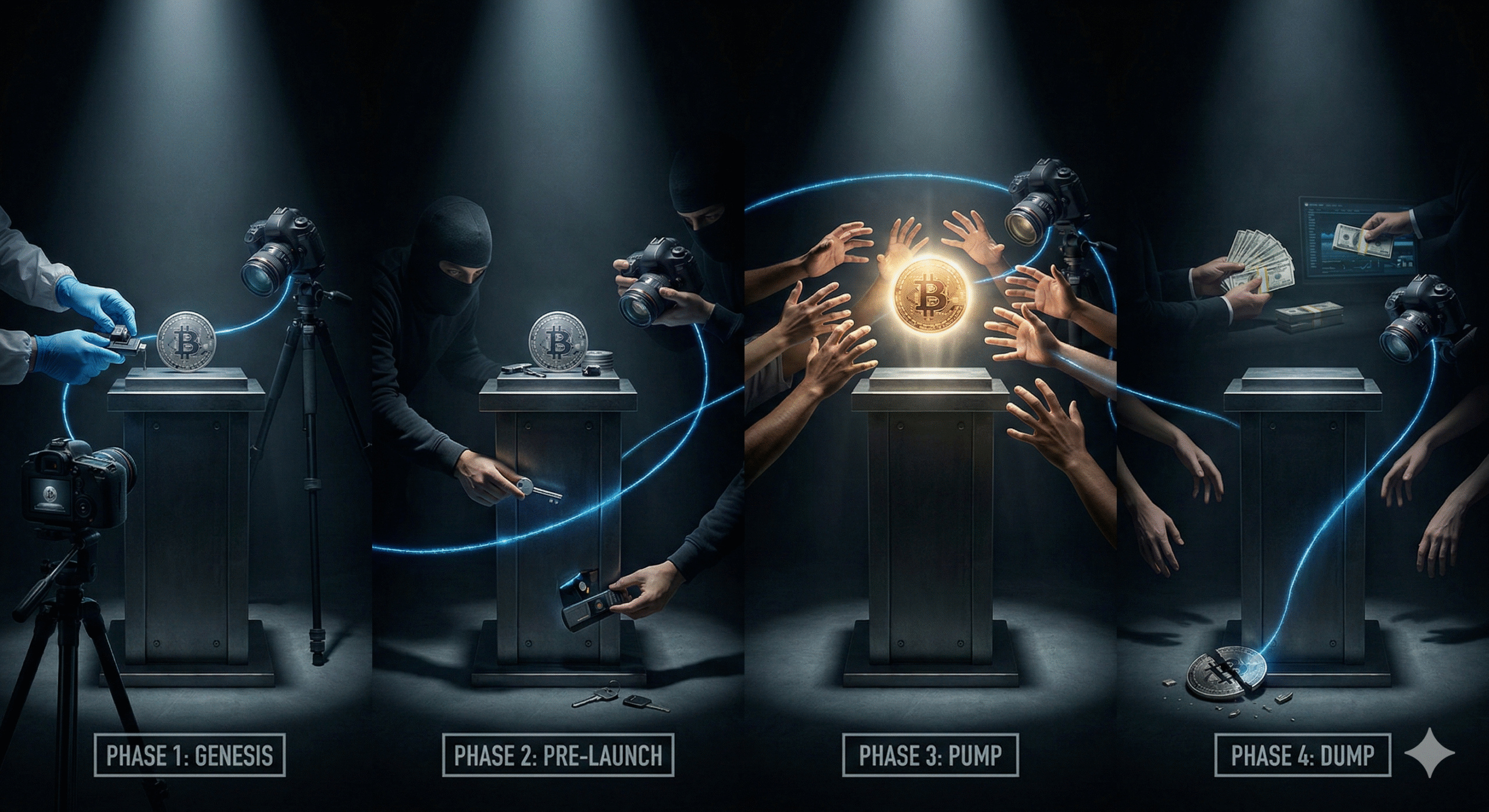
The Four-Phase Forensic Detection Pipeline
Investigators do not detect pump-and-dump schemes through a single signal. They apply a systematic pipeline that examines four distinct phases of the scheme’s lifecycle, where each phase reveals different categories of evidence.
Phase 1: Token Genesis Analysis
Every pump-and-dump begins with a smart contract deployment. Forensic analysis starts here, examining both the contract code and the deployment wallet.
Contract code review identifies manipulation mechanisms embedded before trading begins. These include hidden mint functions that allow the deployer to create additional tokens after launch, sell restrictions that prevent buyers from exiting (honeypot contracts), modifiable tax parameters that can be increased to 100% after buyers enter, and blacklist functions that can lock specific wallets from trading. Automated scanners like Token Sniffer and GoPlus Security flag these patterns, but sophisticated operators increasingly use proxy contracts and timelocked modifications that evade basic detection.
Deployment wallet analysis traces the funding source of the contract creator. When the deployer wallet was funded through a mixer, a bridge from another chain, or a freshly created exchange withdrawal, investigators map these connections using transaction graph analysis to identify whether the same entity has deployed previous fraudulent tokens.
Phase 2: Pre-Launch Wallet Mapping
Between token creation and public promotion, pump-and-dump operators distribute tokens to wallets they control. This pre-launch activity leaves distinctive patterns.
Allocation analysis examines how the token supply is distributed before trading begins. In legitimate token launches, allocation is documented in whitepapers with vesting schedules. In pump-and-dump schemes, large allocations flow to wallets with no public identity, no vesting restrictions, and funding chains that trace back to a common source. Visualisation tools like Bubblemaps can reveal when 50% or more of a token’s supply sits in wallets controlled by a single entity – a hallmark of manipulation readiness.
Sniping infrastructure preparation is another pre-launch signal. Operators stage wallets with pre-approved token spending permissions and ETH or SOL balances sized precisely for immediate purchases when liquidity is added. These wallets often share Sybil-like characteristics – funded from the same source, created within the same time window, exhibiting no prior transaction history.
Phase 3: Coordinated Buying Detection
The pump phase generates the most visible on-chain footprint. Investigators identify coordination through several analytical methods.
Temporal clustering analysis examines whether large purchases occur within abnormally tight time windows. When dozens of wallets execute buy orders within the same block or consecutive blocks – particularly wallets with no prior trading history on that token – the pattern strongly suggests automated coordination rather than organic discovery. Transaction velocity analysis quantifies these timing anomalies precisely.
Volume-to-unique-wallet ratios reveal fabricated demand. A legitimate token gaining organic traction shows a roughly proportional relationship between trading volume and unique participating addresses. In pump-and-dump schemes, volume spikes dramatically while the number of unique wallets remains low – a small group of wallets generating disproportionate activity through rapid buying and selling.
Social media correlation maps on-chain activity to off-chain promotion campaigns. When investigators identify coordinated Telegram pump group signals or paid influencer posts, they timestamp-match these promotions against on-chain buying patterns to establish the connection between promotion and manipulation.
Phase 4: Exit Pattern Reconstruction
The dump phase – where operators extract value from new buyers – provides the evidence most relevant to prosecution. Investigators reconstruct exit patterns to identify the beneficiaries and quantify losses.
Liquidity removal tracking is critical for DEX-listed tokens. In many schemes, the operator adds initial liquidity to a decentralised exchange pool, promotes the token to attract buyers (which increases the pool’s value), then removes the liquidity – taking the buyers’ contributions with it. This liquidity rug pull is traceable transaction by transaction, from the LP token mint to its redemption and the subsequent movement of extracted funds.
Phased selling analysis identifies when insiders distribute their holdings gradually rather than in a single dump. Sophisticated operators sell in small increments across dozens of wallets to obscure the coordinated exit. But layering transaction analysis and wallet clustering techniques can reconstruct these distributed sells into a unified exit timeline.
Fund flow tracing follows the proceeds from sale wallets through any obfuscation layers – mixers, bridges, or intermediate wallets – to their final destinations at exchanges, OTC desks, or fiat off-ramps. This phase connects the on-chain manipulation to real-world identities and is typically where blockchain analytics platforms like Chainalysis and Elliptic add the most value through their exchange attribution databases.
Three Cases That Defined On-Chain Pump-and-Dump Investigation
Operation Token Mirrors: When the FBI Built a Token
The October 2024 Operation Token Mirrors case remains the most significant pump-and-dump enforcement action in cryptocurrency history. FBI agents created NexFundAI as an Ethereum token and approached market manipulation firms requesting their services. The firms – Gotbit, CLS Global, ZM Quant, and associated individuals – were recorded describing and then executing their manipulation techniques on a token that was itself a law enforcement tool.
Gotbit, a Russia-linked market maker, created fake trading volume using approximately 60 wallets per engagement, cycling funds to simulate organic activity. Its founder, Aleksei Andriunin, was charged and ultimately received 8 months imprisonment and forfeited $23 million. CLS Global, based in the UAE, was fined $428,059 and banned from US-accessible cryptocurrency markets for three years. The case established that professional market manipulation services – even when marketed as legitimate market making – constitute criminal conduct under US law.
The forensic significance of Operation Token Mirrors lies in the evidence methodology. Prosecutors presented on-chain transaction data showing precisely how each firm’s wallets interacted with NexFundAI, demonstrating the full pump-and-dump lifecycle from coordinated buying through artificial volume generation to planned distribution. This evidence template is now available to every prosecutor building similar cases.
HAWK Token: Celebrity Promotion Meets Blockchain Forensics
In December 2024, the HAWK token – promoted by internet personality Hailey Welch – launched on Solana and reached approximately $490 million in market capitalisation within its first minutes of trading. Within hours, the price had collapsed more than 90%. On-chain analysis revealed why.
Blockchain investigators identified that approximately 96% of the token supply was concentrated in just 10 insider wallets at launch, with only 3–4% available to the general public. One sniper wallet acquired 17.5% of the entire HAWK supply within seconds of launch for roughly $993,000 in SOL, then sold for a $1.3 million profit within 90 minutes. These insider wallets began selling systematically as the promotional campaign drove retail buyers into the token. The on-chain evidence showed the classic four-phase pattern: pre-positioned wallets, coordinated early buying, social media-driven retail influx, and insider distribution during peak demand.
Multiple class-action lawsuits followed, with plaintiffs citing on-chain evidence of insider concentration and coordinated selling patterns. The case demonstrated that even when a token avoids a classic rug pull by not removing all liquidity, forensic analysis of wallet coordination and selling patterns can still establish market manipulation sufficient for civil and potentially criminal liability.
The Pump.fun Epidemic: Industrial-Scale Token Fraud on Solana
The scale of pump-and-dump activity on Solana’s pump.fun platform redefined what industrial-scale token fraud looks like. By early 2025, the platform had facilitated the creation of over 7 million tokens. Chainalysis analysis found that only approximately 1.4% of these tokens ever reached a market capitalisation of $69,000 – the threshold required for migration from pump.fun’s bonding curve to the Raydium decentralised exchange. The remaining 98.6% either were abandoned by creators or failed to attract sufficient buying interest to generate meaningful extraction.
Forensic analysis of pump.fun patterns revealed a repeating operational signature. A deployer creates a token, allocates a portion to insider wallets, promotes it through Telegram channels and social media bots, and exits once sufficient outside capital enters. Many operators run this process dozens of times daily, creating and abandoning tokens as a volume business. Investigators have identified individual wallet clusters responsible for hundreds of serial token deployments, each following the same template: create, pump, extract, repeat.
The platform itself earned over $800 million in fees by early 2025, raising questions about the responsibility of infrastructure providers that enable mass-scale token fraud – even without direct participation in any individual manipulation scheme.
Smart Contract Red Flags Investigators Prioritise
Not every manipulated token exhibits the same vulnerabilities, but forensic teams have catalogued the indicators most strongly correlated with pump-and-dump intent.
Unrelinquished ownership. When a token’s deployer retains the owner role, they maintain administrative functions including minting, pausing, and blacklisting. Legitimate projects typically renounce ownership or transfer it to a governance contract. Retained ownership is the single most common structural red flag.
Hidden mint functions. Some contracts include functions that allow the owner to create unlimited additional tokens after launch. These may be disguised behind proxy patterns or obfuscated function names. When the owner mints tokens after the public sale begins, they dilute existing holders and create sell pressure without any corresponding buy.
Modifiable transfer taxes. Contracts with adjustable buy/sell tax parameters allow operators to set a 0% tax during the pump phase to encourage buying, then increase the sell tax to 99% – effectively trapping buyers who cannot sell without losing nearly all their value.
Honeypot logic. The most predatory contracts include code that prevents any wallet except pre-approved addresses from selling. Buyers can purchase the token but receive a transaction revert when attempting to sell. On-chain evidence of a honeypot is unambiguous: a pattern of successful buy transactions across many wallets with zero successful sells from any wallet other than the deployer and its affiliates.
No liquidity lock. When LP tokens are not locked in a time-lock contract or burned to a dead address, the deployer can remove all liquidity at any moment. Investigators verify whether LP tokens remain in the deployer’s wallet – and if they do, liquidity removal is a transaction away.
Frequently Asked Questions
How do pump-and-dump schemes work in cryptocurrency?
Organisers create or acquire a large position in a token, artificially inflate its price through coordinated buying and promotional campaigns, then sell their holdings into the inflated demand. On decentralised exchanges, this often involves deploying a new token, adding initial liquidity, promoting the token through social media and Telegram groups, and removing liquidity or selling insider allocations once enough outside capital has entered. The entire cycle can execute in hours on high-throughput chains like Solana.
What percentage of new cryptocurrency tokens are pump-and-dump schemes?
The data suggests the vast majority of token launches are extractive. On Solana’s pump.fun platform, approximately 98.6% of tokens launched in 2024 failed to reach even $69,000 in market capitalisation. While not every abandoned token is necessarily a deliberate pump-and-dump, analysis shows that serial deployers – wallets creating dozens or hundreds of tokens – account for a substantial portion of launches and exhibit consistent extraction patterns across their deployments.
Can pump-and-dump organisers actually be prosecuted?
Yes, and criminal prosecution is accelerating. Operation Token Mirrors in October 2024 produced 18 criminal charges across four countries. Gotbit’s founder received 8 months imprisonment and forfeited $23 million. CLS Global paid $428,059 in penalties. The SEC has brought civil enforcement actions under securities fraud provisions, and the DOJ has pursued wire fraud and conspiracy charges that carry sentences of up to 20 years. Under the EU’s MiCA regulation, market manipulation including pump-and-dump schemes is explicitly prohibited with penalties up to EUR 5 million for individuals.
How quickly can investigators detect a pump-and-dump in progress?
Real-time detection is increasingly feasible. Automated monitoring systems can flag anomalous token launches, suspicious contract code, and coordinated buying patterns within minutes of their occurrence. Blockchain analytics firms operate alert systems that notify subscribers when tokens exhibit pump-and-dump indicators. However, retrospective investigation – reconstructing the complete scheme after the fact using permanently recorded on-chain data – remains the primary approach for enforcement actions.
What tools detect potentially fraudulent tokens before they crash?
Several automated scanning platforms provide pre-trade intelligence. Token Sniffer analyses smart contract code for known vulnerability patterns and manipulation mechanisms. GoPlus Security provides real-time token security assessments including honeypot detection, ownership analysis, and liquidity lock verification. Bubblemaps visualises token holder concentration to identify insider dominance. DEXScreener and DEXTools provide trading data analysis. However, no tool provides complete protection, as sophisticated operators constantly adapt their techniques to evade automated detection.
Are all meme coins pump-and-dump schemes?
Not all, but the category carries disproportionate risk. Some meme coins – notably Dogecoin and Shiba Inu – achieved sustained community adoption and maintain active trading markets years after launch. The vast majority of meme token launches, however, are designed for short-term value extraction. The key forensic distinction is between tokens with distributed ownership and organic community growth versus tokens with concentrated insider holdings and coordinated promotional campaigns. On-chain holder distribution analysis is the most reliable method for distinguishing the two.
When On-Chain Evidence Demands Expert Analysis
Pump-and-dump schemes leave more evidence on-chain than almost any other form of market manipulation. The challenge is not whether the data exists – it is whether the analysis meets the evidentiary standards required for enforcement, litigation, or regulatory reporting. Whether you are a compliance team screening token listings for exchange due diligence, a regulator building a market manipulation case for enforcement action, or a victim seeking to trace extracted funds for recovery proceedings, contact Crypto Trace Labs to discuss how D. Hargreaves and our forensic team can apply four-phase detection methodology to your specific token, market, or portfolio exposure.
About the Author
This guide was prepared by the blockchain forensics team at Crypto Trace Labs. Our founding members held VP and Director-level positions at Blockchain.com, Kraken, and Coinbase, bringing over 10 years of combined experience in cryptocurrency operations, on-chain analysis, and forensic investigation. Our team holds ACAMS certifications, MLRO qualifications across UK, US, and European jurisdictions, and Chartered status at Fellow Grade. We have analyzed vanity address exploitation patterns in hundreds of investigations and provided expert witness testimony on blockchain attribution methodologies in court proceedings.
This content is for informational purposes only and does not constitute legal, financial, or compliance advice. Crypto asset recovery outcomes depend on specific circumstances, regulatory cooperation, and technical factors. Consult qualified professionals regarding your situation.